🚀 A CloudSEK se torna a primeira empresa de segurança cibernética de origem indiana a receber investimentos da Estado dos EUA fundo
Leia mais
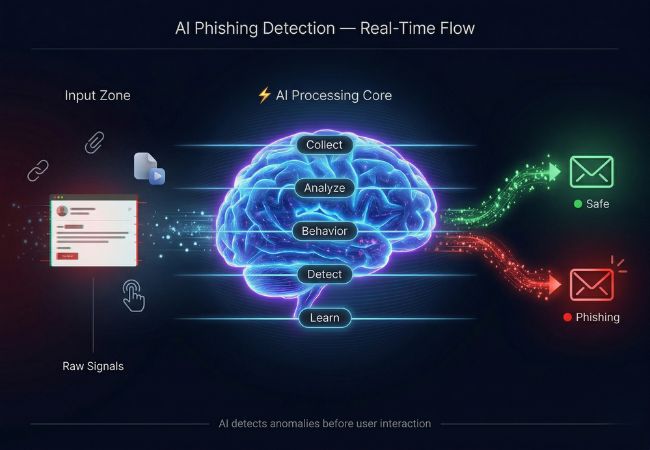
AI phishing detection is a cybersecurity approach that uses machine learning and data analysis to identify malicious emails, links, and communication patterns associated with phishing attacks. Intelligent systems evaluate multiple signals such as content, sender identity, and behavioral anomalies to detect threats accurately.
Traditional security methods rely on static rules, whereas AI-driven detection continuously learns from new data and evolving attack patterns. Adaptive models improve over time, enabling more precise identification of sophisticated phishing attempts that bypass conventional filters.
Growing complexity of cyber threats has made automated detection essential for modern organizations. Advanced AI systems provide real-time insights and proactive protection, ensuring faster response to potential phishing risks.
AI phishing detection works through a structured process that analyzes email data, user behavior, and threat patterns to identify malicious activity in real time.
Multiple advanced technologies combine to analyze phishing signals across email content, user behavior, and threat intelligence systems with high accuracy.
Phishing attacks vary in structure, targeting methods, and delivery channels, requiring AI systems to analyze multiple threat vectors for accurate detection.
Email phishing involves large-scale campaigns where attackers send fraudulent messages to manipulate users into sharing sensitive data. AI systems evaluate email headers, content patterns, attachments, and sender reputation to identify malicious intent.
Spear phishing targets specific individuals using personalized information such as names, roles, or organizational context. Machine learning models detect inconsistencies in communication patterns and intent despite highly customized messaging.
Whaling attacks focus on high-level executives or decision-makers using highly sophisticated and targeted messages. Behavioral analytics and contextual anomaly detection help identify unusual requests or impersonation attempts aimed at leadership roles.
Clone phishing replicates legitimate emails by copying content and replacing links or attachments with malicious versions. AI systems compare historical email patterns and detect subtle modifications that indicate tampering.
AI-generated phishing uses advanced language models to create human-like and context-aware messages. Natural language processing identifies linguistic inconsistencies, unnatural phrasing patterns, and contextual deviations in such content.
URL-based phishing redirects users to spoofed or malicious websites designed to steal credentials or data. AI detection systems analyze domain reputation, URL structure, and redirection behavior to block unsafe links.
Smishing (SMS phishing) and vishing (voice phishing) use text messages or phone calls to deceive users. AI-powered systems analyze communication patterns, sender identity, and behavioral signals across multiple channels to detect these threats.
Read More: Major Phishing Techniques in 2026
The growing scale and complexity of cyber threats have made traditional detection methods less effective in modern cybersecurity environments. Industry data reflects this shift, with APWG reporting 3.8 million phishing attacks globally in 2025, up from 3.76 million in 2024.
Handling such volume has become increasingly difficult with manual review and static filtering approaches. With an estimated 3.4 billion phishing emails reaching inboxes daily, automated detection powered by intelligent systems becomes essential.
Attackers now use advanced techniques, including AI-generated content, to create highly convincing phishing messages. Adaptive detection models help organizations respond faster and reduce risk across evolving threat landscapes.
AI detects phishing attacks by evaluating multiple risk signals and connecting them to identify malicious intent beyond surface-level indicators.
Detection begins with analyzing email content for manipulation tactics such as urgency, impersonation, and deceptive intent. Linguistic inconsistencies and unusual phrasing patterns often indicate potential phishing attempts.
Sender identity is then verified using domain reputation, authentication protocols, and spoofing detection techniques. Mismatches between sender details and expected communication patterns increase suspicion.
Embedded links are examined for domain structure, redirection behavior, and similarity to legitimate websites. Suspicious URL patterns and hidden redirects strengthen the likelihood of a phishing attempt.
Attachments are evaluated for malicious code, abnormal file behavior, and hidden payloads. Detection systems identify threats before execution to prevent system compromise.
User interaction patterns such as login behavior, click activity, and access timing are analyzed for anomalies. Deviations from normal behavior provide additional confirmation of suspicious activity.
All detected signals are combined to generate a final risk score that determines whether the message is malicious. Correlated analysis improves accuracy by validating threats across multiple layers instead of relying on a single indicator.
Modern cybersecurity systems rely on intelligent automation, where AI phishing detection improves threat identification and response while still facing limitations in accuracy and adaptability.
Preventing phishing requires combining security systems, access controls, and user-level practices to reduce exposure to malicious communication.
Email security platforms scan incoming messages and block suspicious content before delivery. Filtering reduces the number of phishing emails reaching user inboxes.
Multi-factor authentication and secure login mechanisms restrict unauthorized account access. Additional verification steps limit misuse of stolen credentials.
Authentication protocols such as SPF, DKIM, and DMARC validate sender domains and identify spoofed emails. Verified sender identity reduces trust in fraudulent messages.
URL scanning tools evaluate links based on domain structure and redirection behavior. Blocking unsafe links prevents interaction with malicious websites.
Security awareness programs train users to identify phishing attempts and suspicious communication patterns. Informed users reduce the likelihood of successful attacks.
Regular updates to security tools and detection systems align protection with new phishing techniques. Updated systems handle evolving attack patterns more reliably.
CloudSEK prevents phishing attacks by shifting from reactive filtering to a proactive, intelligence-driven approach that identifies threats before they reach user inboxes or devices. Contextual AI systems monitor the surface, deep, and dark web to detect early signals of phishing preparation.
The XVigil platform uses specialized modules such as fake domain detection, evasion-resistant scanning, and brand monitoring to uncover phishing infrastructure at an early stage. Continuous tracking of look-alike domains, hidden phishing pages, and fraudulent social profiles reduces exposure to large-scale attacks.
Additional intelligence layers include leaked credential monitoring, supply chain risk analysis, and threat actor tracking to predict targeted phishing campaigns. Automated takedown processes ensure that malicious domains, content, and attacker infrastructure are removed quickly to minimize impact.
Yes, AI phishing detection can identify zero-day attacks by analyzing unusual patterns in email content, sender behavior, and communication context. Instead of relying on known signatures, it flags deviations that indicate a previously unseen threat.
AI phishing detection handles encrypted emails by analyzing metadata such as sender identity, frequency, and communication patterns. Even without accessing content, suspicious behavior and anomalies can still be identified.
AI phishing detection works across multiple channels including email, SMS, and social media platforms. Cross-channel monitoring helps identify phishing campaigns that operate beyond a single communication method.
A IA reduz os falsos positivos avaliando vários sinais, como comportamento do usuário, interações históricas e contexto da mensagem, em vez de depender de um único indicador. Essa análise em camadas ajuda a distinguir e-mails legítimos dos suspeitos com mais precisão.
Sim, pequenas empresas podem usar a detecção de phishing por IA por meio de soluções baseadas em nuvem que exigem configuração e infraestrutura mínimas. Esses sistemas oferecem proteção escalável sem a necessidade de equipes de segurança dedicadas.
A detecção de phishing por IA responde a novas ameaças em tempo real analisando continuamente os dados recebidos e atualizando os modelos de detecção. A adaptação rápida permite que os sistemas identifiquem e mitiguem técnicas emergentes de phishing rapidamente.
