🚀 CloudSEK becomes first Indian origin cybersecurity company to receive investment from US state fund
Read more
Cloud vulnerabilities are security weaknesses in cloud infrastructure, configurations, or services that attackers exploit to access data, disrupt operations, or gain unauthorized control. Most incidents stem from misconfigured storage, excessive identity permissions, insecure APIs, weak authentication, and inadequate monitoring.
Misconfigured cloud storage and overly permissive IAM roles remain the most frequent causes of data breaches in multi-cloud environments. Insecure interfaces, unpatched software, and container mismanagement further expand the attack surface across IaaS, PaaS, and SaaS models.
Effective risk reduction depends on strict access governance, continuous monitoring, encryption enforcement, and adherence to recognized security frameworks. Structured prevention strategies help organizations protect sensitive assets, maintain compliance, and sustain operational resilience.
Cloud vulnerabilities occur due to operational complexity, mismanagement of security controls, and expanding attack surfaces across cloud environments.
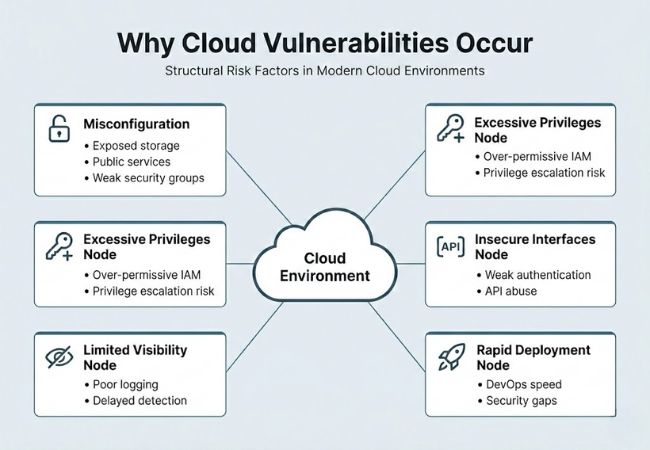
Cloud environments face security weaknesses across storage, identity, networking, and application layers that attackers exploit to access data and disrupt operations.
Public storage buckets with incorrect permission settings expose sensitive data to unauthorized access. Attackers continuously scan cloud environments for open storage instances that lack proper access restrictions.
Human error during configuration or policy updates often leads to unintended public exposure. Even a single misconfigured bucket can result in large-scale data breaches and compliance violations.
Overly permissive IAM roles grant users and services more access than operationally required. Excessive privileges increase the risk of lateral movement and privilege escalation attacks.
Poorly structured access policies often remain undetected until a security incident occurs. Enforcing least-privilege principles significantly reduces the potential blast radius.
APIs connect cloud services, applications, and third-party integrations, making them high-value attack targets. Weak authentication or insufficient input validation allows attackers to exploit these entry points.
Lack of rate limiting and monitoring further increases exposure to automated attacks. Proper API gateway security and token-based authentication strengthen defense mechanisms.
Read More: Exposed APIs
Single-factor authentication exposes cloud accounts to phishing and credential stuffing attacks. Compromised credentials frequently lead to unauthorized administrative access.
Absence of multi-factor authentication significantly increases account takeover risk. Strong authentication controls act as a critical barrier against identity-based threats.
Also See: Social Engineering vs Phishing
Data stored or transmitted without encryption remains vulnerable to interception and unauthorized retrieval. Attackers can exploit unsecured communication channels to capture sensitive information.
Inconsistent encryption policies across workloads create uneven security coverage. Enforcing encryption at rest and in transit strengthens overall data protection.
Employees or contractors with legitimate access may intentionally or accidentally expose confidential data. Insider incidents often bypass traditional perimeter-based defenses.
Limited behavioral monitoring makes early detection difficult. Strict access governance and activity logging help mitigate insider-related risks.
Stolen credentials enable attackers to manipulate infrastructure, delete resources, or extract sensitive information. Phishing and malware campaigns frequently target privileged cloud accounts.
Unusual login patterns often go unnoticed without advanced monitoring systems. Continuous authentication validation helps detect compromised accounts early.
Unauthorized cloud applications deployed outside IT oversight introduce unmanaged vulnerabilities. Lack of centralized governance increases hidden risk exposure.
Unapproved services may not follow corporate security standards. Visibility and policy enforcement tools reduce shadow IT-related threats.
Outdated or unverified container images introduce exploitable software flaws into production environments. Vulnerabilities within a base image can propagate across multiple deployments.
Inadequate image scanning increases the likelihood of running compromised workloads. Regular updates and runtime protection reduce container-related risks.
Improperly secured Kubernetes clusters expose dashboards, APIs, and workloads to public networks. Weak role-based access controls amplify exploitation potential.
Misconfigured network policies allow unauthorized communication between pods. Cluster hardening and continuous configuration monitoring improve resilience.
Serverless functions often operate with broad execution permissions that exceed operational needs. Misconfigured roles may allow unintended resource access.
Limited runtime visibility complicates threat detection. Secure coding practices and granular policy enforcement reduce exposure.
Outdated operating systems and libraries contain known vulnerabilities with publicly available exploits. Attackers commonly target systems lacking timely security updates.
Delayed patch cycles increase exposure windows. Automated vulnerability scanning and patch management reduce exploitation risk.
Absence of centralized logging delays detection of suspicious activity. Without visibility, security teams cannot respond quickly to incidents.
Long dwell times increase the overall impact of breaches. Integrated monitoring solutions improve threat detection and response efficiency.
High volumes of malicious traffic overwhelm cloud-hosted applications and disrupt service availability. Poorly configured traffic filtering mechanisms increase downtime risk.
Attackers often combine DDoS with other intrusion techniques. Scalable mitigation tools and traffic monitoring strengthen availability protection.
Third-party vendors and software dependencies introduce indirect vulnerabilities into cloud environments. Compromised components can serve as hidden attack vectors.
Limited oversight of external integrations increases systemic risk. Vendor risk assessments and dependency audits enhance supply chain security.
Effective cloud security depends on layered controls that protect identities, configurations, workloads, and data across distributed environments.
Least privilege restricts users and services to only the permissions required for their roles. Limiting access boundaries reduces lateral movement and minimizes damage if credentials are compromised.
Multi-factor authentication adds an additional verification step beyond passwords. Stolen credentials alone become insufficient for unauthorized access.
Data encryption secures sensitive information both at rest and in transit. Strong cryptographic standards prevent interception and unauthorized data exposure.
Continuous monitoring provides real-time visibility into suspicious activity across cloud workloads. Early detection shortens breach dwell time and improves incident response effectiveness.
Configuration management ensures cloud settings remain aligned with security policies. Automated checks help prevent misconfigurations from becoming exploitable weaknesses.
Zero Trust enforces strict identity validation for every access request regardless of network location. Micro-segmentation limits internal threat propagation across cloud environments.
Regular audits identify outdated software, exposed services, and policy gaps. Proactive assessments reduce vulnerability exposure and strengthen overall resilience.
Cloud security posture assessment requires continuous evaluation of configurations, identity controls, network exposure, and workload integrity. Structured assessments help organizations detect weaknesses before attackers exploit them.
Risk assessment identifies critical assets, threat vectors, and potential impact across cloud environments. Prioritizing high-risk areas ensures remediation efforts focus on the most exploitable vulnerabilities.
Compliance mapping aligns security controls with regulatory frameworks and industry standards. Mapping policies against requirements reduces legal exposure and strengthens governance maturity.
Configuration review examines storage permissions, network rules, IAM roles, and encryption settings. Regular audits prevent misconfigurations from persisting unnoticed.
Penetration testing simulates real-world attack scenarios against cloud workloads and services. Controlled testing reveals hidden weaknesses that automated scans may overlook.
Log analysis evaluates authentication attempts, API activity, and resource changes across environments. Continuous log review improves anomaly detection and incident response readiness.
Incident readiness measures response plans, communication workflows, and recovery capabilities. Prepared response strategies minimize operational disruption during security events.
Cloud security strategy must balance risk reduction, operational agility, and compliance alignment across all service models.
Identity governance defines how users, roles, and permissions are created, monitored, and revoked. Strong access lifecycle management prevents privilege creep and unauthorized access.
Access visibility provides real-time insight into who can access which cloud resources. Continuous oversight reduces hidden exposure across multi-cloud environments.
Threat detection mechanisms identify suspicious behavior, abnormal login attempts, and unusual data transfers. Early alerts enable faster containment and limit breach impact.
Automation controls enforce consistent security policies across rapidly deployed workloads. Automated guardrails reduce human error and configuration drift.
Compliance alignment ensures security policies meet regulatory requirements and industry standards. Structured controls reduce legal risk and strengthen audit readiness.
Incident response planning defines containment, eradication, and recovery procedures during security events. Clear response workflows minimize downtime and operational disruption.
CloudSEK focuses on securing internet-facing cloud assets through External Attack Surface Management (EASM) and Digital Risk Protection (DRP). Its approach identifies external exposure rather than managing internal infrastructure controls.
BeVigil maps an organization’s digital footprint to detect misconfigured cloud storage, exposed APIs, and unmaintained assets. Infrastructure monitoring scans hundreds of security risks across Amazon Web Services, Microsoft Azure, and Alibaba Cloud to identify real-time vulnerabilities.
CloudSEK also monitors exposed API keys, tokens, and sensitive files leaked into public environments. Its XVigil platform tracks deep and dark web activity to detect stolen credentials and infrastructure exposure, supported by ISO/IEC 27017 cloud security compliance.
Misconfigured cloud storage and overly permissive IAM roles remain the leading causes of cloud data breaches. Incorrect access settings frequently expose sensitive information to unauthorized users.
Cloud providers secure the underlying infrastructure, but customers remain responsible for securing data, identities, and configurations. Misunderstanding this shared model often leads to preventable vulnerabilities.
Small and mid-sized organizations are frequently targeted due to weaker security controls. Automated scanning tools allow attackers to exploit exposed services regardless of company size.
Continuous monitoring should operate daily, with formal security reviews conducted at least quarterly. Regular audits help detect configuration drift and emerging vulnerabilities early.
Encryption protects data confidentiality but does not eliminate risks from misconfiguration or compromised credentials. Strong identity management and monitoring controls must complement encryption policies.
