🚀 CloudSEK becomes first Indian origin cybersecurity company to receive investment from US state fund
Read more
A Cyber Threat Intelligence (CTI) platform is a system that collects and analyzes threat data to produce actionable intelligence for cybersecurity teams. It brings together inputs from threat intelligence feeds, open-source intelligence (OSINT), and internal security logs into a unified, structured view of risks.
Threat data becomes useful when it is connected, not isolated. CTI platforms link entities such as threat actors, Indicators of Compromise (IoCs), malware signatures, and attack techniques to reveal patterns and relationships that support faster and more accurate decision-making within Security Operations Centers (SOC).
Rising breach costs and increasingly complex attack methods make early detection critical for organizations. IBM’s Cost of a Data Breach Report states that the global average cost of a data breach reached USD 4.4 million, reinforcing the need for CTI platforms that improve visibility, reduce response time, and strengthen overall cybersecurity resilience.
The Cyber Threat Intelligence lifecycle consists of six connected stages that continuously transform raw threat data into actionable intelligence.

Intelligence requirements are defined based on business risks, critical assets, and security priorities. Focus is placed on high-impact threats such as ransomware, phishing, and targeted attacks to ensure intelligence efforts remain relevant.
Threat data is gathered from internal systems and external environments to expand visibility. Logs, endpoint telemetry, and external intelligence sources together provide broader coverage and reduce blind spots.
Raw data is cleaned and structured into consistent formats to improve usability. Duplicate, irrelevant, and low-confidence data is removed, while normalization ensures consistency for further analysis.
Processed data is examined to identify patterns, attacker behavior, and potential risks. Correlation across signals and mapping to frameworks like MITRE ATT&CK helps explain how threats operate.
Actionable intelligence is delivered to the appropriate stakeholders in formats suited to their needs. Technical teams receive detailed alerts, while leadership gains summarized insights to support decision-making.
Outcomes from each cycle are evaluated to identify gaps and improve future intelligence efforts. Continuous refinement ensures the lifecycle remains aligned with evolving threats and organizational priorities.
Platforms built for handling large volumes of threat data rely on CTI to make that information usable for real-world security decisions.
Information flows in from a mix of external providers, internal systems, and underground sources where threat activity often surfaces first. This continuous stream keeps teams aware of new risks as they emerge, rather than after damage is done.
Raw indicators on their own offer limited value until they are placed in context. Enrichment adds background such as related infrastructure, historical activity, and known associations, making each signal easier to interpret and act on.
Isolated data points rarely reveal the full picture of an attack. By linking related events and indicators, patterns begin to surface, allowing teams to trace how an intrusion unfolds across systems.
Repetitive tasks such as data ingestion, analysis, and alert generation are automated to reduce manual workload. Integration with SOAR systems enables faster and more consistent incident response.
Complex data becomes easier to work with when it is presented visually. Structured views allow teams to quickly understand what is happening, where attention is needed, and how threats are evolving over time.
Timely notifications ensure that critical issues are not missed during ongoing operations. Reports provide a clearer record of events, helping teams investigate incidents and communicate findings across the organization.
CTI platforms rely on different types of threat intelligence to cover both strategic risks and real-time technical threats.
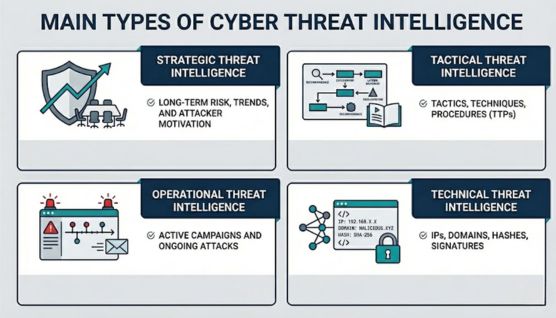
Strategic intelligence focuses on long-term risks, industry trends, and the broader threat landscape affecting an organization. Leadership teams depend on it to understand how cyber threats evolve and where security investments should be directed.
Insights from this layer highlight patterns such as rising ransomware activity across specific sectors or shifts driven by geopolitical events. These signals guide decisions around security policies, budget allocation, and overall risk management.
Tactical intelligence explains how attacks are carried out by analyzing the tactics, techniques, and procedures (TTPs) used by threat actors. Security teams use it to break down common attack methods and strengthen defenses accordingly.
Recurring patterns such as phishing campaigns, credential theft, or lateral movement techniques become easier to identify with this intelligence. Detection rules and defensive controls are then refined to reduce exposure to similar attack paths.
Operational intelligence provides detailed insights into specific threats, including timing, targets, and attacker intent. It plays a direct role in handling active or emerging threats.
Ongoing campaigns, targeted assets, and potential entry points can be tracked more effectively through this intelligence. Coordination between monitoring and response teams improves as a result, especially within Security Operations Centers (SOC).
Technical intelligence focuses on Indicators of Compromise (IoCs) such as IP addresses, domain names, file hashes, and malware signatures. These data points are directly used by security tools to detect and block threats.
Integration with systems like SIEM and firewalls allows these indicators to trigger automated responses. Faster containment becomes possible without relying solely on manual investigation.
Read More: Types of Cyberthreat Intelligence (CTI)
Real-world incidents show how intelligence becomes useful when early signals are connected before threats fully develop.
Third-party exposure often appears outside direct visibility through leaked credentials, misconfigured cloud assets, or external infrastructure signals. These early indicators reveal weaknesses before attackers gain full access.
CloudSEK identified an Oracle Cloud incident where 6 million records were exfiltrated, impacting over 140,000 tenants, showing how a single supply chain weakness can scale across multiple organizations.
Attack campaigns reuse domains, hosting environments, and delivery patterns across targets. Detecting these links early allows teams to block malicious infrastructure before it reaches users.
The UK National Cyber Security Centre (NCSC) reported in 2025 that over 1.2 million phishing campaigns were taken down, with 79% mitigated within 24 hours, demonstrating the impact of early intelligence.
Ransomware follows a sequence that includes initial access, lateral movement, and data exfiltration. Identifying these stages early allows organizations to stop attacks before encryption or data loss occurs.
The UK NCSC confirmed in 2025 that ransomware remains one of the most disruptive threats to critical infrastructure, requiring faster detection to reduce operational impact.
Security teams handle large volumes of alerts, but not all signals carry equal risk. Intelligence-driven prioritization connects related events and highlights what requires immediate action.
The World Economic Forum reported in 2026 that 73% of individuals experienced cyber-enabled fraud in 2025, reflecting the scale of threats and the need for faster, context-based decisions.
Leaked credentials appear in breach datasets and underground forums before they are actively exploited. Detecting them early allows organizations to secure accounts before unauthorized access occurs.
Google Cloud’s Cybersecurity Forecast 2025 identifies credential abuse and identity-based attacks as leading initial access vectors, reinforcing the need for early detection and response.
Understanding and responding to threats becomes more effective with Cyber Threat Intelligence, but results depend on how well it is implemented and operationalized.
Threat intelligence originates from multiple environments where attacker activity, vulnerabilities, and exposure signals continuously emerge across digital ecosystems.
Websites, forums, blogs, and code repositories frequently expose vulnerabilities, leaked credentials, and misconfigured assets. Security disclosures, developer commits, and exposed APIs often reveal weaknesses before attackers actively exploit them, making these sources critical for early-stage visibility.
Dark web forums, encrypted communities, and illicit marketplaces host stolen data, access credentials, and discussions around active or planned attacks. Monitoring these environments provides insight into attacker intent, emerging campaigns, and the circulation of compromised assets long before public awareness.
Logs, endpoint activity, network traffic, and authentication records reflect real interactions within an organization’s infrastructure. Unusual behavior such as privilege escalation, lateral movement, or unauthorized access attempts signals active threats that originate from both external and insider activity.
Curated intelligence from security providers aggregates data collected from global sensors, honeypots, and research operations. These feeds include known malicious infrastructure, threat signatures, and vulnerability intelligence that extend visibility beyond what internal systems can observe.
Published research, threat reports, and vulnerability databases document newly discovered weaknesses and exploitation techniques. Details around CVEs, proof-of-concept exploits, and patch timelines provide context on how attackers may weaponize vulnerabilities in real environments.
Information exchanged across industry groups, ISACs, and government-led initiatives strengthens collective awareness of coordinated attacks. Shared intelligence highlights sector-specific threats, large-scale campaigns, and adversary trends that may not be visible within a single organization.
Successful CTI strategies require aligning threat intelligence with business risk, operational workflows, and decision-making processes.
Clear objectives determine what type of intelligence is required and how it will be used. Goals should align with business risks, critical assets, and the threat landscape relevant to the organization.
Relevant data sources must be selected based on the type of threats being monitored. External signals, internal telemetry, and industry-specific intelligence should be prioritized to ensure meaningful coverage.
Integration with platforms such as SIEM and SOAR ensures intelligence flows directly into detection and response workflows. Connected systems reduce delays between identifying a threat and taking action.
Defined processes for processing, enriching, and correlating threat data improve consistency and accuracy. Structured workflows help teams move from raw data to actionable intelligence without confusion.
Not all threats require the same level of attention, making prioritization essential. Risk-based scoring helps focus resources on high-impact threats that affect critical systems or assets.
Automation reduces manual effort in data collection, enrichment, and alert handling. Repetitive tasks can be handled efficiently, allowing analysts to focus on investigation and decision-making.
Threat environments evolve, requiring constant adjustment of intelligence strategies. Feedback from incidents, new data sources, and changing risks should be used to improve accuracy and effectiveness over time.
CloudSEK collects cyber threat intelligence data by continuously monitoring external environments and processing data through an AI-driven intelligence pipeline.
Surface, deep, and dark web environments are continuously scanned to identify early signals of threats. Activity across underground forums, marketplaces, and encrypted channels such as Telegram and IRC reveals credential leaks, planned attacks, and data exposure before incidents become active.
Publicly available data across news platforms, social media, blogs, and paste sites is tracked to identify emerging risks and exposed information. Code repositories such as GitHub and Bitbucket are also scanned for accidental leaks of API keys, source code, and sensitive assets.
Mobile applications are analyzed using CloudSEK’s BeVigil engine to detect insecure dependencies, hardcoded secrets, and exposed configurations. This layer expands visibility into risks originating from mobile ecosystems and third-party applications.
Malicious infrastructure and technical indicators such as IP addresses, domains, file hashes, and network signals are continuously gathered. These data points help identify active threats and map attacker-controlled environments.
Collected data is standardized and processed using CloudSEK’s ThreatMeter AI model to identify patterns and reduce noise. Correlation across signals helps detect relationships, map threats to business assets, and predict potential initial attack vectors.
Security analysts review high-risk findings to improve accuracy and reduce false positives. Verified intelligence is delivered through dashboards or integrated into systems like Splunk and Cortex XSOAR for immediate action.
A continuously updated data lake maintains records of past breaches, leaks, and threat activity. Historical context strengthens analysis by linking new signals with previously observed patterns.
CloudSEK stands out by combining predictive intelligence, external risk visibility, and AI-driven correlation into a single unified platform.
Cyber Threat Intelligence (CTI) platforms shift security from reactive monitoring to intelligence-driven decision-making. Visibility across attacker behavior, external exposure, and evolving threat patterns allows organizations to act earlier and with greater precision.
Strong platforms combine data coverage, contextual understanding, and automation to reduce noise and highlight what truly matters. As threat environments continue to expand, the ability to connect signals into meaningful intelligence becomes a critical part of maintaining long-term security resilience.
CTI platforms reduce the gap between raw threat data and actionable insight. Security teams gain clearer visibility into attacker behavior, external risks, and emerging threats without manually correlating data.
Pre-processed and enriched intelligence removes the need to analyze isolated signals. Faster correlation of patterns allows teams to identify threats earlier in the attack lifecycle.
External visibility reveals risks that exist outside internal systems, such as exposed credentials, leaked data, and attacker discussions. Early awareness of these signals helps prevent threats before they reach the organization.
Contextual intelligence provides details about attack methods, infrastructure, and behavior. Response teams use this information to investigate incidents more efficiently and take targeted actions.
Standalone usage provides visibility, but integration with systems like SIEM and SOAR improves response speed and automation. Connected environments allow intelligence to trigger real-time actions.
Modern platforms focus on correlation, context, and prediction rather than simple data aggregation. Intelligence is structured around risk, behavior, and relevance instead of isolated indicators.
