🚀 أصبحت CloudSek أول شركة للأمن السيبراني من أصل هندي تتلقى استثمارات منها ولاية أمريكية صندوق
اقرأ المزيد
منصة Threat Intelligence Platform (TIP) هي نظام يستخدم لجمع وتنظيم بيانات التهديدات من مصادر مختلفة حتى تتمكن فرق الأمان من فهم التهديدات المهمة بالفعل. بدلاً من العمل مع التنبيهات المتناثرة أو الخلاصات الأولية، يقوم TIP بتحويل تلك البيانات إلى ذكاء واضح وقابل للاستخدام من أجل استجابة أسرع.
تعتمد فرق الأمان على TiPs لربط المؤشرات والجهات الفاعلة في مجال التهديد ونقاط الضعف وبيانات التهديدات الخارجية بأدوات مثل SIEM و SOAR في سير عمل واحد. يسمح ذلك بإثراء بيانات التهديدات وربطها وتحديد أولوياتها بحيث تركز الفرق فقط على الأنشطة عالية المخاطر بدلاً من الضوضاء.
زادت أهمية TiPs مع زيادة سرعة التهديدات وصعوبة تتبعها، حيث أفاد تقرير المنتدى الاقتصادي العالمي للأمن السيبراني لعام 2026 أن 87٪ من المؤسسات ترى نقاط الضعف الناشئة القائمة على التكنولوجيا كخطر كبير. كما سجل ENISA Threat scape 2025 ما يقرب من 4900 حادث كبير، مما يوضح مدى سرعة انتشار التهديدات وسبب الحاجة إلى منصات استخبارات منظمة.
تعمل منصة Threat Intelligence Platform من خلال تحويل بيانات التهديدات المتناثرة إلى ذكاء منظم يمكن لفرق الأمان استخدامه مباشرة في عمليات سير عمل الكشف والاستجابة.
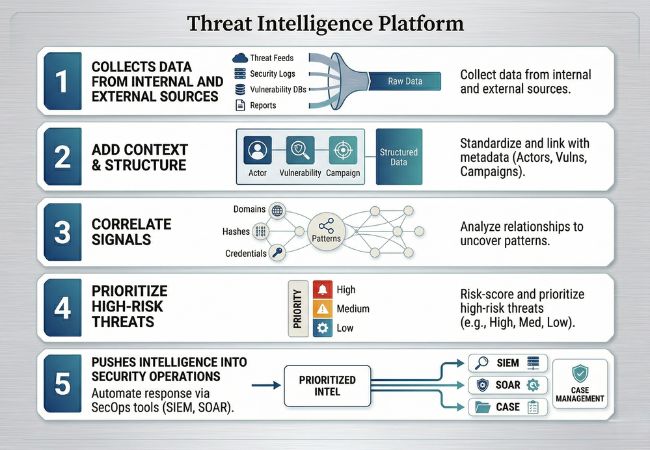
تبدأ العملية بجمع البيانات من مصادر متعددة، مثل خلاصات التهديدات وسجلات الأمان وتقارير البرامج الضارة وقواعد بيانات الثغرات الأمنية وقنوات المراقبة الخارجية. تبني هذه المجموعة الواسعة من البيانات الأساس، ولكن في هذه المرحلة، تظل المعلومات خام ويصعب تفسيرها.
يتم بعد ذلك توحيد البيانات المجمعة وإثرائها بحيث يمكن ربط المؤشرات بنقاط الضعف والجهات الفاعلة في مجال التهديد والحملات والأصول المتأثرة. وجدت M-Trends 2025 من Mandiant أن عمليات الاستغلال تمثل 33٪ من ناقلات العدوى الأولية وبيانات الاعتماد المسروقة بنسبة 16٪، وهو ما يسلط الضوء على سبب ضرورة السياق لفهم كيفية عمل التهديدات فعليًا.
بمجرد إضافة السياق، تربط المنصة المؤشرات ذات الصلة للكشف عن الأنماط عبر أحداث متعددة. تسمح هذه الخطوة للمحللين بمعرفة ما إذا كانت النطاقات أو التجزئات أو تسريبات بيانات الاعتماد أو الثغرات الأمنية المستغلة جزءًا من نفس النشاط المنسق.
بعد الارتباط، يتم تصنيف الذكاء بناءً على الشدة والملاءمة والتعرض بحيث ينتقل الانتباه إلى الأمور الأكثر أهمية. وهذا يقلل من الضوضاء ويضمن تركيز فرق الأمن على التهديدات التي لها تأثير تشغيلي حقيقي بدلاً من الإشارات المعزولة منخفضة المخاطر.
ثم تتم مشاركة المعلومات ذات الأولوية مع أنظمة مثل SIEM وSOAR وأدوات إدارة الحالات، حيث تدعم إجراءات الكشف والتنبيه والاستجابة. تعكس التحديثات المستمرة لكتالوج الثغرات الأمنية المستغلة المعروفة من CISA في عام 2026 مدى سرعة تطور التهديدات النشطة، مما يجعل من الضروري أن تنتقل الذكاء مباشرة إلى عمليات سير العمل التشغيلية.
تتعامل منصات استخبارات التهديدات مع طبقات ذكاء متعددة استنادًا إلى كيفية استخدام المعلومات عبر صنع القرار والتخطيط الدفاعي والعمليات في الوقت الفعلي.
يركز الذكاء الاستراتيجي على أنماط المخاطر طويلة الأجل واتجاهات الصناعة والدوافع المعادية التي تؤثر على التخطيط الأمني على المستوى التنظيمي. تساعد هذه الطبقة القيادة على فهم أين تتطور التهديدات وتدعم القرارات المتعلقة بالاستثمار والسياسة وإدارة المخاطر.
تركز الاستخبارات التكتيكية على سلوك المهاجم، بما في ذلك التقنيات والأدوات والأساليب المستخدمة أثناء الاختراقات. تستخدم فرق الأمان هذا لتكييف الدفاعات بناءً على كيفية تنفيذ الهجمات بدلاً من الاعتماد فقط على المؤشرات الثابتة.
توفر المعلومات التشغيلية رؤية للتهديدات النشطة، وتوضح كيفية تطور الهجوم عبر الأنظمة والوقت. يسمح هذا للمحللين بالتحقيق في الحوادث وتتبع حركة الخصم والرد قبل تصاعد التأثير.
يتضمن الذكاء الفني مؤشرات محددة مثل عناوين IP والمجالات وتجزئات الملفات والتوقيعات المستخدمة داخل أنظمة الكشف. تدعم هذه المؤشرات الاكتشاف الآلي والحظر ولكنها تتطلب سياقًا من طبقات أخرى لتجنب الضوضاء والإيجابيات الكاذبة.
تصف القدرات الأساسية كيفية انتقال إشارات الأمان من المدخلات المتناثرة إلى الذكاء المنظم الذي يدعم الاكتشاف والتحقيق والاستجابة عبر سطح الهجوم.
تنشأ مدخلات الأمان من السجلات، والقياس عن بُعد للشبكة، والكشف عن الثغرات الأمنية، وتحليل البرامج الضارة، ومصادر الاستخبارات الخارجية، ولكنها تظل مجزأة عبر الأنظمة. يعمل الدمج على جلب هذه الإشارات إلى بيئة مشتركة، مما يسمح بالرؤية عبر الأصول والمستخدمين ونقاط التعرض الخارجية.
يمكن أن تتوافق تسريبات بيانات الاعتماد التي تم تحديدها خارج الشبكة مع سلوك تسجيل الدخول غير الطبيعي داخل الأنظمة الداخلية. تكشف هذه الإشارات معًا عن متجه وصول مشترك بدلاً من نشاط غير ذي صلة.
تفتقر الإشارات الأولية إلى المعنى حتى يتم ربطها بسمات مثل التعرض للأصول، وأهمية الضعف، والبنية التحتية للخصم، والأنماط السلوكية. يحدد تخطيط السياق مكان وضع كل إشارة ضمن مسار الهجوم وكيفية ارتباطها بالأنشطة الأخرى.
يمثل عنوان IP المرتبط بالبنية التحتية للأوامر والتحكم نشاطًا ضارًا يتم التحكم فيه، بينما يظل عنوان IP غير المعروف غير مؤكد. إن ربط الإشارات بالبنية التحتية والسلوك يوضح النية والتأثير التشغيلي.
تكتسب الملاحظات الفردية قيمة بمجرد إنشاء العلاقات عبر الوقت والأنظمة والإجراءات. يعرض الربط التسلسلات التي تعكس كيفية تقدم نشاط التسلل بدلاً من عرض الأحداث المعزولة.
يشكل الوصول إلى بيانات الاعتماد متبوعًا بتصاعد الامتيازات والحركة الجانبية تقدمًا واضحًا بمجرد توصيل الأحداث. وبدون الربط، تبدو كل مرحلة منفصلة وتفقد المعنى الاستقصائي.
لا تحمل كل إشارة وزنًا متساويًا، مما يجعل التقييم ضروريًا قبل الاستجابة. يأخذ تصنيف المخاطر في الاعتبار مستوى التعرض وحرجية الأصول ومرحلة تقدم الهجوم لتحديد ما يتطلب اهتمامًا فوريًا.
يمثل النشاط الذي يستهدف الأنظمة التي تواجه الإنترنت مخاطر أعلى مقارنة بالسلوك المماثل في البيئات الخاضعة للرقابة. يضمن تحديد الأولويات تركيز الجهد على السيناريوهات ذات التأثير التشغيلي الحقيقي.
يجب أن تنتقل الإحصاءات عبر أنظمة الكشف وسير عمل المحلل وعمليات الاستجابة للحفاظ على الاتساق. يضمن التوزيع أن الأنماط المحددة تؤثر على كيفية اكتشاف نشاط مماثل والتعامل معه في مكان آخر.
يمكن تطبيق المعرفة بالبنية التحتية للخصم عبر أنظمة متعددة لاكتشاف النشاط المتكرر على الفور. هذا يمنع التحقيق المكرر ويحسن تنسيق الاستجابة.
تؤدي معالجة كميات كبيرة من الإشارات يدويًا إلى حدوث تأخيرات وعدم تناسق عبر عمليات سير العمل. تدعم الأتمتة المعالجة المستمرة من خلال التصنيف ووضع العلامات وإنشاء التنبيهات وتشغيل الاستجابة.
يمكن للمؤشرات التي تم تحديدها حديثًا الانتقال مباشرةً إلى عمليات سير عمل الاكتشاف والاستجابة دون انتظار الإجراء اليدوي. تعمل الحركة السريعة من الملاحظة إلى العمل على تقليل وقت التعرض.
يصبح الذكاء جاهزًا بمجرد اتصاله بأنظمة الكشف والاستجابة بدلاً من البقاء معزولًا. يسمح التكامل للمخرجات المهيكلة بالتأثير على المراقبة والتنبيه والإجراءات الآلية عبر حزمة الأمان.
يمكن للإشارات التي تتم معالجتها داخل النظام الأساسي تشغيل التنبيهات في SIEM أو بدء سير عمل الاستجابة في SOAR. هذا يخلق دورة مستمرة حيث يغذي الذكاء العمليات والعمليات تولد ذكاء جديد.
تعتمد الصناعات ذات التعرض الخارجي العالي وأصول البيانات القيمة والاستهداف المستمر بشكل كبير على الذكاء الأمني المتقدم، حيث تساعد منصة معلومات التهديدات على اتخاذ قرارات أسرع وأكثر استنارة.
تعمل المؤسسات المالية في بيئة تتشكل من الاحتيال والتصيد الاحتيالي وإساءة استخدام بيانات الاعتماد ومحاولات الاستيلاء على الحسابات. تساعد المعلومات فرق الأمان على تتبع البنية التحتية الضارة ومراقبة انتحال هوية العلامة التجارية وتحديد التهديدات التي تستهدف الخدمات التي تواجه العملاء وأنظمة الدفع والقنوات المصرفية الرقمية.
تدير مؤسسات الرعاية الصحية الأنظمة السريرية وسجلات المرضى وتطبيقات الطرف الثالث والبنية التحتية المتصلة التي لا يمكنها تحمل التعطيل المطول. تدعم المعلومات إمكانية الرؤية المبكرة لنشاط برامج الفدية والسجلات المسربة والأصول المكشوفة وحملات التهديد التي يمكن أن تؤثر على تقديم الرعاية بالإضافة إلى أمن البيانات.
تواجه بيئات البيع بالتجزئة والتجارة الإلكترونية ضغوطًا مستمرة من النطاقات المزيفة والاحتيال في المعاملات وحشو بيانات الاعتماد وإساءة الاستخدام التي تستهدف حسابات العملاء. تضيف المعلومات قيمة من خلال الكشف عن أصول التصيد الاحتيالي ومراقبة انتحال الهوية ومساعدة الفرق على اكتشاف النشاط الذي يؤثر على واجهات المتاجر وتدفقات الدفع وثقة المستخدم.
تعد الأنظمة الحكومية أهدافًا متكررة للتجسس وتعطيل الخدمة والهجمات ضد البنية التحتية العامة. تمنح المعلومات لفرق القطاع العام رؤية أوسع لنشاط الخصم والأنظمة المكشوفة والمخاطر الخارجية التي يمكن أن تؤثر على خدمات المواطنين والعمليات الداخلية والأصول الرقمية على المستوى الوطني.
تقوم شركات التكنولوجيا وموفرو SaaS بإدارة الأصول السحابية وهويات المستخدمين وواجهات برمجة التطبيقات والتطبيقات التي تواجه الإنترنت والتي تتعرض باستمرار لسوء الاستخدام. تساعد المعلومات على ربط الأنشطة المشبوهة عبر هذه البيئات، مما يسهل اكتشاف إساءة استخدام الحساب واستهداف البنية التحتية والتهديدات المرتبطة بتسليم البرامج أو الوصول إلى الخدمة.
غالبًا ما تتعامل الشركات ذات العلامات التجارية والنطاقات والشركات التابعة والبائعين والأصول العامة مع مساحة هجوم أوسع من المؤسسات الصغيرة. تعمل المعلومات على تحسين الرؤية عبر هذه التبعيات الخارجية وتساعد فرق الأمن على تحديد المخاطر المتعلقة بالأصول المكشوفة والبيانات المسربة وتعرض الموردين واستطلاع الخصم.
تحتاج المؤسسات إلى منصة معلومات التهديدات لتحديد التهديدات ذات الصلة ببيئتها، وتقليل وقت التحقيق، ودعم الاستجابات الأسرع والقائمة على المخاطر.
تتعامل فرق الأمان مع النشاط المستمر عبر نقاط النهاية وحركة مرور الشبكة وسلوك المستخدم والتعرض الخارجي، مما ينتج عددًا كبيرًا من التنبيهات والأحداث. حلل تقرير تحقيقات خرق البيانات لعام 2025 الصادر عن Verizon أكثر من 22,000 حادث، وسلط الضوء على كيفية تعامل العمليات الأمنية مع نشاط أكثر بكثير مما يمكن مراجعته يدويًا.
تظهر بيانات الأمان بتنسيقات متعددة، بما في ذلك الخلاصات المنظمة والسجلات والتقارير والمصادر غير المهيكلة مثل رسائل البريد الإلكتروني أو الإفصاحات الخارجية. تجعل الاختلافات في التنسيق والبنية من الصعب دمج هذه البيانات وتحليلها بدون نظام مصمم لتطبيعها وتنظيمها.
يشمل نشاط الهجوم التصيد الاحتيالي وإساءة استخدام بيانات الاعتماد وتسليم البرامج الضارة وبرامج الفدية و محاولات الحرمان من الخدمة، كل منها يتطلب أساليب كشف وتحليل مختلفة. هذا الاختلاف يجعل من الصعب تطبيق طريقة واحدة للتحقيق في جميع التهديدات.
أعداد كبيرة من المؤشرات، مثل المجالات وعناوين IP وتجزئات الملفات و أوراق اعتماد مكشوفة، تظهر عبر البيئات الداخلية والخارجية. وبدون الارتباط وتحديد الأولويات، يصبح من الصعب تحديد المؤشرات المرتبطة بنشاط بالهجوم والتي تتطلب اتخاذ إجراءات فورية.
غالبًا ما يحدث تقدم الهجوم في غضون أطر زمنية قصيرة، خاصة بعد الحصول على الوصول الأولي. يؤدي التأخير في تحديد النشاط ذي الصلة إلى زيادة احتمالية الحركة الجانبية أو الوصول إلى البيانات أو تعطيل النظام. تعرف على كيفية حماية وصولك الأولي.
لا يمكن لفرق الأمان الاعتماد فقط على التنبيهات التي يتم إنشاؤها بعد حدوث النشاط لأن إشارات المرحلة المبكرة غالبًا ما تظهر خارج أنظمة المراقبة التقليدية. أدوات التحليل القائمة على الذكاء تساعد في تحديد التعرض وإعداد المهاجم والمؤشرات المبكرة قبل أن تتطور إلى حوادث كاملة.
يعتمد الاختيار على مدى ملاءمة الذكاء لسير العمل الأمني الحقيقي، وتحسين وضوح التحقيق، ودعم اتخاذ قرارات أسرع أثناء الحوادث النشطة.
يجب أن تمتد التغطية عبر المعلومات مفتوحة المصدر (OSINT) وبيانات الاختراق والموجزات التجارية و مراقبة الويب المظلم لذلك يكون نشاط الخصم خارج الأنظمة الداخلية مرئيًا. غالبًا ما تؤخر النقاط العمياء في المصادر الخارجية الوعي بتسريبات بيانات الاعتماد والبنية التحتية للتصيد الاحتيالي والحملات الناشئة.
لا تكتسب المؤشرات معنى إلا بعد أن يربطها الإثراء مؤشرات التسوية (IOCs)، التكتيكاتوالتقنيات والإجراءات (TTPs)، وأهمية الأصول، والسلوك الملحوظ. يقلل السياق القوي من الحاجة إلى التحقق اليدوي ويساعد المحللين على فهم كيفية ملاءمة النشاط لسيناريو الهجوم بسرعة.
يجب ربط الإشارات ذات الصلة عبر الملاحظات للكشف عما إذا كان النشاط يمثل تدخلاً منسقًا أو أحداثًا غير ذات صلة. يسمح الارتباط عند هذا المستوى بالتحقيق بالانتقال من التنبيهات المعزولة إلى فهم تقدم الهجوم.
يجب أن يتطابق الذكاء مع كيفية حدوث العمل داخل مركز العمليات الأمنية (SOC)، حيث يتم إجراء التحقيق والفرز والاستجابة بشكل مستمر. تؤدي أي فجوة بين مخرجات الذكاء وسير العمل التشغيلي إلى إبطاء الاستجابة أثناء اللحظات الحرجة.
تؤدي معالجة كميات كبيرة من الإشارات يدويًا إلى حدوث تأخيرات وعدم تناسق عبر عمليات سير العمل. يجب أن تدعم الأتمتة داخل TIP الإثراء والتصنيف ومعالجة التنبيهات حتى يقضي المحللون وقتًا أطول في التحقيق مقارنة بمعالجة المدخلات.
غالبًا ما يبدأ نشاط التهديد خارج البيئات الخاضعة للرقابة، مما يجعل الرؤية في الأصول المكشوفة أمرًا ضروريًا. قدرات مثل الحماية من المخاطر الرقمية (DRP) وتساعد مراقبة سطح الهجوم على تحديد المخاطر قبل استخدامها في الهجمات النشطة.
يجب أن يدعم الذكاء الاكتشاف بشكل مباشر من خلال تغذية المخرجات المهيكلة في أنظمة مثل أداة اكتشاف نقطة النهاية، حيث يتم تشغيل التنبيهات وإجراءات الاستجابة. بدون هذا الاتصال، تظل المعلومات منفصلة عن عمليات الأمان في الوقت الفعلي.
غالبًا ما تفتقر فرق الأمان إلى الرؤية فيما يتعلق بتهديدات المرحلة المبكرة التي تنشأ خارج الأنظمة الداخلية، حيث تظهر إشارات مثل بيانات الاعتماد المكشوفة والبنية التحتية للتصيد الاحتيالي واستطلاع الخصم قبل الوصول. يعالج CloudSek هذا من خلال التركيز على الذكاء الخارجي ورسم خرائط كيفية ارتباط هذه الإشارات بنقاط دخول الهجوم الحقيقية عبر سطح هجوم المؤسسة.
بدلاً من معالجة الإشارات بشكل مستقل، تربط المنصة النشاط الخارجي بمتجهات الهجوم الأولي (IAVs)، مما يساعد الفرق على فهم كيفية انتقال التهديدات من التعرض إلى الاستغلال. يتم دمج إمكانات مثل الحماية من المخاطر الرقمية (DRP) ومراقبة سطح الهجوم وتتبع عوامل التهديد مع الارتباط القائم على الذكاء الاصطناعي لربط نقاط الضعف والبنية التحتية وسلوك الخصم في وجهة نظر استقصائية واحدة.
يسمح هذا النهج لفرق الأمن باكتشاف المخاطر في وقت مبكر من خلال تحديد الظروف القابلة للاستغلال، وتتبع استعداد الخصم، وتحديد أولويات التهديدات بناءً على التعرض الحقيقي بدلاً من الإشارات المعزولة. من خلال ربط الذكاء الخارجي بسير العمل التشغيلي، يتيح CloudSek استجابة أسرع واتخاذ قرارات أكثر دقة عبر عمليات الأمان.
توفر خلاصة التهديدات معلومات أولية، مثل المؤشرات أو التنبيهات، دون سياق أو ترتيب أولويات. يقوم TIP بمعالجة خلاصات متعددة وإثراء البيانات وربط الإشارات بحيث يمكن استخدامها في التحقيق والاستجابة.
نعم، من خلال تحليل الإشارات الخارجية مثل الأصول المكشوفة وبيانات الاعتماد المسربة ونشاط الخصم، يمكن لـ TIP تسليط الضوء على المخاطر قبل استخدامها في الهجمات النشطة. يسمح هذا لفرق الأمن بالتصرف خلال المراحل المبكرة بدلاً من الرد بعد التسوية.
لا يحل TIP محل أنظمة الكشف أو الاستجابة ولكنه يدعمها من خلال تحسين جودة الذكاء الذي تعتمد عليه. وهي تعمل كطبقة مركزية تربط المعلومات وتثريها عبر بيئة الأمان.
يستخدم محللو الأمن وفرق استخبارات التهديدات والمستجيبون للحوادث TIP للتحقيق في النشاط والتحقق من صحة التنبيهات وتتبع التهديدات المستمرة. يتم استخدامه بشكل شائع في بيئات العمليات الأمنية حيث تتطلب المراقبة والتحليل المستمر.
من خلال ربط الإشارات وإضافة السياق تلقائيًا، يزيل TIP الحاجة إلى توصيل المؤشرات يدويًا عبر مصادر متعددة. وهذا يسمح للمحللين بالتركيز بشكل مباشر على فهم التهديدات والاستجابة لها.
نعم، لأن الأتمتة وتحديد الأولويات تقلل الجهد المطلوب لتحليل كميات كبيرة من الإشارات. يمكن للفرق الصغيرة التركيز على الأنشطة عالية المخاطر بدلاً من مراجعة كل تنبيه يدويًا.
يقلل TIP من الإيجابيات الكاذبة عن طريق إثراء الإشارات وربطها قبل وصولها إلى المحللين، وتصفية الأنشطة غير ذات الصلة أو منخفضة المخاطر. هذا يحسن الدقة في الكشف ويمنع جهود التحقيق غير الضرورية.
نعم، تساعد المعلومات المنظمة والتحقيقات المتعقبة في إنشاء تقارير حول التهديدات والحوادث وإجراءات الاستجابة. هذا يدعم متطلبات التدقيق ويوفر رؤية لكيفية تحديد المخاطر والتعامل معها.
