🚀 A CloudSEK se torna a primeira empresa de segurança cibernética de origem indiana a receber investimentos da Estado dos EUA fundo
Leia mais
Um ataque de Kerberoasting é um roubo de credenciais e técnica pós-exploração que visa senhas de contas de serviço em ambientes Microsoft Active Directory explorando o protocolo de autenticação Kerberos. O invasor solicita tíquetes de serviço Kerberos legítimos e extrai dados de senha criptografados desses tíquetes. O ataque não exige acesso de administrador para começar.
O Kerberoasting se concentra em contas de serviço vinculadas a nomes principais de serviços (SPNs). Essas contas geralmente executam aplicativos essenciais, como bancos de dados, servidores web ou serviços de backup. Os dados criptografados do ticket podem ser decifrados offline usando métodos de força bruta. O objetivo principal é escalação de privilégios (obtendo acesso e controle de alto nível) dentro do domínio do Windows após recuperar a senha da conta de serviço.
De acordo com a pesquisa de ameaças da Microsoft, os ataques baseados no Kerberos, como o Kerberoasting, são responsáveis por uma parte significativa da atividade local de roubo de credenciais do Active Directory. A Microsoft relatou observar milhares de solicitações suspeitas de tíquetes de serviço Kerberos diariamente em ambientes corporativos, destacando a frequência com que os atacantes tentam abusar dos mecanismos de autenticação Kerberos.
A autenticação Kerberos é um protocolo de segurança baseado em tickets usado no Microsoft Active Directory para verificar identidades de usuários e serviços sem enviar senhas pela rede. Ele se baseia em tíquetes criptografados emitidos por uma autoridade confiável chamada Centro de Distribuição de Chaves (KDC). Esse sistema permite que os usuários acessem os recursos da rede com segurança após fazer login uma vez.
O processo de autenticação começa quando um usuário solicita um Ticket Granting Ticket (TGT). O TGT prova a identidade do usuário para o controlador de domínio. Quando o usuário precisa acessar um serviço específico, como um banco de dados ou aplicativo web, o sistema emite um ticket do Ticket Granting Service (TGS) para esse serviço. Cada serviço é identificado por um nome principal de serviço (SPN), que vincula o serviço a uma conta específica. As contas de serviço geralmente têm senhas de longa duração, o que as torna alvos atraentes em ataques baseados em Kerberos.
Um ataque Kerberoasting funciona solicitando tíquetes de serviço legítimos do Kerberos e quebrando seu conteúdo criptografado off-line para recuperar senhas de contas de serviço. O invasor usa a funcionalidade padrão do domínio para obter dados do ticket e, em seguida, quebra a senha fora da rede.
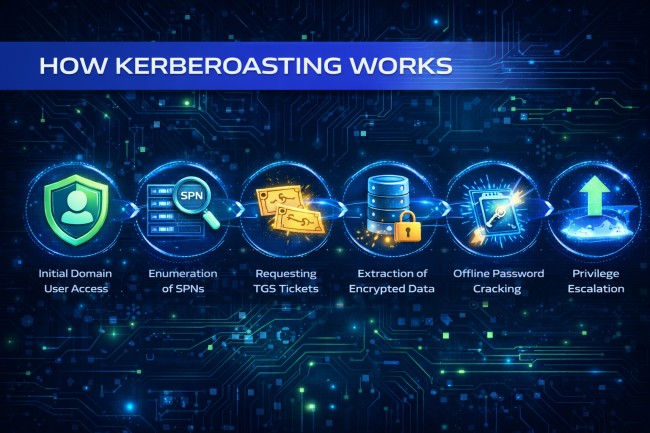
Aqui está o processo passo a passo do ataque Kerberoasting:
O atacante/ator de ameaça primeiro obtém acesso a uma conta de usuário de domínio regular. Esse acesso pode vir de phishing, reutilização de senhas ou outra forma de comprometimento. Privilégios administrativos não são necessários neste estágio.
O invasor verifica o domínio para identificar contas associadas aos nomes principais de serviços. Os SPNs mapeiam serviços como servidores SQL ou aplicativos web para contas de serviço específicas. Essas contas se tornam alvos em potencial.
O atacante solicita tíquetes do Ticket Granting Service (TGS) para os SPNs identificados. O controlador de domínio emite esses tickets como parte das operações normais do Kerberos. Cada ticket contém dados criptografados com o hash da senha da conta de serviço.
O invasor extrai a parte criptografada do ticket TGS da memória ou das respostas da rede. Esses dados incluem o material de credencial da conta de serviço em formato criptografado. A extração não alerta o usuário cuja conta foi usada.
Os dados criptografados do ticket são transferidos para um sistema externo para serem descobertos off-line. O atacante usa ataques de força bruta ou de dicionário para adivinhar a senha da conta de serviço. O craqueamento offline evita a detecção porque não gera tráfego de rede.
Se a senha for decifrada com sucesso, o atacante se autentica como a conta de serviço. Muitas contas de serviço têm privilégios elevados dentro do domínio. O acesso elevado permite o movimento lateral e o comprometimento adicional de sistemas críticos.
O Kerberoasting é eficaz porque usa o comportamento normal do sistema em vez de ferramentas óbvias de hacking. O atacante não precisa de malware ou código de exploração para solicitar tíquetes de serviço. O invasor simplesmente solicita tíquetes de serviço ao sistema da mesma forma que usuários e aplicativos comuns. Como as solicitações parecem legítimas, elas não geram alarmes imediatamente.
O ataque não exige direitos de administrador para começar. Até mesmo uma conta de usuário regular dentro da rede da empresa pode solicitar tíquetes de serviço. Muitas contas de serviço usam senhas fracas ou raramente alteradas, o que aumenta as taxas de sucesso na quebra. Os atacantes os decifram usando ferramentas offline de quebra de senhas sem serem detectados.
Outro motivo pelo qual ele é bem-sucedido é que a quebra de senha acontece fora da rede da empresa. Nenhum tráfego incomum aparece durante o processo de craqueamento. No momento em que a senha é recuperada, o invasor já pode ter acesso a contas poderosas com altos privilégios.
O Kerberoasting cria sérios riscos de segurança, pois pode levar ao comprometimento total do domínio se as senhas das contas de serviço forem quebradas. Depois que os invasores obtêm acesso a contas poderosas (como usuários root ou administradores de domínio), eles podem se aprofundar na rede e controlar sistemas críticos.
Muitas contas de serviço têm permissões elevadas. Se um invasor decifrar a senha de uma conta de serviço de alto privilégio, ele poderá obter controle administrativo. O acesso de administrador do domínio permite controle total sobre usuários, servidores e políticas de segurança.
Com as credenciais comprometidas, os atacantes podem acessar outros sistemas dentro da rede. Eles se movem de um servidor para outro usando autenticação legítima. Esse movimento espalha o ataque entre departamentos e ambientes.
Depois de obter acesso elevado, os invasores podem localizar e copiar dados confidenciais. Esses dados podem incluir registros financeiros, informações de clientes ou documentos internos. Os dados roubados podem ser vendidos ou usados para novos ataques.
O acesso privilegiado permite que os invasores implantem ransomware em vários sistemas. Eles podem criptografar servidores, bancos de dados e backups. O amplo acesso aumenta a escala e o impacto do ataque de ransomware.
Os invasores podem criar novas contas ou modificar as permissões para manter o acesso a longo prazo. A persistência permite que eles retornem mesmo após a remediação parcial. A persistência não detectada aumenta o risco de segurança a longo prazo.
Os ataques de Kerberoasting geralmente são realizados usando ferramentas de teste de segurança disponíveis publicamente que interagem com o Active Directory e o Kerberos. Essas ferramentas permitem que os invasores solicitem tíquetes de serviço e extraiam os dados criptografados necessários para a quebra de senhas offline.
Aqui estão algumas ferramentas comuns que os cibercriminosos usam no Kerberoasting:
O Rubeus é uma ferramenta baseada em Windows projetada para interagir diretamente com o protocolo Kerberos. Ele pode solicitar tíquetes de serviço para nomes de principais de serviços específicos e exportar os dados criptografados dos tíquetes. Os profissionais de segurança o usam para testes, mas os invasores o usam para coletar hashes para decifrar off-line.
O Mimikatz é uma ferramenta de extração de credenciais que pode acessar dados de autenticação armazenados na memória. Embora seja amplamente conhecido pelo despejo de senhas, ele pode ajudar no Kerberoasting ao interagir com os tickets do Kerberos. Sua capacidade de extrair material credencial o torna útil em cenários pós-comprometimento.
Impacket é uma coleção de ferramentas Python para trabalhar com protocolos de rede. Ele inclui scripts que podem solicitar tíquetes de serviço do Active Directory e formatá-los para serem quebrados. Os atacantes costumam usá-lo em ambientes Linux durante a penetração da rede.
Os scripts do PowerShell podem consultar o Active Directory para listar os nomes principais do serviço. Esses scripts identificam quais contas de serviço são alvos disponíveis. A enumeração ajuda os invasores a escolher contas que possam ter senhas fracas.
Entre 2018 e 2020, o grupo de ameaças com motivação financeira FIN7 usou o Kerberoasting como parte de sua atividade pós-comprometimento em redes corporativas. Depois de obter acesso inicial por meio de e-mails de phishing e anexos maliciosos, o grupo enumerou os nomes principais do serviço e solicitou tíquetes de serviço do Kerberos. Eles extraíram hashes de tíquetes e decifraram senhas fracas de contas de serviço offline.
O FIN7 tem como alvo cadeias de varejo, hospitalidade e restaurantes em toda a América do Norte. Em vários casos, as credenciais quebradas da conta de serviço permitiram o escalonamento de privilégios para o nível de administrador do domínio. O resultado incluiu roubo de dados de cartões de pagamento e persistência de longo prazo em ambientes corporativos, resultando em milhões de dólares em perdas por fraude.
Em 2020, o grupo APT29, ligado à Rússia, também conhecido como Cozy Bear, usou técnicas de abuso de ingressos da Kerberos durante invasões nas redes do governo e do setor privado dos EUA. Depois de obter credenciais de domínio válidas, os atacantes solicitaram tíquetes de serviço associados a contas de alto privilégio. Senhas fracas de contas de serviço aumentaram a viabilidade de quebra.
A campanha afetou várias agências federais e organizações de tecnologia. O aumento de privilégios permitiu que os invasores acessassem sistemas de e-mail e comunicações internas confidenciais. A violação levou a investigações extensas e custos significativos de remediação nas entidades afetadas.
Vários operadores de ransomware, incluindo grupos associados à Conti, incorporaram o Kerberoasting durante as fases de movimento lateral entre 2019 e 2022. Depois de entrar nas redes por meio de phishing ou acesso remoto exposto, os invasores solicitaram tíquetes de serviço e quebraram senhas de contas de serviço offline.
As contas de serviço comprometidas permitiram amplo acesso a servidores e sistemas de backup. Em muitos incidentes, os invasores aumentaram os privilégios antes de implantar o ransomware em todo o domínio. As consequências incluíram criptografia total da rede, paralisação operacional que durou dias ou semanas e despesas de recuperação multimilionárias.
Para detectar o Kerberoasting, monitore a atividade incomum dos tíquetes de serviço e os padrões de criptografia nos registros do Active Directory. O ataque deixa sinais técnicos que as equipes de segurança podem identificar com registros e análises adequados.
Aqui estão os melhores métodos para detectar o Kerberoasting:
Monitore a ID de evento de segurança do Windows 4769, que registra solicitações de tíquetes de serviço. Um aumento repentino nas solicitações do Ticket Granting Service (TGS) de uma única conta de usuário pode indicar atividade de enumeração. Usuários normais raramente solicitam muitos tíquetes de serviço em pouco tempo.
Fique atento às contas de usuário regulares que solicitam tickets para vários serviços de alto valor, como SQL ou serviços relacionados ao domínio. Funcionários padrão geralmente acessam serviços limitados. Solicitações amplas de tickets podem sinalizar um comportamento de reconhecimento.
Identifique tíquetes de serviço usando criptografia RC4 em vez de criptografia AES mais forte. Os tíquetes criptografados com RC4 são mais fáceis de decifrar off-line. O uso contínuo do RC4 aumenta a exposição ao Kerberoasting.
Monitore as consultas de diretórios que listam muitos nomes principais de serviços. Os atacantes geralmente enumeram os SPNs antes de solicitar tickets. Consultas repetidas de SPN de contas não administrativas indicam atividades suspeitas.
Use ferramentas de monitoramento de segurança que detectem um comportamento incomum de autenticação. Os alertas podem ser acionados quando uma conta de usuário se comporta de maneira diferente do padrão normal. A detecção comportamental ajuda a identificar ataques que parecem legítimos à primeira vista.
Para evitar o Kerberoasting, fortaleça a segurança da conta de serviço e limite a exposição desnecessária do Kerberos no Active Directory. O gerenciamento robusto de senhas e a configuração adequada reduzem o sucesso da quebra.

Aqui estão as melhores estratégias de prevenção para Kerberoasting:
Defina as senhas da conta de serviço com pelo menos 25 caracteres com alta complexidade. Senhas longas e aleatórias resistem a ataques de força bruta e de dicionário. Senhas fortes reduzem significativamente o sucesso de crackeamento offline.
Use contas de serviço gerenciadas em grupo para automatizar o gerenciamento de senhas. O gMSA alterna as senhas regularmente e as armazena com segurança. A rotação automatizada elimina os riscos de reutilização manual de senhas.
Desative a criptografia RC4 e aplique o AES para tíquetes Kerberos. O AES fornece uma proteção criptográfica mais forte. Uma criptografia mais forte aumenta a dificuldade de decifrar.
Revise e remova SPNs desnecessários do domínio. Menos SPNs expostos reduzem a superfície de ataque. Auditorias regulares evitam contas de serviço esquecidas ou desatualizadas.
Conceda às contas de serviço somente as permissões de que elas precisam. Evite atribuir direitos de administrador de domínio, a menos que seja necessário. Privilégios limitados reduzem o impacto do comprometimento de credenciais.
Altere as senhas da conta de serviço em um cronograma definido. A rotação frequente limita a utilidade de credenciais quebradas. A higiene das credenciais fortalece a defesa a longo prazo.
A contenção rápida limita a escalação de privilégios e evita uma maior disseminação. Aqui está a melhor estratégia que uma organização/indivíduo pode usar para responder se estiver sob um ataque de Kerberoasting:
Analise os registros de segurança em busca de alterações incomuns de atividades e privilégios do Ticket Granting Service (TGS). Concentre-se nas contas vinculadas aos nomes principais do serviço. A identificação de contas expostas determina o escopo do comprometimento.
Redefina as senhas de contas de serviço suspeitas imediatamente. Use senhas longas e complexas ou migre para contas de serviços gerenciados por grupos (gMSA). A redefinição de credenciais bloqueia a reutilização de senhas quebradas pelo invasor.
Audite a associação do administrador do domínio e de outros grupos de alto privilégio. Remova permissões elevadas desnecessárias. A revisão de privilégios limita a persistência do atacante.
Examine os registros de autenticação em busca de logins incomuns em todos os servidores. Procure a criação de novas contas ou atribuições de privilégios. A análise do movimento revela se o ataque se espalhou além da conta inicial.
Ative o registro detalhado do Kerberos e monitore a atividade do Event ID 4769. Configure alertas para solicitações anormais de tíquetes de serviço. O monitoramento aprimorado evita ataques repetidos e melhora a visibilidade a longo prazo.
Não, o Kerberoasting não exige privilégios de administrador para iniciar. Qualquer usuário de domínio autenticado pode solicitar tíquetes de serviço para contas vinculadas a nomes principais de serviços. O ataque começa com o acesso regular do usuário.
Sim, o Kerberoasting continua sendo amplamente usado em ataques do Active Directory. Os invasores continuam atacando senhas fracas de contas de serviço porque muitos ambientes ainda dependem de configurações antigas.
Sim, o Kerberoasting pode funcionar sem malware. O ataque usa solicitações legítimas de tíquetes do Kerberos e quebra senhas offline, o que evita gerar tráfego de rede suspeito.
As contas de serviço com senhas fracas ou raramente alteradas são as mais vulneráveis. Contas vinculadas a serviços de banco de dados, aplicativos da web ou sistemas de backup são alvos comuns.
Depende do tamanho e da complexidade da senha. Senhas fracas podem ser quebradas em minutos, enquanto senhas aleatórias fortes com mais de 25 caracteres podem resistir a tentativas de quebra por anos.
