🚀 A CloudSEK se torna a primeira empresa de segurança cibernética de origem indiana a receber investimentos da Estado dos EUA fundo
Leia mais
O ransomware é estruturado em torno de modelos funcionais distintos que determinam como as vítimas perdem o acesso aos dados ou sistemas. A classificação se concentra na mecânica operacional, como controle de criptografia, restrição do sistema e design de extorsão em várias camadas.
A divergência funcional aparece na forma como os atacantes impõem o pagamento, seja por meio do bloqueio criptográfico de arquivos, da negação em toda a rede ou da exposição de informações roubadas. A arquitetura de implantação e a estrutura de monetização separam ainda mais um modelo do outro.
As campanhas modernas de ransomware operam como estruturas de extorsão coordenadas, em vez de incidentes de malware isolados. A segmentação funcional clara explica como esses modelos de ataque diferem em nível técnico e estratégico.
O ransomware é categorizado em seis tipos funcionais principais com base no comportamento de criptografia, arquitetura de extorsão, controle de infraestrutura e estrutura de monetização.
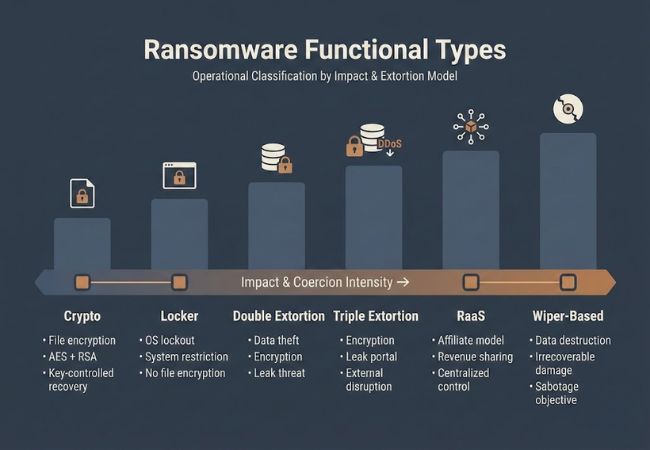
Ransomware criptográfico criptografa arquivos usando modelos criptográficos híbridos que combinam criptografia simétrica, como AES, com mecanismos de troca de chaves assimétricos, como RSA. As chaves de decodificação são geradas por vítima e transmitidas aos servidores de comando e controle controlados pelo atacante.
A disponibilidade dos arquivos é totalmente restrita enquanto os processos do sistema permanecem operacionais. A monetização depende inteiramente do controle exclusivo da chave privada armazenada na infraestrutura remota e das instruções de pagamento vinculadas às carteiras de criptomoedas.
O ransomware Locker restringe o acesso no nível do sistema operacional bloqueando interfaces de login, entrada de teclado ou ambientes de desktop. A execução da carga útil modifica os processos do sistema ou as configurações de inicialização para evitar a interação do usuário.
Os dados podem permanecer intactos na mídia de armazenamento, mas a disponibilidade do sistema é interrompida até que o mecanismo de bloqueio seja removido. A coerção depende da negação no nível do dispositivo, em vez do controle criptográfico de arquivos.
O ransomware de extorsão dupla realiza a exfiltração de dados antes de iniciar a criptografia de arquivos, transferindo informações confidenciais para servidores controlados pelo invasor. Os dados roubados são catalogados e preparados para publicação em portais dedicados a vazamentos hospedados em redes anônimas.
A perda de confidencialidade se torna um mecanismo de pressão paralelo ao lado da interrupção da disponibilidade. As demandas de pagamento são reforçadas por meio de ameaças de exposição regulatória, violação contratual e danos à reputação.
O ransomware de extorsão tripla expande o modelo ao introduzir um vetor coercitivo adicional além da criptografia e do vazamento de dados. Os atacantes podem lançar ataques distribuídos de negação de serviço ou contatar diretamente clientes, parceiros e partes interessadas para aumentar a pressão.
A interrupção em várias camadas visa simultaneamente a disponibilidade, a confidencialidade e a continuidade do serviço. O design operacional integra cargas úteis de criptografia, infraestrutura de vazamento e campanhas externas de interrupção em uma estrutura coordenada de extorsão.
O Ransomware-as-a-Service opera por meio de um ecossistema estruturado de afiliados, no qual os desenvolvedores mantêm códigos de malware, portais de pagamento e painéis de gerenciamento de decodificação. Os afiliados obtêm acesso a cargas úteis e ferramentas de distribuição prontas em troca de acordos de compartilhamento de receita.
A centralização da infraestrutura permite atualizações rápidas de carga útil, rastreamento de campanhas e portais automatizados de negociação de resgate. A separação funcional entre o criador e o implantador distingue o RaaS das operações de ransomware de um único ator.
O ransomware baseado em Wiper incorpora cargas destrutivas que sobrescrevem ou corrompem estruturas de dados além da recuperação. As rotinas de criptografia podem ser superficiais ou ausentes, servindo apenas como fachada para danos irreversíveis ao sistema.
A destruição da integridade substitui a monetização recuperável como resultado principal. Os objetivos do ataque geralmente se alinham com interrupção, sabotagem ou desestabilização estratégica, em vez de pagamento garantido de resgate.
Os tipos funcionais de ransomware diferem com base no método de coerção, no impacto na segurança, no design da infraestrutura e na estrutura de monetização.
A classificação do ransomware depende da arquitetura funcional em vez de nomes de marcas ou famílias de malware. Controle de criptografia, negação do sistema, exposição de dados, infraestrutura de afiliados e execução destrutiva definem como cada tipo opera.
A separação clara entre esses seis modelos funcionais melhora a compreensão técnica de como a coerção é estruturada e monetizada. A evolução estrutural da simples criptografia de arquivos às estruturas de extorsão em camadas reflete a crescente complexidade operacional das campanhas modernas de ransomware.
O ransomware de extorsão tripla cria a maior interrupção ao combinar criptografia, exposição de dados e ataques a serviços externos, como negação de serviço distribuída. A coerção em várias camadas afeta simultaneamente a disponibilidade, a confidencialidade e a continuidade dos negócios.
O ransomware como serviço define uma arquitetura de implantação e monetização, enquanto o ransomware criptográfico define um mecanismo de coerção baseado em criptografia. As plataformas RaaS podem distribuir criptomoedas, extorsão dupla ou cargas híbridas por meio de redes afiliadas.
O ransomware Locker normalmente restringe o acesso ao sistema sem criptografar os arquivos armazenados. A integridade dos dados geralmente permanece intacta, a menos que seja combinada com cargas destrutivas adicionais.
A extorsão dupla introduz ameaças de exfiltração e vazamento de dados no portal, juntamente com a criptografia de arquivos. A perda de confidencialidade aumenta a exposição regulatória e os danos à reputação, além da simples inacessibilidade dos dados.
O ransomware baseado em Wiper pode exibir demandas de resgate mesmo quando a capacidade de decodificação não existe. O design da carga útil prioriza a corrupção ou a substituição irreversíveis de dados em vez de uma recuperação garantida.
