🚀 أصبحت CloudSek أول شركة للأمن السيبراني من أصل هندي تتلقى استثمارات منها ولاية أمريكية صندوق
اقرأ المزيد
منصة Cyber Threat Intelligence (CTI) هي نظام يجمع بيانات التهديدات ويحللها لإنتاج معلومات استخباراتية قابلة للتنفيذ لفرق الأمن السيبراني. فهو يجمع المدخلات من خلاصات معلومات التهديدات والاستخبارات مفتوحة المصدر (OSINT) وسجلات الأمان الداخلية في رؤية موحدة ومنظمة للمخاطر.
تصبح بيانات التهديد مفيدة عندما تكون متصلة وليست معزولة. تربط منصات CTI كيانات مثل الجهات الفاعلة في مجال التهديد ومؤشرات التسوية (IOCs) وتوقيعات البرامج الضارة وتقنيات الهجوم للكشف عن الأنماط والعلاقات التي تدعم اتخاذ القرار بشكل أسرع وأكثر دقة داخل مراكز العمليات الأمنية (SOC).
إن ارتفاع تكاليف الاختراق وأساليب الهجوم المعقدة بشكل متزايد تجعل الاكتشاف المبكر أمرًا بالغ الأهمية للمؤسسات. يشير تقرير تكلفة خرق البيانات من IBM إلى أن متوسط التكلفة العالمية لخرق البيانات بلغ 4.4 مليون دولار أمريكي، مما يعزز الحاجة إلى منصات CTI التي تعمل على تحسين الرؤية وتقليل وقت الاستجابة وتعزيز مرونة الأمن السيبراني بشكل عام.
تتكون دورة حياة Cyber Threat Intelligence من ست مراحل متصلة تعمل باستمرار على تحويل بيانات التهديدات الأولية إلى ذكاء قابل للتنفيذ.

يتم تحديد متطلبات الذكاء بناءً على مخاطر الأعمال والأصول الهامة وأولويات الأمان. يتم التركيز على التهديدات عالية التأثير مثل برامج الفدية والتصيد الاحتيالي والهجمات المستهدفة لضمان بقاء جهود الاستخبارات ذات صلة.
يتم جمع بيانات التهديدات من الأنظمة الداخلية والبيئات الخارجية لتوسيع الرؤية. توفر السجلات والقياس عن بُعد لنقطة النهاية ومصادر الذكاء الخارجية معًا تغطية أوسع وتقليل النقاط العمياء.
يتم تنظيف البيانات الأولية وتنظيمها في تنسيقات متسقة لتحسين قابلية الاستخدام. تتم إزالة البيانات المكررة وغير ذات الصلة ومنخفضة الثقة، بينما يضمن التطبيع الاتساق لمزيد من التحليل.
يتم فحص البيانات التي تمت معالجتها لتحديد الأنماط وسلوك المهاجم والمخاطر المحتملة. يساعد الارتباط عبر الإشارات ورسم الخرائط لأطر مثل MITRE ATT&CK على شرح كيفية عمل التهديدات.
يتم تقديم المعلومات القابلة للتنفيذ إلى أصحاب المصلحة المناسبين بتنسيقات مناسبة لاحتياجاتهم. تتلقى الفرق الفنية تنبيهات مفصلة، بينما تلخص مكاسب القيادة الرؤى لدعم صنع القرار.
يتم تقييم نتائج كل دورة لتحديد الفجوات وتحسين جهود الاستخبارات المستقبلية. يضمن التحسين المستمر أن تظل دورة الحياة متوافقة مع التهديدات المتطورة والأولويات التنظيمية.
تعتمد المنصات المصممة للتعامل مع كميات كبيرة من بيانات التهديدات على CTI لجعل هذه المعلومات قابلة للاستخدام في قرارات الأمان في العالم الحقيقي.
تتدفق المعلومات من مزيج من المزودين الخارجيين والأنظمة الداخلية والمصادر السرية حيث غالبًا ما يظهر نشاط التهديد أولاً. يُبقي هذا التدفق المستمر الفرق على دراية بالمخاطر الجديدة عند ظهورها، وليس بعد حدوث الضرر.
تقدم المؤشرات الأولية بمفردها قيمة محدودة حتى يتم وضعها في السياق. يضيف الإثراء خلفية مثل البنية التحتية ذات الصلة والنشاط التاريخي والارتباطات المعروفة، مما يجعل تفسير كل إشارة والعمل عليها أسهل.
نادرًا ما تكشف نقاط البيانات المعزولة الصورة الكاملة للهجوم. من خلال ربط الأحداث والمؤشرات ذات الصلة، تبدأ الأنماط في الظهور، مما يسمح للفرق بتتبع كيفية تطور الاختراق عبر الأنظمة.
يتم تشغيل المهام المتكررة مثل استيعاب البيانات والتحليل وإنشاء التنبيهات تلقائيًا لتقليل عبء العمل اليدوي. التكامل مع أنظمة سولار يتيح الاستجابة للحوادث بشكل أسرع وأكثر اتساقًا.
تصبح البيانات المعقدة أسهل في التعامل معها عندما يتم تقديمها بشكل مرئي. تسمح المشاهدات المهيكلة للفرق بفهم ما يحدث بسرعة، وأين يلزم الاهتمام، وكيف تتطور التهديدات بمرور الوقت.
تضمن الإشعارات في الوقت المناسب عدم تفويت المشكلات الحرجة أثناء العمليات الجارية. توفر التقارير سجلاً أوضح للأحداث، مما يساعد الفرق على التحقيق في الحوادث وإبلاغ النتائج عبر المؤسسة.
تعتمد منصات CTI على أنواع مختلفة من معلومات التهديدات لتغطية كل من المخاطر الاستراتيجية والتهديدات الفنية في الوقت الحقيقي.
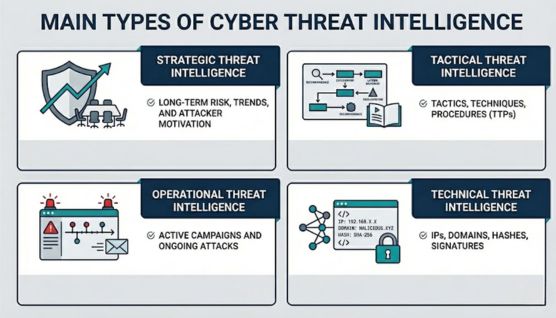
يركز الذكاء الاستراتيجي على المخاطر طويلة الأجل واتجاهات الصناعة ومشهد التهديدات الأوسع الذي يؤثر على المؤسسة. تعتمد فرق القيادة على ذلك لفهم كيفية تطور التهديدات السيبرانية وأين يجب توجيه الاستثمارات الأمنية.
تسلط الرؤى من هذه الطبقة الضوء على أنماط مثل زيادة نشاط برامج الفدية عبر قطاعات محددة أو التحولات التي تقودها الأحداث الجيوسياسية. توجه هذه الإشارات القرارات المتعلقة بسياسات الأمان وتخصيص الميزانية وإدارة المخاطر الشاملة.
يشرح الذكاء التكتيكي كيفية تنفيذ الهجمات من خلال تحليل التكتيكات والتقنيات والإجراءات (TTPs) التي تستخدمها الجهات الفاعلة في مجال التهديد. تستخدمه فرق الأمن لكسر أساليب الهجوم الشائعة وتعزيز الدفاعات وفقًا لذلك.
الأنماط المتكررة مثل حملات التصيدأو سرقة بيانات الاعتماد أو تقنيات الحركة الجانبية يصبح من السهل التعرف عليها باستخدام هذا الذكاء. يتم بعد ذلك تحسين قواعد الكشف والضوابط الدفاعية لتقليل التعرض لمسارات الهجوم المماثلة.
توفر المعلومات التشغيلية رؤى تفصيلية حول تهديدات محددة، بما في ذلك التوقيت والأهداف ونية المهاجم. إنها تلعب دورًا مباشرًا في التعامل مع التهديدات النشطة أو الناشئة.
يمكن تتبع الحملات المستمرة والأصول المستهدفة ونقاط الدخول المحتملة بشكل أكثر فعالية من خلال هذه المعلومات. ونتيجة لذلك، يتحسن التنسيق بين فرق الرصد والاستجابة، لا سيما داخل مراكز العمليات الأمنية (SOC).
يركز الذكاء الفني على مؤشرات التسوية (IOCs) مثل عناوين IP وأسماء النطاقات وتجزئات الملفات وتوقيعات البرامج الضارة. يتم استخدام نقاط البيانات هذه مباشرةً بواسطة أدوات الأمان لاكتشاف التهديدات وحظرها.
التكامل مع أنظمة مثل SIEM وتسمح جدران الحماية لهذه المؤشرات بتشغيل الاستجابات الآلية. يصبح الاحتواء الأسرع ممكنًا دون الاعتماد فقط على التحقيق اليدوي.
اقرأ المزيد: أنواع المعلومات المتعلقة بالتهديدات الإلكترونية (CTI)
تُظهر حوادث العالم الحقيقي كيف يصبح الذكاء مفيدًا عند توصيل الإشارات المبكرة قبل تطور التهديدات بشكل كامل.
غالبًا ما يظهر التعرض من طرف ثالث خارج نطاق الرؤية المباشرة من خلال بيانات الاعتماد المسربة أو أصول السحابة التي تم تكوينها بشكل خاطئ أو إشارات البنية التحتية الخارجية. تكشف هذه المؤشرات المبكرة نقاط الضعف قبل أن يتمكن المهاجمون من الوصول الكامل.
حددت CloudSek حادثة Oracle Cloud حيث تم تسريب 6 ملايين سجل، مما أثر على أكثر من 140,000 مستأجر، مما أظهر كيف يمكن لنقطة ضعف واحدة في سلسلة التوريد أن تتوسع عبر مؤسسات متعددة.
تعيد حملات الهجوم استخدام النطاقات وبيئات الاستضافة وأنماط التسليم عبر الأهداف. يسمح اكتشاف هذه الروابط مبكرًا للفرق بحظر البنية التحتية الضارة قبل وصولها إلى المستخدمين.
أفاد المركز الوطني للأمن السيبراني في المملكة المتحدة (NCSC) في عام 2025 أنه تم إزالة أكثر من 1.2 مليون حملة تصيد، مع تخفيف 79٪ منها في غضون 24 ساعة، مما يدل على تأثير الذكاء المبكر.
تتبع برامج الفدية تسلسلاً يتضمن الوصول الأولي والحركة الجانبية وتسريب البيانات. يتيح تحديد هذه المراحل مبكرًا للمؤسسات إيقاف الهجمات قبل حدوث التشفير أو فقدان البيانات.
أكدت NCSC في المملكة المتحدة في عام 2025 أن برامج الفدية لا تزال واحدة من أكثر التهديدات المدمرة للبنية التحتية الحيوية، مما يتطلب اكتشافًا أسرع لتقليل التأثير التشغيلي.
تتعامل فرق الأمان مع كميات كبيرة من التنبيهات، ولكن لا تحمل جميع الإشارات مخاطر متساوية. تحديد الأولويات القائم على الذكاء يربط الأحداث ذات الصلة ويسلط الضوء على ما يتطلب اتخاذ إجراءات فورية.
أفاد المنتدى الاقتصادي العالمي في عام 2026 أن 73٪ من الأفراد تعرضوا للاحتيال عبر الإنترنت في عام 2025، مما يعكس حجم التهديدات والحاجة إلى قرارات أسرع تستند إلى السياق.
تظهر بيانات الاعتماد المسربة في مجموعات بيانات الاختراق والمنتديات السرية قبل أن يتم استغلالها بنشاط. يتيح اكتشافها مبكرًا للمؤسسات تأمين الحسابات قبل حدوث الوصول غير المصرح به.
تحدد توقعات الأمن السيبراني لعام 2025 من Google Cloud إساءة استخدام بيانات الاعتماد والهجمات القائمة على الهوية كعوامل وصول أولية رائدة، مما يعزز الحاجة إلى الاكتشاف المبكر والاستجابة.
يصبح فهم التهديدات والاستجابة لها أكثر فعالية مع ذكاء التهديدات السيبرانية، لكن النتائج تعتمد على مدى جودة تنفيذها وتشغيلها.
تنشأ المعلومات المتعلقة بالتهديدات من بيئات متعددة تظهر فيها أنشطة المهاجمين ونقاط الضعف وإشارات التعرض باستمرار عبر النظم البيئية الرقمية.
غالبًا ما تعرض مواقع الويب والمنتديات والمدونات ومستودعات التعليمات البرمجية الثغرات الأمنية وبيانات الاعتماد المسربة والأصول التي تم تكوينها بشكل خاطئ. غالبًا ما تكشف عمليات الكشف عن الأمان وإلتزامات المطورين وواجهات برمجة التطبيقات المكشوفة نقاط الضعف قبل أن يستغلها المهاجمون بشكل فعال، مما يجعل هذه المصادر ضرورية للرؤية في المراحل المبكرة.
منتديات الويب المظلمةتستضيف المجتمعات المشفرة والأسواق غير المشروعة البيانات المسروقة وبيانات الوصول إلى بيانات الاعتماد والمناقشات حول الهجمات النشطة أو المخطط لها. توفر مراقبة هذه البيئات نظرة ثاقبة على نية المهاجم والحملات الناشئة وتداول الأصول المخترقة قبل وقت طويل من الوعي العام.
تعكس السجلات ونشاط نقطة النهاية وحركة مرور الشبكة وسجلات المصادقة التفاعلات الحقيقية داخل البنية التحتية للمؤسسة. يشير السلوك غير المعتاد مثل تصعيد الامتيازات أو الحركة الجانبية أو محاولات الوصول غير المصرح بها إلى التهديدات النشطة التي تنشأ من كل من النشاط الخارجي والداخلي.
تجمع المعلومات المنسقة من مزودي الأمن البيانات التي تم جمعها من أجهزة الاستشعار العالمية والمصائد وعمليات البحث. تتضمن هذه الخلاصات البنية التحتية الضارة المعروفة وتوقيعات التهديدات ومعلومات الثغرات الأمنية التي تعمل على توسيع نطاق الرؤية بما يتجاوز ما يمكن للأنظمة الداخلية ملاحظته.
توثق الأبحاث المنشورة وتقارير التهديدات وقواعد بيانات الثغرات نقاط الضعف المكتشفة حديثًا وتقنيات الاستغلال. توفر التفاصيل حول CVEs وعمليات استغلال إثبات المفهوم والجداول الزمنية للتصحيح سياقًا حول كيفية قيام المهاجمين بتسليح الثغرات الأمنية في البيئات الحقيقية.
تعمل المعلومات المتبادلة عبر مجموعات الصناعة و ISACS والمبادرات التي تقودها الحكومة على تعزيز الوعي الجماعي بالهجمات المنسقة. تسلط المعلومات المشتركة الضوء على التهديدات الخاصة بالقطاع والحملات واسعة النطاق والاتجاهات المعادية التي قد لا تكون مرئية داخل مؤسسة واحدة.
تتطلب استراتيجيات CTI الناجحة مواءمة معلومات التهديدات مع مخاطر الأعمال وسير العمل التشغيلي وعمليات صنع القرار.
تحدد الأهداف الواضحة نوع الذكاء المطلوب وكيف سيتم استخدامه. يجب أن تتوافق الأهداف مع مخاطر الأعمال والأصول الهامة ومشهد التهديدات ذي الصلة بالمؤسسة.
يجب تحديد مصادر البيانات ذات الصلة بناءً على نوع التهديدات التي تتم مراقبتها. يجب إعطاء الأولوية للإشارات الخارجية والقياس الداخلي والذكاء الخاص بالصناعة لضمان تغطية ذات مغزى.
يضمن التكامل مع منصات مثل SIEM و SOAR تدفق الذكاء مباشرة إلى عمليات سير عمل الاكتشاف والاستجابة. تعمل الأنظمة المتصلة على تقليل التأخير بين تحديد التهديد واتخاذ الإجراءات.
تعمل العمليات المحددة لمعالجة بيانات التهديدات وإثرائها وربطها على تحسين الاتساق والدقة. تساعد عمليات سير العمل المهيكلة الفرق على الانتقال من البيانات الأولية إلى الذكاء القابل للتنفيذ دون ارتباك.
لا تتطلب جميع التهديدات نفس المستوى من الاهتمام، مما يجعل تحديد الأولويات أمرًا ضروريًا. يساعد التقييم المستند إلى المخاطر في تركيز الموارد على التهديدات عالية التأثير التي تؤثر على الأنظمة أو الأصول الهامة.
تعمل الأتمتة على تقليل الجهد اليدوي في جمع البيانات وإثرائها ومعالجة التنبيهات. يمكن التعامل مع المهام المتكررة بكفاءة، مما يسمح للمحللين بالتركيز على التحقيق واتخاذ القرار.
تتطور بيئات التهديد، مما يتطلب تعديلًا مستمرًا لاستراتيجيات الذكاء. يجب استخدام التعليقات من الحوادث ومصادر البيانات الجديدة والمخاطر المتغيرة لتحسين الدقة والفعالية بمرور الوقت.
تقوم CloudSek بجمع بيانات استخبارات التهديدات الإلكترونية من خلال المراقبة المستمرة للبيئات الخارجية ومعالجة البيانات من خلال خط أنابيب استخبارات قائم على الذكاء الاصطناعي.
يتم فحص بيئات الويب السطحية والعميقة والمظلمة باستمرار لتحديد الإشارات المبكرة للتهديدات. يكشف النشاط عبر المنتديات السرية والأسواق والقنوات المشفرة مثل Telegram و IRC عن تسريبات بيانات الاعتماد والهجمات المخطط لها والتعرض للبيانات قبل أن تصبح الحوادث نشطة.
يتم تتبع البيانات المتاحة للجمهور عبر منصات الأخبار ووسائل التواصل الاجتماعي والمدونات ومواقع اللصق لتحديد المخاطر الناشئة والمعلومات المكشوفة. يتم أيضًا فحص مستودعات التعليمات البرمجية مثل GitHub و Bitbucket بحثًا عن التسريبات العرضية لمفاتيح API وشفرة المصدر والأصول الحساسة.
يتم تحليل تطبيقات الهاتف المحمول باستخدام محرك BeVigil من CloudSek لاكتشاف التبعيات غير الآمنة والأسرار المشفرة والتكوينات المكشوفة. تعمل هذه الطبقة على توسيع نطاق الرؤية في المخاطر الناشئة عن النظم البيئية للأجهزة المحمولة وتطبيقات الطرف الثالث.
يتم تجميع البنية التحتية الضارة والمؤشرات الفنية مثل عناوين IP والمجالات وتجزئات الملفات وإشارات الشبكة باستمرار. تساعد نقاط البيانات هذه في تحديد التهديدات النشطة وتعيين البيئات التي يتحكم فيها المهاجمون.
يتم توحيد البيانات المجمعة ومعالجتها باستخدام نموذج ThreatMeter AI الخاص بـ CloudSek لتحديد الأنماط وتقليل الضوضاء. يساعد الارتباط عبر الإشارات على اكتشاف العلاقات وتحديد التهديدات لأصول الأعمال والتنبؤ بموجهات الهجوم الأولية المحتملة.
يقوم محللو الأمن بمراجعة النتائج عالية المخاطر لتحسين الدقة وتقليل الإيجابيات الكاذبة. يتم تسليم المعلومات التي تم التحقق منها من خلال لوحات المعلومات أو دمجها في أنظمة مثل Splunk و Cortex XSOAR لاتخاذ إجراءات فورية.
تحتفظ بحيرة البيانات التي يتم تحديثها باستمرار بسجلات الاختراقات والتسريبات وأنشطة التهديد السابقة. يعزز السياق التاريخي التحليل من خلال ربط الإشارات الجديدة بالأنماط التي تمت ملاحظتها سابقًا.
تتميز CloudSek من خلال الجمع بين الذكاء التنبئي ورؤية المخاطر الخارجية والارتباط القائم على الذكاء الاصطناعي في منصة واحدة موحدة.
تعمل منصات استخبارات التهديدات الإلكترونية (CTI) على تحويل الأمن من المراقبة التفاعلية إلى صنع القرار القائم على الاستخبارات. تسمح الرؤية عبر سلوك المهاجم والتعرض الخارجي وأنماط التهديد المتطورة للمؤسسات بالتصرف في وقت مبكر وبدقة أكبر.
تجمع المنصات القوية بين تغطية البيانات والفهم السياقي والأتمتة لتقليل الضوضاء وإبراز ما يهم حقًا. مع استمرار توسع بيئات التهديدات، تصبح القدرة على توصيل الإشارات بذكاء ذي مغزى جزءًا مهمًا من الحفاظ على المرونة الأمنية على المدى الطويل.
تعمل منصات CTI على تقليل الفجوة بين بيانات التهديدات الأولية والرؤية القابلة للتنفيذ. تكتسب فرق الأمان رؤية أوضح لسلوك المهاجم والمخاطر الخارجية والتهديدات الناشئة دون ربط البيانات يدويًا.
يزيل الذكاء المعالج مسبقًا والمعزز الحاجة إلى تحليل الإشارات المعزولة. يسمح الارتباط السريع للأنماط للفرق بتحديد التهديدات في وقت مبكر من دورة حياة الهجوم.
تكشف الرؤية الخارجية عن المخاطر الموجودة خارج الأنظمة الداخلية، مثل بيانات الاعتماد المكشوفة والبيانات المسربة ومناقشات المهاجمين. يساعد الوعي المبكر بهذه الإشارات على منع التهديدات قبل وصولها إلى المؤسسة.
يوفر الذكاء السياقي تفاصيل حول أساليب الهجوم والبنية التحتية والسلوك. تستخدم فرق الاستجابة هذه المعلومات للتحقيق في الحوادث بشكل أكثر كفاءة واتخاذ الإجراءات المستهدفة.
يوفر الاستخدام المستقل الرؤية، ولكن التكامل مع أنظمة مثل SIEM و SOAR يحسن سرعة الاستجابة والأتمتة. تسمح البيئات المتصلة للذكاء بتشغيل الإجراءات في الوقت الفعلي.
تركز المنصات الحديثة على الارتباط والسياق والتنبؤ بدلاً من تجميع البيانات البسيط. يتمحور الذكاء حول المخاطر والسلوك والأهمية بدلاً من المؤشرات المعزولة.
