🚀 A CloudSEK se torna a primeira empresa de segurança cibernética de origem indiana a receber investimentos da Estado dos EUA fundo
Leia mais
O ransomware Ryuk surgiu em agosto de 2018 e foi atribuído ao grupo cibercriminoso Wizard Spider, que também operava malware como o TrickBot. Ao contrário do ransomware distribuído em massa, o Ryuk foi implantado depois que os atacantes obtiveram acesso total à rede, permitindo que eles criptografassem sistemas corporativos e exigissem pagamentos multimilionários em Bitcoin.
Entre 2019 e 2021, o Ryuk se tornou uma das cepas de ransomware mais prejudiciais financeiramente, com o Federal Bureau of Investigation relatando perdas de dezenas de milhões de dólares somente com vítimas dos EUA. Seus ataques afetaram fortemente hospitais, governos municipais e grandes empresas, onde o tempo de inatividade se traduziu diretamente em interrupções financeiras e operacionais.
Em 2025, o ransomware estava envolvido em 44% das violações globais de dados, de acordo com o Relatório de Investigações de Violações de Dados da Verizon, refletindo o domínio contínuo de táticas pioneiras de grupos como o Wizard Spider. Embora as operações da Ryuk tenham diminuído depois que as afiliadas mudaram para modelos mais novos de ransomware, sua estratégia de caça a grandes jogos continua sendo fundamental para a extorsão cibernética moderna com foco nas empresas.
O Ryuk é uma estrutura de ransomware direcionada criada para ataques controlados e de alto impacto contra redes corporativas. Sua função principal é tornar os dados organizacionais inacessíveis por meio de criptografia avançada e, ao mesmo tempo, exigir criptomoedas em troca de restauração.
Ao contrário dos kits automatizados de ransomware, o Ryuk exige supervisão humana durante a implantação, permitindo que os invasores bloqueiem seletivamente servidores, ambientes virtuais e bancos de dados essenciais. Esse modelo de execução deliberada o posicionou como uma ferramenta de extorsão cibernética com precisão, em vez de uma ameaça de infecção em massa.
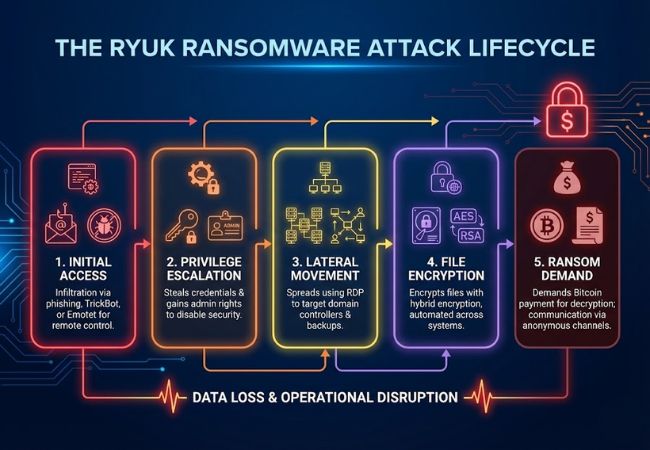
O ransomware Ryuk funciona se infiltrando em uma rede corporativa, aumentando os privilégios, criptografando sistemas críticos e exigindo o pagamento em Bitcoin pela decodificação.
O Ryuk tem como alvo setores em que o tempo de inatividade do sistema leva à perda financeira imediata e à crise operacional.
Hospitais e redes médicas eram alvos frequentes porque os sistemas criptografados interrompem o atendimento ao paciente e os serviços de emergência. A urgência de restaurar as operações clínicas aumentou a pressão de pagamento do resgate.
Instituições municipais e estaduais foram atacadas devido à infraestrutura legada e aos recursos limitados de segurança cibernética. A criptografia de sistemas administrativos atrasou os serviços públicos e as operações essenciais.
As empresas com ambientes de TI centralizados foram direcionadas por sua capacidade financeira e escala de rede. A criptografia de servidores e bancos de dados principais maximizou a interrupção dos negócios.
Fornecedores de energia, logística e serviços públicos enfrentaram riscos porque a interrupção do serviço afeta as cadeias de suprimentos e a estabilidade pública. A paralisação operacional nesses setores criou uma alta alavancagem de negociação para os atacantes.
A prevenção de ataques no estilo Ryuk exige controles de segurança em camadas que bloqueiam o acesso inicial e limitam a propagação interna.
A aplicação da autenticação multifator (MFA) para acesso remoto reduz o risco de abuso de credenciais. Restringir privilégios administrativos limita o movimento do invasor dentro da rede.
A filtragem avançada de e-mail ajuda a bloquear anexos e links maliciosos antes que eles cheguem aos usuários. O treinamento regular de conscientização sobre phishing reduz a probabilidade de comprometimento das credenciais.
Separar servidores críticos dos endpoints do usuário evita a criptografia completa da rede. A segmentação limita o movimento lateral se os atacantes obtiverem acesso inicial.
As ferramentas de detecção e resposta de terminais (EDR) identificam comportamentos incomuns, como aumento de privilégios ou modificação em massa de arquivos. O monitoramento contínuo permite uma contenção mais rápida antes que a criptografia se espalhe.
A manutenção de backups off-line e imutáveis garante a recuperação sem pagar resgate. Testes regulares de restauração confirmam a integridade do backup durante incidentes reais.
A resposta efetiva depende da detecção precoce, contenção rápida e procedimentos de recuperação controlada.
A elevação inesperada dos privilégios do usuário pode indicar atividade do invasor dentro da rede. O monitoramento de alterações na conta administrativa ajuda a identificar o comprometimento antes do início da criptografia.
Sessões incomuns do Remote Desktop Protocol (RDP) ou logins após o expediente podem sinalizar um movimento lateral. Registrar e revisar a atividade de acesso remoto reduz os pontos cegos.
Conexões de saída com endereços IP externos desconhecidos podem revelar o armazenamento de malware. As ferramentas de monitoramento de rede devem sinalizar padrões suspeitos de tráfego criptografado.
A renomeação rápida de arquivos ou a criptografia simultânea em unidades compartilhadas são um indicador importante de ransomware. Alertas automatizados para atividades anormais de arquivos permitem uma resposta mais rápida.
Os sistemas comprometidos devem ser desconectados da rede para impedir uma maior disseminação. As credenciais afetadas devem ser desativadas para cortar o acesso do invasor.
Os sistemas devem ser restaurados a partir de backups off-line verificados após a confirmação da remoção da ameaça. A análise pós-incidente garante que os mecanismos de persistência sejam eliminados antes da reconexão total da rede.
O ransomware Ryuk marcou uma mudança em direção à extorsão cibernética orientada pela precisão e focada na empresa, que priorizou a interrupção operacional máxima em vez da infecção em massa. Seu modelo de implantação direcionado e sua estratégia de resgate de alto valor remodelaram a forma como as campanhas modernas de ransomware são executadas.
Embora as operações originais da Ryuk tenham diminuído, as táticas estabelecidas continuam influenciando o cenário atual de ameaças. Entender como o Ryuk funcionou ajuda as organizações a fortalecer as defesas contra ataques de ransomware operados por humanos atuais e futuros.
As campanhas diretas de Ryuk diminuíram, mas os métodos de ataque pioneiros permanecem ativos nas operações modernas de ransomware. A extorsão operada por humanos e focada na empresa continua dominando os incidentes cibernéticos em grande escala.
Os pedidos de resgate geralmente variavam de várias centenas de milhares a vários milhões de dólares em Bitcoin. O valor geralmente era calculado com base no tamanho e na receita da organização vítima.
Geralmente, a recuperação só é possível por meio de backups seguros e off-line. O modelo de criptografia usado torna a decodificação por força bruta impraticável sem a chave privada do atacante.
O comprometimento inicial geralmente ocorria por meio de campanhas de phishing ou carregadores de malware, como o TrickBot. Os atacantes usaram credenciais roubadas para expandir o controle antes de implantar a criptografia.
O Ryuk foi implantado manualmente após o comprometimento da rede, em vez de se espalhar automaticamente em grande escala. Essa execução seletiva permitiu que os atacantes atacassem sistemas de alto valor e maximizassem o impacto operacional.
