🚀 A CloudSEK se torna a primeira empresa de segurança cibernética de origem indiana a receber investimentos da Estado dos EUA fundo
Leia mais
O ransomware de extorsão dupla é um método de ataque cibernético em que os atacantes criptografam sistemas e exfiltram dados confidenciais durante uma única intrusão. O pagamento é exigido pela decodificação e as informações roubadas são ameaçadas de divulgação pública se os pedidos de resgate forem rejeitados.
A estrutura de ataque combina criptografia de arquivos com roubo deliberado de dados para aumentar a coerção. A restauração do backup não elimina o risco de exposição devido a possíveis vazamentos públicos.
A paralisação operacional ocorre por meio de criptografia, e danos regulatórios, financeiros e de reputação resultam de ameaças de divulgação de dados. A estratégia de dupla pressão define o ransomware de extorsão dupla como uma forma avançada de extorsão cibernética.
O ransomware de extorsão dupla difere do ransomware tradicional ao combinar criptografia de arquivos com roubo de dados e ameaças de vazamento público para aumentar a pressão coercitiva.
O ransomware de extorsão dupla segue um modelo de intrusão de vários estágios projetado para garantir a interrupção operacional e a alavancagem de dados. Cada fase fortalece a pressão de extorsão antes do início da negociação do resgate.
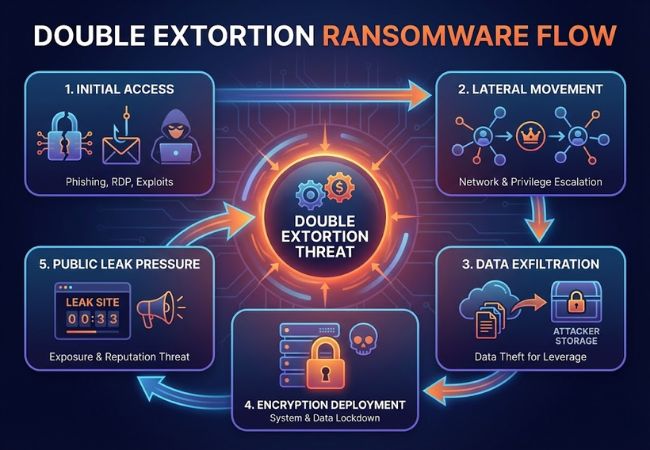
Os invasores conseguem entrar por meio de campanhas de phishing, serviços expostos do Protocolo de Desktop Remoto, preenchimento de credenciais ou exploração de vulnerabilidades não corrigidas. As contas comprometidas geralmente oferecem privilégios administrativos em ambientes corporativos.
Os agentes de ameaças percorrem segmentos de rede para identificar infraestruturas críticas e repositórios de dados de alto valor. As ferramentas de escalonamento de privilégios permitem um acesso mais profundo a controladores de domínio, servidores de arquivos e sistemas de backup.
Dados confidenciais, como registros financeiros, propriedade intelectual e bancos de dados de clientes, são copiados para a infraestrutura controlada pelo atacante. Conjuntos de dados roubados servem como alavanca caso os pedidos de resgate sejam rejeitados.
As cargas de ransomware criptografam endpoints, servidores e compartilhamentos de rede usando algoritmos criptográficos fortes. As chaves de decodificação permanecem controladas pelos atacantes enquanto aguardam o pagamento da criptomoeda.
Sites de vazamento dedicados hospedados em redes da dark web publicam amostras de dados roubados para demonstrar autenticidade. As ameaças de divulgação total aumentam os danos à reputação, a exposição regulatória e a responsabilidade legal.
O ransomware de extorsão dupla aumenta o impacto ao combinar a interrupção operacional com a exposição à violação de dados.
Vários grupos de ransomware operacionalizaram táticas de dupla extorsão para aumentar a conformidade com o resgate e a pressão pública.
A Maze lançou sites públicos de vazamento em novembro de 2019 para expor dados corporativos roubados após a recusa do resgate. A publicação dos dados das vítimas estabeleceu um novo modelo de coerção posteriormente adotado em ecossistemas de ransomware.
O REvil conduziu ataques corporativos e de cadeia de suprimentos em grande escala usando criptografia combinada com ameaças de vazamento de dados. Campanhas direcionadas a provedores de serviços gerenciados demonstraram como a dupla extorsão pode ampliar a disrupção sistêmica.
A Conti operou equipes internas estruturadas responsáveis pela intrusão, negociação e publicação de dados. Vazamentos internos de bate-papo revelaram fluxos de trabalho organizados de extorsão e estratégias de pagamento formalizadas.
A LockBit aproveitou um modelo de ransomware como serviço para distribuir recursos de dupla extorsão aos afiliados. Portais de vazamento dedicados exibiram publicamente conjuntos de dados roubados para pressionar o pagamento rápido de criptomoedas.
O ransomware de extorsão tripla expande as táticas de extorsão dupla ao introduzir uma camada adicional de coerção além da criptografia e do roubo de dados. Os atacantes exigem pagamento pela decodificação, prevenção de vazamentos de dados e mitigação de um terceiro mecanismo de pressão.
A pressão adicional geralmente inclui ataques distribuídos de negação de serviço contra infraestrutura voltada para o público ou ameaças diretas a clientes e parceiros de negócios. Alguns grupos entram em contato diretamente com as partes interessadas para ampliar os danos à reputação e a urgência da negociação.
A escalada da extorsão dupla para tripla reflete a evolução contínua nas estratégias de monetização de ransomware. A pressão em várias camadas aumenta a exposição financeira e complica a resposta a incidentes nas organizações afetadas.
A prevenção do ransomware de extorsão dupla exige controles de segurança em camadas que abordem o acesso, a detecção, a contenção e a recuperação.
A arquitetura Zero Trust impõe a verificação contínua de identidade entre usuários, dispositivos e recursos de rede. O acesso com menos privilégios reduz o movimento lateral e limita o alcance do invasor em ambientes corporativos.
As soluções de EDR monitoram o comportamento dos terminais para detectar padrões incomuns de criptografia e atividades de escalonamento de privilégios. A análise comportamental permite uma contenção rápida antes que ocorra a exfiltração de dados em grande escala.
A segmentação da rede isola os sistemas críticos dos ambientes gerais do usuário. O fluxo restrito de tráfego interno impede que os invasores acessem servidores de alto valor após o comprometimento inicial.
Backups off-line e imutáveis garantem a restauração dos dados sem depender do pagamento de resgate. Os testes regulares de recuperação validam a integridade do backup e os cronogramas de restauração.
Simulações de phishing e educação contínua em segurança cibernética reduzem o risco de comprometimento de credenciais. A defesa centrada no ser humano continua sendo fundamental contra os pontos de entrada da engenharia social.
A contenção imediata, a investigação e a comunicação estruturada determinam a gravidade do impacto durante um incidente de ransomware de dupla extorsão.
Desconecte terminais, servidores e segmentos de rede infectados para evitar uma maior disseminação. Desative as credenciais comprometidas e bloqueie o tráfego malicioso de comando e controle.
Inicie protocolos internos de resposta a incidentes e envolva especialistas externos em segurança cibernética, se necessário. Preserve evidências forenses, incluindo registros, capturas de memória e imagens do sistema.
Avalie quais arquivos, bancos de dados e registros foram acessados ou transferidos. Determine a exposição de informações regulamentadas, como dados financeiros, de saúde ou pessoais.
Consulte um advogado para avaliar as obrigações de comunicação de acordo com as leis de proteção de dados aplicáveis. Envie as notificações de violação necessárias dentro dos prazos obrigatórios.
Prepare divulgações controladas para clientes, parceiros e funcionários. A comunicação transparente reduz a especulação e limita os danos à reputação.
Reconstrua a infraestrutura afetada usando backups limpos verificados após a validação de segurança. Fortaleça os controles de acesso e os recursos de monitoramento antes da restauração operacional completa.
A proteção eficaz contra ransomware requer recursos integrados que evitem intrusões, detectem comportamentos maliciosos e contenham a exfiltração de dados.
Os sistemas de segurança devem monitorar continuamente o tráfego da rede, a atividade dos terminais e os padrões de autenticação. O alerta imediato reduz o tempo de permanência do atacante antes do início da criptografia.
Mecanismos de análise avançados detectam anomalias, como acesso incomum a arquivos ou tentativas de escalonamento de privilégios. A detecção comportamental identifica padrões de ransomware além dos métodos baseados em assinaturas.
O monitoramento do tráfego de saída evita transferências de dados não autorizadas para a infraestrutura externa. A detecção de exfiltração reduz a alavancagem disponível para dupla extorsão.
A contenção automatizada isola dispositivos comprometidos sem demora manual. A resposta rápida limita o movimento lateral nas redes corporativas.
Os backups devem permanecer off-line ou à prova de adulteração para evitar a criptografia ou a exclusão por atacantes. Testes regulares garantem uma capacidade de restauração confiável.
As trilhas de auditoria integradas apoiam a documentação regulatória e as obrigações de comunicação de violações. Os relatórios estruturados simplificam a investigação pós-incidente e a revisão legal.
As plataformas modernas de cibersegurança reduzem o risco de dupla extorsão por meio de visibilidade unificada, resposta automatizada e detecção baseada em inteligência.
As plataformas integradas combinam proteção de terminais, monitoramento de rede, segurança de identidade e defesa na nuvem em um único ecossistema. A visibilidade centralizada reduz os pontos cegos explorados durante o movimento lateral.
Os feeds de inteligência de ameaças em tempo real identificam a infraestrutura conhecida de ransomware, domínios maliciosos e táticas emergentes de atacantes. A correlação de inteligência melhora a detecção precoce antes da implantação da criptografia.
Os modelos de aprendizado de máquina detectam padrões de criptografia anormais, atividade de preparação de dados e transferências externas incomuns. A análise comportamental fortalece a defesa contra variantes de ransomware de dia zero.
Os centros de operações de segurança utilizam o monitoramento contínuo para reduzir o tempo de permanência do invasor. Ações rápidas de contenção evitam a criptografia generalizada e a exfiltração de dados em grande escala.
O isolamento automatizado de terminais restringe os dispositivos comprometidos sem atrasos manuais. Os controles em nível de rede bloqueiam os canais de comunicação de comando e controle.
A classificação abrangente de dados identifica ativos confidenciais em ambientes corporativos. Os controles de governança restringem o acesso não autorizado a repositórios de alto valor.
O ransomware de extorsão dupla representa uma grande evolução na extorsão cibernética ao combinar criptografia com roubo deliberado de dados e ameaças de exposição pública. A interrupção operacional por si só não define mais o impacto do ransomware, já que a responsabilidade regulatória e os danos à reputação agora amplificam o risco financeiro.
A resiliência contra a dupla extorsão exige controles de segurança em camadas, monitoramento contínuo, forte governança de acesso e recursos testados de resposta a incidentes. As organizações que priorizam a prevenção, a detecção e a recuperação segura reduzem a exposição a um dos modelos de ransomware mais agressivos da cibersegurança moderna.
