🚀 A CloudSEK se torna a primeira empresa de segurança cibernética de origem indiana a receber investimentos da Estado dos EUA fundo
Leia mais
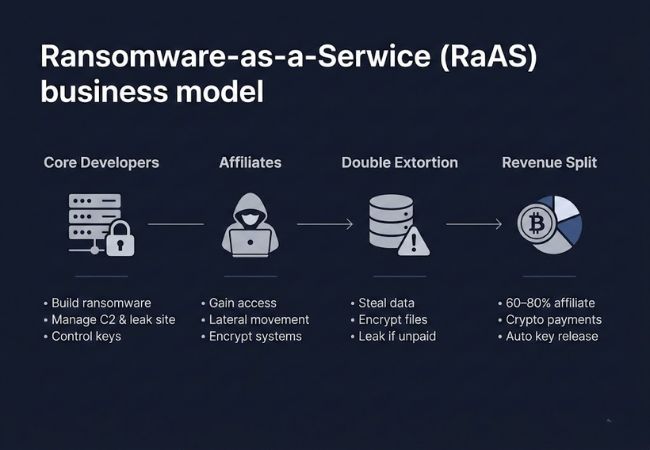
O Ransomware-as-a-Service (RaaS) é um modelo de negócios de crime cibernético em que os desenvolvedores de ransomware criam e mantêm software malicioso e, em seguida, o alugam para afiliados que realizam ataques. Os afiliados implantam o ransomware contra as vítimas e compartilham uma porcentagem dos pagamentos do resgate com as operadoras.
A separação clara entre desenvolvimento e execução distingue o RaaS das campanhas tradicionais de ransomware. Essa divisão de trabalho aumenta a escala, permitindo que uma única variedade de ransomware potencialize dezenas de ataques simultaneamente em diferentes regiões e setores.
Os incentivos de participação nos lucros impulsionam a inovação contínua nos ecossistemas RaaS. Atualizações contínuas, aprimoramentos de criptografia e técnicas de evasão garantem que o malware permaneça eficaz contra as defesas de segurança modernas.
O RaaS opera por meio de um ecossistema coordenado com funções operacionais claramente definidas.
As plataformas RaaS dependem de uma infraestrutura especializada que permite a implantação escalável de ataques e o controle centralizado.
As ferramentas personalizadas do construtor permitem que os afiliados gerem executáveis de ransomware com parâmetros de criptografia ajustáveis, tipos de arquivos direcionados e instruções de resgate incorporadas. As técnicas de geração polimórfica modificam as assinaturas dos arquivos para evitar os mecanismos de detecção baseados em antivírus e assinaturas.
A infraestrutura de comando e controle coordena as máquinas infectadas e transmite chaves de criptografia durante a execução. Os canais de comunicação criptografados reduzem a probabilidade de interceptação no nível da rede e rastreamento forense.
Sites dedicados a vazamentos hospedam conjuntos de dados roubados e publicam nomes de vítimas para exercer pressão pública. Cronômetros de contagem regressiva e divulgações em etapas aumentam a urgência da negociação e o risco de reputação.
Os portais de pagamento de criptomoedas orientam as vítimas por meio da transferência de resgate usando carteiras Bitcoin ou Monero. Os sistemas de verificação automatizados confirmam as transações de blockchain antes de liberar os utilitários de decodificação.
As chaves criptográficas por vítima são geradas para impedir o desenvolvimento universal de decodificadores. Bancos de dados seguros de back-end armazenam material importante até que a confirmação do resgate acione a liberação controlada.
Os ataques RaaS seguem um ciclo de vida de intrusão estruturado projetado para maximizar a alavancagem e a recuperação do resgate.
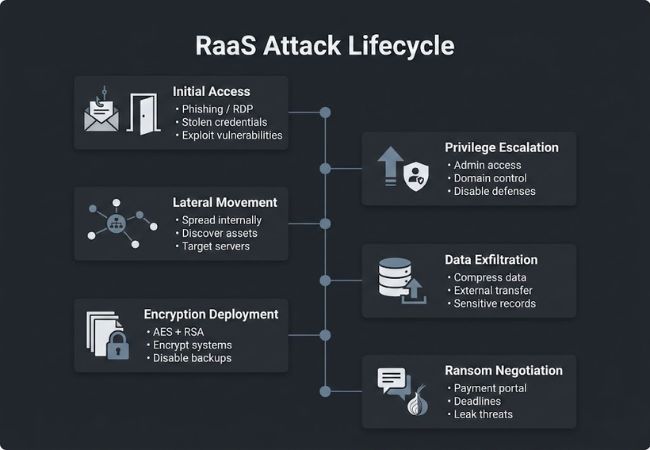
A entrada é obtida por meio de e-mails de phishing, serviços expostos do Protocolo de Área de Trabalho Remota, preenchimento de credenciais ou vulnerabilidades em aplicativos voltados para a Internet. Os corretores de acesso inicial geralmente vendem credenciais de rede pré-comprometidas para acelerar os cronogramas de implantação.
Os invasores exploram configurações incorretas ou sistemas não corrigidos para obter privilégios administrativos. O acesso elevado permite o controle sobre controladores de domínio, servidores de backup e sistemas de gerenciamento de segurança.
As credenciais comprometidas e as ferramentas de administração remota permitem a disseminação pelas redes internas. As ferramentas de descoberta identificam ativos de alto valor, como servidores de arquivos, bancos de dados e ambientes virtualizados.
Os dados confidenciais são compactados e transferidos para servidores externos antes do início da criptografia. Propriedade intelectual, registros financeiros e informações de identificação pessoal são priorizados para alavancagem.
As cargas de ransomware criptografam arquivos críticos usando algoritmos criptográficos fortes, como o AES, combinados com o agrupamento de chaves RSA. Os pontos de restauração do sistema e os serviços de backup geralmente são desativados para evitar uma fácil recuperação.
As vítimas são direcionadas para portais baseados em TOR, onde os canais de comunicação facilitam as discussões sobre pagamentos. Prazos e ameaças de vazamento intensificam a pressão durante as etapas de negociação.
O RaaS separa o desenvolvimento de malware da execução de ataques, permitindo operações escaláveis e estruturas comerciais que faltam aos ransomwares tradicionais.
O Ransomware-as-a-Service depende de operadores organizados que fornecem malware, infraestrutura e redes afiliadas para executar ataques globalmente. Cada grupo se diferencia por meio de táticas, metas e inovações técnicas.
A REvil iniciou suas operações em 2019 e rapidamente construiu uma rede global de afiliados. Os operadores gerenciam as chaves de criptografia e negociam resgates enquanto monitoram o progresso de cada ataque. As atualizações contínuas aprimoram as técnicas de evasão e mantêm a eficácia do malware.
O LockBit foi lançado em 2019 e ficou conhecido por seu programa automatizado de afiliados e implantação rápida de ataques. Painéis centralizados rastreiam infecções e pagamentos de resgate, garantindo a eficiência operacional. Atualizações frequentes de código sustentam a resiliência contra a proteção moderna de terminais.
DarkSide apareceu publicamente em maio de 2021 após o ataque do Colonial Pipeline. O grupo coordena o movimento lateral e a exfiltração de dados enquanto controla os procedimentos de criptografia e vazamento. O sigilo operacional protege tanto os operadores quanto os afiliados durante campanhas de alto perfil.
A Conti tornou-se ativa em 2020, com foco em redes de saúde, educação e governo. Os operadores supervisionam o desempenho dos afiliados e refinam o malware para contornar as ferramentas de detecção. O monitoramento das cobranças de resgate garante uma execução tranquila da campanha.
O Hive surgiu em 2021, visando forças de trabalho remotas e serviços baseados em nuvem. Painéis e sistemas de monitoramento rastreiam as taxas de infecção e o status do pagamento, enquanto as ferramentas de decodificação automatizadas simplificam a resposta. Os portais públicos de vazamento mantêm uma dupla influência de extorsão sobre as vítimas.
O LockBit Black surgiu em 2022 como uma evolução do ecossistema LockBit com criptografia mais rápida e evasão avançada. As atualizações contínuas aprimoram as ferramentas para detecção e prevenção, e os portais de vazamento pressionam as vítimas não pagantes. Modelos de pagamento baseados em desempenho recompensam afiliados de alto desempenho.
A Royal surgiu em meados de 2022, priorizando serviços RDP expostos e sistemas legados para um rápido comprometimento. As chaves de decodificação são gerenciadas com segurança e a extorsão dupla é aplicada por meio de portais de vazamento. O monitoramento da conformidade do resgate garante um controle operacional estruturado.
O ransomware como serviço continua se expandindo devido à automação, especialização e incentivos financeiros que reduzem as barreiras para os cibercriminosos. Fatores tecnológicos e econômicos agora permitem que operadoras e afiliadas escalem ataques com mais eficiência do que nunca.
As campanhas de phishing com inteligência artificial criam e-mails convincentes que aumentam as taxas de comprometimento da rede. Os scripts automatizados identificam endpoints vulneráveis e priorizam ativos de alto valor para os afiliados.
Os corretores de crimes cibernéticos vendem credenciais pré-comprometidas, permitindo uma implantação mais rápida para afiliados. Contas RDP expostas, credenciais de VPN e detalhes de login na nuvem reduzem os prazos de ataque e aumentam a eficiência operacional.
As plataformas RaaS separam o desenvolvimento da execução, permitindo que vários afiliados implantem o mesmo ransomware simultaneamente. Os operadores gerenciam servidores C2, portais de vazamento e painéis, enquanto os afiliados se concentram na movimentação lateral e na negociação de resgate.
Os modelos de participação nos lucros recompensam os afiliados com base em cobranças de resgate bem-sucedidas. Os pagamentos de criptomoedas usando Bitcoin e Monero mantêm o anonimato, enquanto a liberação controlada da chave de decodificação impõe acordos de receita.
Grupos modernos de RaaS combinam criptografia com roubo de dados para pressionar as vítimas. Portais públicos de vazamentos e divulgações em etapas maximizam a alavancagem regulatória e de reputação.
As operadoras utilizam a IA para escanear redes em busca de configurações incorretas e vulnerabilidades não corrigidas. Esse reconhecimento automatizado acelera a seleção de alvos e aumenta as taxas de sucesso do ataque.
As operações de RaaS abrangem setores em todo o mundo, incluindo saúde, finanças, manufatura e governo. Os operadores coordenam afiliados em todas as regiões, otimizando o impacto dos ataques e a arrecadação de receita.
A defesa eficaz contra o RaaS exige segurança em camadas, monitoramento contínuo e estratégias de resposta proativa. As organizações devem abordar as vulnerabilidades técnicas e os fatores humanos para reduzir a exposição.
A implementação da MFA fortalece os controles de acesso em endpoints, serviços em nuvem e conexões remotas. As credenciais comprometidas se tornam menos eficazes, limitando o acesso inicial dos afiliados.
As plataformas Advanced Endpoint Detection and Response (EDR) identificam comportamentos incomuns de criptografia de arquivos e movimentos laterais em tempo real. O rápido isolamento dos sistemas afetados evita o impacto generalizado e a exfiltração de dados.
Backups off-line regulares garantem que as organizações possam recuperar arquivos essenciais sem pagar resgate. O armazenamento imutável e os exercícios de recuperação automatizados reduzem o tempo de inatividade e as perdas financeiras.
As políticas do Zero Trust restringem o movimento lateral e impõem uma verificação rigorosa para cada dispositivo, usuário e aplicativo. A segmentação limita a propagação do ransomware, mesmo que ocorra uma violação inicial.
O treinamento contínuo de phishing e engenharia social capacita os funcionários a detectar campanhas maliciosas. A vigilância humana complementa as defesas técnicas e reduz a superfície geral de ataque.
O ransomware como serviço transformou o cibercrime em um ecossistema escalável, semelhante ao de negócios, com alcance global. Compreender a mecânica, a infraestrutura e o ciclo de vida operacional do RaaS em 2026 ajuda as organizações a implementar defesas proativas e reduzir a exposição.
Investir em segurança em camadas, conscientização dos funcionários e monitoramento em tempo real capacita as empresas a mitigar os ataques de forma eficaz. Manter-se informado sobre as ameaças em evolução garante resiliência contra campanhas modernas de ransomware.
Os operadores geralmente anunciam em fóruns clandestinos ou canais privados e examinam possíveis afiliados em busca de habilidades técnicas e confiabilidade. O recrutamento garante que somente participantes confiáveis possam acessar a infraestrutura de ransomware.
Os corretores vendem credenciais pré-comprometidas e acesso à rede aos afiliados. Isso permite que os invasores ignorem as etapas iniciais de intrusão e se concentrem na implantação do ransomware.
Os grupos usam canais de comunicação criptografados, transações anônimas de criptomoedas e infraestrutura segmentada. Essas medidas protegem tanto as operadoras quanto as afiliadas da detecção policial.
Setores de alto valor, como saúde, finanças, infraestrutura crítica e provedores de serviços gerenciados, são frequentemente alvos. Organizações com controles de segurança fracos ou acesso remoto exposto enfrentam riscos maiores.
As autoridades apreendem servidores, portais de pagamento e sites de vazamento enquanto coordenam globalmente com equipes de segurança cibernética. A interrupção interrompe temporariamente as operações, mas os afiliados geralmente se adaptam para continuar os ataques em outros lugares.
