🚀 A CloudSEK se torna a primeira empresa de segurança cibernética de origem indiana a receber investimentos da Estado dos EUA fundo
Leia mais
A Ameaça Persistente Avançada é um ataque cibernético altamente direcionado, projetado para manter o acesso prolongado à rede de uma organização. Os atacantes visam exfiltrar informações confidenciais, manipular sistemas ou interromper operações sem serem detectados.
Os alvos comuns incluem redes governamentais, instituições financeiras, sistemas de saúde e infraestrutura de energia. As técnicas geralmente envolvem malware personalizado, e-mails de spear-phishing, explorações de dia zero e acesso secreto à rede para permanecerem ocultos.
As campanhas da APT são definidas pela persistência, planejamento cuidadoso e operações furtivas. Eles confiam na inteligência de ameaças, no movimento lateral nas redes e na extração sistemática de dados para atingir objetivos de longo prazo.
Os ataques de APT seguem um processo estruturado que permite que os atacantes permaneçam sem serem detectados enquanto extraem informações valiosas. Cada estágio se baseia no anterior para manter o acesso e o controle de longo prazo.
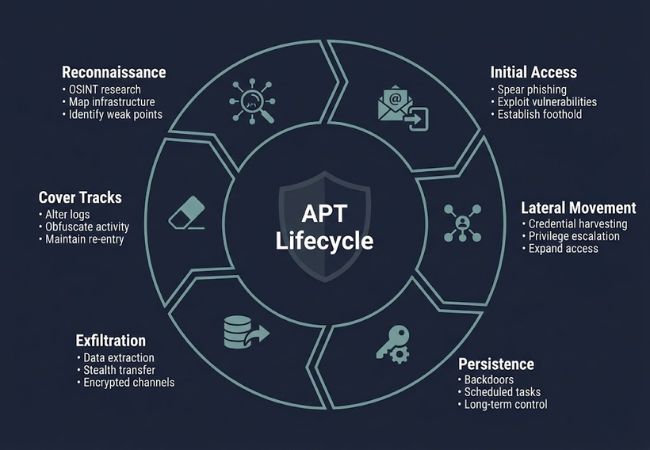
Durante essa fase, os atacantes coletam informações sobre a organização alvo, incluindo arquitetura de rede, funções dos funcionários e vulnerabilidades do sistema. Ferramentas de pesquisa, engenharia social e escaneamento de código aberto ajudam a identificar pontos fracos antes de lançar um ataque.
Os invasores entram por meio de métodos como spear-phishing, exploração de vulnerabilidades não corrigidas ou implantação de malware. O objetivo é estabelecer uma posição na rede sem acionar alertas de segurança.
Uma vez lá dentro, os invasores navegam pela rede para acessar sistemas adicionais e dados confidenciais. Técnicas como escalonamento de privilégios, exploração remota de desktops e coleta de credenciais permitem uma penetração mais profunda.
Os invasores mantêm o acesso de longo prazo usando backdoors, tarefas agendadas ou malware que evita a detecção. A presença contínua garante que os dados possam ser exfiltrados ou os sistemas manipulados ao longo de meses ou até anos.
Os dados ou a propriedade intelectual são extraídos da rede e transmitidos para servidores externos. Criptografia, métodos de transferência furtivos e táticas de direcionamento incorreto minimizam a chance de descoberta pelas equipes de segurança.
Os atacantes removem ou ofuscam evidências de suas atividades para atrasar a detecção e a análise forense. Os registros podem ser alterados, o malware disfarçado e os pontos de acesso mantidos para possíveis ataques futuros.
Os ataques de APT dependem de vários elementos coordenados para obter acesso a longo prazo e exfiltração de dados. A compreensão desses componentes ajuda as organizações a detectar e mitigar ameaças com mais eficiência.
O malware personalizado forma a espinha dorsal de muitas operações do APT. Spywares, trojans e keyloggers geralmente são implantados para monitorar sistemas, capturar credenciais e manter o acesso oculto.
Os atacantes usam vários vetores para entrar nas redes, incluindo e-mails de spear-phishing, atualizações de software infectados e exploração de vulnerabilidades não corrigidas. A combinação de vários vetores aumenta as chances de uma violação bem-sucedida.
Os servidores C2 permitem que os invasores gerenciem remotamente os sistemas comprometidos. Comunicações criptografadas e redes proxy ajudam a manter a discrição ao enviar comandos e receber dados extraídos.
Os alvos de alto valor geralmente incluem bancos de dados, registros financeiros, repositórios de propriedade intelectual e sistemas essenciais de tecnologia operacional. O acesso a esses sistemas fornece o máximo impacto para os atacantes, permanecendo sob o radar.
As ferramentas de exfiltração garantem que os dados roubados saiam da rede sem serem detectados. As técnicas incluem transferências criptografadas, movimentos disfarçados de arquivos e uso de serviços em nuvem para mascarar atividades.
Os ataques APT representam uma ameaça única devido à sua persistência e capacidade de operar sem serem detectados por longos períodos. Métodos furtivos permitem que os invasores acessem continuamente sistemas críticos sem acionar alertas de segurança.
Dados confidenciais, incluindo propriedade intelectual, registros financeiros e informações pessoais, podem ser exfiltrados com o tempo, causando danos operacionais e econômicos significativos. A presença persistente também permite que os atacantes manipulem sistemas, interrompam serviços ou se preparem para ataques futuros.
A infiltração de longo prazo por APTs pode ter consequências estratégicas para setores específicos, como governo, finanças, saúde e energia. As organizações enfrentam não apenas perdas imediatas, mas também danos à reputação e possíveis penalidades regulatórias quando violações são descobertas.
Os grupos APT são agentes de ameaças organizados que realizam campanhas cibernéticas sofisticadas e de longo prazo. Compreender suas características, métodos e metas ajuda as organizações a se anteciparem e se defenderem contra possíveis ataques.
A detecção de APTs exige vigilância constante para identificar sinais sutis de intrusão. A combinação de tecnologia, inteligência e políticas organizacionais melhora a capacidade de detectar e interromper ataques antes que dados críticos sejam perdidos.
As plataformas de inteligência de ameaças analisam métodos de ataque, assinaturas de malware e ameaças emergentes. A integração dessas informações permite que as equipes antecipem os ataques e respondam de forma proativa.
Compartilhar e atualizar feeds de ameaças garante a percepção em tempo real da evolução dos padrões de ataque. A colaboração entre organizações aprimora a detecção precoce de campanhas sofisticadas.
Firewalls, sistemas de detecção de intrusão (IDS) e ferramentas de monitoramento de rede rastreiam atividades incomuns. A análise baseada em comportamento pode sinalizar movimentos laterais, logins suspeitos ou transferências de dados inesperadas.
A segmentação das redes limita a propagação de invasores uma vez lá dentro. A verificação regular de vulnerabilidades identifica os pontos fracos antes que eles sejam explorados.
As soluções de EDR e o software antivírus protegem os dispositivos contra malware e acesso não autorizado. O monitoramento contínuo dos endpoints ajuda a detectar ferramentas furtivas usadas em campanhas de APT.
O gerenciamento de patches e o fortalecimento de dispositivos reduzem as vulnerabilidades em estações de trabalho, servidores e dispositivos móveis. Os alertas de endpoint alimentam sistemas de detecção mais amplos para uma resposta coordenada.
A autenticação multifatorial e o gerenciamento estrito de privilégios evitam o acesso não autorizado. A revisão regular das permissões garante que os usuários tenham apenas o acesso necessário.
O treinamento de funcionários sobre phishing, engenharia social e higiene de senhas fortalece as defesas contra pontos de entrada frequentemente explorados por APTs.
Planos definidos de resposta a incidentes permitem contenção e investigação rápidas. A ação oportuna minimiza o impacto das violações e ajuda a restaurar as operações normais.
Testes regulares, backups e prontidão forense garantem que as organizações possam se recuperar rapidamente e manter a continuidade dos negócios. As lições aprendidas contribuem para melhorar as defesas futuras.
Implemente monitoramento constante de rede e endpoint para detectar atividades incomuns. A identificação precoce de anomalias pode impedir o acesso prolongado não autorizado.
Implemente software antivírus, ferramentas de detecção e resposta de terminais (EDR) e scanners de malware. Proteger estações de trabalho, servidores e dispositivos móveis reduz as superfícies de ataque para APTs.
Integre feeds de inteligência de ameaças para se manter informado sobre padrões de ataque emergentes e assinaturas de malware. Aproveitar os insights em tempo real permite que as organizações antecipem os ataques e respondam de forma proativa.
Use autenticação multifatorial, controle estrito de privilégios e revisões regulares de permissões. Limitar o acesso desnecessário reduz o risco de movimento lateral dos atacantes.
Eduque a equipe sobre práticas de phishing, engenharia social e senhas seguras. A consciência humana fortalece as defesas organizacionais contra os métodos comuns de entrada no APT.
Desenvolva um plano estruturado de resposta a incidentes com funções e procedimentos definidos. Testar o plano regularmente garante contenção, investigação e recuperação rápidas durante violações.
Mantenha backups regulares e criptografados de dados e sistemas críticos. Isso garante que as organizações possam se recuperar rapidamente em caso de exfiltração ou ransomware.
Aplique patches, atualizações e configurações de segurança de forma consistente em todos os dispositivos e servidores. Reduzir as vulnerabilidades torna mais difícil para os invasores explorarem os sistemas.
As ameaças persistentes avançadas (APTs) podem comprometer as redes por meses ou anos, causando graves perdas de dados e interrupções operacionais. As organizações precisam de monitoramento robusto, segurança em camadas e análise proativa de ameaças para detectar e impedir ataques.
O conhecimento dos métodos de ataque, das vulnerabilidades do sistema e das técnicas de exfiltração ajuda a implementar defesas eficazes. Atualizações regulares, políticas de acesso seguro e vigilância dos funcionários reduzem o risco de infiltração a longo prazo.
Os APTs são altamente direcionados e de longo prazo, usando métodos furtivos para permanecer dentro das redes, enquanto os ataques regulares costumam ser oportunistas e de curta duração.
Sim, os atacantes podem atacar pequenas empresas como parte de ataques à cadeia de suprimentos ou para acessar redes maiores de parceiros.
As campanhas do APT podem permanecer ocultas por meses ou até anos, dependendo da habilidade do atacante e das defesas da rede.
Não, embora muitos estejam vinculados a atores do estado-nação, alguns são motivados financeiramente ou dirigidos por grupos de crimes cibernéticos organizados.
A combinação de inteligência contra ameaças, monitoramento proativo, treinamento de funcionários e um plano robusto de resposta a incidentes reduz significativamente o risco.
