🚀 CloudSEK becomes first Indian origin cybersecurity company to receive investment from US state fund
Read more
An enterprise threat intelligence solution is a cybersecurity system built to collect, process, and operationalize threat data across large-scale infrastructures. Security teams rely on it to gain visibility into adversary behavior, attack techniques, and evolving risk patterns.
Data flows into the system from network telemetry, endpoint activity, and external threat feeds, forming a unified intelligence layer. Correlation and enrichment processes surface indicators of compromise (IoCs), behavioral signals, and attack patterns aligned with frameworks such as MITRE ATT&CK.
Integration with SIEM, SOAR, and EDR platforms enables intelligence to drive detection and automated response workflows. Security operations teams use these insights to prioritize critical threats, reduce dwell time, and maintain a continuously adaptive defense posture.
Enterprise threat intelligence solutions function as a connected system where data is continuously collected, analyzed, and turned into operational decisions. Each component builds on the previous stage, allowing raw signals to evolve into actionable security intelligence.
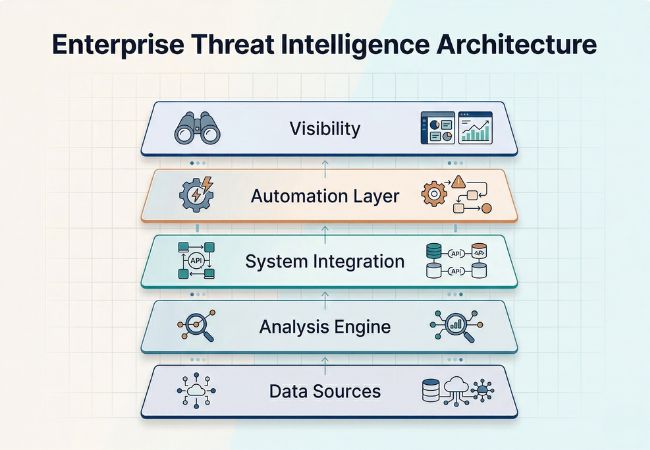
Security data originates from endpoints, network traffic, cloud environments, and external intelligence sources, forming the foundation of the system. Coverage across these layers ensures that no single point of activity remains isolated or invisible.
Collected data moves into analysis pipelines where it is processed, enriched, and examined for indicators of compromise and behavioral anomalies. Patterns begin to emerge at this stage, linking seemingly unrelated events into meaningful threat signals.
Analyzed intelligence does not remain isolated and instead feeds directly into SIEM, SOAR, and EDR platforms that manage detection and response. Security operations gain contextual depth as alerts become enriched with intelligence rather than raw event data.
Integrated systems use this intelligence to trigger predefined actions, allowing faster containment and remediation of threats. Response workflows adapt based on threat severity, reducing delays that typically occur with manual intervention.
Outputs are presented through dashboards and reports that highlight prioritized risks, ongoing threats, and historical trends. Decision-making becomes more precise as security teams operate with context rather than fragmented alerts.
Security operations rely on SIEM, SOAR, and threat intelligence working as a connected system where data, context, and response continuously reinforce each other.
Operational decisions become more accurate when threat intelligence connects alerts with attacker behavior, risk, and real-world context.
Security teams gain clarity on which threats matter most as intelligence maps alerts to real attacker tactics and campaigns. Alignment with frameworks like MITRE ATT&CK allows risks to be evaluated based on real-world relevance instead of isolated signals.
Raw alerts generated by SIEM systems become more meaningful once enriched with threat intelligence context. Indicators of compromise and behavioral patterns help filter out benign activity, significantly lowering false positives.
Actionable intelligence feeds directly into SOAR workflows, enabling quicker containment and remediation of active threats. Response decisions rely on verified threat context rather than manual investigation, reducing delays during critical incidents.
Integration with EDR, SIEM, and automation systems allows security teams to handle increasing threat volumes without proportional resource expansion. Intelligence-driven workflows replace repetitive analysis, improving efficiency across the SOC.
Long-term visibility into adversary behavior, attack trends, and threat evolution supports better security planning. Organizations strengthen their posture by adapting controls, detection rules, and response strategies based on continuously evolving intelligence.
Emerging threats are identified earlier as intelligence highlights attacker infrastructure, tactics, and campaigns before they fully execute. Security teams shift from reacting to incidents toward anticipating and preventing them.
Business risk becomes clearer as threat intelligence connects technical indicators with potential impact on assets, data, and operations. Security decisions align more closely with enterprise priorities rather than isolated security events.
Evaluation becomes meaningful only when intelligence is tested against real alerts, ongoing investigations, and response activity inside the environment.
Early testing usually exposes whether intelligence aligns with what the organization is already seeing across endpoints, network activity, and cloud telemetry. Gaps appear quickly when external signals fail to match internal observations.
Attention shifts to how intelligence behaves during triage and investigation, especially under time pressure. Anything that requires extra steps or context switching tends to slow analysts down instead of helping them.
Large volumes of indicators often create more noise than clarity. Value comes from intelligence that highlights relevant threats and reduces the effort needed to separate real risk from background activity.
Practical usefulness becomes clear during incident scenarios where intelligence either supports containment decisions or adds friction. Systems that connect insight directly to action stand out immediately.
Short evaluations rarely reflect long-term performance, as intelligence quality can vary across different threat situations. Teams tend to trust solutions that remain reliable across multiple use cases and time periods.
Selection decisions usually begin with understanding where intelligence will make a measurable difference, especially in environments already handling large volumes of alerts and security signals.
Initial focus stays on whether the intelligence reflects real exposure across critical assets, users, and external dependencies. Gaps become visible when threat coverage does not match the organization’s actual risk profile.
Once relevance is established, attention shifts to whether the intelligence can support high-impact decisions during incidents. Inconsistent or unclear insights tend to create hesitation at the exact moment when speed matters.
As evaluation progresses, the question becomes how intelligence fits into existing detection and response layers. Systems that fail to influence alerting and investigation workflows often remain underutilized.
Integration alone is not enough if it increases the burden on security teams. Additional effort in validation, tuning, or enrichment quickly reduces the practical value of the solution.
Over time, threat patterns change, and intelligence must keep pace with evolving attacker behavior and infrastructure. Systems that cannot adapt lose relevance even if they perform well initially.
Short-term performance can appear reliable during controlled testing, but variation across different threat scenarios reveals long-term stability. Consistent intelligence builds trust across both analysts and leadership.
At this stage, confidence also depends on how clearly the vendor explains data sources, update cycles, and coverage limitations. Lack of transparency often leads to uncertainty in critical situations.
Final decisions usually connect intelligence capabilities to business outcomes such as downtime risk, compliance exposure, and financial impact. Solutions that bridge technical signals with business context carry more strategic value.
Enterprise security has shifted from reactive monitoring to intelligence-driven operations where context determines how quickly threats are understood and contained. Enterprise threat intelligence solutions enable this shift by connecting signals, behavior, and risk into a single operational view.
Security teams benefit most when intelligence integrates directly into detection and response workflows, reducing noise and improving decision speed. An enterprise threat intelligence solution like CloudSEK demonstrates how real-time insights and contextual analysis can strengthen both tactical response and long-term security posture.
Long-term value depends on consistency, adaptability, and alignment with evolving threat landscapes and business priorities. Organizations that operationalize intelligence effectively build resilience, reduce exposure, and maintain control over increasingly complex attack surfaces.
