🚀 CloudSEK becomes first Indian origin cybersecurity company to receive investment from US state fund
Read more
A scam website can collect payment details or login credentials within seconds by imitating a legitimate online platform. Victims often realize the fraud only after unauthorized transactions or account access occurs.
Scam websites evolved from basic imitation pages and mass phishing emails into professionally designed clones of real businesses. Today, fraudsters use paid ads, social media distribution, and rapidly rotated domains to scale deception.
By late 2025, phishing activity remained at a critical level. The Anti-Phishing Working Group (APWG) recorded 853,244 phishing attacks in Q4 2025 alone, demonstrating how frequently users are directed to malicious credential-harvesting websites.
Scam websites are fraudulent online platforms designed to obtain money, personal information, or login credentials through deception. Operators build these sites to simulate legitimate businesses while concealing criminal intent.
Imitation branding, copied layouts, and manipulated payment systems create an appearance of authenticity. Visual credibility combined with urgency tactics increases the likelihood of user interaction and financial loss.
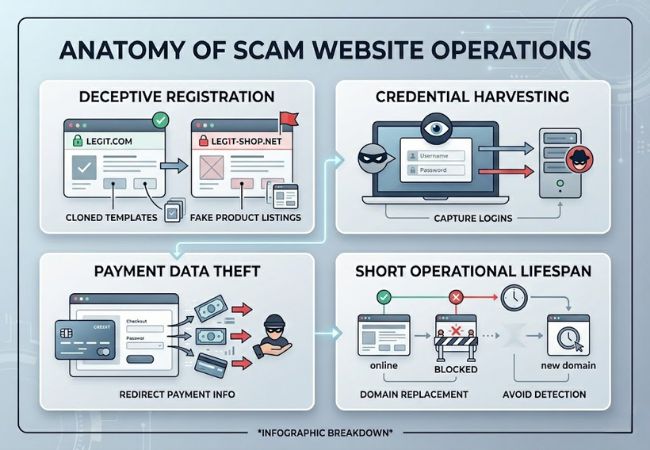
Fraudsters register deceptive domain names that resemble legitimate brands, often using minor spelling variations or alternative extensions. Cloned website templates and copied product listings reinforce perceived authenticity.
Credential harvesting forms a central objective, with fake login portals capturing usernames and passwords. Payment pages may transmit credit card data directly to attackers instead of processing legitimate transactions.
Short operational lifespans reduce detection risk, as domains disappear after reports or blacklisting. New domains replace shut-down sites quickly, allowing the fraud cycle to continue at scale.
Scam websites operate in multiple structured formats, each engineered to exploit a specific transaction point such as login authentication, online checkout, or financial investment.
Phishing websites clone legitimate sign-in pages for banks, email services, and SaaS platforms to capture credentials, one-time passcodes, and card details. High-quality replicas mirror branding, interface layout, and URL path structures so the page appears authentic even though the domain name is fraudulent.
In Canada, reported spear-phishing fraud losses exceeded $43 million in 2025, demonstrating how a single compromised login can escalate into wire fraud or payroll diversion in business environments.
Fake e-commerce websites imitate retail storefronts or limited-time outlet pages while promoting unrealistic discounts and artificial scarcity indicators. Payment submission becomes the primary objective, leading to non-delivery, counterfeit goods, or unauthorized reuse of card details.
Authorities in Singapore reported approximately $16.7 million lost to e-commerce scams in 2025, confirming that fraudulent checkout systems continue to generate significant financial damage despite awareness campaigns.
Investment and cryptocurrency scam platforms simulate professional trading dashboards with fabricated profit charts and staged withdrawal activity. Larger deposits are requested after trust is built, followed by blocked withdrawals justified through false “tax” or “verification” fees.
In Hong Kong, online investment fraud reached 5,135 reported cases in 2025 with losses totaling HK$3.58 billion, highlighting the scale of financial harm driven by fake digital investment environments.
Technical support scam pages use alarming malware warnings and full-screen system alerts to create urgency. Victims are directed to call fraudulent support numbers, where remote access and payment are requested under the pretense of resolving non-existent security issues.
Australia recorded $4.2 million in reported remote access scam losses between January and September 2025, indicating that device-based deception remains financially effective despite declining case numbers.
Donation scam websites appear during natural disasters or major public events, copying legitimate charity branding to attract rapid contributions. Collected funds rarely reach genuine relief organizations and may be followed by secondary impersonation attempts.
Australian Scamwatch data cited $1.4 million in reported losses to fake charity scams over recent years, reinforcing that crisis-linked fraud persists due to emotionally driven payment decisions.
Structured verification reduces the probability of interacting with fraudulent platforms during login, registration, or payment stages.

Examine the full URL carefully for spelling errors, added characters, unusual extensions, or brand variations. Search for the official website independently instead of relying on links from emails or advertisements.
Use a WHOIS lookup tool to check when the domain was registered. Recently created domains posing as established retailers or financial institutions require heightened scrutiny.
Click the browser padlock to view certificate details and issuing authority. Mismatched organization names or recently issued certificates for well-known brands indicate risk.
Search for independent reviews across multiple platforms and confirm consistent contact information. Legitimate businesses maintain verifiable addresses, phone numbers, and transparent corporate details.
Call the listed number or send a support inquiry before making payment. Non-functional numbers, delayed responses, or generic replies suggest operational concealment.
Avoid websites requesting wire transfers, cryptocurrency, or peer-to-peer payments without buyer protection. Legitimate online stores typically use secure payment gateways with dispute resolution mechanisms.
Enter the website URL into established website reputation services to identify known fraud reports. Prior scam complaints or blacklist flags provide critical warning signals.
Psychological triggers and technical imitation work together to lower suspicion and accelerate user decisions.
Recognizable logos, copied layouts, and familiar interface patterns create instant brand association. Visual similarity reduces friction during login or payment submission.
Countdown timers and low-stock alerts compress decision time. Accelerated choices limit independent verification and increase impulsive transactions.
Fabricated reviews and inflated ratings simulate customer validation. Perceived popularity increases trust even without legitimate user activity.
Professional templates, mobile optimization, and encrypted connections enhance surface credibility. High production quality masks anonymous ownership and fraudulent intent.
Financial loss and identity exposure represent the most immediate consequences of interacting with a fraudulent platform.
Login details entered on cloned portals are captured and reused for account takeover. Compromised email or banking access often leads to broader financial exploitation.
Card information submitted through fake checkout pages may be used for unauthorized transactions. Stolen payment data is frequently resold or reused across multiple fraudulent purchases.
Personal information such as full name, address, and phone number enables impersonation schemes. Fraud networks combine stolen data to open accounts or bypass security verification systems.
Hidden scripts or malicious downloads can infect devices during site interaction. Compromised systems may leak stored passwords, browser data, or financial credentials.
Preventive security requires structured verification habits and layered digital safeguards before any login or payment action.
Examine the full domain name carefully for spelling variations, added characters, or unusual extensions. Cross-check the official website address through independent search results rather than embedded links.
Enable Two-Factor Authentication (2FA) across banking, email, and business platforms. Additional verification layers significantly reduce account takeover risk even after credential exposure.
Use credit cards or protected payment gateways that support dispute resolution and chargeback mechanisms. Avoid wire transfers, cryptocurrency payments, or peer-to-peer transfers to unfamiliar sellers.
Search independent reviews across multiple platforms before submitting financial information. WHOIS lookup tools can reveal domain registration age and ownership signals.
Maintain updated operating systems, browsers, and endpoint protection software. Regular updates patch vulnerabilities that malicious scripts attempt to exploit.
Verification before payment reduces exposure to fraudulent checkout systems and credential harvesting.
Confirm exact spelling of the domain and review the full URL structure, not just the homepage label. Suspicious subdomains or extra characters often signal impersonation.
Select the browser padlock icon to inspect certificate details and issuing authority. Mismatched organization names or recently issued certificates require caution.
Search for independent company records, verified customer feedback, and consistent contact details across platforms. Absence of traceable business information increases risk probability.
Use WHOIS lookup tools to review domain registration history and creation date. Newly registered retail or investment sites demand higher scrutiny.
Confirm use of recognized payment gateways that support dispute mechanisms and transaction monitoring. Requests for direct transfers outside protected systems indicate elevated fraud risk.
Reporting a scam website helps disrupt fraudulent operations and reduces the likelihood of additional victims.
Capture screenshots of the website, including the full URL, checkout pages, and confirmation messages. Save transaction records, email communications, and any payment receipts linked to the interaction.
Notify your bank or card issuer immediately if payment information was submitted. Request transaction review, card replacement, and activation of fraud monitoring safeguards.
Submit a report through your national consumer protection or cybercrime reporting portal. Provide detailed information, including the website address, payment method used, communication history, and dates of activity.
Identify the domain registrar using a WHOIS lookup and file an abuse complaint. Registrars can suspend or investigate domains involved in fraudulent activity.
Submit the URL to browser security and safe browsing databases to trigger warning alerts for other users. Collective reporting accelerates blacklisting and reduces the site’s operational lifespan.
Continue reviewing financial statements and login history for suspicious behavior. Early detection of secondary fraud attempts minimizes extended damage.
Scam websites represent a persistent and evolving form of online fraud that targets both individuals and businesses across digital platforms. Professional design, psychological pressure, and technical imitation make detection more difficult than in earlier internet eras.
Consistent verification habits, layered authentication controls, and cautious payment behavior significantly reduce exposure to financial loss and identity compromise. Structured awareness, rather than reactive response, remains the strongest long-term defense against fraudulent websites.
Yes. HTTPS encryption protects data transmission but does not verify business legitimacy, and fraudulent operators can obtain basic SSL certificates.
Short domain lifespans reduce detection and enforcement pressure. Fraud networks often abandon flagged domains and relaunch identical sites under new web addresses.
Paid advertising does not guarantee legitimacy. Fraudulent websites can purchase ad placements to appear above legitimate search results.
Recovery depends on the payment method used and the speed of reporting. Credit card transactions generally offer stronger dispute protections than wire transfers or cryptocurrency payments.
Data may be collected through phishing emails, previous data breaches, or exposed personal information online. Stolen credentials are frequently reused across multiple fraud schemes.
