🚀 أصبحت CloudSek أول شركة للأمن السيبراني من أصل هندي تتلقى استثمارات منها ولاية أمريكية صندوق
اقرأ المزيد
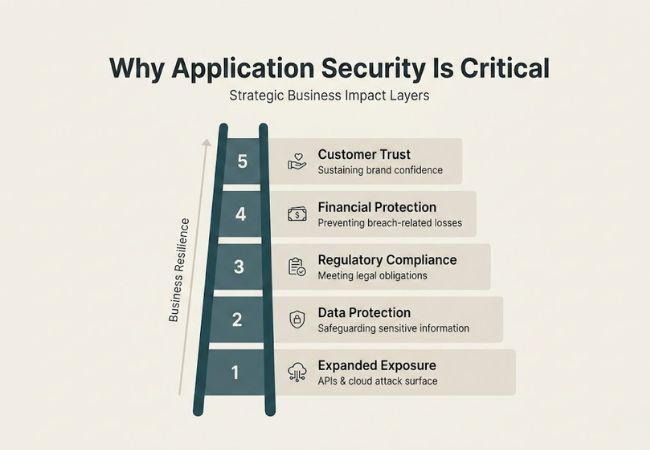
تعمل أفضل ممارسات أمان التطبيقات على حماية البرامج من الثغرات الأمنية عبر بيئات التطوير والنشر ووقت التشغيل. تعمل التطبيقات الحديثة عبر واجهات برمجة التطبيقات والأنظمة الأساسية السحابية والأنظمة الموزعة حيث يمكن أن تؤدي نقطة ضعف واحدة إلى كشف البيانات الهامة.
أدى تزايد تعقيد الهجمات وتوسع النظم البيئية الرقمية إلى جعل تطوير البرامج الآمنة أولوية تجارية. تقوم المؤسسات بدمج ضوابط الأمان مباشرةً في عمليات سير عمل التصميم والترميز والاختبار والنشر لتقليل المخاطر القابلة للاستغلال.
تعمل العمليات المهيكلة مثل نمذجة التهديدات ومعايير الترميز الآمنة والاختبار الآلي والمراقبة المستمرة على تعزيز مرونة البرامج. يضمن النهج القائم على دورة الحياة تحديد نقاط الضعف مبكرًا والتخفيف من حدتها بكفاءة ومنعها من الظهور مرة أخرى في أنظمة الإنتاج.
يعد أمان التطبيقات أمرًا ضروريًا لأن التطبيقات تعمل كبوابات أساسية للبيانات الحساسة والعمليات التجارية والخدمات الرقمية.
تدمج أفضل ممارسات أمان التطبيقات عناصر التحكم في البنية وطرق التطوير الآمنة والاختبار الآلي وتقوية البنية التحتية والمراقبة التشغيلية لتقليل المخاطر القابلة للاستغلال عبر أنظمة البرامج الحديثة.
تقوم نمذجة التهديدات بتقييم متجهات الهجوم وتدفقات البيانات وحدود الثقة قبل بدء التطوير. تساعد الأطر مثل STRIDE في تحديد مخاطر الانتحال والعبث وتصاعد الامتيازات على مستوى التصميم.
متطلبات الأمان المستمدة من النمذجة توجه قرارات الهندسة وتنفيذ التحكم. يمنع رسم خرائط المخاطر المبكرة نقاط الضعف الهيكلية التي لا يمكن للاختبار اللاحق تصحيحها بالكامل.
تطبق البنية الآمنة مبادئ مثل أقل الامتيازات والدفاع بعمق والتجزئة عبر الخدمات والبيئات. بنية زيرو تراست يفرض التحقق الصارم من الهوية بين المكونات الداخلية والخارجية.
تتطلب الخدمات المصغرة والأنظمة السحابية الأصلية العزل بين أحمال العمل وواجهات برمجة التطبيقات. تعمل أدوات التحكم المعمارية على تقليل الحركة الجانبية أثناء سيناريوهات الاختراق.
تعمل معايير الترميز الآمنة على مواءمة ممارسات التطوير مع إرشادات من OWASP ومعايير أمن الصناعة. تعمل قواعد الترميز المتسقة على تقليل عيوب الحقن وإلغاء التسلسل غير الآمن والأخطاء المنطقية.
تعمل مراجعات الأقران وأدوات الفحص الآلي على تعزيز الامتثال للمعايير المحددة. تعمل حوكمة التطوير المهيكلة على تعزيز سلامة التعليمات البرمجية عبر الفرق.
يضمن التحقق من صحة الإدخال تطهير جميع البيانات الخارجية وتطبيعها والتحقق منها قبل المعالجة. يؤدي التحقق من جانب الخادم إلى حظر إدخال SQL والبرمجة النصية عبر المواقع وهجمات إدخال الأوامر.
يؤدي إدراج تنسيقات الإدخال المقبولة في القائمة البيضاء إلى تقليل الغموض في معالجة الطلب. التحقق القوي يحمي قواعد البيانات الخلفية وواجهات برمجة التطبيقات من التلاعب.
تتحقق المصادقة القوية من الهوية باستخدام آليات اعتماد آمنة وأنظمة قائمة على الرموز. المصادقة متعددة العوامل (MFA) يضيف التحقق متعدد الطبقات بما يتجاوز كلمات المرور.
تقوم أطر المصادقة الحديثة بتطبيق OAuth 2.0 و OpenID Connect لإدارة الجلسة الآمنة. يقلل التحقق القوي من الهوية من حشو بيانات الاعتماد ومعدلات نجاح التصيد الاحتيالي.
يفرض التفويض المناسب التحكم في الوصول المستند إلى الأدوار (RBAC) والسياسات القائمة على السمات للوصول إلى الموارد. يجب أن يعمل منطق التخويل من جانب الخادم لمنع التجاوز من خلال التلاعب بالعميل.
تعمل إدارة الأذونات الدقيقة على تقييد الوظائف الإدارية للأدوار التي تم التحقق منها. تعمل عمليات تدقيق الامتيازات المستمرة على تقليل التعرض المفرط للوصول.
يحمي تشفير البيانات المعلومات الحساسة باستخدام معايير تشفير قوية. يقوم أمان طبقة النقل (TLS) بتأمين الاتصال بين العملاء والخوادم.
يحمي التشفير أثناء الراحة البيانات المخزنة داخل قواعد البيانات وأنظمة التخزين السحابية. إدارة المفاتيح الآمنة تمنع فك التشفير غير المصرح به.
يقوم اختبار أمان التطبيقات الثابت بتحليل التعليمات البرمجية المصدر دون تنفيذ لاكتشاف العيوب المنطقية والأنماط غير الآمنة. يتيح التكامل في خطوط أنابيب CI الكشف المبكر عن الثغرات الأمنية.
يحدد الفحص الآلي واجهات برمجة التطبيقات غير الآمنة والأسرار المشفرة والتبعيات غير الآمنة. العلاج المبكر يقلل من الديون الأمنية النهائية.
يقوم اختبار أمان التطبيقات الديناميكي بتقييم التطبيقات الحية من خلال محاكاة سلوك الهجوم في العالم الحقيقي. يكتشف تحليل وقت التشغيل التكوينات الخاطئة ونقاط النهاية المكشوفة.
DAST يكمل التحليل الثابت من خلال الكشف عن نقاط الضعف التي تم تشغيلها أثناء التنفيذ. يعمل الاختبار المشترك على تحسين التغطية الشاملة.
يراقب تحليل تكوين البرامج المكتبات مفتوحة المصدر وتبعيات الطرف الثالث بحثًا عن نقاط الضعف المعروفة. تستهدف هجمات سلسلة التوريد بشكل متزايد المكونات القديمة.
يحدد تتبع التبعية المستمر CVEs التي تؤثر على الحزم المتكاملة. تعمل التحديثات التلقائية على تقليل مخاطر الأمان الموروثة.
يحمي أمان API نقاط نهاية REST و GraphQL من الوصول غير المصرح به وإساءة الاستخدام. يؤدي التحقق من صحة الرمز وتطبيق المخطط وتحديد المعدل إلى تقييد النشاط الضار.
تفرض بوابات API سياسات المصادقة وفحص حركة المرور. تمنع المراقبة سرقة البيانات واستغلال الحرمان من الخدمة.
تعمل خطوط أنابيب CI/CD الآمنة على حماية أنظمة البناء من العبث وحقن الكود غير المصرح به. تعمل آليات التحكم في الوصول على تقييد تعديل عمليات سير عمل النشر.
يتحقق توقيع Artifact من سلامة البرنامج قبل الإصدار. تضمن مراقبة خطوط الأنابيب إمكانية التتبع عبر مراحل التطوير.
يعمل أمان الحاوية على تقوية صور Docker وتكوينات وقت التشغيل. تعمل الصور الأساسية البسيطة على تقليل سطح الهجوم غير الضروري.
تكتشف أدوات مسح الصور الثغرات الأمنية المعروفة قبل النشر. تعمل سياسات أمان وقت التشغيل على تقييد تصعيد الامتيازات داخل الحاويات.
يعمل أمان Kubernetes على تعزيز تكوين المجموعة وعزل عبء العمل والإدارة السرية. يحد تطبيق RBAC المناسب من الامتيازات الإدارية.
تعمل سياسات الشبكة على تقييد الاتصال من pod-to-pod داخل المجموعات. يضمن التدقيق المستمر الامتثال لمعايير الأمان.
تقوم جدران حماية تطبيقات الويب بفحص حركة مرور HTTP لحظر الطلبات الضارة. تعمل التصفية المستندة إلى القواعد على تخفيف محاولات الحقن والبرمجة النصية عبر المواقع.
يضيف نشر WAF طبقة واقية قبل وصول حركة المرور إلى خدمات الواجهة الخلفية. يعمل الدفاع متعدد الطبقات على تحسين المرونة ضد تهديدات يوم الصفر.
تقوم المراقبة المستمرة بتحليل السجلات وأنماط حركة المرور والشذوذات السلوكية في الوقت الفعلي. منصات المعلومات الأمنية وإدارة الأحداث (SIEM) تمركز التنبيهات عبر الأنظمة.
يحدد اكتشاف الشذوذ أنماط الوصول المشبوهة واستدعاءات API غير الطبيعية. تعمل الرؤية في الوقت الفعلي على تقليل وقت الانتظار أثناء التهديدات النشطة.
تخطيط الاستجابة للحوادث يحدد إجراءات الكشف والاحتواء والاستئصال والتعافي. تعمل أطر الاستجابة المهيكلة على تقليل الارتباك التشغيلي أثناء الانتهاكات.
تمارين المحاكاة المنتظمة تتحقق من بروتوكولات الجاهزية والتواصل. تقوم الفرق الجاهزة باستعادة الخدمات بشكل أسرع والحد من التأثير طويل المدى.
يجب أن يتماشى اختيار الأداة مع النضج التنظيمي والنطاق التشغيلي وتحمل المخاطر بدلاً من حجم الميزة وحده.
يحدد نطاق التغطية ما إذا كان الحل يعالج منطق التطبيق ونقاط ضعف التكوين والتعرض لوقت التشغيل. الرؤية الشاملة تمنع البقع العمياء عبر البيئات المختلفة.
تؤثر مستويات الدقة على عدد الإيجابيات الكاذبة التي يجب على فرق الأمن مراجعتها يدويًا. تقلل الدقة العالية من إجهاد التنبيه وتحسن الكفاءة التشغيلية.
تضمن مرونة التكامل التوافق مع أنظمة التحكم في الإصدار ومنصات التذاكر وأدوات تنسيق البنية التحتية. تدعم قابلية التشغيل البيني السلس عمليات سير عمل المعالجة بشكل أسرع.
تحدد سعة قابلية التوسع ما إذا كان الحل قادرًا على التعامل مع أعباء العمل المتزايدة والبنى الموزعة. يصبح الأداء المرن أمرًا بالغ الأهمية مع نمو حركة مرور التطبيقات وتعقيدها.
توفر إمكانات إعداد التقارير مسارات التدقيق والملخصات التنفيذية والوثائق الجاهزة للامتثال. تدعم التقارير الواضحة الإشراف على الحوكمة وشفافية أصحاب المصلحة.
تعمل CloudSek على تحسين أمان التطبيقات من خلال ذكاء التهديدات في الوقت الفعلي المستند إلى الذكاء الاصطناعي والمراقبة المستمرة عبر البيئات السحابية والويب والجوال. ويحدد الثغرات الأمنية ومفاتيح API المكشوفة والتكوينات الخاطئة المتوافقة مع OWASP Top 10 قبل أن يتم استغلالها.
تقوم المنصة بمسح الأصول السحابية الخارجية عبر AWS و Azure و Alibaba أثناء الاندماج في خطوط أنابيب CI/CD لتمكين المراقبة المستمرة بدون وكيل. تعمل قدرة BeVigil الخاصة به على تعزيز أمان تطبيقات الهاتف المحمول من خلال اكتشاف الأسرار المشفرة والبرامج الضارة والتكوينات الخاطئة في تطبيقات Android و iOS.
يعمل Svigil أيضًا على تحسين أمان تطبيقات الويب من خلال تحديد حقن SQL و XSS وإدارة الجلسة الضعيفة في البيئات الحية. تدعم المراقبة المتكاملة عبر الويب المظلم والويب العميق والويب السطحي، جنبًا إلى جنب مع عمليات تكامل SIEM مثل IBM QRadar و Azure Sentinel و ArcSight، الاستجابة التلقائية للحوادث والرؤية التشغيلية المستدامة.
يوفر أمان التطبيق عناصر تحكم موثقة وقيود وصول وسجلات مراقبة مطلوبة أثناء مراجعات الامتثال. يعمل التنفيذ السليم على تبسيط إعداد التدقيق وتقليل العقوبات التنظيمية.
تعمل الأتمتة على فرض فحوصات أمنية متسقة دون الاعتماد فقط على المراجعة اليدوية. إنه يقلل الخطأ البشري ويسرع اكتشاف الثغرات الأمنية عبر دورات التطوير.
يحد أمان التطبيق من مسارات الهجوم من خلال آليات التحكم في الوصول والتجزئة والتشفير. تعمل ضوابط الاحتواء القوية على تقليل التعرض للبيانات وتعطيل التشغيل.
ينطبق أمان التطبيقات على الويب والجوال وسطح المكتب والأنظمة المستندة إلى API والأنظمة السحابية الأصلية. يتطلب أي برنامج يعالج البيانات أو يتصل بالشبكات حماية منظمة.
يتم تقاسم المسؤولية بين المطورين وفرق الأمان وموظفي العمليات. تضمن الملكية الواضحة والسياسات المحددة المساءلة عبر دورة حياة البرنامج.
