🚀 CloudSEK becomes first Indian origin cybersecurity company to receive investment from US state fund
Read more
Sensitive data sits at the core of nearly every digital operation today, from customer records and financial transactions to intellectual property and internal systems. As organizations expand across cloud platforms, third-party tools, and remote work environments, sensitive information spreads across more locations than ever before.
According to the IBM Cost of a Data Breach Report 2023, 83% of organizations experienced more than one data breach, and most of those incidents involved the compromise of sensitive data. These breaches lead directly to financial loss, regulatory action, and long-term damage to trust, which is why sensitive data remains the primary target for attackers.
Knowing what sensitive data is, why it matters, how it is classified, and how it is protected allows organizations to reduce risk by treating sensitive data as a critical business asset rather than an afterthought.
Sensitive data is information that causes measurable harm when accessed, disclosed, altered, or destroyed without authorization. The harm includes financial loss, legal penalties, operational disruption, or personal damage, depending on the data subject and misuse context. Sensitivity is defined by impact severity.
Not all information qualifies as sensitive data. Data becomes sensitive when exposure results in identity theft, regulatory fines, competitive disadvantage, or national security risk. Information without material impact does not meet the sensitivity threshold.
Sensitive data is context-dependent. Context determines sensitivity because identical data varies in risk based on usage, aggregation with other datasets, or access conditions. In distributed cloud and third-party environments, exposure probability increases, making precise identification essential.
Sensitive data matters because its exposure creates direct, measurable, and often irreversible harm. When sensitive data is accessed without authorization, the impact goes beyond technical issues and quickly becomes a business, legal, and security problem.
Exposure of sensitive personal data can result in identity theft, financial fraud, loss of privacy, and long-term personal harm. Once leaked, this data is difficult to recover or invalidate, and misuse can continue for years.
Sensitive business data drives operations, revenue, and competitive advantage. Its exposure can lead to financial losses, regulatory penalties, operational disruption, and permanent damage to trust with customers and partners.
Sensitive government data underpins national security, public services, and diplomatic stability. Unauthorized access can compromise intelligence, weaken defense capabilities, and disrupt critical infrastructure or public confidence.
Across all three, sensitive data is valuable because it enables control, leverage, and decision-making. Protecting it is essential to maintaining security, stability, and trust in digital systems.
Sensitive data can be grouped into distinct categories based on who the data affects and the impact of its exposure. Each type carries different risks, but all require protection because misuse leads to serious consequences.
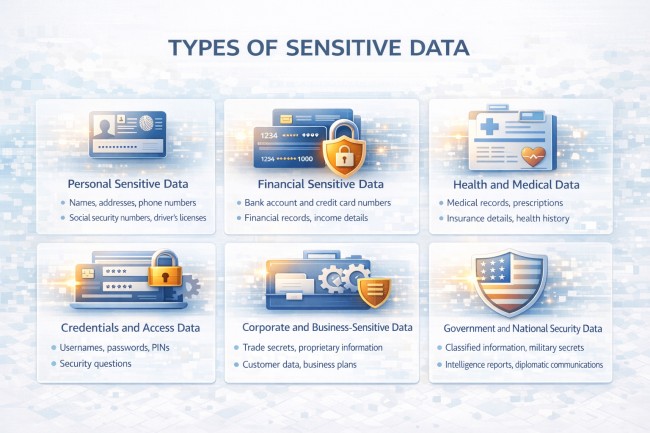
This includes information that can directly identify or harm an individual. Examples include government-issued IDs, biometric data, precise location information, and unique personal identifiers. Exposure commonly leads to identity theft, fraud, or personal safety risks.
Financial data relates to money, transactions, and access to funds. This includes bank account numbers, payment card details, transaction records, and financial credentials. Unauthorized access often results in fraud, financial loss, and compliance violations.
Medical records, health histories, diagnostic results, and insurance details fall into this category. This data is highly regulated because misuse can cause personal harm, discrimination, and long-term privacy violations.
Usernames, passwords, authentication tokens, API keys, and access certificates are highly sensitive because they provide direct entry into systems. Exposure allows attackers to bypass security controls and access other sensitive data.
Organizations generate sensitive information tied to operations and competitive advantage. This includes intellectual property, trade secrets, internal communications, business strategies, and customer databases. Exposure can weaken market position and erode trust.
This category includes classified information, defense data, intelligence records, and critical infrastructure details. Unauthorized disclosure can threaten public safety, national security, and geopolitical stability.
Here is a comparison table for better understanding:
Organizations can identify sensitive data by locating where it exists, understanding its impact, and tracking how it is accessed and shared. The steps below explain this process in simple terms.
Scan databases, applications, cloud services, endpoints, file storage, and collaboration tools to locate sensitive data wherever it resides.
Review emails, documents, spreadsheets, chat platforms, and file shares where sensitive information is often stored informally.
Label data based on the harm caused if it is exposed, misused, or lost. Data with high financial, legal, or security impact is classified as sensitive.
Locate usernames, passwords, API keys, tokens, and privileged accounts that provide access to sensitive systems and data.
Track how sensitive data moves between systems, users, vendors, and regions to identify exposure points and unnecessary sharing.
Review who can view, modify, or export sensitive data and identify excessive, unused, or high-risk access.
Identify sensitive data stored in vendor platforms or unsanctioned tools that operate outside formal security controls.
Use automated tools to maintain visibility at scale, because manual identification cannot keep pace with dynamic environments.
Repeat identification regularly as systems, users, and business processes change, since data sensitivity evolves over time.
These steps help organizations move from assumptions to continuous visibility, ensuring sensitive data is identified accurately and protected based on real-world risk rather than static labels.
When sensitive data is exposed, the impact is immediate, cumulative, and often long-lasting. The risks extend beyond technical damage and affect individuals, organizations, and broader trust.
Exposed personal and financial data allows attackers to impersonate individuals. This leads to account takeovers, unauthorized transactions, and ongoing financial harm.
Data protection laws impose strict requirements on handling sensitive data. Exposure can result in fines, lawsuits, regulatory investigations, and mandatory reporting obligations.
Stolen trade secrets, designs, or strategic plans weaken competitive advantage. Once intellectual property is exposed, exclusivity cannot be restored.
Breaches often force system shutdowns, credential resets, access reviews, and internal investigations. Normal operations are disrupted while security and legal teams respond.
Beyond immediate response, organizations face ongoing costs for remediation, audits, customer notification, credit monitoring, legal defense, and higher insurance premiums.
Sensitive data is frequently resold, reused, or combined with other stolen information. This creates repeated risk long after the initial exposure is contained.
Customers, partners, and investors lose confidence when sensitive data is compromised. Rebuilding trust takes time and directly affects revenue and market position.
Exposure of government or critical infrastructure data can threaten public safety and geopolitical stability, with consequences far beyond the affected organization.
Sensitive data is the primary objective in most modern cyber threats. Attackers focus on information that enables fraud, extortion, intelligence gathering, or long-term access, rather than targeting systems at random. Personal records, credentials, intellectual property, and strategic documents consistently deliver the highest value when exposed.
Ransomware attacks demonstrate this shift clearly. Many attackers now steal sensitive data before encrypting systems, using the threat of public disclosure to force payment. Even after recovery, exposed data continues to create legal, financial, and reputational risk.
Credential theft accelerates sensitive data exposure across environments. Stolen passwords, access tokens, and keys allow attackers to move quietly through cloud services, third-party tools, and internal systems, often without triggering alerts. Once trusted access is gained, multiple data stores become reachable.
Sensitive data is also exposed through misconfigurations and cloud sprawl, not just active attacks. Public storage buckets, excessive permissions, and unmanaged assets frequently leak sensitive information without any intrusion. In cyber espionage, state-backed threat actors exploit these weaknesses to collect sensitive data quietly over long periods, making detection difficult and recovery limited. These realities make sensitive data protection a central concern in modern cybersecurity, not a secondary issue tied only to compliance or perimeter defense.
Protecting sensitive data requires layered, continuous controls that reduce exposure, restrict access, and detect misuse early. Effective protection combines classification, access management, technical safeguards, and continuous monitoring.
Here are best tactics to prevent sensitive data:
Sensitive data must be identified and labeled so the right protections are applied. Classification ensures controls match the data’s risk and impact.
Only authorized users and systems should access sensitive data. Restricting access based on role and need limits damage if credentials are compromised.
Multi-factor authentication and secure identity management prevent attackers from relying on stolen passwords alone. Strong identity controls protect sensitive data even during credential exposure.
Encryption protects sensitive data when stored and when transmitted. Even if systems are breached, encrypted data remains unreadable without keys.
Sensitive values are replaced with masked or tokenized versions during processing, analytics, and testing. This reduces exposure while preserving usability.
DLP controls monitor and block unauthorized data sharing, downloads, or transfers. These controls reduce accidental leaks and insider-driven exposure.
Continuous monitoring identifies unusual access patterns, data movement, or behavior. Early detection limits how long sensitive data is exposed.
Sensitive systems are isolated from the broader environment. Segmentation limits lateral movement and reduces blast radius during incidents.
Backups containing sensitive data are encrypted, access-controlled, and monitored. Secure recovery ensures data can be restored without introducing new exposure.
Vendors with access to sensitive data must follow strict security requirements. Limiting and auditing third-party access prevents indirect exposure.
Ongoing reviews and security testing validate that controls remain effective as systems and data change.
Sensitive data matters because its exposure causes real harm. When information like personal records, financial details, or proprietary business data is accessed without permission, the impact is felt immediately through financial loss, legal pressure, operational disruption, and loss of trust.
As organizations rely more on cloud services, partners, and digital tools, sensitive data becomes harder to track and easier to expose, making accurate identification a critical first step.
Protecting sensitive data is not just about meeting compliance requirements. It requires knowing where the data lives, limiting who can access it, and watching for misuse as systems and risks change. Organizations that treat sensitive data as a core business responsibility, rather than a checkbox exercise, are far better prepared to reduce exposure and respond when incidents occur.
