🚀 أصبحت CloudSek أول شركة للأمن السيبراني من أصل هندي تتلقى استثمارات منها ولاية أمريكية صندوق
اقرأ المزيد
نادرًا ما تواجه المنظمات حوادث إلكترونية بشكل متوقع. غالبًا ما تتصاعد الأحداث الأمنية بسرعة، مما يجبر الفرق على اتخاذ قرارات فنية وقانونية وتجارية تحت الضغط. بسبب حالة عدم اليقين هذه، تمارس العديد من المنظمات استجابتها من خلال تمارين منظمة تحاكي الأزمات الإلكترونية الحقيقية وتقيم كيفية تنسيق الفرق أثناء الحوادث عالية التأثير.
أصبح الاستعداد لهذه المواقف مهمًا بشكل متزايد مع استمرار التهديدات الإلكترونية في الارتفاع. وفقًا لتقرير تكلفة خرق البيانات لعام 2023 الصادر عن IBM، بلغ متوسط التكلفة العالمية لخرق البيانات 4.45 مليون دولار، مما يسلط الضوء على التأثير المالي الكبير الذي تواجهه المنظمات عندما تكون الاستجابة للحوادث والاستعداد الأمني غير كافية. تساعد التمارين المنضدية للأمن السيبراني المؤسسات على مراجعة استراتيجيات الاستجابة وتقييم عمليات الاتصال والتأكد من قدرة الفرق على الاستجابة بفعالية في حالة وقوع حادث إلكتروني حقيقي.
تمرين الطاولة (TTX) في الأمن السيبراني هو نشاط قائم على المناقشة حيث تستعرض الفرق حادثة إلكترونية تمت محاكاتها لتقييم كيفية استجابتها.
بدلاً من تشغيل هجوم تقني مباشر، يراجع المشاركون السيناريو ويشرحون الإجراءات التي سيتخذونها في كل مرحلة من مراحل الحادث. الهدف هو اختبار مدى فهم الأشخاص لأدوارهم ومسؤولياتهم وإجراءات الاستجابة.
تعتبر تمارين الطاولة مهمة لأنها تساعد المؤسسات على تقييم مدى استجابة فرقها للحوادث الإلكترونية قبل حدوث هجوم حقيقي. تكشف هذه التمارين عن نقاط الضعف في العمليات والتواصل واتخاذ القرار التي قد لا تظهر أثناء العمليات العادية.

فيما يلي الفوائد الرئيسية:
تسمح تمارين الطاولة للفرق بالتدرب على كيفية استجابتها لحادث إلكتروني. يراجع المشاركون كل خطوة من خطوات عملية الاستجابة ويؤكدون فهم الإجراءات. يساعد هذا الإعداد الفرق على التفاعل بشكل أكثر فعالية أثناء الهجمات الحقيقية.
غالبًا ما يكشف السير في حادث تمت محاكاته عن نقاط ضعف في خطط الاستجابة الحالية. قد تكتشف الفرق الإجراءات المفقودة أو المسؤوليات غير الواضحة أو الوثائق القديمة. إن تحديد هذه الثغرات يسمح للمنظمات بتحسينها الاستجابة للحوادث استراتيجيات.
تشمل الحوادث الإلكترونية أقسام متعددة، بما في ذلك الأمن وتكنولوجيا المعلومات والقيادة والشؤون القانونية والاتصالات. تجمع تمارين الطاولة هذه الفرق معًا لمناقشة كيفية تنسيق الإجراءات أثناء الأزمة. يعمل هذا على تحسين التعاون ويضمن فهم الجميع لدورهم.
تساعد محاكاة سيناريوهات الهجوم الواقعية المؤسسات على فهم التأثير التشغيلي والتجاري لحادث إلكتروني. تكتسب الفرق خبرة في اتخاذ القرارات تحت الضغط وتقييم خيارات الاستجابة. يعزز هذا الإعداد المرونة الإلكترونية الشاملة.
يعمل تمرين الأمن السيبراني على الطاولة من خلال توجيه المشاركين من خلال محاكاة حادث إلكتروني في مناقشة منظمة. يقدم الميسر سيناريو، مثل هجوم برامج الفدية أو خرق البيانات، ويشرح كيفية تطور الموقف. ثم يصف المشاركون الإجراءات التي سيتخذونها بناءً على أدوارهم ومسؤولياتهم. يركز التمرين على صنع القرار بدلاً من تنفيذ الإجراءات الفنية على الأنظمة الحقيقية.
ومع تطور السيناريو، يقدم الميسر معلومات جديدة لمحاكاة كيفية تطور حادث حقيقي. تناقش الفرق كيفية اكتشاف التهديد واحتواء التأثير والتواصل مع أصحاب المصلحة واستعادة الأنظمة المتأثرة. تسمح كل خطوة للمشاركين بفحص كيفية عمل خطط الاستجابة الحالية عمليًا.
في نهاية التمرين، تقوم المجموعة بمراجعة القرارات التي تم اتخاذها أثناء المناقشة. يحدد الميسرون والمراقبون نقاط القوة والضعف والمجالات التي تتطلب التحسين. تساعد هذه النتائج المؤسسات على تحديث خطط الاستجابة للحوادث وتحسين التنسيق بين الفرق.
يتضمن تمرين الأمن السيبراني العديد من أصحاب المصلحة الذين يعملون معًا لتقييم كيفية استجابة المنظمة أثناء وقوع حادث إلكتروني.
يمكن أن تركز تمارين الأمن السيبراني على أنواع مختلفة من الحوادث اعتمادًا على المخاطر التي تريد المؤسسة اختبارها. يحاكي كل نوع سيناريو تهديد معين لتقييم كيفية استجابة الفرق والتنسيق أثناء هذا الموقف.
تركز التمارين المنضدية للاستجابة للحوادث على اختبار كيفية اكتشاف الفرق للحوادث الإلكترونية وتحليلها واحتوائها. يمر المشاركون بخطوات مثل تحديد النشاط المشبوه وتفعيل خطة الاستجابة للحوادث وتنسيق الإجراءات الفنية.
رانسوم وير تحاكي التمارين موقفًا يتم فيه تشفير الأنظمة أو البيانات من قبل المهاجمين. يناقش المشاركون القرارات المتعلقة بالاحتواء واستعادة النظام واستمرارية الأعمال والتواصل مع أصحاب المصلحة.
تركز تمارين خرق البيانات على السيناريوهات التي يتم فيها الكشف عن المعلومات الحساسة أو سرقتها. تقوم الفرق بمراجعة كيفية التحقيق في الخرق وتقييم البيانات المتأثرة وإخطار المنظمين والتواصل مع الأفراد المتأثرين.
تركز التدريبات المنضدية لإدارة الأزمات على صنع القرار القيادي أثناء الحوادث الإلكترونية الكبرى. يناقش التنفيذيون مخاطر الأعمال والأولويات التشغيلية واستراتيجيات الاتصال العام أثناء الاستجابة للوضع المتطور.
عادةً ما يتبع التمرين على الطاولة سيناريو منظمًا حيث يطلع المشاركون على كيفية استجابتهم لحادث إلكتروني تمت محاكاته. يقدم الميسر تطورات جديدة أثناء التمرين بينما تشرح الفرق قراراتها وأفعالها.
يقدم الميسر السيناريو. على سبيل المثال، يتلقى فريق الأمان تنبيهات تشير إلى نشاط مريب قد يشير إلى هجوم رانسوم وير.
يناقش المشاركون خطوات الاستجابة الفورية. قد يشمل ذلك عزل الأنظمة المتأثرة وتفعيل خطة الاستجابة للحوادث وإخطار الفرق الداخلية.
يتطور السيناريو عندما يقدم الميسر تطورات جديدة، مثل الأنظمة المشفرة أو نشاط الشبكة المشبوه. تناقش الفرق خطوات التحقيق واستراتيجيات الاحتواء.
تناقش القيادة والفرق القانونية وفرق الاتصالات كيفية إخطار أصحاب المصلحة والعملاء والمنظمين إذا لزم الأمر.
يستعرض المشاركون كيفية استعادة الأنظمة والإجراءات المطلوبة لمنع وقوع حوادث مماثلة في المستقبل.
يساعد كل من التمرين على الطاولة ومحاكاة الأمن السيبراني المؤسسات على الاستعداد للحوادث الإلكترونية، ولكنهما يعملان بطرق مختلفة. يركز التمرين على الطاولة على المناقشة واتخاذ القرار، حيث يشرح المشاركون كيفية استجابتهم للسيناريو. تتضمن محاكاة الأمن السيبراني تشغيل سيناريوهات الهجوم الفني في بيئة خاضعة للرقابة لاختبار الأنظمة والدفاعات.
يقوم شكل الطاولة بتقييم التنسيق والتخطيط، بينما تختبر المحاكاة القدرات الفنية وأدوات الكشف. فيما يلي جدول المقارنة لفهم الاختلافات بسهولة:
قم بإجراء تمرين على سطح الطاولة للأمن السيبراني من خلال عملية منظمة تقيم كيفية استجابة الفرق لحادث إلكتروني تمت محاكاته. يسمح التمرين المنظم جيدًا للمشاركين بفحص إجراءات صنع القرار والتنسيق والاستجابة.
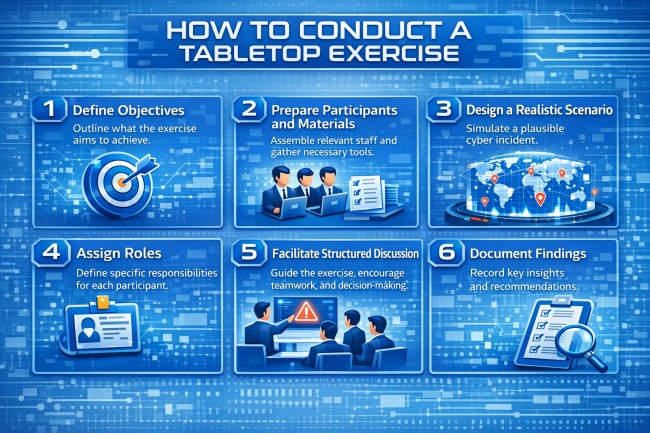
ابدأ بتحديد ما يهدف التمرين إلى تقييمه. قد ترغب المنظمات في اختبار إجراءات الاستجابة للحوادث أو التواصل في الأزمات أو اتخاذ القرارات القيادية. أهداف واضحة توجه التمرين بأكمله.
قبل بدء التمرين، يراجع المشاركون خطة الاستجابة للحوادث ويتلقون معلومات أساسية حول السيناريو. يقوم الميسرون بإعداد المواد الداعمة مثل الجداول الزمنية والمطالبات وأسئلة المناقشة. يضمن هذا الإعداد أن الجميع يفهم سياق التمرين.
قم بإنشاء سيناريو يعكس التهديدات الإلكترونية ذات الصلة بالمؤسسة. تشمل الأمثلة هجمات برامج الفدية أو خروقات البيانات أو تنازلات الخدمة السحابية. يساعد السيناريو الواقعي المشاركين على تقييم قرارات الاستجابة العملية.
حدد المشاركين وحدد مسؤولياتهم أثناء التمرين. تشمل الأدوار النموذجية فرق الأمن وموظفي تكنولوجيا المعلومات والمديرين التنفيذيين والمستشارين القانونيين وموظفي الاتصالات. تساعد الأدوار الواضحة في تنظيم المناقشة.
يقوم الميسر بتوجيه التمرين من خلال تقديم السيناريو خطوة بخطوة. يشرح المشاركون كيف سيستجيبون مع تطور الحادث. تكشف هذه المناقشة كيف تعمل خطط الاستجابة في الممارسة العملية.
سجل الملاحظات الرئيسية والقرارات والدروس المستفادة أثناء التمرين. بعد الجلسة، تقوم المؤسسات بمراجعة النتائج وتحديث خطط الاستجابة لمعالجة أي فجوات يتم اكتشافها.
تُجري المؤسسات عادةً تمارين الأمن السيبراني على الطاولة مرة أو مرتين في السنة على الأقل. تساعد التمارين المنتظمة الفرق على البقاء على دراية بإجراءات الاستجابة للحوادث والحفاظ على تحديث خطط الاستجابة.
يشمل المشاركون عادةً فرق الأمن السيبراني وموظفي تكنولوجيا المعلومات والقيادة التنفيذية والمستشارين القانونيين وفرق الاتصالات. يساعد إشراك أقسام متعددة في تقييم التنسيق أثناء وقوع حادث إلكتروني.
تمرين الطاولة هو مراجعة قائمة على المناقشة لكيفية استجابة الفرق لحادث إلكتروني. تتضمن المحاكاة تشغيل سيناريوهات الهجوم الفني في بيئة خاضعة للرقابة لاختبار الأنظمة والدفاعات.
بعض الأطر واللوائح الأمنية تشجع أو تتطلب اختبار الاستجابة للحوادث. قد تستخدم المنظمات تمارين الطاولة لإظهار الاستعداد وتحسين الامتثال لمعايير الأمان.
