🚀 أصبحت CloudSek أول شركة للأمن السيبراني من أصل هندي تتلقى استثمارات منها ولاية أمريكية صندوق
اقرأ المزيد
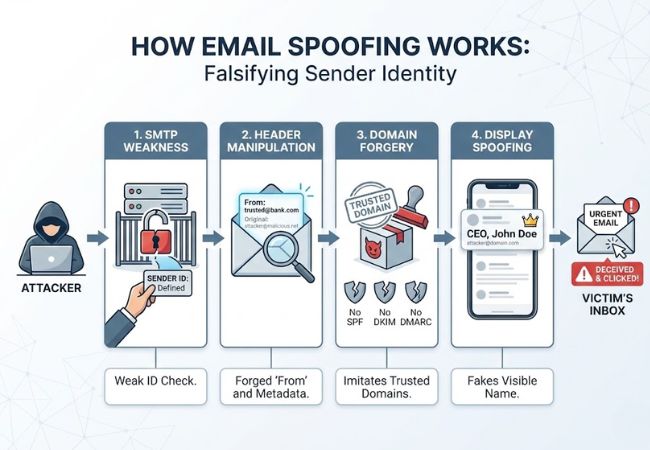
انتحال البريد الإلكتروني هو أسلوب هجوم إلكتروني يقوم بتزوير عنوان المرسل للرسالة لجعلها تبدو كما لو أنها صادرة عن شخص أو منظمة موثوق بها. يقوم المهاجم بتغيير بيانات رأس البريد الإلكتروني بحيث لا تتطابق الهوية المرئية مع مصدر الإرسال الفعلي.
الوصول إلى الحساب غير مطلوب حتى يحدث الانتحال. يستهدف الاستغلال نقاط الضعف في بروتوكول نقل البريد البسيط والثغرات في التحقق من مصادقة المرسل.
يحكم معظم المستلمين على الشرعية بناءً على الاسم أو العنوان المعروض في عرض البريد الوارد. هذا الاعتماد على الهوية السطحية يمكّن هجمات التصيد الاحتيالي والاحتيال واختراق البريد الإلكتروني للأعمال من النجاح على نطاق واسع.
يعمل انتحال البريد الإلكتروني عن طريق التلاعب بالعناصر الفنية لنقل البريد الإلكتروني لتزوير هوية المرسل.
يزيد انتحال البريد الإلكتروني من احتمالية أن تتجاوز الرسالة الضارة الشك وتؤدي إلى اتخاذ إجراء.
غالبًا ما تنتحل رسائل البريد الإلكتروني المخادعة شخصية المديرين التنفيذيين أو الإدارات المالية لطلب تحويلات برقية عاجلة. يتم استخدام السلطة وضغط الوقت لتقليل التحقق.
يقوم المهاجمون بإعادة توجيه المستلمين إلى بوابات تسجيل الدخول المزيفة المصممة لالتقاط أسماء المستخدمين وكلمات المرور. تمكّن بيانات الاعتماد المسروقة من اختراق الشبكة بشكل أعمق.
إن انتحال شخصية القيادة الداخلية أو الموردين الموثوق بهم يدعم مخططات تحويل المدفوعات المستهدفة. يمكن أن تصل الخسائر المالية في مثل هذه الهجمات إلى الملايين في حادث واحد.
يتم إخفاء المرفقات الضارة في صورة فواتير أو عقود أو مستندات شحن. قد يؤدي التنفيذ الناجح إلى تثبيت برامج الفدية أو برامج التجسس أو أدوات الوصول عن بُعد.
قد تطلب الرسائل المخادعة ملفات داخلية حساسة بحجة عمليات التدقيق أو فحوصات الامتثال. يتم بيع البيانات السرية التي تم جمعها من خلال الخداع أو استغلالها لاحقًا.
تسيء الجماعات الإجرامية استخدام نطاقات الشركات الشرعية لزيادة مصداقية الرسائل. غالبًا ما يتبع الضرر بالسمعة وانعدام ثقة العملاء حملات انتحال واسعة النطاق.
يظهر انتحال البريد الإلكتروني بأشكال متعددة اعتمادًا على كيفية التلاعب بهوية المرسل.

يتم تغيير اسم المرسل المرئي فقط ليشبه فردًا موثوقًا به. يعطي عملاء البريد الإلكتروني الأولوية لأسماء العرض، مما يزيد من فعالية الخداع.
تم إنشاء نطاق الإرسال ليطابق عنوان شركة شرعي. يؤدي عدم وجود تطبيق صارم لـ SPF أو DKIM أو DMARC إلى زيادة نجاح التسليم.
يقوم المهاجمون بتسجيل المجالات التي تشبه إلى حد كبير النطاقات الحقيقية مع اختلافات إملائية طفيفة. يقلل التشابه المرئي من شكوك المستلم.
يتم إرسال الرسائل الاحتيالية باستخدام نطاقات فرعية تم التلاعب بها تبدو صالحة من الناحية الهيكلية. غالبًا ما يتجاهل المستلمون الاختلافات الدقيقة في التسلسل الهرمي للنطاقات.
قد يبدو المرسل المرئي شرعيًا، لكن عنوان الرد يعيد توجيه الردود إلى صندوق بريد يتحكم فيه المهاجم. ينقل الضحايا معلومات حساسة دون علمهم.
تتلاعب الجهات الفاعلة المتقدمة بمعلومات التوجيه على مستوى الخادم لإخفاء البنية التحتية الحقيقية للإرسال. يتطلب الاكتشاف عادةً تحليلًا أعمق للرأس.
يرتبط انتحال البريد الإلكتروني والتصيد الاحتيالي ارتباطًا وثيقًا ولكنهما يختلفان في الغرض والتنفيذ والنطاق.
يتطلب اكتشاف انتحال البريد الإلكتروني التحقق الفني جنبًا إلى جنب مع مراجعة دقيقة للرسائل.
تكشف عناوين البريد الإلكتروني الكاملة عن مسارات التوجيه والخوادم الأصلية ونتائج المصادقة. غالبًا ما تشير النطاقات غير المتطابقة أو البنية التحتية للإرسال المشبوهة إلى التزوير.
تُظهر نتائج SPF وDKIM وDMARC ما إذا كانت هوية المرسل قد اجتازت اختبارات التحقق. تزيد النتائج الفاشلة أو الضعيفة من احتمالية انتحال المجال.
تشير الاختلافات الإملائية الصغيرة في أسماء النطاقات إلى محاولات انتحال الشخصية. غالبًا ما تستبدل نطاقات Lookalike الأحرف بأحرف متشابهة.
قد يختلف المرسل المرئي عن عنوان الرد المضمن في الرسالة. تعرض الردود المعاد توجيهها البيانات الحساسة للحسابات التي يتحكم فيها المهاجم.
تخلق طلبات الدفع غير المتوقعة أو طلبات البيانات السرية ضغطًا اصطناعيًا. التلاعب العاطفي هو مؤشر قوي على النية الاحتيالية.
تزيد المرفقات غير المرغوب فيها أو الروابط المختصرة من خطر الإصابة. يكشف فحص مؤشر الماوس لعناوين URL عن مسارات إعادة التوجيه المخفية.
يتطلب منع انتحال البريد الإلكتروني عناصر تحكم مصادقة متعددة الطبقات ومراقبة البنية التحتية وسياسات التوعية الداخلية.
يسمح إطار سياسة المرسل لمالكي النطاقات بتحديد خوادم البريد المصرح لها بإرسال الرسائل نيابة عنهم. تقوم خوادم الاستقبال بمقارنة إرسال عناوين IP مقابل سجلات DNS المنشورة للتحقق من الشرعية.
يقوم البريد المحدد لـ DomainKeys بإرفاق توقيع مشفر برسائل البريد الإلكتروني الصادرة. تتحقق أنظمة الاستلام من سلامة الرسائل وتؤكد أن المحتوى لم يتم تغييره أثناء النقل.
تعتمد مصادقة الرسائل وإعداد التقارير والمطابقة المستندة إلى المجال على SPF وDKIM لتحديد كيفية التعامل مع محاولات المصادقة الفاشلة. قد تقوم السياسات بمراقبة رسائل البريد الإلكتروني المشبوهة أو عزلها أو رفضها أثناء إنشاء تقارير الرؤية.
تقوم أنظمة التصفية المتقدمة بتحليل حركة مرور البريد الإلكتروني الواردة والصادرة لأنماط انتحال الشخصية. تكتشف نماذج التعلم الآلي الحالات الشاذة في سلوك المرسل وبنية الرسالة.
يقلل التحقق الإضافي من الهوية من مخاطر الاستحواذ على الحساب، مما قد يؤدي إلى تضخيم حملات الانتحال. تصبح بيانات الاعتماد المسروقة أقل فائدة بدون طبقات المصادقة الثانوية.
تحدد المراقبة المستمرة استخدام النطاق غير المصرح به أو التسجيلات المشابهة. يحد الاكتشاف المبكر من إساءة استخدام العلامة التجارية والتوسع في التصيد الاحتيالي.
يعمل تعليم الموظفين على تحسين التعرف على محاولات انتحال الشخصية. إجراءات الإبلاغ الواضحة تعزز سرعة الاستجابة للحوادث.
يتطلب تحديد حل أمان البريد الإلكتروني تقييم قوة المصادقة ودقة الاكتشاف والرؤية التشغيلية.
يجب أن تدعم المنصة بشكل كامل تطبيق SPF و DKIM و DMARC. يمنع التحقق الصحيح من المحاذاة استخدام المجال غير المصرح به.
يجب أن تحدد ميزة الكشف المتقدم عن التهديدات انتحال اسم العرض وإساءة استخدام النطاق المشابه. يعمل التحليل السلوكي على تحسين الدقة بما يتجاوز تصفية الكلمات الرئيسية البسيطة.
يجب فحص حركة المرور الواردة والصادرة على الفور بحثًا عن الأنماط الضارة. يعمل الحظر الفوري على تقليل التعرض قبل تفاعل المستخدم.
توفر لوحات المعلومات التفصيلية نظرة ثاقبة لحالات فشل المصادقة ومحاولات الانتحال. تدعم التقارير الواضحة التحقيق والمعالجة بشكل أسرع.
تعمل التنبيهات الآلية وعمليات سير الاستجابة على تقليل التدخل اليدوي. تكتسب فرق الأمان قدرة احتواء أسرع.
يجب أن يتناسب الحل مع النمو التنظيمي ويدعم المعايير التنظيمية. يضمن توافق البنية الأساسية استقرار النشر على المدى الطويل.
يستغل انتحال البريد الإلكتروني نقاط الضعف في البنية الأساسية للبريد الإلكتروني لإنشاء ثقة زائفة وتمكين هجمات الاحتيال والتصيد الاحتيالي واختراق البريد الإلكتروني للأعمال. يظل التلاعب بهوية المرسل أحد أكثر نقاط الدخول فعالية للجرائم الإلكترونية المالية والقائمة على البيانات.
يؤدي تطبيق المصادقة القوي من خلال SPF و DKIM و DMARC جنبًا إلى جنب مع المراقبة ووعي الموظفين إلى تقليل التعرض بشكل كبير. تعمل المؤسسات التي تعطي الأولوية لأمان البريد الإلكتروني متعدد الطبقات على تعزيز النزاهة التشغيلية وثقة العلامة التجارية.
يصبح انتحال البريد الإلكتروني غير قانوني عند استخدامه للاحتيال أو سرقة الهوية أو الجرائم المالية. تعتمد العواقب القانونية على الاختصاص والنية وراء النشاط.
نعم، لا يتطلب الانتحال اختراق الحساب. يستغل المهاجمون نقاط الضعف في بروتوكولات البريد الإلكتروني بدلاً من اختراق بيانات اعتماد صندوق البريد.
يقلل DMARC بشكل كبير من الانتحال المستند إلى المجال عند تطبيقه بشكل صحيح. قد تستمر هجمات نطاق Lookalike في تجاوز الحماية إذا تم تسجيل نطاقات منفصلة.
لا يزال انتحال البريد الإلكتروني أحد أكثر تقنيات انتحال الشخصية استخدامًا في الجرائم الإلكترونية. وهو يدعم في كثير من الأحيان مخططات التصيد الاحتيالي وتسوية البريد الإلكتروني للأعمال.
غالبًا ما يتم استهداف الشركات الصغيرة بسبب ضوابط الأمان المحدودة. عادةً ما تركز مخططات الاحتيال المالي وتحويل مدفوعات البائعين على المؤسسات الصغيرة.
