🚀 أصبحت CloudSek أول شركة للأمن السيبراني من أصل هندي تتلقى استثمارات منها ولاية أمريكية صندوق
اقرأ المزيد
Double extoration ransomware هي طريقة هجوم إلكتروني حيث يقوم المهاجمون بتشفير الأنظمة واستخراج البيانات الحساسة أثناء عملية اختراق واحدة. يُطلب الدفع لفك التشفير، ويتم تهديد المعلومات المسروقة بالإفراج العام إذا تم رفض طلبات الفدية.
تجمع بنية الهجوم بين تشفير الملفات والسرقة المتعمدة للبيانات لزيادة الإكراه. لا تؤدي استعادة النسخ الاحتياطي إلى القضاء على مخاطر التعرض بسبب التسريبات العامة المحتملة.
يحدث إيقاف التشغيل من خلال التشفير، وينتج الضرر التنظيمي والمالي والسمعة عن تهديدات الكشف عن البيانات. تُعرّف استراتيجية الضغط المزدوج برامج الفدية بالابتزاز المزدوج كشكل متقدم من الابتزاز الإلكتروني.
تختلف برامج الفدية ذات الابتزاز المزدوج عن برامج الفدية التقليدية من خلال الجمع بين تشفير الملفات وسرقة البيانات وتهديدات التسرب العام لزيادة الضغط القسري.
تتبع برامج الفدية ذات الابتزاز المزدوج نموذج اختراق متعدد المراحل مصمم لتأمين كل من التعطيل التشغيلي والاستفادة من البيانات. كل مرحلة تعزز ضغط الابتزاز قبل بدء التفاوض على الفدية.
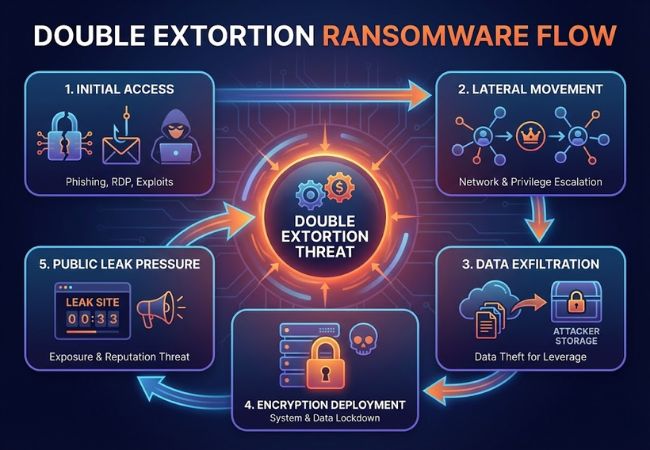
يحصل المهاجمون على إمكانية الدخول من خلال حملات التصيد الاحتيالي أو خدمات بروتوكول سطح المكتب البعيد المكشوفة أو حشو بيانات الاعتماد أو استغلال الثغرات الأمنية غير المصححة. غالبًا ما توفر الحسابات المخترقة امتيازات إدارية داخل بيئات المؤسسة.
تنتقل الجهات الفاعلة في مجال التهديد عبر قطاعات الشبكة لتحديد البنية التحتية الحيوية ومستودعات البيانات عالية القيمة. تتيح أدوات تصعيد الامتيازات وصولاً أعمق إلى وحدات تحكم المجال وخوادم الملفات وأنظمة النسخ الاحتياطي.
يتم نسخ البيانات الحساسة مثل السجلات المالية والملكية الفكرية وقواعد بيانات العملاء إلى البنية التحتية التي يتحكم فيها المهاجم. تعمل مجموعات البيانات المسروقة كرافعة في حالة رفض طلبات الفدية.
تقوم حمولات برامج الفدية بتشفير نقاط النهاية والخوادم ومشاركات الشبكة باستخدام خوارزميات تشفير قوية. تظل مفاتيح فك التشفير تحت سيطرة المهاجمين في انتظار دفع العملة المشفرة.
تنشر مواقع التسرب المخصصة المستضافة على شبكات الويب المظلمة عينات من البيانات المسروقة لإثبات صحتها. تؤدي تهديدات الإفصاح الكامل إلى تصعيد الضرر بالسمعة والتعرض التنظيمي والمسؤولية القانونية.
تزيد برامج الفدية ذات الابتزاز المزدوج من التأثير من خلال الجمع بين التعطيل التشغيلي والتعرض لخرق البيانات.
قامت مجموعات برامج الفدية المتعددة بتفعيل أساليب الابتزاز المزدوج لزيادة الامتثال للفدية والضغط العام.
قدمت Maze مواقع التسرب العامة في نوفمبر 2019 لفضح بيانات الشركة المسروقة بعد رفض الفدية. أدى نشر بيانات الضحايا إلى إنشاء نموذج إكراه جديد تم اعتماده لاحقًا عبر أنظمة برامج الفدية.
نفذت Revil هجمات واسعة النطاق على المؤسسات وسلسلة التوريد باستخدام التشفير جنبًا إلى جنب مع تهديدات تسرب البيانات. أظهرت الحملات التي تستهدف مزودي الخدمات المُدارة كيف يمكن للابتزاز المزدوج أن يضخم الاضطراب المنهجي.
قامت شركة Conti بتشغيل فرق داخلية منظمة مسؤولة عن التدخل والتفاوض ونشر البيانات. كشفت تسريبات الدردشة الداخلية عن عمليات ابتزاز منظمة واستراتيجيات دفع رسمية.
استفادت LockBit من نموذج Ransomware-as-a-Service لتوزيع قدرات الابتزاز المزدوجة على الشركات التابعة. عرضت بوابات التسريب المخصصة علنًا مجموعات البيانات المسروقة للضغط على الدفع السريع للعملات المشفرة.
تعمل برامج الفدية ثلاثية الابتزاز على توسيع أساليب الابتزاز المزدوج من خلال تقديم طبقة إكراه إضافية تتجاوز التشفير وسرقة البيانات. يطلب المهاجمون الدفع مقابل فك التشفير ومنع تسرب البيانات وتخفيف آلية الضغط الثالثة.
غالبًا ما يتضمن الضغط الإضافي هجمات الحرمان من الخدمة الموزعة ضد البنية التحتية العامة أو التهديدات المباشرة للعملاء وشركاء الأعمال. تتصل بعض المجموعات بأصحاب المصلحة مباشرة لتضخيم الضرر بالسمعة وإلحاح التفاوض.
يعكس التصعيد من الابتزاز المزدوج إلى الثلاثي التطور المستمر في استراتيجيات تحقيق الدخل من برامج الفدية. يزيد الضغط متعدد الطبقات من التعرض المالي ويعقد الاستجابة للحوادث عبر المنظمات المتأثرة.
يتطلب منع الابتزاز المزدوج رانسوم وير ضوابط أمنية متعددة الطبقات تتناول الوصول والكشف والاحتواء والاسترداد.
تقوم بنية Zero Trust بفرض التحقق المستمر من الهوية عبر المستخدمين والأجهزة وموارد الشبكة. يقلل الوصول الأقل امتيازًا من الحركة الجانبية ويحد من وصول المهاجم داخل بيئات المؤسسة.
تراقب حلول EDR سلوك نقطة النهاية لاكتشاف أنماط التشفير غير العادية ونشاط تصعيد الامتيازات. تتيح التحليلات السلوكية الاحتواء السريع قبل حدوث عملية استخراج البيانات على نطاق واسع.
يعمل تقسيم الشبكة على عزل الأنظمة الهامة عن بيئات المستخدم العامة. يمنع تدفق حركة المرور الداخلية المقيد المهاجمين من الوصول إلى الخوادم عالية القيمة بعد الاختراق الأولي.
تضمن النسخ الاحتياطية غير المتصلة بالإنترنت وغير القابلة للتغيير استعادة البيانات دون الاعتماد على دفع الفدية. يعمل اختبار الاسترداد المنتظم على التحقق من سلامة النسخ الاحتياطي والجداول الزمنية للاستعادة.
تعمل عمليات محاكاة التصيد الاحتيالي والتعليم المستمر للأمن السيبراني على تقليل مخاطر اختراق بيانات الاعتماد. يظل الدفاع المرتكز على الإنسان أمرًا بالغ الأهمية ضد نقاط دخول الهندسة الاجتماعية.
يحدد الاحتواء الفوري والتحقيق والتواصل المنظم شدة التأثير أثناء حادثة الابتزاز المزدوج لطلب الفدية.
افصل نقاط النهاية والخوادم ومقاطع الشبكة المصابة لمنع المزيد من الانتشار. قم بتعطيل بيانات الاعتماد المخترقة وحظر حركة مرور الأوامر والتحكم الضارة.
قم ببدء بروتوكولات الاستجابة الداخلية للحوادث وإشراك متخصصي الأمن السيبراني الخارجيين إذا لزم الأمر. احتفظ بالأدلة الجنائية بما في ذلك السجلات والتقاط الذاكرة وصور النظام.
تقييم الملفات وقواعد البيانات والسجلات التي تم الوصول إليها أو نقلها. تحديد التعرض للمعلومات المنظمة مثل البيانات المالية أو الرعاية الصحية أو البيانات الشخصية.
استشر المستشار القانوني لتقييم التزامات الإبلاغ بموجب قوانين حماية البيانات المعمول بها. قم بإرسال إشعارات الاختراق المطلوبة ضمن الجداول الزمنية الإلزامية.
قم بإعداد الإفصاحات الخاضعة للرقابة للعملاء والشركاء والموظفين. التواصل الشفاف يقلل من المضاربة ويحد من الضرر بالسمعة.
قم بإعادة إنشاء البنية التحتية المتأثرة باستخدام نسخ احتياطية نظيفة تم التحقق منها بعد التحقق من الأمان. تعزيز ضوابط الوصول وقدرات المراقبة قبل الاستعادة التشغيلية الكاملة.
تتطلب الحماية الفعالة من برامج الفدية إمكانات متكاملة تمنع التسلل وتكتشف السلوك الضار وتحتوي على تسريب البيانات.
يجب أن تراقب أنظمة الأمان باستمرار حركة مرور الشبكة ونشاط نقطة النهاية وأنماط المصادقة. يعمل التنبيه الفوري على تقليل وقت بقاء المهاجم قبل بدء التشفير.
تكتشف محركات التحليلات المتقدمة الحالات الشاذة مثل الوصول غير المعتاد إلى الملفات أو محاولات تصعيد الامتيازات. يحدد الاكتشاف السلوكي أنماط برامج الفدية بما يتجاوز الأساليب القائمة على التوقيع.
تمنع مراقبة حركة المرور الصادرة عمليات نقل البيانات غير المصرح بها إلى البنية التحتية الخارجية. يقلل اكتشاف التسلل من الرافعة المالية المتاحة للابتزاز المزدوج.
يعمل الاحتواء الآلي على عزل الأجهزة المخترقة دون تأخير يدوي. تحد الاستجابة السريعة من الحركة الجانبية عبر شبكات المؤسسة.
يجب أن تظل النسخ الاحتياطية غير متصلة بالإنترنت أو غير قابلة للعبث لمنع التشفير أو الحذف من قبل المهاجمين. يضمن الاختبار المنتظم قدرة استعادة موثوقة.
تدعم مسارات التدقيق المضمنة الوثائق التنظيمية والتزامات الإبلاغ عن الخرق. تعمل التقارير المنظمة على تبسيط التحقيق بعد الحادث والمراجعة القانونية.
تعمل منصات الأمن السيبراني الحديثة على تقليل مخاطر الابتزاز المزدوج من خلال الرؤية الموحدة والاستجابة الآلية والكشف القائم على الذكاء.
تجمع المنصات المتكاملة بين حماية نقطة النهاية ومراقبة الشبكة وأمن الهوية والدفاع السحابي في نظام بيئي واحد. تعمل الرؤية المركزية على تقليل النقاط العمياء التي يتم استغلالها أثناء الحركة الجانبية.
تحدد خلاصات معلومات التهديدات في الوقت الفعلي البنية التحتية المعروفة لبرامج الفدية والنطاقات الضارة وتكتيكات المهاجمين الناشئين. يعمل الارتباط الذكي على تحسين الاكتشاف المبكر قبل نشر التشفير.
تكتشف نماذج التعلم الآلي أنماط التشفير غير الطبيعية ونشاط تنظيم البيانات وعمليات النقل الصادرة غير العادية. يعزز التحليل السلوكي الدفاع ضد متغيرات برامج الفدية ذات اليوم الصفري.
تستفيد مراكز العمليات الأمنية من المراقبة المستمرة لتقليل وقت بقاء المهاجم. تمنع إجراءات الاحتواء السريع التشفير الواسع النطاق وتسريب البيانات على نطاق واسع.
يعمل العزل التلقائي لنقطة النهاية على تقييد الأجهزة المخترقة دون تأخير يدوي. تعمل عناصر التحكم على مستوى الشبكة على حظر قنوات اتصال الأوامر والتحكم.
يعمل التصنيف الشامل للبيانات على تحديد الأصول الحساسة عبر بيئات المؤسسات. تعمل ضوابط الحوكمة على تقييد الوصول غير المصرح به إلى المستودعات عالية القيمة.
تمثل برامج الفدية ذات الابتزاز المزدوج تطورًا كبيرًا في الابتزاز الإلكتروني من خلال الجمع بين التشفير وسرقة البيانات المتعمدة وتهديدات التعرض العام. لم يعد الاضطراب التشغيلي وحده يحدد تأثير برامج الفدية، حيث تعمل المسؤولية التنظيمية والأضرار التي تلحق بالسمعة الآن على تضخيم المخاطر المالية.
تتطلب المرونة ضد الابتزاز المزدوج ضوابط أمنية متعددة الطبقات، والمراقبة المستمرة، وإدارة الوصول القوية، وقدرات الاستجابة للحوادث التي تم اختبارها. تعمل المؤسسات التي تعطي الأولوية للوقاية والكشف والاسترداد الآمن على تقليل التعرض لواحد من أكثر نماذج برامج الفدية عدوانية في الأمن السيبراني الحديث.
