🚀 أصبحت CloudSek أول شركة للأمن السيبراني من أصل هندي تتلقى استثمارات منها ولاية أمريكية صندوق
اقرأ المزيد
يبحث مجرمو الإنترنت باستمرار عن طرق للربح من الأنظمة المخترقة، وإحدى الطرق التي جذبت الانتباه هي استخدام برامج تعدين العملات المشفرة المخفية. بدلاً من سرقة البيانات أو قفل الملفات، يتحكم المهاجمون سرًا في موارد الحوسبة ويحولون تلك القوة إلى عملة رقمية. يتيح لهم هذا النهج تحقيق إيرادات مستمرة بينما يستمر جهاز الضحية في العمل بشكل طبيعي.
نما حجم هذا النشاط بسرعة حيث يقوم المهاجمون بأتمتة التعدين عبر آلاف الأجهزة. ووفقًا لتقرير سيسكو تالوس لمعلومات التهديدات، فإن البرامج الضارة لتعدين العملات المشفرة كانت تمثل في السابق أكثر من 90% من جميع البرامج الضارة المكتشفة في البيئات السحابية، مما يسلط الضوء على مدى استغلال المهاجمين لموارد الحوسبة لتعدين العملات المشفرة. يعد فهم كيفية عمل البرامج الضارة المشفرة أمرًا ضروريًا للتعرف على السلوك المشبوه وحماية الأجهزة ومنع نشاط التعدين غير المصرح به.
البرامج الضارة المشفرة هي برامج ضارة تستخدم سرًا كمبيوتر الضحية أو خادمها لتعدين العملة المشفرة للمهاجم. بدلاً من سرقة الملفات أو قفل الأنظمة، تستغل هذه البرامج الضارة قوة المعالجة، مثل وحدة المعالجة المركزية أو وحدة معالجة الرسومات، لتوليد عملات رقمية مثل Bitcoin أو Monero.
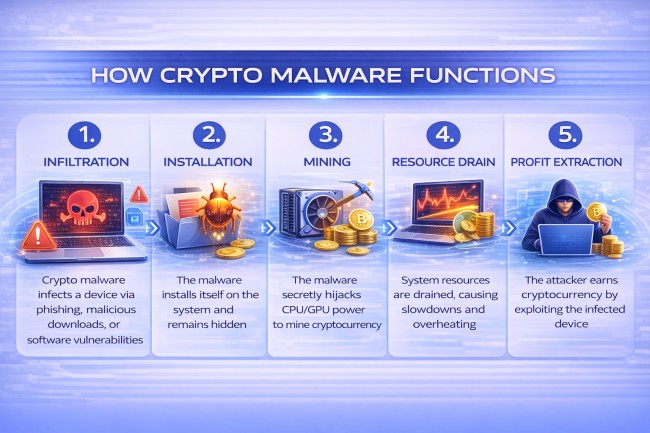
تعمل برامج التشفير الضارة عن طريق تثبيت برامج التعدين سراً على جهاز الضحية واستخدام قوة المعالجة الخاصة بها لتوليد العملة المشفرة. يمكن للمهاجمين أولاً الوصول إلى النظام من خلال طرق مثل التنزيلات الضارة أو مرفقات البريد الإلكتروني المصابة أو مواقع الويب المخترقة. بمجرد دخول البرامج الضارة إلى النظام، تقوم بتثبيت مكون التعدين دون علم المستخدم.
بعد التثبيت، تبدأ البرامج الضارة باستخدام وحدة المعالجة المركزية للجهاز أو وحدة معالجة الرسومات لحل حسابات التشفير المعقدة المطلوبة لتعدين العملات المشفرة. يتم إجراء هذه الحسابات بشكل مستمر في الخلفية بينما يظل الجهاز قيد الاستخدام. ويتصل النظام المصاب بمجموعة تعدين عن بُعد يتحكم فيها المهاجم، والتي تنسق نشاط التعدين عبر العديد من الأجهزة المخترقة.
نظرًا لأن الجهاز يساهم بقوة الحوسبة في مجمع التعدين، يتم نقل أي عملة مشفرة يتم إنشاؤها إلى المحفظة الرقمية للمهاجم. لا تتلقى الضحية أي فائدة ولكنها تعاني من أداء أبطأ واستهلاك أعلى للطاقة وإجهاد محتمل للأجهزة بسبب عبء العمل المستمر.
تتخذ البرامج الضارة المشفرة عدة أشكال اعتمادًا على كيفية دخولها إلى النظام وكيفية استخدامها لموارد الجهاز للتعدين. يستخدم كل نوع أسلوبًا مختلفًا لاستغلال موارد الحوسبة لتوليد عملة مشفرة للمهاجم.
فيما يلي الأنواع الرئيسية من البرامج الضارة المشفرة:
تقوم البرامج الضارة Cryptojacking بتثبيت برنامج تعدين على جهاز دون إذن المالك. بمجرد تنشيطه، فإنه يستخدم قوة معالجة النظام لتعدين العملة المشفرة بشكل مستمر. يقوم المهاجم بجمع العملات المعدنية الملغومة بينما تعاني الضحية من انخفاض الأداء وزيادة استخدام الطاقة.
تعمل البرامج الضارة المشفرة القائمة على الملفات كبرنامج ضار تقليدي مثبت على النظام. وعادةً ما تصل من خلال التنزيلات المصابة أو مرفقات البريد الإلكتروني أو برامج تثبيت البرامج المخترقة. بعد التنفيذ، تقوم البرامج الضارة بتثبيت مكون تعدين يعمل في الخلفية.
تعمل برامج التشفير الضارة التي لا تحتوي على ملفات في ذاكرة النظام بدلاً من تثبيت الملفات على القرص الصلب. غالبًا ما يستخدم أدوات النظام الشرعية مثل PowerShell أو بيئات البرمجة النصية. نظرًا لأنه يترك آثارًا أقل على الجهاز، فقد يكون من الصعب على أدوات الأمان التقليدية اكتشافها.
تستخدم البرامج الضارة لتعدين العملات المشفرة المستندة إلى المتصفح البرامج النصية المضمنة في مواقع الويب لبدء تعدين العملة المشفرة عندما يزور المستخدم الصفحة. تتم عملية التعدين من خلال متصفح الويب وتتوقف بمجرد مغادرة المستخدم للموقع. هذه البرامج النصية تسيء استخدام موارد جهاز الزائر أثناء فتح الصفحة.
بوت نتتصيب البرامج الضارة المشفرة القائمة على أعداد كبيرة من الأجهزة وتربطها بشبكة الأوامر والتحكم. يتحكم المهاجمون عن بُعد في الأجهزة المصابة ويجمعون بين قوتهم الحاسوبية لتعدين العملات المشفرة على نطاق واسع. يسمح هذا النهج للمجرمين بتوليد إيرادات تعدين مستمرة من آلاف الأنظمة المخترقة.
التشفير البرامج الضارة وبرامج الفدية كلاهما شكل من أشكال البرامج الضارة، ولكنهما يدران الربح بطرق مختلفة. تستخدم البرامج الضارة المشفرة سرًا موارد الحوسبة الخاصة بالضحية لتعدين العملة المشفرة للمهاجم، بينما تقوم برامج الفدية بتشفير الملفات والمطالبة بالدفع لاستعادة الوصول.
عادةً ما تعمل البرامج الضارة المشفرة بصمت في الخلفية، مما يسمح للمهاجمين بكسب المال بمرور الوقت دون تنبيه الضحية. رانسوم وير، من ناحية أخرى، يعطل الأنظمة بشكل علني ويجبر الضحية على دفع فدية لاستعادة بياناتها.
تعد البرامج الضارة المشفرة خطيرة لأنها تستهلك موارد الحوسبة بصمت دون إذن المالك. تستخدم الأنظمة المصابة وحدة المعالجة المركزية أو وحدة معالجة الرسومات الخاصة بها باستمرار لتعدين العملة المشفرة للمهاجمين. يقلل عبء العمل المستمر هذا من أداء النظام ويبطئ العمليات اليومية.
وبمرور الوقت، يمكن أن يتسبب الاستخدام المكثف للموارد في إجهاد الأجهزة. قد ترتفع درجة حرارة الأجهزة، وقد تتلف المكونات الداخلية مثل المعالجات وأنظمة التبريد بشكل أسرع. في البيئات الكبيرة مثل مراكز البيانات أو شبكات الشركات، يمكن أن يؤدي هذا النشاط إلى زيادة تكاليف الكهرباء وتقليل موثوقية النظام.
يمكن أن تؤدي البرامج الضارة المشفرة أيضًا إلى مخاطر أمنية تتجاوز إساءة استخدام الموارد. بمجرد وصول المهاجمين إلى النظام، يمكنهم تثبيت برامج ضارة إضافية أو استخدام الجهاز المخترق لنشر العدوى عبر الشبكة. هذا يجعل البرامج الضارة المشفرة ليست مشكلة في الأداء فحسب، بل أيضًا بوابة محتملة لهجمات إلكترونية أكبر.
في عام 2017، انتشرت حملة كبيرة لتعدين العملات المشفرة تُعرف باسم Smominru عبر الإنترنت من خلال استغلال ثغرة أمنية في Windows تسمى EternalBlue. أصابت العملية أكثر من 500,000 جهاز كمبيوتر في جميع أنحاء العالم وقامت بتثبيت برنامج تعدين العملات المشفرة سراً. استخدم المهاجمون الأجهزة المصابة لتعدين عملة Monero المشفرة بينما عانى الضحايا من أنظمة أبطأ واستخدام أعلى للموارد. قدر باحثو الأمن أن المهاجمين حققوا ملايين الدولارات من العملات المشفرة قبل تعطيل الروبوتات.
بين عامي 2017 و 2019، أساء المهاجمون على نطاق واسع استخدام برنامج تعدين قائم على المتصفح يسمى Coinhive. تم تصميم البرنامج النصي في الأصل لمالكي مواقع الويب لتعدين Monero باستخدام موارد وحدة المعالجة المركزية للزوار، ولكن العديد من المهاجمين قاموا بتضمينه سراً في مواقع الويب المخترقة. عندما زار المستخدمون هذه الصفحات، بدأت متصفحاتهم في تعدين العملات المشفرة دون علمهم. تأثر الملايين من مستخدمي الإنترنت قبل أن تبدأ المتصفحات وأدوات الأمان في حظر البرنامج النصي.
في عام 2020، استهدفت حملة LemonDuck للبرامج الضارة المنظمات والأنظمة الفردية من خلال الانتشار عبر رسائل البريد الإلكتروني المخادعة والخوادم الضعيفة. بمجرد التثبيت، استخدمت البرامج الضارة الأجهزة المصابة لتعدين العملة المشفرة وانتشارها إلى أنظمة أخرى على الشبكة. أثرت الحملة على آلاف أجهزة الكمبيوتر في جميع أنحاء العالم وقللت بشكل كبير من أداء النظام في البيئات المعرضة للخطر. أفاد باحثو الأمن لاحقًا أن المهاجمين قاموا بتحديث البرامج الضارة باستمرار لتجنب الاكتشاف والحفاظ على السيطرة على الأجهزة المصابة.

عندما يكون الجهاز مصابًا ببرامج تشفير ضارة، فإنه عادةً ما يظهر علامات مثل:
تكتشف فرق الأمان البرامج الضارة للعملات المشفرة من خلال مراقبة نشاط النظام غير المعتاد واستخدام الموارد وسلوك الشبكة الذي يشير إلى التعدين غير المصرح به للعملات المشفرة. كشف يركز على تحديد الأنماط التي تختلف عن عمليات الجهاز العادية.
تراقب فرق الأمان استخدام وحدة المعالجة المركزية ووحدة معالجة الرسومات عبر الأنظمة. غالبًا ما تعمل البرامج الضارة المشفرة بشكل مستمر وتتسبب في استخدام المعالج بشكل غير طبيعي حتى عندما يكون الجهاز خاملاً. يمكن أن يشير الاستهلاك العالي المستمر للموارد إلى نشاط تعدين غير مصرح به.
تتعقب منصات أمان Endpoint النشاط على أجهزة الكمبيوتر والخوادم. تراقب هذه الأدوات العمليات الجارية وتغييرات البرامج وسلوك النظام غير الطبيعي. قد تشير البرامج المشبوهة التي تستخدم كميات كبيرة من طاقة المعالجة إلى برامج التعدين الضارة.
تقارن أدوات التحليل السلوكي النشاط الحالي مع أنماط الاستخدام العادية. عندما يُظهر الجهاز فجأة ارتفاعًا مستمرًا في المعالج أو سلوكًا غير عادي للتطبيق، يقوم النظام بوضع علامة عليه للتحقيق. تساعد هذه الطريقة في تحديد عمليات التعدين المخفية.
عادةً ما تتصل البرامج الضارة المشفرة بمجمعات تعدين العملات المشفرة أو خوادم الأوامر. تقوم فرق الأمان بتحليل حركة مرور الشبكة لاكتشاف الاتصال بالمجالات المشبوهة أو البنية التحتية للتعدين. يمكن أن تكشف الاتصالات الخارجية غير المتوقعة عن إصابات نشطة.
توفر منصات معلومات التهديدات معلومات حول حملات التعدين المعروفة والنطاقات الضارة والبنية التحتية للمهاجمين. تقارن فرق الأمان نشاط الشبكة الداخلية بهذه المعلومات لتحديد الإصابات المحتملة بالبرامج الضارة المشفرة.
يمكنك منع البرامج الضارة المشفرة من خلال تأمين الأجهزة والتحكم في تنفيذ البرامج ومراقبة نشاط الشبكة. تقلل الممارسات الوقائية القوية من فرص المهاجمين في تثبيت برامج التعدين غير المصرح بها.
فيما يلي أفضل الممارسات لمنع البرامج الضارة المشفرة:
قم بتثبيت الحماية الموثوقة لنقطة النهاية وأدوات مكافحة الفيروسات على جميع الأنظمة. تقوم هذه الحلول باكتشاف وحظر الملفات الضارة وبرامج التعدين والعمليات المشبوهة. تضمن التحديثات المنتظمة الحماية ضد تهديدات التعدين المشفرة الجديدة.
استخدم إعدادات أمان المتصفح والإضافات التي تحظر البرامج النصية غير المصرح بها. تعتمد العديد من هجمات التشفير المستندة إلى المتصفح على البرامج النصية المخفية المضمنة في مواقع الويب. تساعد أدوات حظر البرامج النصية وتكوينات المتصفح الآمنة على منع هذه الهجمات.
حافظ على تحديث أنظمة التشغيل والتطبيقات والمكونات الإضافية بأحدث تصحيحات الأمان. تستغل العديد من حالات الإصابة بالتعدين المشفر نقاط ضعف البرامج القديمة. تعمل التحديثات المنتظمة على سد هذه الثغرات الأمنية.
الحد من القدرة على تشغيل برامج أو نصوص غير معروفة على الأنظمة. تسمح سياسات التحكم في التطبيقات بتنفيذ البرامج المعتمدة فقط. هذا يمنع برامج التعدين المخفية من البدء.
راقب حركة مرور الشبكة وحظر الاتصالات بمجمعات تعدين العملات المشفرة المعروفة أو المجالات المشبوهة. يمكن لبوابات الأمان وجدران الحماية إيقاف الأجهزة المصابة من الاتصال بالبنية التحتية للمهاجم.
قم بتوعية المستخدمين بمخاطر تنزيل برامج غير معروفة أو النقر فوق الروابط المشبوهة أو فتح مرفقات بريد إلكتروني غير متوقعة. تبدأ العديد من إصابات البرامج الضارة المشفرة من خلال التنزيلات غير الآمنة أو محاولات التصيد الاحتيالي.
نعم، البرامج الضارة المشفرة غير قانونية. يستخدم سرًا كمبيوتر أو خادم شخص آخر لتعدين العملة المشفرة دون إذن.
تستخدم البرامج الضارة المشفرة موارد النظام لتعدين العملة المشفرة في الخلفية. تقوم Ransomware بتشفير الملفات والمطالبة بالدفع لاستعادة الوصول.
نعم، يمكن أن تصيب البرامج الضارة المشفرة الهواتف الذكية والأجهزة اللوحية. يمكن للتطبيقات الضارة أو مواقع الويب المصابة تثبيت برامج التعدين المخفية على الأجهزة المحمولة.
نعم، يمكن لأدوات مكافحة الفيروسات الحديثة وأدوات أمان نقطة النهاية اكتشاف العديد من تهديدات التشفير. وهي تحدد العمليات المشبوهة ونصوص التعدين والاستخدام غير المعتاد للموارد.
