🚀 أصبحت CloudSek أول شركة للأمن السيبراني من أصل هندي تتلقى استثمارات منها ولاية أمريكية صندوق
اقرأ المزيد
يُعد اكتشاف التهديدات والاستجابة لها إطارًا للأمن السيبراني مصممًا لتحديد الأنشطة الضارة عبر نقاط النهاية والشبكات والأنظمة السحابية. إنه يمكّن المؤسسات من اكتشاف التهديدات الأمنية مبكرًا والحد من الاضطرابات التشغيلية.
تولد بيئات تكنولوجيا المعلومات الحديثة كميات هائلة من بيانات الأمان التي تتطلب مراقبة منظمة وإجراءات منسقة. تقوم الفرق المخصصة داخل مركز عمليات الأمان بإدارة التنبيهات والتحقق من المخاطر وتنفيذ استراتيجيات الاحتواء للحفاظ على سلامة النظام.
يعزز TDR الوضع الأمني العام من خلال الجمع بين الرؤية والتحليل والمعالجة المنسقة في نهج دفاعي موحد. تعتمد المؤسسات هذا الإطار للحد من تأثير الاختراق والحفاظ على استمرارية الأعمال.
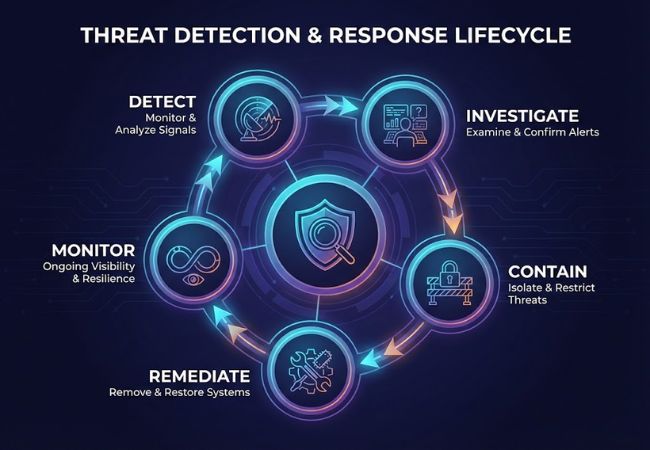
يعمل اكتشاف التهديدات والاستجابة لها من خلال دورة حياة تشغيلية منظمة تحول إشارات الأمان إلى علاج متحكم فيه.
يعتمد اكتشاف التهديدات والاستجابة لها على العديد من القدرات التأسيسية التي توفر الرؤية والسياق والتحكم الأمني المنسق عبر البنية التحتية الرقمية للمؤسسة.
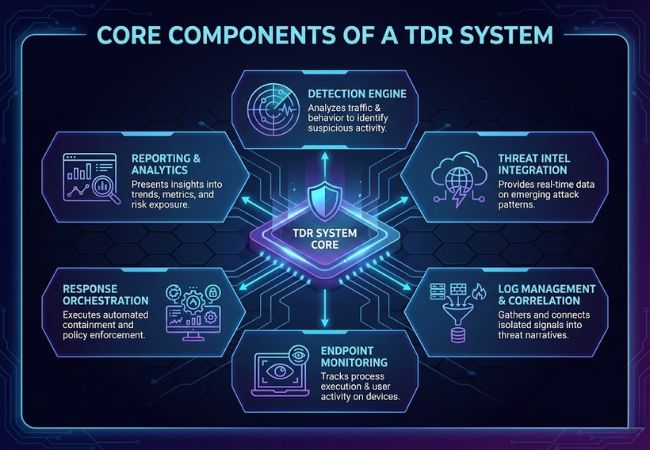
تقوم محركات الكشف بتحليل حركة مرور الشبكة وسجلات النظام ونشاط نقطة النهاية لتحديد السلوك المشبوه. تساعد التحليلات السلوكية والتعرف القائم على التوقيع في الكشف عن مؤشرات التسوية قبل انتشار الضرر.
توفر خلاصات معلومات التهديدات معلومات محدثة حول أنماط الهجوم الناشئة وعناوين IP الضارة وتقنيات الاستغلال. تعمل المعلومات المتكاملة على تحسين دقة التنبيه وتساعد على تحديد أولويات الحوادث عالية الخطورة.
تجمع مجموعة السجلات المركزية بيانات الأمان من الخوادم وجدران الحماية والتطبيقات والأنظمة الأساسية السحابية. تربط آليات الارتباط الإشارات المعزولة بروايات التهديد الهادفة التي توجه التحقيق.
تقوم مراقبة مستوى نقطة النهاية بتتبع تنفيذ العملية وتعديلات الملفات ونشاط المستخدم على الأجهزة. تتيح الرؤية العميقة الاكتشاف المبكر لبرامج الفدية وإساءة استخدام بيانات الاعتماد وتغييرات النظام غير المصرح بها.
تقوم أدوات التنسيق الآلي بتنفيذ إجراءات الاحتواء المحددة مسبقًا بمجرد تأكيد التهديد. يؤدي عزل الجهاز وتقييد الوصول وتطبيق السياسة إلى تقليل وقت الاستجابة والحد من الحركة الجانبية.
تقدم لوحات معلومات الأمان رؤى في الوقت الفعلي حول اتجاهات التهديدات ومقاييس الاستجابة والتعرض للمخاطر بشكل عام. تدعم البيانات القابلة للقياس متطلبات الامتثال ومبادرات التحسين المستمر.
تم تصميم اكتشاف التهديدات والاستجابة لها لتحديد مجموعة واسعة من التهديدات الإلكترونية التي تتراوح من البرامج الضارة الشائعة إلى حملات الهجوم المتقدمة والمستمرة.
تتضمن البرامج الضارة برامج ضارة مثل أحصنة طروادة وبرامج التجسس والديدان التي تتسلل إلى الأنظمة لسرقة البيانات أو تعطيل العمليات. تساعد المراقبة السلوكية على اكتشاف أنماط التنفيذ الضارة حتى عندما يكون توقيع الملف غير معروف.
تقوم Ransomware بتشفير الملفات الهامة وتطالب بالدفع مقابل الوصول إلى الاستعادة. يقلل الاكتشاف المبكر لنشاط تشفير الملفات غير الطبيعي من احتمالية اختراق النظام على نطاق واسع.
تخدع هجمات التصيد الاحتيالي المستخدمين للكشف عن بيانات اعتماد تسجيل الدخول أو البيانات الحساسة من خلال الاتصالات الخادعة. تساعد مراقبة محاولات المصادقة غير العادية وتصعيد الامتيازات في الكشف عن إساءة استخدام بيانات الاعتماد بسرعة.
تنشأ التهديدات الداخلية من الموظفين أو المقاولين الذين يسيئون استخدام الوصول المصرح به. تكتشف مراقبة النشاط عمليات نقل البيانات غير المنتظمة أو انتهاكات السياسة أو الوصول غير المصرح به إلى النظام.
تستهدف عمليات الاستغلال في Zero day الثغرات الأمنية غير المعروفة سابقًا قبل أن تصبح التصحيحات متاحة. يزيد اكتشاف الشذوذ وتحليل السلوك من فرص تحديد محاولات الاستغلال دون الاعتماد على التوقيعات المعروفة.
تتضمن التهديدات المستمرة المتقدمة حملات اختراق طويلة المدى مدفوعة بالخفي غالبًا ما تستهدف الأصول ذات القيمة العالية. يساعد تحليل الأحداث المترابطة في الكشف عن أنماط الهجوم الدقيقة متعددة المراحل التي تتطور بمرور الوقت.
يمثل اكتشاف التهديدات والاستجابة لها إطارًا استراتيجيًا، بينما تمثل EDR و XDR و SIEM تقنيات محددة تدعم وظائف الكشف والتحقيق.
تعمل قدرات الكشف والاستجابة القوية على تحسين المرونة الأمنية وتقليل تأثير الاختراق وتعزيز التحكم التشغيلي عبر البيئات الرقمية.
تتيح المراقبة المستمرة التعرف المبكر على النشاط المشبوه عبر نقاط النهاية والشبكات. يقلل وقت الاكتشاف المنخفض من حركة المهاجم ويمنع التصعيد.
يؤدي التحقيق السريع والاحتواء إلى تقليل الوقت الذي يظل فيه المهاجم غير مكتشف داخل الأنظمة. يقلل وقت الإقامة الأقصر بشكل مباشر من التعرض للبيانات والخسارة المالية.
تقوم عمليات سير عمل الاستجابة المحددة مسبقًا بتنفيذ إجراءات الاحتواء دون تأخير يدوي. تعمل الأتمتة على تحسين الاتساق وتقليل الضغط على فرق الأمان.
تعمل الرؤية المركزية على تبسيط إدارة التنبيهات وتحديد الأولويات. تقضي فرق الأمان وقتًا أقل في تصفية الإيجابيات الكاذبة والمزيد من الوقت في حل التهديدات الحقيقية.
يعمل الاحتواء المبكر على تقليل وقت التعطل وتكاليف الاسترداد والعقوبات التنظيمية. تحمي الحوادث التي يتم التحكم فيها سمعة العلامة التجارية واستمرارية الأعمال على المدى الطويل.
يدعم التسجيل المنظم وعمليات المعالجة الموثقة متطلبات إعداد التقارير التنظيمية. تعمل مسارات التدقيق الواضحة على تحسين المساءلة والإشراف على الحوكمة.
يتطلب اختيار حل اكتشاف التهديدات والاستجابة لها تقييم العمق التقني والملاءمة التشغيلية وقابلية التوسع على المدى الطويل.
تتكامل الحلول القوية بسلاسة مع أدوات الأمان الحالية مثل حماية نقطة النهاية والمنصات السحابية وأنظمة الهوية. يمنع التكامل السلس صوامع البيانات ويحسن الرؤية عبر الأنظمة الأساسية.
تجمع المنصات الفعالة بين التحليلات السلوكية وذكاء التهديدات لتقليل الإيجابيات الكاذبة. تضمن الدقة العالية تركيز فرق الأمن على المخاطر الحقيقية بدلاً من إرهاق التنبيه.
توفر الحلول المتقدمة عمليات سير عمل الاحتواء المؤتمتة التي تؤدي إلى إجراءات استجابة محددة مسبقًا. تعمل الأتمتة على تقليل وقت الاستجابة وضمان التعامل المتسق مع الحوادث.
تدعم البنيات القابلة للتطوير النمو عبر البيئات السحابية والهجينة والبيئات المحلية. تضمن التغطية الواسعة امتداد الحماية إلى نقاط النهاية والشبكات وطبقات الهوية.
تعمل ميزات إعداد التقارير الشاملة على إنشاء مسارات التدقيق ووثائق الحوادث. الرؤية الواضحة للمقاييس تدعم متطلبات الحوكمة والمتطلبات التنظيمية.
يعمل دعم البائع الموثوق به على تعزيز الاستعداد للاستجابة للحوادث وتحسين النظام الأساسي. الوصول إلى إرشادات الخبراء يعزز الوضع الأمني على المدى الطويل.
يوفر اكتشاف التهديدات والاستجابة لها نهجًا منظمًا لتحديد التهديدات الإلكترونية والتحقيق فيها والتخفيف من حدتها عبر البيئات الرقمية المعقدة. يعمل الاكتشاف القوي المقترن بالاستجابة المنسقة على تقليل تأثير الاختراق وتعزيز المرونة الأمنية على المدى الطويل.
تضع المؤسسات التي تستثمر في الرؤية المتكاملة وقدرات الاحتواء السريع نفسها لإدارة المخاطر السيبرانية المتطورة بشكل أكثر فعالية. تعمل الإستراتيجية الناضجة لاكتشاف التهديدات والاستجابة لها على تحويل الأمان من معالجة التنبيهات التفاعلية إلى إدارة مخاطر خاضعة للرقابة وقابلة للقياس.
تعتمد أدوات مكافحة الفيروسات التقليدية بشكل أساسي على الاكتشاف المستند إلى التوقيع لحظر التهديدات المعروفة. يعمل اكتشاف التهديدات والاستجابة لها على تحليل السلوك وربط الأحداث عبر الأنظمة وتنسيق الاحتواء خارج جهاز واحد.
لا يوجد حل أمني يمكن أن يضمن الوقاية الكاملة من جميع الانتهاكات. يقلل اكتشاف التهديدات والاستجابة لها من التعرض للمخاطر من خلال تحديد النشاط المشبوه مبكرًا والحد من حركة المهاجم قبل حدوث ضرر كبير.
تكتسب الصناعات التي تتعامل مع البيانات الحساسة مثل التمويل والرعاية الصحية وتجارة التجزئة والحكومة قيمة كبيرة من قدرات الكشف والاستجابة المنظمة. يزيد الضغط التنظيمي المرتفع واستهداف التهديدات المرتفع من أهمية الاحتواء السريع.
تعزز الخبرة الداخلية التنفيذ والإشراف، لكن خدمات الكشف المُدارة يمكن أن تكمل القدرات الداخلية. تجمع العديد من المؤسسات بين الأتمتة ودعم المراقبة الخارجية للحفاظ على تغطية متسقة.
توفر المراقبة المركزية وتحليل الأحداث المترابطة رؤية موحدة للنشاط المشبوه عبر الأنظمة. تعمل الرؤية الموحدة على تقليل النقاط العمياء وتحسين عملية صنع القرار أثناء الحوادث النشطة.
