🚀 أصبحت CloudSek أول شركة للأمن السيبراني من أصل هندي تتلقى استثمارات منها ولاية أمريكية صندوق
اقرأ المزيد
Real-time threat detection is the capability of security systems to identify and respond to malicious activity as it happens. Continuous monitoring enables immediate visibility into suspicious behavior across networks, endpoints, and cloud environments.
Security platforms analyze streams of data such as login activity, traffic patterns, and system events to detect irregularities. Rapid detection helps prevent threats from escalating into larger security incidents or breaches.
Modern cybersecurity environments rely on real-time detection to maintain operational resilience and reduce response time. Growing complexity of digital infrastructure makes instant threat identification essential for maintaining control and visibility.
Security platforms detect threats in real time by analyzing continuous data streams using multiple detection methods.
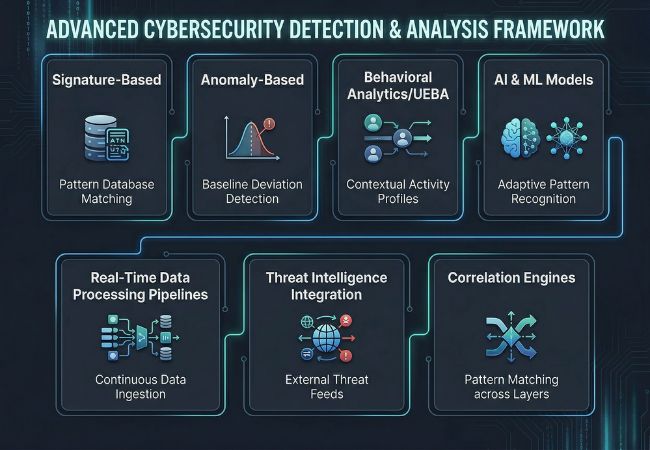
Signature-based detection matches activity against a database of known threat patterns and malware signatures. High reliability makes it effective for identifying previously documented attacks quickly.
Limitations appear when new or evolving threats do not match existing signatures. Dependence on known patterns reduces its effectiveness against zero-day attacks.
Anomaly-based detection identifies deviations from established normal behavior using statistical and machine learning models. Ability to detect unknown threats makes it essential for modern security systems.
Baseline behavior is continuously analyzed to flag unusual spikes or irregular activity patterns. Detection of subtle deviations improves early identification of emerging threats.
Behavioral analytics monitors user and entity activities to identify suspicious patterns over time. Systems like UEBA evaluate login behavior, access patterns, and lateral movement across networks.
Context-driven analysis improves differentiation between legitimate actions and malicious intent. Deeper visibility reduces reliance on static rules and enhances detection accuracy.
AI and machine learning models analyze large-scale security data to detect patterns that traditional rules may miss. Adaptive learning enables systems to improve detection as new threats emerge.
Automated analysis reduces manual effort and increases detection speed across complex environments. Continuous model training helps systems stay aligned with evolving attack techniques.
Real-time processing pipelines ingest and analyze data from multiple sources without delay. Stream processing engines evaluate events instantly to identify suspicious activity.
Low-latency processing ensures threats are detected as they occur rather than after analysis delays. Efficient pipelines are essential for maintaining real-time visibility and response.
Threat intelligence integration enriches detection systems with external data on known threats and attack indicators. Updated intelligence feeds provide insights into active attack campaigns and emerging risks.
Integration of global threat data improves contextual awareness and detection precision. Continuous updates ensure systems remain aligned with evolving threat landscapes.
Correlation engines combine data from multiple sources to identify meaningful threat patterns. Cross-layer analysis helps eliminate isolated signals that may not indicate real threats.
Correlated insights improve threat identification by providing full context of an event. This reduces duplicate alerts and strengthens decision-making.
False positives occur due to gaps in context, data interpretation, and detection configuration within security systems.
Security systems reduce false positives in real time by combining contextual analysis, adaptive learning, and multi-layered data validation.
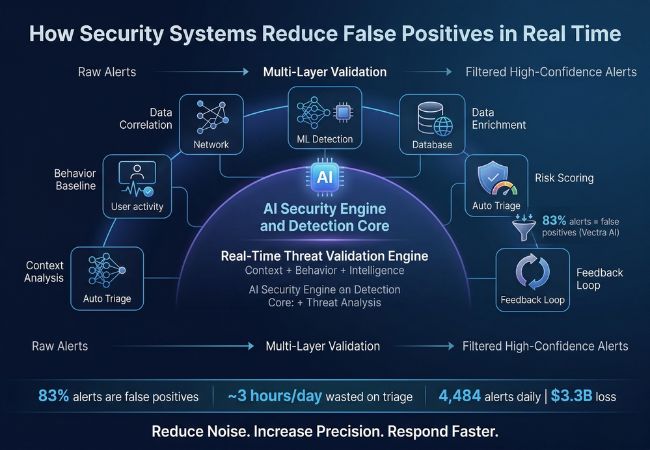
Data correlation engines connect signals from endpoints, networks, and cloud systems to validate suspicious activity. Cross-source visibility helps filter out isolated alerts that often appear misleading.
Behavioral baselining builds a clear picture of normal user and system activity over time. Familiar patterns help systems spot real anomalies instead of reacting to routine behavior.
Machine learning models process large volumes of historical and real-time data to refine detection patterns. Continuous improvement helps reduce repeated false alerts and improves precision.
AI-driven systems analyze relationships between events, users, and systems to add deeper context. Better context allows platforms to distinguish between harmless activity and real threats more accurately.
Real-time data enrichment adds external and internal context such as threat intelligence and asset details to alerts. Richer data helps systems make more informed decisions during detection.
Risk scoring assigns severity levels to alerts based on impact and likelihood. Clear prioritization ensures critical threats are addressed while low-risk alerts are filtered out.
Automated triage systems filter low-confidence alerts before they reach analysts. Vectra AI reports that SOC analysts lose nearly three hours daily to manual triage because 83% of alerts are false positives, contributing to $3.3 billion in annual losses and around 4,484 alerts each day.
Feedback loops allow analysts to validate alerts and refine detection logic over time. Ongoing tuning helps systems adapt to changing threat patterns while steadily reducing false positives.
Accuracy in real-time threat detection depends on how effectively systems manage signal clarity, processing latency, and alert validation across high-volume environments. Detection pipelines must filter irrelevant activity early to ensure only high-confidence events move forward for analysis.
Sensitivity control plays a critical role in maintaining balance between over-alerting and missed detections. Dynamic thresholding and event weighting help systems adjust based on risk levels, reducing unnecessary escalation of low-impact activities.
Environmental awareness and continuous calibration further improve detection outcomes over time. Systems that adapt to infrastructure changes and evolving usage patterns maintain higher consistency in alert relevance and operational efficiency.
AI, SIEM, and XDR improve detection accuracy by enhancing visibility, analysis depth, and response coordination across security environments.
Technology
Core Function
How It Improves Accuracy
Key Advantage
AI (Artificial Intelligence)
Processes large-scale security data and identifies complex patterns
Enhances decision-making by detecting subtle anomalies and evolving attack behaviors
Improves detection speed and reduces manual analysis
SIEM (Security Information and Event Management)
Aggregates and analyzes logs from multiple systems in one place
Provides centralized visibility and event correlation for better threat validation
Helps identify patterns that isolated systems may miss
XDR (Extended Detection and Response)
Integrates data across endpoints, networks, and cloud environments
Connects multi-layer signals to reduce fragmented alerts and improve context
Enables unified threat detection and faster response actions
Real-time threat detection systems involve balancing multiple performance factors that directly impact accuracy, speed, and operational efficiency.
Faster detection enables immediate response to potential threats across active environments. Deeper analysis improves validation accuracy but introduces delays in processing.
Detailed inspection of events improves threat validation and reduces misclassification. Increased depth can slow down response time in high-volume environments.
Higher sensitivity increases the likelihood of identifying suspicious activity across systems. Excessive sensitivity also raises alert volume and creates noise.
High alert noise makes it difficult to identify meaningful threats within large datasets. Reduced noise improves focus but may hide subtle threat signals.
Automated systems process large-scale data quickly and consistently. Heavy reliance on automation may overlook nuanced or context-driven threats.
Human analysis adds context-aware judgment and validation to detection outcomes. Manual review improves decision quality by identifying nuances that automated systems may overlook.
Scalable systems handle large volumes of data across distributed environments. Increased scale can reduce detection precision if logic becomes generalized.
آليات الكشف المتقدمة تتطلب الطاقة الحاسوبية وموارد البنية التحتية. يمكن أن تقيد الموارد المحدودة أداء النظام وقدرة الكشف.
يتطلب اختيار النظام الأساسي المناسب للكشف عن التهديدات تقييم مدى توازنه بين الدقة والكفاءة وقابلية الاستخدام التشغيلي في بيئات العالم الحقيقي.
يجب أن تولد المنصات تنبيهات عالية الثقة دون إرباك الفرق بالضوضاء. تضمن الدقة المتسقة إمكانية اعتماد فرق الأمان على نتائج الاكتشاف.
تعد المراقبة المستمرة عبر نقاط النهاية والشبكات والبيئات السحابية ضرورية للاكتشاف الفعال. تتيح الرؤية القوية التعرف على الأنشطة المشبوهة والاستجابة لها بشكل أسرع.
يجب أن تقوم الأنظمة بتقييم الأحداث ذات السياق البيئي والسلوكي الكامل. يعمل السياق الأفضل على تحسين ملاءمة التنبيه وتقليل التصعيد غير الضروري.
يعمل التكامل السلس مع أدوات الأمان الحالية على تحسين تدفق البيانات والكفاءة التشغيلية. توفر الأنظمة المتصلة رؤية أكثر اكتمالاً للتهديدات المحتملة.
يجب أن تتعامل المنصات مع أحجام البيانات المتزايدة دون تدهور الأداء. تحافظ الأنظمة القابلة للتطوير على الاتساق حتى في البيئات المعقدة.
تعمل التصفية الآلية والفرز والاستجابة على تقليل عبء العمل اليدوي لفرق الأمان. تعمل الأتمتة الفعالة على تحسين سرعة الاستجابة مع الحفاظ على التحكم.
تعمل المنصات مثل CloudSek على تحسين دقة اكتشاف التهديدات من خلال توسيع المراقبة خارج الأنظمة الداخلية إلى الويب السطحي والعميق والمظلم. يتيح التتبع المستمر لمنتديات القراصنة والبيانات المسربة والأصول المكشوفة التعرف المبكر على المخاطر التي غالبًا ما تفوتها طرق الكشف التقليدية.
يساعد التحليل السياقي القائم على الذكاء الاصطناعي في تحديد أولويات التهديدات من خلال تعيين الإشارات لأصول تجارية محددة وتعيين درجات المخاطر بناءً على التأثير الحقيقي. تعمل نماذج التعلم الآلي على تصفية تدفقات البيانات الضخمة إلى رؤى قابلة للتنفيذ، مما يقلل الضوضاء ويسمح للمحللين بالتركيز على التنبيهات عالية الثقة.
يعمل الذكاء الاستباقي للتهديدات وتكامل النظام البيئي على تعزيز فعالية الكشف عبر البيئات. تتيح المراقبة التنبؤية وحماية المخاطر الرقمية والتكامل السلس مع أنظمة SIEM و SOAR استجابة أسرع مع تقليل الإيجابيات الكاذبة.
تحدث النتيجة الإيجابية الكاذبة عندما يقوم نظام الأمان بوضع علامة على نشاط عادي أو غير ضار كتهديد. يمكن للتنبيهات الخاطئة المتكررة أن تقلل الكفاءة وتجعل من الصعب على الفرق تحديد المخاطر الحقيقية.
غالبًا ما تنتج الإيجابيات الكاذبة عن السياق المحدود أو البيانات الصاخبة أو قواعد الكشف شديدة الحساسية. تزيد أحجام التنبيه العالية والبيانات غير المرتبطة من فرص التصنيف الخاطئ.
يمكن تقليل الإيجابيات الكاذبة من خلال التحليل السياقي وربط البيانات ونماذج التعلم التكيفي. تساعد التغذية الراجعة المستمرة والضبط الأنظمة على تحسين الدقة بمرور الوقت.
يساعد الذكاء الاصطناعي في تحليل كميات كبيرة من البيانات وتحديد الأنماط التي قد تفوتها الطرق التقليدية. يعمل على تحسين دقة الكشف عن طريق تصفية الضوضاء والتكيف مع التهديدات المتطورة.
تركز دقة الكشف على تحديد التهديدات الحقيقية مع الحد الأدنى من التنبيهات الخاطئة. تشير سرعة الاكتشاف إلى مدى سرعة النظام في التعرف على النشاط المشبوه والاستجابة له.
