🚀 أصبحت CloudSek أول شركة للأمن السيبراني من أصل هندي تتلقى استثمارات منها ولاية أمريكية صندوق
اقرأ المزيد
Spear phishing هو هجوم إلكتروني مستهدف يقوم فيه أحد عناصر التهديد بانتحال شخصية فرد أو منظمة موثوق بها للتلاعب بضحية معينة للكشف عن معلومات حساسة أو منح حق الوصول إلى النظام. على عكس حملات التصيد الاحتيالي الواسعة، يعتمد التصيد الاحتيالي على التخصيص والدقة السياقية والاستهداف المتعمد.
يجمع المهاجمون معلومات استخبارية من ملفات تعريف الوسائط الاجتماعية ومواقع الشركات وقواعد البيانات المسربة والاتصالات السابقة لصياغة رسائل قابلة للتصديق. تزيد تقنيات انتحال البريد الإلكتروني وانتحال شخصية المسؤولين التنفيذيين وجمع بيانات الاعتماد من احتمالية تجاوز كل من الشكوك البشرية والفلاتر التقنية.
تؤدي محاولات التصيد الاحتيالي الناجحة في كثير من الأحيان إلى الاحتيال المالي واختراق الحساب السحابي ونشر برامج الفدية. الدقة والبحث والتلاعب النفسي تجعل التصيد الاحتيالي أحد أكثر تهديدات الهندسة الاجتماعية فعالية التي تواجه المؤسسات اليوم.
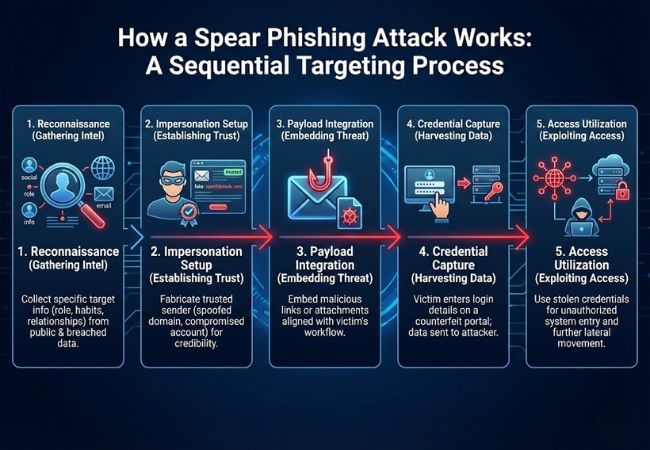
يعمل Spear phishing من خلال عملية استهداف متسلسلة تحول الاتصالات المخصصة إلى وصول غير مصرح به.
يتخذ Spear phishing أشكالًا متعددة اعتمادًا على الملف الشخصي المستهدف وقناة الاتصال وهدف الاحتيال.

يركز التصيد الاحتيالي القائم على البريد الإلكتروني على موظف معين باستخدام اتصالات تجارية مخصصة. غالبًا ما تشير الرسائل إلى مشاريع حقيقية أو أقسام داخلية أو موردين موثوقين للمطالبة بتقديم بيانات الاعتماد أو الوصول إلى المستندات.
يستهدف صيد الحيتان القيادة العليا مثل الرؤساء التنفيذيين والمديرين التنفيذيين الماليين. تركز الاتصالات عادةً على المسائل القانونية السرية أو عمليات الاندماج أو الموافقات عالية القيمة لاستغلال السلطة التنفيذية.
تتلاعب تسوية البريد الإلكتروني للأعمال بالفرق المالية من خلال انتحال شخصية المديرين التنفيذيين أو الموردين. تتضمن الطلبات عادةً تحويلات برقية عاجلة أو تغييرات في الفواتير أو تعليمات إعادة توجيه الدفع.
يكرر التصيد الاحتيالي المستنسخ بريدًا إلكترونيًا شرعيًا استلمته الضحية سابقًا. يتم استبدال الروابط أو المرفقات الأصلية بإصدارات ضارة مع الحفاظ على التنسيق والسياق.
يوفر Smishing محاولات تصيد شخصية من خلال الرسائل النصية. تشجع المطالبات العاجلة القصيرة الضحايا على التحقق من الحسابات أو إعادة تعيين بيانات الاعتماد عبر الروابط الاحتيالية.
تُستخدم منصات الشبكات الاحترافية مثل LinkedIn لبدء محادثات قائمة على الثقة. يقوم المهاجمون لاحقًا بنقل الاتصال نحو صفحات تسجيل الدخول الضارة أو بوابات مشاركة المستندات.
لا تزال تسوية البريد الإلكتروني للأعمال واحدة من أكثر أنماط التصيد الاحتيالي توثيقًا. في هذه الحالات، يتلقى موظف الشؤون المالية بريدًا إلكترونيًا مستهدفًا ينتحل شخصية أحد كبار المسؤولين التنفيذيين ويتم الضغط عليه للموافقة على تحويل إلكتروني عاجل، حيث أبلغ مكتب التحقيقات الفيدرالي عن مليارات الدولارات من الخسائر العالمية التراكمية المرتبطة بمخططات BEC.
كما زاد انتحال شخصية المسؤولين الحكوميين من خلال الرسائل النصية والمكالمات الصوتية الناتجة عن الذكاء الاصطناعي. تصف تحذيرات مكتب التحقيقات الفيدرالي (FBI) الحملات النشطة منذ عام 2023 حيث يقوم المهاجمون ببناء المصداقية من خلال الرسائل النصية، ثم نقل الضحايا إلى منصات مشفرة حيث تصبح سرقة بيانات الاعتماد أو الطلبات المالية أسهل في التنفيذ.
يعكس الاحتيال في الفواتير الذي يستهدف الجامعات والمؤسسات العامة تكتيكًا دقيقًا آخر. تسلط التقارير الموثقة الضوء على حالة قامت فيها إحدى الجامعات الأمريكية بتحويل 1.9 مليون دولار بعد الرد على بريد إلكتروني مخصص للمورد، مما يوضح كيف يمكن التلاعب بتدفقات العمل المالية الروتينية بشكل مقنع.
لا يزال Spear Phishing أحد أكثر طرق الهجمات الإلكترونية فعالية نظرًا لدقته وقدرته على التكيف واعتماده على الثقة البشرية بدلاً من العيوب التقنية.
يستغل التصيد الاحتيالي السلطة والإلحاح والألفة لتجاوز الحكم العقلاني. تعمل اللغة المختارة بعناية والملاءمة السياقية على تقليل الشكوك وتسريع عملية صنع القرار.
غالبًا ما يؤدي الاحتيال المستهدف عبر البريد الإلكتروني إلى تحويلات بنكية غير مصرح بها وخطط إعادة توجيه الفواتير. تُعد الخسائر المرتبطة بانتحال شخصية المسؤولين التنفيذيين والاحتيال في الدفع من بين أغلى فئات الجرائم الإلكترونية التي أبلغ عنها مكتب التحقيقات الفيدرالي.
تعتمد المنصات السحابية وحسابات البريد الإلكتروني والأنظمة الداخلية بشكل كبير على بيانات اعتماد تسجيل الدخول باعتبارها بوابة الأمان الأساسية. تسمح تفاصيل المصادقة المسروقة للمهاجمين بتجاوز دفاعات المحيط دون إطلاق إنذارات فورية.
غالبًا ما يؤدي الوصول الأولي المكتسب من خلال التصيد الاحتيالي السريع إلى اختراق الشبكة على نطاق أوسع. تحدد إرشادات الأمان الصادرة عن وكالة الأمن السيبراني وأمن البنية التحتية رسائل البريد الإلكتروني المخادعة المستهدفة كآلية تسليم رائدة لهجمات برامج الفدية.
تعمل أدوات التشغيل الآلي والذكاء الاصطناعي الآن على تحسين تخصيص الرسائل ودقة انتحال الشخصية. تسمح التكتيكات التكيفية للمهاجمين بتحسين الحملات بسرعة استنادًا إلى أنماط الاستجابة وضوابط الأمان.
يتطلب الاكتشاف الانتباه إلى التناقضات الدقيقة بدلاً من علامات التحذير الواضحة.
غالبًا ما تشير الاختلافات الطفيفة في النطاق أو عناوين الرد غير المعتادة أو النطاقات المسجلة حديثًا إلى انتحال الشخصية. قد تتطابق أسماء العرض مع جهة اتصال موثوقة بينما يختلف عنوان البريد الإلكتروني الأساسي قليلاً.
يجب أن تثير الطلبات التي تحيد عن سير العمل العادي الشكوك. غالبًا ما يشير الإلحاح غير المعتاد أو تعليمات الدفع غير المتوقعة أو مطالبات التحقق من تسجيل الدخول خارج الدورات الروتينية إلى التلاعب.
يمكن لبروتوكولات مصادقة البريد الإلكتروني مثل DMARC الكشف عن نطاقات المرسل المخادعة. غالبًا ما تصاحب عمليات التحقق من المصادقة الفاشلة أو غير المتوافقة الرسائل الاحتيالية.
قد تكتشف أنظمة مراقبة الأمان عمليات تسجيل الدخول من مواقع أو أجهزة غير مألوفة بعد تقديم بيانات الاعتماد. يمكن أن تشير محاولات تسجيل الدخول الفاشلة المتعددة أو الحالات الشاذة في الجلسة إلى وجود حل وسط قيد التقدم.
قد يؤدي تمرير مؤشر الماوس فوق الارتباطات التشعبية إلى إظهار عناوين URL غير متطابقة أو نطاقات غير مألوفة. يجب التعامل مع المرفقات التي تطلب تمكين الماكرو أو إعادة إدخال بيانات الاعتماد على أنها تفاعلات عالية المخاطر.
يتطلب منع التصيد الاحتيالي ضوابط متعددة الطبقات تعالج السلوك البشري ونقاط الضعف التقنية.
يجب أن يفهم الموظفون كيف تختلف محاولات التصيد المخصصة عن عمليات الاحتيال العامة. تعزز عمليات المحاكاة المنتظمة والتمارين القائمة على السيناريوهات التعرف على أساليب انتحال الشخصية والطلبات الاحتيالية.
تضيف المصادقة متعددة العوامل طبقة تحقق إضافية تتجاوز كلمات المرور. تصبح بيانات الاعتماد المخترقة وحدها غير كافية للوصول إلى الحساب.
تعمل معايير مثل DMARC وSPF وDKIM على التحقق من شرعية المرسل وتقليل انتحال النطاق. يقلل التكوين الصحيح بشكل كبير من محاولات انتحال الشخصية الناجحة.
تقوم بوابات أمان البريد الإلكتروني الحديثة بتحليل الأنماط السلوكية وسمعة الارتباط وشذوذ الرسائل. تكتشف نماذج التعلم الآلي أساليب التخصيص الدقيقة التي قد تفوتها عوامل تصفية البريد العشوائي التقليدية.
تراقب أدوات اكتشاف نقطة النهاية والاستجابة تنفيذ الملفات المشبوهة وسلوك النظام غير الطبيعي. يمنع الاحتواء المبكر المهاجمين من توسيع الوصول بعد التسوية الأولية.
يفرض Zero Trust Security التحقق المستمر من المستخدمين والأجهزة عبر الشبكة. تحد الحركة الجانبية المقيدة من التلف حتى في حالة كشف أوراق الاعتماد.
يتطلب تحديد الحل الصحيح لمكافحة التصيد الاحتيالي أكثر من إمكانات تصفية البريد العشوائي الأساسية.
يجب أن تقوم أنظمة الحماية بتحليل سلوك الرسالة وسمعة المرسل وأنماط الشذوذ في وقت التسليم. يعمل المسح الفوري على تقليل الفترة بين التسليم وتفاعل المستخدم.
يجب أن تكتشف نماذج التعلم الآلي التلاعب السياقي ومحاولات انتحال الشخصية. يساعد التحليل المتقدم في تحديد حملات التصيد الاحتيالي ذات الطابع الشخصي للغاية والتي تتجاوز القواعد الثابتة.
يجب أن تتكامل الحلول مع معايير المصادقة مثل DMARC لفرض التحقق من صحة المجال. تعمل المحاذاة مع سياسات SPF و DKIM على تعزيز ضوابط التحقق من المرسل.
يضيف التوافق السلس مع أنظمة إدارة الهوية ومنصات المصادقة متعددة العوامل المرونة ضد اختراق بيانات الاعتماد. تعمل التنبيهات الآلية لسلوك تسجيل الدخول غير الطبيعي على تحسين سرعة الاستجابة.
تعمل عناصر التحكم المضمنة في العزل وميزات المعالجة الآلية على الحد من التعرض بعد الاكتشاف. تسمح لوحات المعلومات المركزية لفرق الأمان بتتبع أنماط الهجوم وحالة الاحتواء.
تعمل أزرار إعداد التقارير سهلة الاستخدام على تشجيع الموظفين على الإبلاغ عن الرسائل المشبوهة. تعمل التقارير الداخلية السريعة على تحسين معدلات الكشف وتقوية الوعي التنظيمي.
يستهدف Spear phishing فردًا أو مؤسسة معينة باستخدام معلومات مخصصة، بينما يوزع التصيد الاحتيالي العادي رسائل عامة على مجموعات كبيرة. يزيد التخصيص بشكل كبير من المصداقية ومعدلات المشاركة.
يقوم المهاجمون بجمع البيانات من ملفات تعريف الوسائط الاجتماعية ومواقع الشركات والملفات العامة وقواعد البيانات المسربة سابقًا. يسمح الاستطلاع للرسائل بالإشارة إلى الأسماء الحقيقية والأدوار الوظيفية وأنشطة الأعمال.
يمكن للرسائل المخصصة للغاية المرسلة من حسابات مخترقة أو مخادعة أن تتجنب عوامل تصفية البريد العشوائي الأساسية. تعتمد أنظمة الكشف المتقدمة على التحليل السلوكي بدلاً من مطابقة الكلمات الرئيسية وحدها.
تواجه قطاعات التمويل والرعاية الصحية والحكومة والتكنولوجيا استهدافًا متكررًا بسبب الوصول إلى البيانات الحساسة والمعاملات عالية القيمة. تظل الفرق التنفيذية والإدارات المالية أهدافًا أساسية عبر الصناعات.
تقلل المصادقة متعددة العوامل بشكل كبير من مخاطر الاستحواذ على الحساب من خلال طلب تحقق إضافي. لا تزال عناصر التحكم ذات الطبقات مثل مصادقة البريد الإلكتروني ومراقبة نقطة النهاية ضرورية للحماية الكاملة.
يستمر التصيد الاحتيالي بالرمح في النجاح لأنه يستغل الثقة والسلطة والمعرفة السياقية بدلاً من عيوب النظام الفني. الاستهداف الدقيق وجمع بيانات الاعتماد وتكتيكات انتحال الشخصية تجعلها تهديدًا مستمرًا في جميع الصناعات.
يعتمد الدفاع المستدام على الوعي وضوابط المصادقة القوية والمراقبة المستمرة. المنظمات التي تجمع بين اليقظة البشرية والبنية الأمنية متعددة الطبقات تقلل بشكل كبير من مخاطر الاختراق المستهدف.
