🚀 أصبحت CloudSek أول شركة للأمن السيبراني من أصل هندي تتلقى استثمارات منها ولاية أمريكية صندوق
اقرأ المزيد
تهديد الهوية هو خطر الأمن السيبراني الذي يستهدف الهويات الرقمية للحصول على وصول غير مصرح به إلى الأنظمة أو البيانات. إنه يركز على استغلال عمليات تسجيل الدخول وأذونات الوصول بدلاً من مهاجمة البنية التحتية مباشرة.
يقوم المهاجمون بإساءة استخدام الحسابات المخترقة أو بيانات الاعتماد المسروقة أو الجلسات المتلاعب بها للظهور كمستخدمين شرعيين. بمجرد منح الوصول، غالبًا ما تمتزج الأنشطة مع السلوك الطبيعي ويصبح من الصعب اكتشافها.
تزيد البيئات الحديثة من التعرض لأن الهوية تتحكم الآن في الدخول إلى منصات السحابة والتطبيقات والموارد الداخلية. غالبًا ما تعني السيطرة على الهوية السيطرة على أصول المؤسسة الأكثر أهمية.
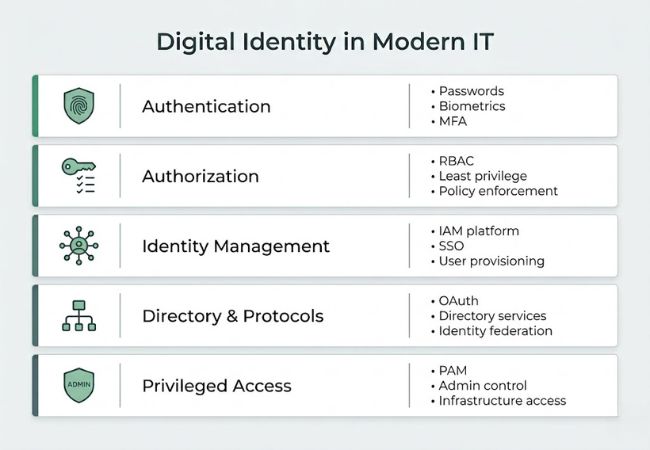
تحدد أنظمة الهوية الرقمية من يمكنه الوصول إلى ما داخل المؤسسة. وهي تعتمد على المصادقة للتحقق من الهوية والترخيص لتحديد الأذونات.
تؤكد المصادقة هوية المستخدم باستخدام كلمات المرور أو القياسات الحيوية أو المصادقة متعددة العوامل (MFA). تقلل المصادقة القوية من الوصول غير المصرح به ولكنها لا تقضي على إساءة استخدام الهوية تمامًا.
يحدد التخويل ما يمكن للمستخدمين المصادق الوصول إليه استنادًا إلى السياسات المحددة مسبقًا. يساعد التحكم في الوصول المستند إلى الأدوار (RBAC) ومبادئ أقل الامتيازات على تقليل التعرض.
تعمل منصات إدارة الهوية والوصول (IAM) على تركيز توفير المستخدم وسياسات الوصول وتسجيل الدخول الأحادي (SSO). تقوم تقنيات مثل OAuth وخدمات الدليل مثل Active Directory بإدارة علاقات الهوية عبر الأنظمة.
تعمل إدارة الوصول المميز (PAM) على تأمين الحسابات الإدارية والأذونات المرتفعة. نظرًا لأن الهويات المميزة تتحكم في البنية التحتية الحيوية، فهي أهداف عالية القيمة للمهاجمين.
تحدد الهوية الوصول عبر أنظمة تكنولوجيا المعلومات الحديثة حيث لم يعد موقع الشبكة يحدد الثقة.
تستغل الهجمات القائمة على الهوية أنظمة المصادقة وأذونات الوصول وعلاقات الثقة بالهوية للحصول على تحكم غير مصرح به.
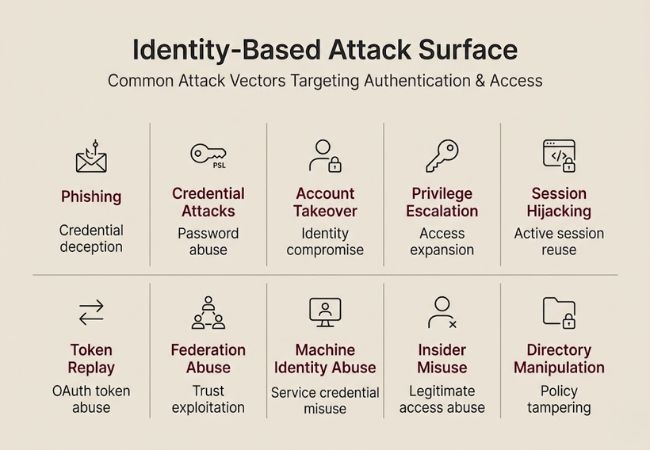
تتلاعب هجمات التصيد الاحتيالي بالمستخدمين للكشف عن بيانات اعتماد المصادقة من خلال رسائل البريد الإلكتروني الخادعة أو بوابات تسجيل الدخول المزيفة أو الاتصالات المنتحلة. تسمح أسماء المستخدمين وكلمات المرور المسروقة للمهاجمين بتجاوز عناصر التحكم في الوصول دون استغلال عيوب البرامج.
يعمل Spear phishing على زيادة الدقة من خلال استهداف موظفين محددين برسائل تدرك السياق. غالبًا ما يؤدي التصيد الاحتيالي الناجح إلى اختراق الحساب داخل أنظمة هوية المؤسسة.
تعتمد هجمات بيانات الاعتماد على كلمات المرور المسروقة أو المعاد استخدامها التي تم الحصول عليها من خروقات البيانات أو الإصابات بالبرامج الضارة. تحاول تقنيات مثل حشو بيانات الاعتماد ورش كلمة المرور محاولات تسجيل دخول واسعة النطاق ضد بوابات المصادقة.
يؤدي ضعف نظافة كلمة المرور ونقص المصادقة متعددة العوامل إلى زيادة التعرض. بمجرد تحديد بيانات اعتماد صالحة، يحصل المهاجمون على وصول شرعي إلى التطبيقات والخدمات السحابية.
تحدث هجمات الحساب عندما يتحكم الخصوم في هويات المستخدم الصالحة داخل النظام. يتيح الاستيلاء على الحساب الوصول غير المصرح به إلى البريد الإلكتروني ومنصات SaaS والتطبيقات الداخلية.
تساعد أساليب التعب من MFA وانتحال الهوية في تجاوز آليات التحقق الثانوية. غالبًا ما يبدو النشاط ضمن حساب مخترق مشروعًا في سجلات التدقيق.
تركز هجمات الامتيازات على توسيع حقوق الوصول بعد الإدخال الأولي. يتيح تصعيد الامتيازات للمهاجمين الانتقال من أدوار المستخدم القياسية إلى التحكم الإداري.
تؤدي تعيينات الأدوار التي تم تكوينها بشكل خاطئ والأذونات المفرطة إلى زيادة احتمالية إساءة الاستخدام. توفر الامتيازات المرتفعة الوصول إلى إعدادات التكوين وقواعد البيانات الحساسة وعناصر التحكم في الأمان.
تستغل هجمات الجلسة جلسات المصادقة النشطة بدلاً من بيانات الاعتماد نفسها. تسمح سرقة الجلسة وسرقة ملفات تعريف الارتباط للمهاجمين بإعادة استخدام معرفات الجلسة الصالحة.
تحافظ الجلسات المخترقة على الوصول دون تشغيل عمليات إعادة تعيين كلمة المرور. تتجاوز هذه الطريقة خطوات التحقق من تسجيل الدخول التقليدية.
تستهدف هجمات الرموز رموز المصادقة التي تم إصدارها أثناء عمليات تسجيل الدخول الحديثة. يمكن إعادة تشغيل رموز OAuth ورموز التحديث للحفاظ على الوصول غير المصرح به إلى API.
يؤدي التخزين غير الصحيح للرموز أو التحقق منها إلى زيادة مخاطر التعرض. غالبًا ما توفر الرموز المسروقة وصولاً مباشرًا إلى الخدمات المتصلة دون تحقق إضافي.
تستغل هجمات الاتحاد علاقات الثقة بين مزودي الهوية ومقدمي الخدمة. تتيح تأكيدات SAML التي تم التلاعب بها أو تكوينات الاتحاد المخترقة الوصول عبر الأنظمة الأساسية.
تعمل أنظمة الهوية الموحدة على توسيع المصادقة خارج نطاق واحد. يؤدي التحقق الضعيف داخل سلاسل الثقة هذه إلى توسيع سطح الهجوم.
تستهدف الهجمات الآلية هويات غير بشرية مثل حسابات الخدمة وبيانات اعتماد التطبيق. غالبًا ما تحمل مفاتيح API والشهادات وهويات عبء العمل امتيازات وصول دائمة.
غالبًا ما تفتقر هويات الأجهزة إلى المراقبة المطبقة على المستخدمين البشريين. يمكن لحسابات الخدمة المخترقة أتمتة الإجراءات غير المصرح بها على نطاق واسع.
تتضمن الهجمات الداخلية المستخدمين المصرح لهم الذين يسيئون استخدام امتيازات الوصول المشروعة. قد تقوم البرامج الداخلية الضارة باستخراج البيانات الحساسة أو تعديل تكوينات النظام.
يمثل الاكتشاف تحديًا لأن الإجراءات تنشأ من حسابات صالحة. تزيد الأذونات المفرطة من التأثير المحتمل للإساءة الداخلية.
تتلاعب هجمات الدليل بمخازن الهوية المركزية وهياكل الوصول. يمكن أن تؤدي التغييرات في كائنات الدليل أو سياسات المجموعة إلى تغيير الأذونات عبر البيئة.
تؤثر خدمات الدليل المخترقة على المصادقة عبر الأنظمة المتصلة. يمكن أن يؤدي التحكم في البنية التحتية للهوية إلى تعطيل عمليات المؤسسة بأكملها.
تمر الهجمات القائمة على الهوية بمراحل متميزة تعمل على توسيع الوصول والتحكم بمرور الوقت.
يقوم المهاجمون بتحديد حسابات المستخدمين الصالحة ونقاط نهاية المصادقة المكشوفة وخدمات الهوية التي يمكن الوصول إليها. غالبًا ما توفر بيانات الاعتماد المسربة وبوابات تسجيل الدخول العامة بيانات الاستهداف الأولية.
يتم استخدام كلمات المرور المسروقة أو نتائج التصيد الاحتيالي أو الرموز المخترقة للمصادقة بنجاح. يسمح الحصول على وصول صالح للمهاجمين بالعمل تحت هوية موثوقة.
تعمل الأدوار التي تم تكوينها بشكل خاطئ والأذونات المفرطة على تمكين التصعيد بما يتجاوز الوصول الأولي. تزيد الامتيازات المرتفعة من التحكم في الوظائف الإدارية والموارد الحساسة.
يتم الاستفادة من الحسابات المخترقة للوصول إلى الأنظمة المتصلة من خلال علاقات الثقة. يمكن لنماذج تسجيل الدخول الأحادي والهوية الموحدة توسيع نطاق الوصول عبر تطبيقات متعددة.
يقوم المهاجمون بتنفيذ أهداف مثل سرقة البيانات أو الاحتيال المالي أو نشر برامج الفدية. يحدث التأثير عادةً بعد أن تظل إساءة استخدام الهوية غير مكتشفة عبر الأنظمة.
غالبًا ما يتم الخلط بين تهديدات الهوية وسرقة الهوية، ولكنها تختلف اختلافًا كبيرًا في النطاق والهدف والتأثير.
تخلق تهديدات الهوية عواقب تشغيلية ومالية وتنظيمية تتجاوز الأنظمة التقنية.
يتطلب منع الهجمات القائمة على الهوية عناصر تحكم متعددة الطبقات تعمل على تأمين المصادقة وأذونات الوصول ومراقبة الهوية.
تقلل المصادقة متعددة العوامل من الاعتماد على كلمات المرور وحدها وتحظر العديد من المحاولات القائمة على بيانات الاعتماد. يعزز التحقق التكيفي الحماية من خلال تقييم الجهاز والموقع والسلوك.
يجب أن تقتصر حقوق الوصول على ما يطلبه المستخدمون والخدمات فقط لأداء أدوار محددة. تمنع مراجعات الوصول المنتظمة انحراف الأذونات وتقلل من التعرض المفرط للامتيازات.
تقوم إدارة الوصول المميز بتقييد الحسابات الإدارية ومراقبة الجلسات المرتفعة. يقلل الوصول المحدد زمنياً من المخاطر طويلة الأجل من الأذونات عالية المستوى.
يقلل التخزين الآمن والتحقق الصارم من رموز OAuth ومعرفات الجلسة من مخاطر إعادة التشغيل وسوء الاستخدام. سياسات انتهاء صلاحية الرمز تحد من الوصول المستمر غير المصرح به.
يجب جرد حسابات الخدمة ومفاتيح API والشهادات ومراقبتها باستمرار. يقلل التدوير الآلي والأذونات المحددة النطاق من إساءة استخدام هوية الجهاز.
تحدد التحليلات السلوكية أنماط تسجيل الدخول غير العادية والوصول إلى الحالات الشاذة في الوقت الفعلي. يتيح اكتشاف تهديدات الهوية والاستجابة لها الاحتواء السريع للهويات المخترقة.
يجب أن يوفر الحل الفعال للحماية من تهديدات الهوية الرؤية والكشف والاستجابة عبر النظام البيئي للهوية بأكمله.
يجب أن توفر المنصة رؤية مركزية عبر المستخدمين والحسابات المميزة وحسابات الخدمة والهويات الموحدة. تعمل المراقبة الموحدة على تقليل النقاط العمياء عبر البيئات السحابية والبيئات المحلية.
يجب أن تكتشف التحليلات المتقدمة سلوك تسجيل الدخول غير الطبيعي وإساءة استخدام الامتيازات والعيوب الرمزية. يعمل تصنيف المخاطر المستند إلى السياق على تحسين الكشف المبكر عن التهديدات.
يجب أن يتتبع الحل باستمرار النشاط الإداري والوصول إلى التغييرات. تعمل التنبيهات في الوقت الفعلي على تقليل وقت الاستجابة لإساءة استخدام الامتيازات.
يجب مراقبة أنماط استخدام الرمز المميز لمحاولات إعادة التشغيل واستدعاءات API غير العادية. التحقق القوي يمنع إساءة استخدام الرمز المميز على المدى الطويل.
تتطلب الهويات غير البشرية مثل واجهات برمجة التطبيقات وحسابات عبء العمل الإشراف المستمر. يعمل التدوير الآلي للمفاتيح وتتبع الشهادات على تعزيز الحماية.
يجب أن تسمح عمليات سير عمل الاستجابة المتكاملة بالتعليق السريع للحساب وإنهاء الجلسة. يحد الاحتواء الآلي من تأثير اختراق الهوية.
لقد حولت تهديدات الهوية الأمن السيبراني من حماية حدود الشبكة إلى حماية أنظمة المصادقة وآليات التحكم في الوصول. توفر بيانات الاعتماد والرموز والامتيازات المخترقة الآن للمهاجمين مسارات مباشرة إلى البنية التحتية الحيوية.
تُبلغ Microsoft عن أكثر من 600 مليون هجوم على الهوية يوميًا، وتستهدف أكثر من 99 بالمائة كلمات مرور المستخدمين، مما يوضح حجم التهديدات التي تركز على بيانات الاعتماد. تهيمن تهديدات الهوية الآن على مخاطر الأمن السيبراني، مما يجعل المعرفة الواضحة بتعريفها وفئات الهجوم والتقدم أمرًا بالغ الأهمية لحماية أنظمة المصادقة والترخيص.
تعمل الحوكمة القوية للهوية والمراقبة المستمرة وإنفاذ أقل الامتيازات على تقليل مخاطر الوصول غير المصرح به. يعد تأمين الهويات البشرية والآلية على قدم المساواة أمرًا ضروريًا للحفاظ على التحكم في البيئات الحديثة القائمة على السحابة.
نعم، تتزايد الهجمات القائمة على الهوية حيث تعتمد المؤسسات بشكل أكبر على الخدمات السحابية والمصادقة عن بُعد. يعطي المهاجمون الأولوية لأنظمة الهوية لأن الوصول الصحيح لتسجيل الدخول غالبًا ما يتجاوز ضوابط الأمان التقليدية.
غالبًا ما تحتوي هويات الأجهزة على بيانات اعتماد ثابتة وأذونات واسعة. تزيد المراقبة المحدودة لحسابات الخدمة من مخاطر التسوية غير الملحوظة.
تقلل المصادقة متعددة العوامل بشكل كبير من الهجمات القائمة على كلمات المرور. ومع ذلك، تتطلب إساءة استخدام الرمز المميز واختطاف الجلسة وإساءة استخدام الامتيازات عناصر تحكم إضافية للمراقبة.
تواجه قطاعات التمويل والرعاية الصحية والحكومة والتكنولوجيا تعرضًا مرتفعًا بسبب البيانات الحساسة والبنى التحتية المعقدة للهوية. الأصول الرقمية عالية القيمة تجعل هذه الصناعات أهدافًا جذابة.
يتطلب Zero Trust التحقق المستمر من الهوية وسياق الوصول. يقلل هذا النموذج من الثقة الضمنية ويقلل من تأثير بيانات الاعتماد المخترقة.
