🚀 أصبحت CloudSek أول شركة للأمن السيبراني من أصل هندي تتلقى استثمارات منها ولاية أمريكية صندوق
اقرأ المزيد



.png)
يوجد IP6.arpa TLD لغرض واحد: عمليات البحث العكسية عن DNS. لم يتم تصميمه أبدًا لاستضافة مواقع الويب أو خدمة المحتوى أو الإشارة إلى عناوين IPv4. وهذا يجعلها غير مرئية لمعظم أدوات الأمان - وهذا هو بالضبط سبب بدء الجهات الفاعلة في التهديد في استخدامها.
في فبراير 2026، إنفوبلووكس قام المهاجمون بتوثيق الاستغلال المعروف لهذه النقطة العمياء حيث قاموا بوضع سجلات wildcard A داخل مناطق DNS العكسية ip6.arpa، ثم تضمين هذه المناطق كعناوين URL في رسائل البريد الإلكتروني المخادعة. نظرًا لأن ip6.arpa لا يحمل أي سمعة للنطاق، فإن بوابات البريد الإلكتروني وماسحات عناوين URL تمر بها دون فحص.
بعد إجراء مزيد من التحقيق، أجرينا مسحًا عالميًا لـ BGP مقابل 127906 بادئات IPv6 للتحقق من صحة النتائج وتوسيعها بواسطة Infoblox. لقد أكدنا أن الحملة الأصلية لا تزال نشطة ووجدنا حملة ثانية مستقلة تعمل على بنية تحتية مختلفة تمامًا: خادم في فرانكفورت، ألمانيا، تحت ASN مختلف، بدون وكيل Cloudflare.
أما المنطقة الثانية، وهي 0.d.7.2.7.0.1.b.e.0.a.2.ip6.arpa، فتحل إلى 85.215.34.119. كان نشطًا أثناء نافذة الفحص الخاصة بنا، وكان نشطًا منذ 29 يناير 2026 على الأقل، وفي وقت كتابة هذا التقرير لا يزال نشطًا مع وجود سجلات Cloudflare NS في مكانها.
إن فهم سبب استخدام الجهات الفاعلة في مجال التهديد لهذه التقنية يساعد على فهم ما يفترض أن يفعله ip6.arpa. عندما يتلقى خادم البريد بريدًا إلكترونيًا، فإنه غالبًا ما يقوم بإجراء بحث DNS عكسي على عنوان IP الخاص بالمرسل - الاستعلام عن مساحة اسم ip6.arpa للعثور على اسم المضيف المرتبط. تتعامل أدوات الأمان مع مساحة الاسم هذه على أنها أداة للبنية التحتية، وليس كمصدر لعناوين URL الضارة.
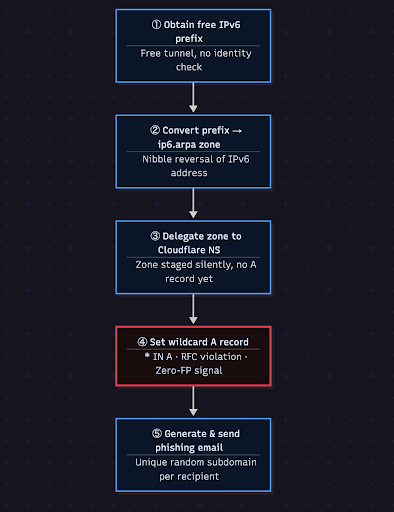
أولاً، يحصلون على بادئة IPv6 /48 مجانية من مزود النفق مثل Hurricane Electric. وهذا يمنحهم التحكم الإداري في منطقة DNS العكسية ip6.arpa المقابلة - وهي منطقة يجب، وفقًا لتصميم RFC، أن تحتوي فقط على سجلات PTR التي تعيد تعيين العناوين إلى أسماء المضيفين.
<malicious-ip>بدلاً من ذلك، قاموا بتعيين سجل البدل A: * IN A. الآن يتم تحويل كل نطاق فرعي محتمل ضمن تلك المنطقة إلى الخادم الخاص بهم. عنوان URL مثل xqjerorqxs.d.d.e.0.3.0.0.7.4.0.0.0.1.0.0.0.0.2.ip6.arpa هو DNS صالح تقنيًا، ويتم تحويله إلى عنوان IP حقيقي، وينظر إلى الماسحات الضوئية الآلية مثل استعلام PTR روتيني بدلاً من رابط التصيد الاحتيالي.
تتضمن كل رسالة بريد إلكتروني احتيالية بادئة نطاق فرعية مختلفة تم إنشاؤها عشوائيًا، ويحصل كل مستلم على عنوان URL فريد. ونظرًا لأن المنطقة تحتوي على سجل البدل A، يتم حلها جميعًا دون أن يقوم المهاجم بتسجيل أي شيء. قوائم الحظر المجمعة غير مجدية: فبحلول الوقت الذي يستخرج فيه المحلل نطاقًا فرعيًا واحدًا ويحظره، تحصل كل ضحية أخرى بالفعل على نطاق مختلف.
أي استجابة لسجل A من منطقة ip6.arpa تعد انتهاكًا لـ RFC. لا توجد حالة استخدام مشروعة. معدل إيجابي كاذب: 0%.

لمزيد من التحقيق، قمنا باختبار جدول توجيه IPv6 BGP العالمي. في المرحلة الأولى، سحبت جميع البادئات المحددة لـ //48 وأكثر من BGP.tools 127,906 في المجموع وحولت كل منها إلى منطقة ip6.arpa nibble المقابلة لها، وفحصت خوادم أسماء Cloudflare. إن Cloudflare NS في منطقة ip6.arpa هي إشارة الانطلاق: قام المهاجم بتفويض المنطقة، وهو جاهز لإضافة سجلات A عند إطلاق الحملة.
أعادت المرحلة الأولى 384 منطقة باستخدام Cloudflare NS. أطلقت المرحلة الثانية 100 مسبار للنطاق الفرعي تم إنشاؤها عشوائيًا في كل من هذه المناطق. أكدت استجابة السجل «البدل» أن المنطقة ضارة بشكل نشط.
من بين 127,906 منطقة تم اختبارها: 384 منطقة مشبوهة واثنتان من المناطق الخبيثة المؤكدة.
كانت الضربة الأولى هي المنطقة التي وثقتها Infoblox: d.d.e.0.6.3.0.0.7.4.0.1.0.0.2.ip6.arpa، المقابلة لبادئة إعصار إلكتريك IPv6 2001:470:63 d: :/48. وقد كان نشطًا أثناء الفحص، حيث قام 100 من أصل 100 مسبار للنطاق الفرعي بإرجاع سجلات A لعناوين IP الخاصة بـ Cloudflare edge 104.21.3.194 و 172.67.131.33.
كانت هذه المنطقة نشطة وخاملة بشكل متقطع عبر عمليات المسح المتعددة في 12 مارس 2026، وهو ما يتوافق مع التنشيط المستند إلى الحملة، حيث يقوم المهاجم بتشغيل البدل عند إرسال رسائل البريد الإلكتروني المخادعة وإيقافها بين الحملات، مما يجعل المراقبة السلبية غير موثوقة.
الضربة الثانية لم تكن في تقرير Infoblox. تتوافق المنطقة 0.d.7.2.7.0.1.b.e.0.a.2.ip6.arpa مع بادئة IPv6 2a0e:b 107:27 d0: :/48 ويتم حلها إلى 85.215.34.119 - عنوان IP واحد غير CloudFlare في فرانكفورت بألمانيا، ويتم استضافته على البنية التحتية لـ IONOS SE.
على عكس الحملة A، لا تستخدم هذه المنطقة Cloudflare كوكيل. يتم الكشف عن عنوان IP الخاص بالخادم الأصلي بشكل مباشر. مكدس الخادم حاليًا هو nginx + Plesk على خادم مُدار.
يؤكد التشابه الهيكلي بين الحملة A والحملة B بقوة إعادة استخدام التقنية. يستخدم كلاهما نفس سجلات البدل A التي تقبل بادئات النطاق الفرعي العشوائية، وكلاهما يستخدم Cloudflare NS لتفويض المنطقة، وكان كلاهما نشطًا في نفس اليوم.
تمثل كلتا المنطقتين الضارتين المؤكدتين 2 من أصل 384 اجتازت المرحلة الأولى من الفحص الذي أجريناه. تحتوي الـ 382 المتبقية على سجلات Cloudflare NS في مناطق ip6.arpa ولكن لا توجد سجلات A نشطة. يتم تنظيمها.
هذه هي النتيجة الأكثر أهمية من وجهة نظر دفاعية. لا يحتاج المهاجم إلى تسجيل نطاق أو تكوين خادم في اليوم الذي يطلق فيه الحملة. يمكنهم تنظيم أسابيع البنية التحتية
مسبقًا، قم بتفويض المنطقة، وقم بتوجيهها إلى Cloudflare، وانتظر. عندما يكونون مستعدين لإرسال رسائل البريد الإلكتروني المخادعة، فإنهم يضيفون حرف البدل A record. يتم نشر الحملة في غضون ثوانٍ. عند الانتهاء، يقومون بإزالته. عادت المنطقة إلى الهدوء مرة أخرى، لكنها لا تزال مسلحة.
إن مراقبة هذه المناطق البالغ عددها 382 لتنشيط السجل أمر قابل للتنفيذ بشكل مباشر. يمكن لأي منظمة تقوم بمراقبة DNS التنبيه على استجابات سجل A من أي منطقة *.ip6.arpa. أي من تلك المناطق الـ 382 التي يتم تنشيطها هي إشارة إيجابية زائفة صفرية لإطلاق الحملة.
Note: As of 2026-03-12, the wildcard A record on 0.d.7.2.7.0.1.b.e.0.a.2.ip6.arpa remains active and resolving to 85.215.34.119. The DNS infrastructure for Campaign B is fully operational. However, no phishing email, TDS redirect chain, or phishing landing page directly linked to this zone has been observed by our team. Active probes of 85.215.34.119 returned a Plesk default page. This does not rule out a TDS-gated or referrer-filtered landing page that would only activate via the correct attack chain. The malicious intent is confirmed by DNS, a wildcard A record on ip6.arpa has no legitimate use case under any RFC but downstream victim-facing infrastructure has not been directly observed.
إن تقنية إساءة استخدام ip6.arpa التي وثقتها Infoblox في فبراير 2026 ليست حملة معزولة. وجد المسح العالمي المستقل الخاص بنا أنه قيد الاستخدام بنشاط مع اقتراح حملات مستقلة.
المناطق المرحلية البالغ عددها 382 التي وجدناها هي الاكتشاف الأكثر أهمية من الناحية التشغيلية. إنها ليست قطعًا أثرية تاريخية ولكن يمكن التعامل معها على أنها أسلحة محملة. يمكن للمهاجم الذي قام بالفعل بعمل تفويض منطقة إلى Cloudflare NS إطلاق حملة بتغيير سجل DNS واحد، بشكل أسرع من أي قائمة حظر يمكن أن تستجيب لها.