🚀 أصبحت CloudSek أول شركة للأمن السيبراني من أصل هندي تتلقى استثمارات منها ولاية أمريكية صندوق
اقرأ المزيد




ال تنبيه أحمر تمثل حملة التجسس عبر الهاتف المحمول ناقلًا خطيرًا للتهديد يستغل بشكل مباشر الذعر المدني المتزايد المحيط بالصراع الحركي الحالي بين إسرائيل وإيران. تستفيد الجهات الفاعلة في مجال التهديد من الحاجة الماسة إلى تنبيهات الصواريخ في الوقت الفعلي من خلال توزيع نسخة أحصنة من تطبيق Home Front Command الرسمي من خلال التصيد الاحتيالي المستهدف عبر الرسائل القصيرة (smishing). تتجاوز آلية التسليم هذه عمدًا متجر Google Play - المستودع الشرعي الوحيد لتطبيق «Red Alert» الأصلي، والذي يعمل بشكل نظيف مع الوصول الأساسي فقط إلى الإشعارات. من خلال التلاعب بالضحايا لتحميل ملف APK الضار هذا تحت ستار تحديث عاجل في زمن الحرب، نجح الخصوم في نشر واجهة تنبيه تعمل بكامل طاقتها تخفي محرك مراقبة غازيًا مصممًا للاعتداء على السكان المتيقظين للغاية.
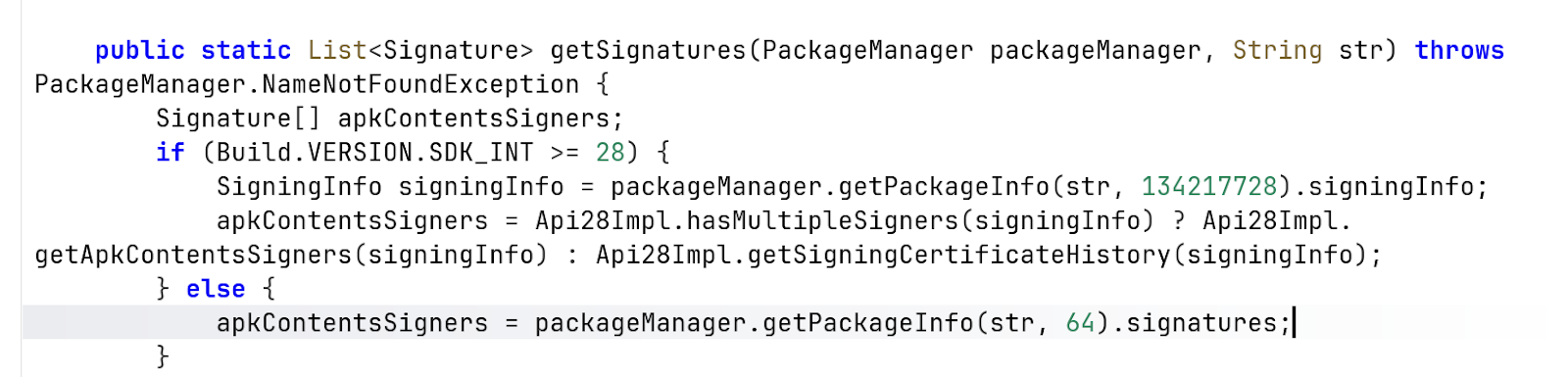
تحت المظهر الخارجي الشرعي، تنفذ البرامج الضارة عدوى معقدة متعددة المراحل، باستخدام خطافات بروكسي ديناميكية لتزوير شهادة توقيع التطبيق الأصلي لعام 2014 والتهرب من عمليات التحقق من سلامة نظام Android. تقوم الحمولة الأساسية، التي يتم التشويش عليها بشدة داخل الفصل، بإجراء استطلاعات قوية للحصول على أذونات النظام عالية المخاطر لاعتراض صناديق البريد الوارد الكاملة للرسائل القصيرة، وجمع دفاتر جهات الاتصال، وتتبع إحداثيات GPS الدقيقة باستمرار. يتم تنظيم هذه المعلومات الاستخبارية المجمعة بشكل منهجي وتسريبها إلى البنية التحتية التي يتحكم فيها المهاجم عبر حلقة تحميل سريعة. إن الجمع بين تتبع المواقع المدنية في الوقت الفعلي أثناء الغارات الجوية النشطة والقدرة على تجاوز 2FA من خلال اعتراض الرسائل القصيرة يحول هذه الحملة إلى مخاطر أمنية استراتيجية ومادية شديدة، مما يتطلب بروتوكولات الحجر الصحي الفورية والحظر على مستوى الشبكة.

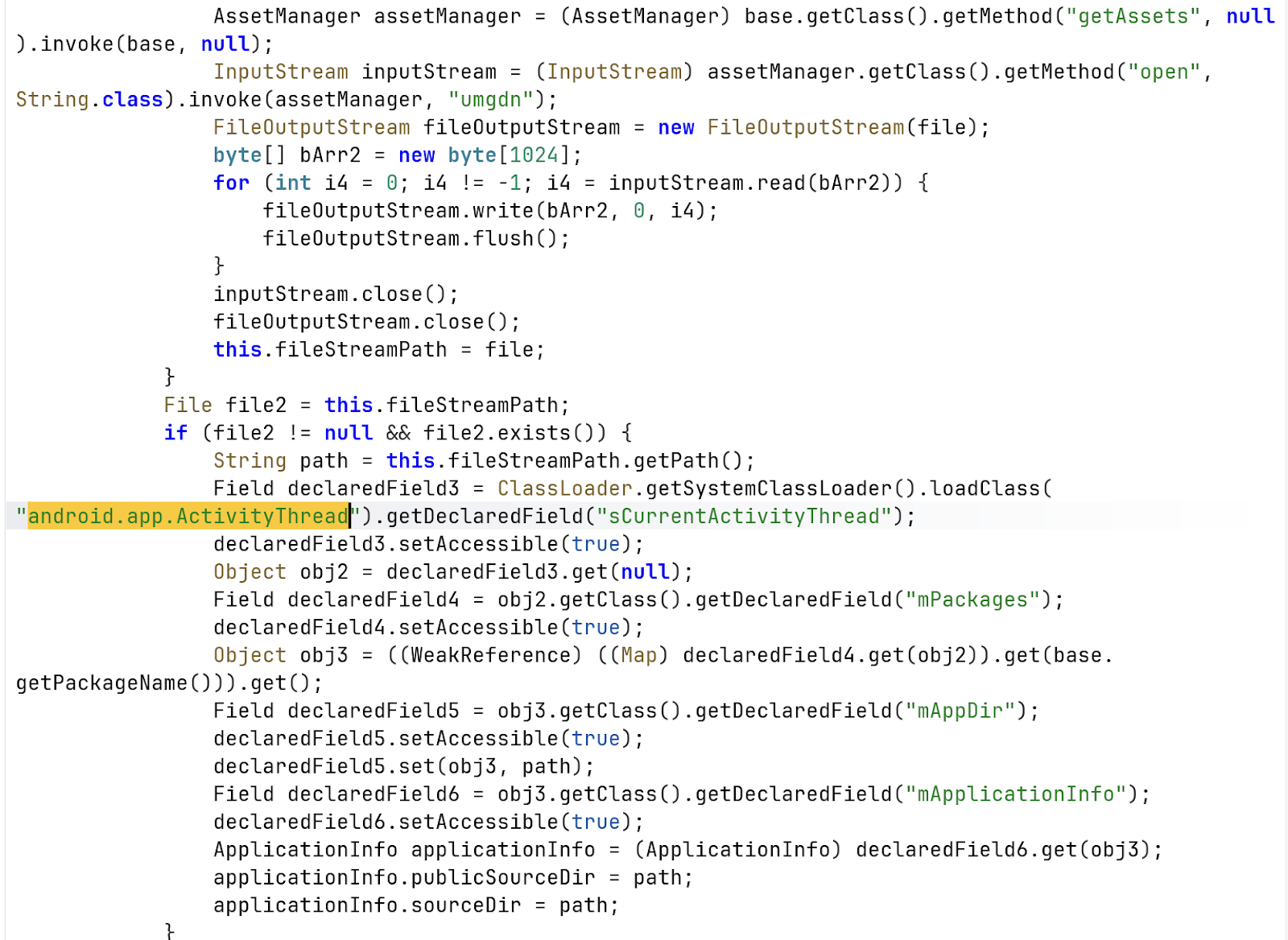
تستخدم الشفرة الانعكاس لربط iPackageManager (على وجه التحديد من خلال SpackageManager في ActivityThread).
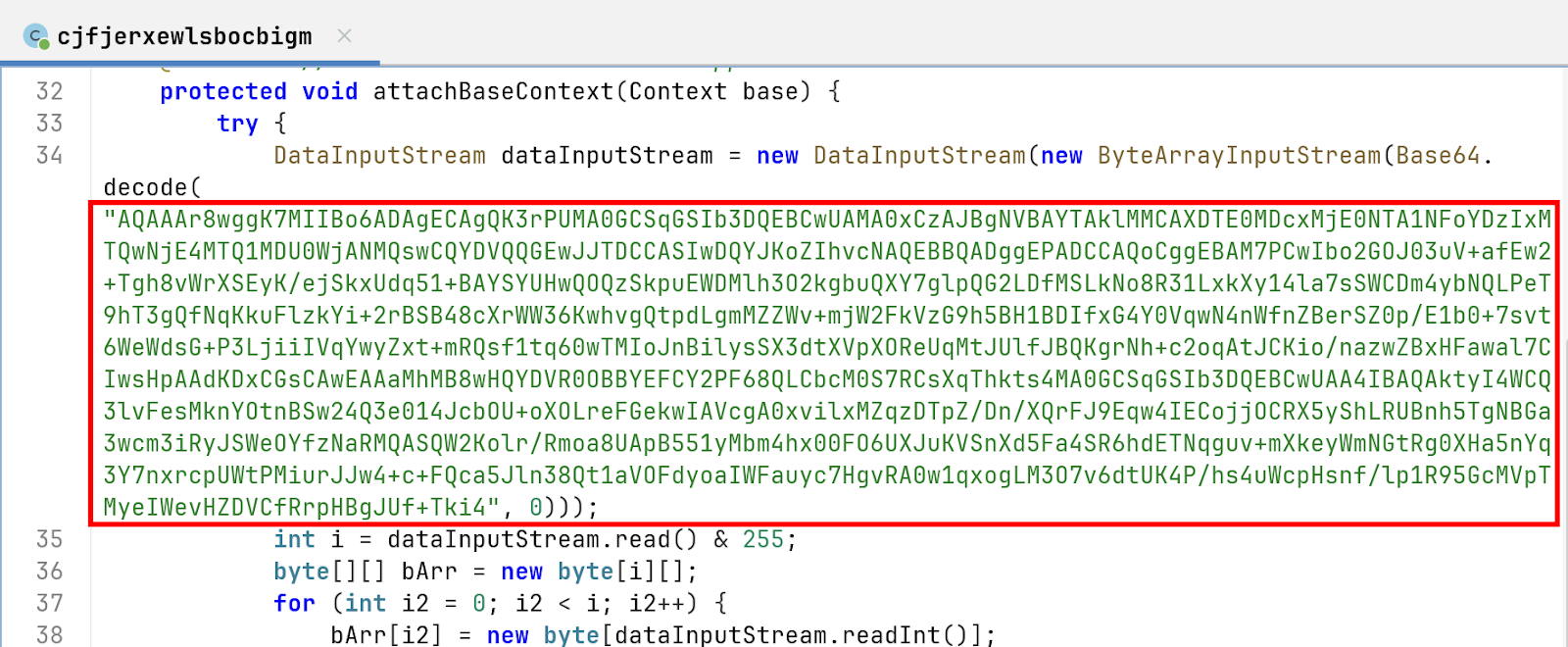
1. وحدات البايت الخاصة بالعنوان (AqaAar8) البايتات القليلة الأولى من السلسلة التي تم فك تشفيرها هي تعليمات لبرنامج DataInputStream الخاص بالبرامج الضارة حول كيفية قراءة الحمولة:
2. شهادة X.509 (WGGK7MiiBO6ad...) وتشكل 703 بايت المتبقية الشهادة الفعلية. يكشف تحليل بنية ASN.1/DER هذه عن تفاصيل التشفير التالية:
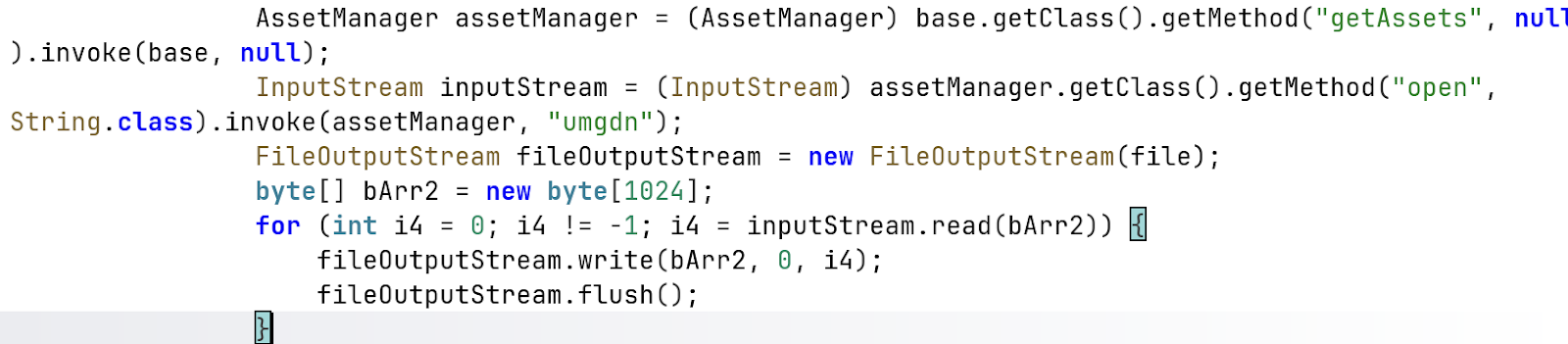
تحتوي طريقة AttachBaseContext على روتين لاستخراج ملف مخفي:
لماذا يعتبر هذا ضارًا: هذه تقنية تستخدم لتحميل حمولة ثانوية «مسقطة» (مثل ملف.dex أو .so) مع جعل النظام يعتقد أنه يتفاعل مع APK الأصلي. من خلال تحديث MappDir و mApplicationInfo عبر التفكير، يمكن للبرامج الضارة تنفيذ التعليمات البرمجية من ملف umgdn مع إخفائها من الفحص القياسي.
تتجنب الشفرة استخدام واجهات برمجة تطبيقات Android القياسية مباشرةً، وتختار بدلاً من ذلك:
تنقسم سلسلة الإصابة بالبرامج الضارة إلى ثلاث مراحل:
المرحلة 1: المحمل الأولي (APK الرئيسي)
يعمل الغلاف الخارجي لـ APK بشكل أساسي كمحمل. اللودر يستخرجه ويحمله كملف DEX في وقت التشغيل، يستخدم التفكير ويربط بمدير حزم Android (على سبيل المثال، عبر فئة تطبيق PMSDexHookApplication) لانتحال توقيعه وتجاوز عمليات التحقق الأولية من التلاعب. وتتمثل مهمتها الأساسية في استخراج أصول المرحلة 2 المخفية وتنفيذها. يتوقع التطبيق الحقيقي شهادة توقيع محددة، ولكن تمت إعادة تعبئة ملف APK أو تغليفه باستخدام أداة تحميل.
يقوم اللودر باعتراض المكالمات مثل: مدير الحزم. احصل على معلومات الحزمة () وتقوم بإرجاع الشهادة الأصلية، مما يمنع التطبيق من اكتشاف أنه تم تعديلها.
المرحلة 2: الحمولة المتوسطة (umgdn)
يتم تخزين هذا المكون داخل دليل assets/ كملف يسمى umgdn (بدون ملحق ملف)، ويتم تحميل هذا المكون ديناميكيًا في الذاكرة بحلول المرحلة 1. من خلال التعامل مع هذا الأصل الخام باعتباره Dalvik Executable (DEX)، تقوم البرامج الضارة بتحويل مسار التنفيذ بعيدًا عن المكونات القابلة للمسح بشكل ثابت لملف APK الأولي.
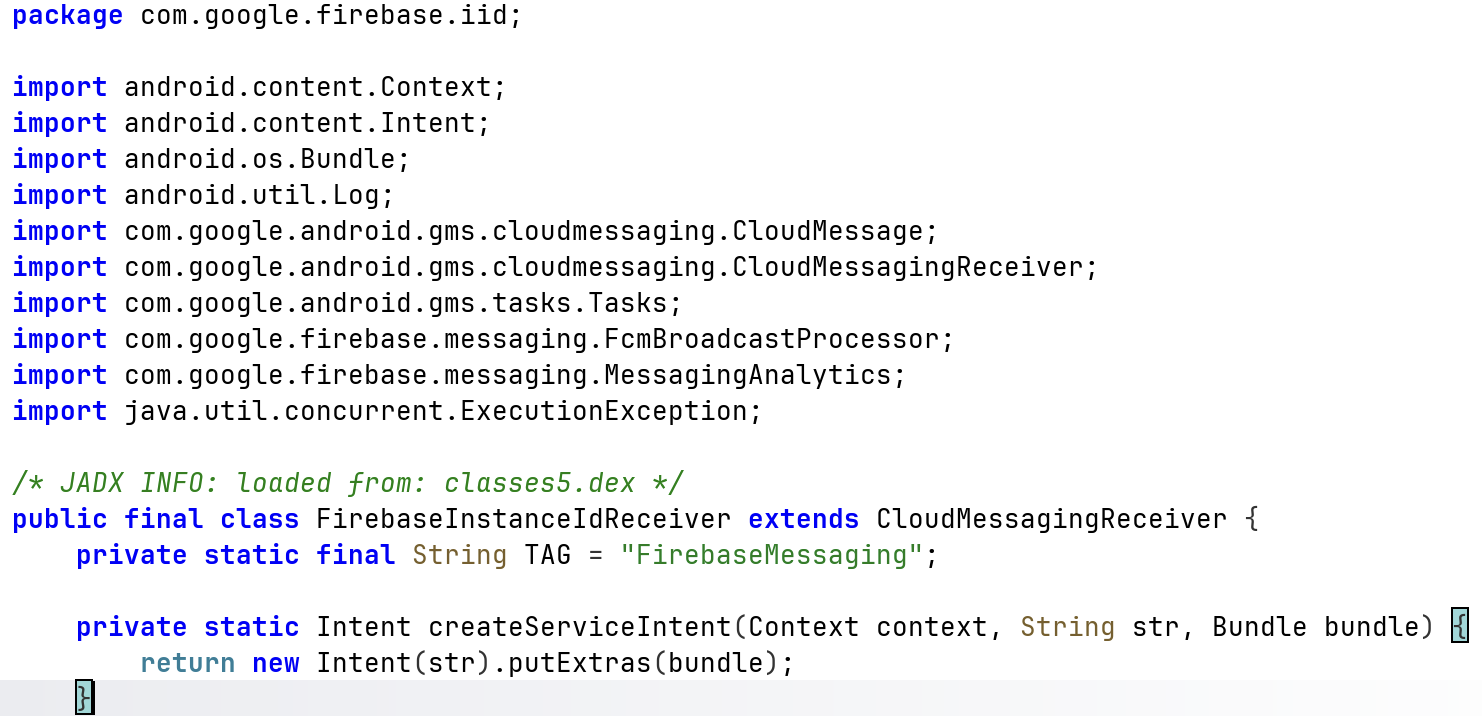
يُظهر تحليل حمولة umgdn أنها تحتوي على منطق تطبيق RedAlert الأصلي، بما في ذلك المكونات التي تتفاعل مع واجهات برمجة تطبيقات Firebase وخدمة Pushy لتسليم الإشعارات الفورية ومعالجة التنبيهات.
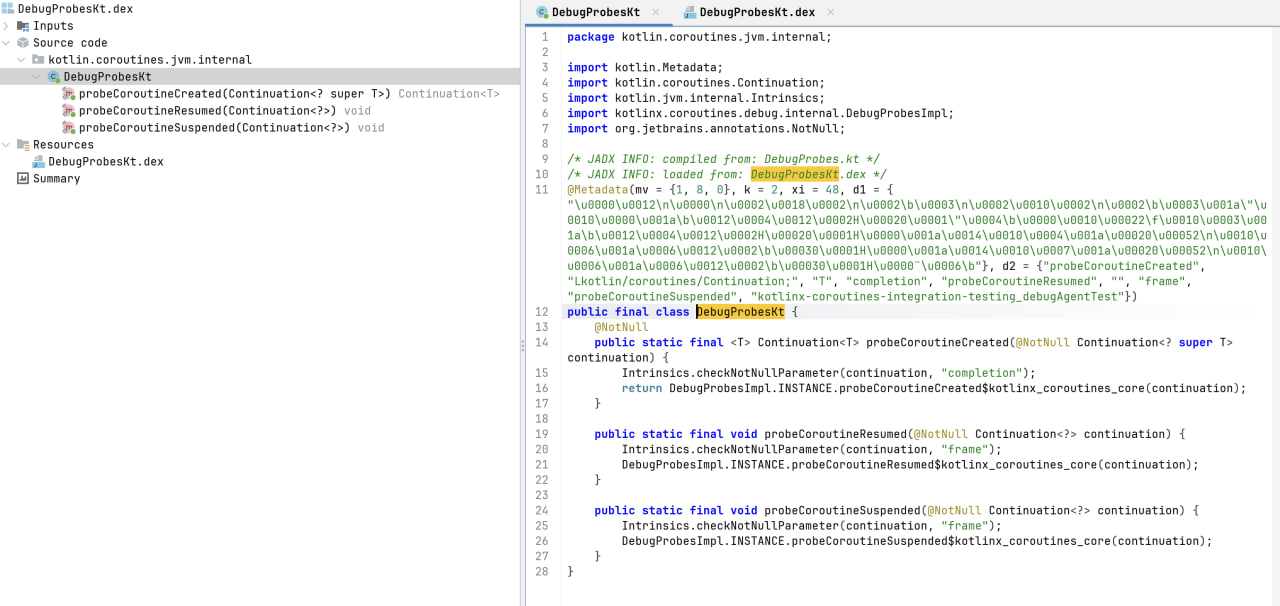
المرحلة 3: مجسات تصحيح الأخطاء التاجية (DebugProbeskt.dex)
تتضمن المرحلة النهائية آليات تحويل فئة وقت التشغيل الموجودة داخل التعليمات البرمجية المحملة ديناميكيًا. المكون المرصود (محول مسبار التصحيح) يعترض تحميل Kotlin.coRoutines.jvm. اختبار داخلي لتصحيح الأخطاء فئة وتستبدل رمز البايت الخاص بها بمورد مضمن (DebugProbesKt.bin).
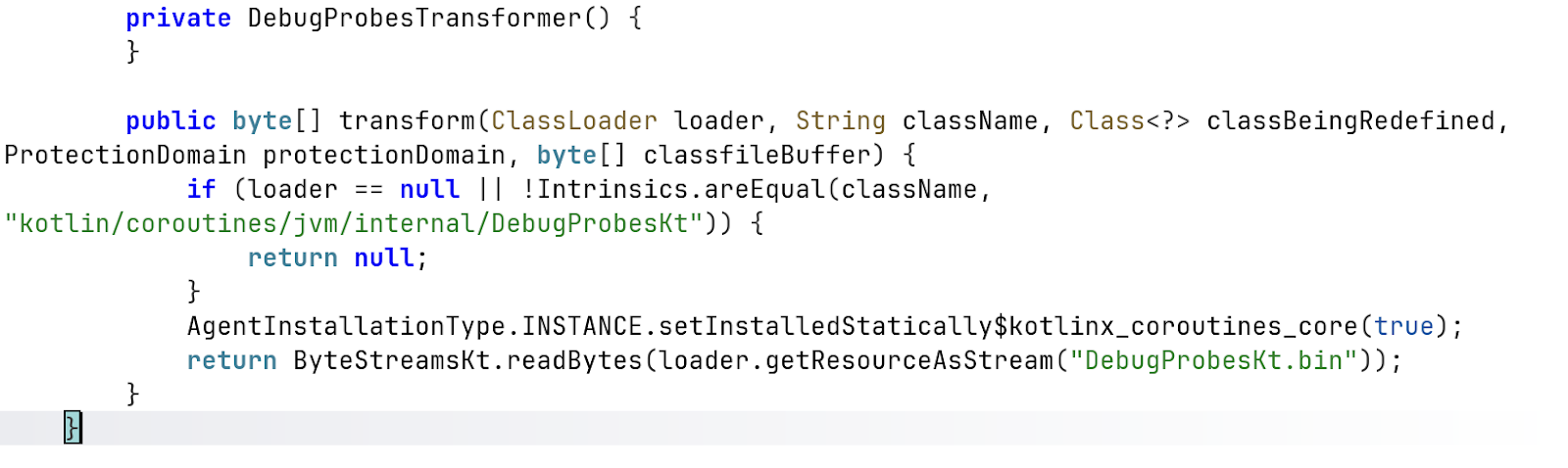
يبدو أن هذه الآلية مرتبطة بأجهزة تصحيح أخطاء Kotlin coroutine بدلاً من الوظائف الضارة المباشرة. ومع ذلك، يمكن لتقنيات استبدال رمز البايت لوقت التشغيل هذه أن تعقد التحليل الثابت عن طريق تغيير سلوك الفئة في وقت التحميل وإخفاء التنفيذ الفعال لوقت التشغيل من الكود المترجم الأصلي.
1. التنفيذ وإخفاء واجهة المستخدم (UI):
أثناء التنفيذ الديناميكي، الحزمة الثلاثية (com.red.alertx) يتم إطلاقه بنجاح ويعكسه تمامًا واجهة المستخدم الرسومية (GUI) لتطبيق Red Alert الرسمي لقيادة الجبهة الداخلية الإسرائيلية. بالنسبة للمستخدم النهائي، لا يوجد أي تناقض مرئي على الإطلاق في الوظائف الأساسية، حيث يقدم التطبيق الضار بنشاط تنبيهات حقيقية للهجمات الصاروخية للحفاظ على تمويهه.

يحدث الاختلاف السلوكي الحرج حصريًا أثناء إطلاق التطبيق الأولي ومرحلة الإعداد. في حين أن التطبيق الشرعي يقيد مطالبته بشكل صارم بالوصول القياسي إلى الإشعارات لإرسال التنبيهات، فإن الحمولة الضارة تطالب الضحية بقوة بأذونات النظام عالية المخاطر (مثل جهات الاتصال والرسائل القصيرة والموقع)، وتخفيها كمتطلبات ضرورية للعمليات الأساسية للتطبيق.
2. سلوك وقت التشغيل ومشغلات التسلل:
بمجرد التنفيذ، تبدأ البرامج الضارة سلسلة رسائل خلفية صامتة تستطلع باستمرار نظام التشغيل Android لتغييرات حالة الإذن. لا تنتظر حتى يتم منح مجموعة كاملة من الأذونات؛ في اللحظة التي يوافق فيها المستخدم على إذن واحد مطلوب، يتم تشغيل وحدة تجميع البيانات المرتبطة ديناميكيًا.
وقد لوحظ أن البرنامج الضار يقوم بتجميع المعلومات الاستخباراتية المجمعة (بما في ذلك البريد الوارد للرسائل القصيرة وقوائم جهات الاتصال الكاملة وإحداثيات GPS في الوقت الفعلي) في ملفات محلية مصنفة قبل بدء حلقة التسلل الخاصة بها.
3. اتصالات الشبكة والبنية التحتية:
يؤكد تحليل حركة مرور الشبكة أن البرامج الضارة تحافظ على اتصالات قوية ومستمرة مع البنية التحتية للقيادة والتحكم (C2). بمجرد تنظيم البيانات محليًا، يتم تكرار سلسلة رسائل التحميل المخصصة، مما يؤدي إلى إنشاء اتصالات خارجية سريعة لنقل الحمولة عبر طلبات HTTP POST إلى https://api[.]ra-backup[.]com/analytics/submit.php.
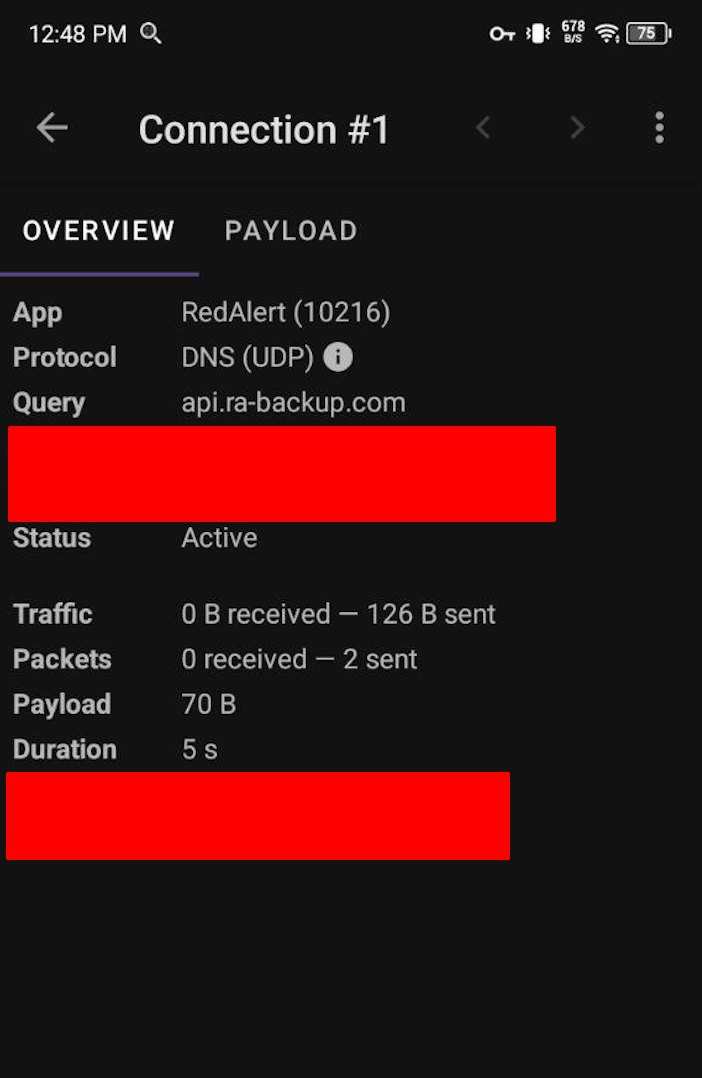
تم التقاط عناوين IP التالية أثناء مرحلة التنفيذ الديناميكي، والتي تمثل البنية التحتية التي تسهل التسلل واتصالات C2:
ملاحظة: يشير وجود عناوين 104.21.xx و 172.67.xx إلى أن الجهات الفاعلة في مجال التهديد تستفيد من Cloudflare لتوكيل البنية التحتية الخلفية الحقيقية وحمايتها، بينما تشير عناوين 44.x.xx إلى بيئات استضافة AWS.
اسم التطبيق: RedAlert.apk
1. تسليح الذعر النشط في زمن الحرب (الإغراء):
ومع الهجمات الانتقامية الإيرانية بالصواريخ الباليستية والطائرات بدون طيار التي تستهدف بنشاط الأراضي الإسرائيلية والقواعد الأمريكية في جميع أنحاء الخليج، فإن المواطنين بحاجة ماسة إلى أنظمة الإنذار المبكر في الوقت الفعلي. إن التنكر في زي تطبيق «الإنذار الأحمر» الرسمي التابع لقيادة الجبهة الداخلية الإسرائيلية يستغل بشكل مباشر هذه الضرورة الملحة للحياة أو الموت، مما يضمن فعليًا معدل إصابة مرتفعًا بشكل استثنائي حيث يتجاوز الضحايا النظافة الأمنية القياسية بحثًا عن الأمان.
2. الاستهداف الحركي ومخاطر الأمن المادي (تتبع الموقع):
في سياق حرب نشطة متعددة الجبهات، تتجاوز وظيفة التتبع المستمر لنظام تحديد المواقع العالمي (GPS) للبرامج الضارة المراقبة الرقمية القياسية. يوفر تحديد الموقع الجغرافي لآلاف الأجهزة المصابة في الوقت الفعلي للخصوم - معلومات استخبارية جماعية وقابلة للتنفيذ. يمكن استخدام هذه البيانات كسلاح لرسم خرائط لمواقع الملاجئ المدنية، أو تتبع الحركة الجماعية للسكان النازحين، أو تحديد تركيز ونشر جنود الاحتياط في جيش الدفاع الإسرائيلي، مما قد يؤدي إلى تحسين استهداف وابل الصواريخ القادمة.
3. جمع المعلومات الاستراتيجية (استخراج البيانات):
يسمح التسلل العدواني لمدير حساب الجهاز وقوائم جهات الاتصال الكاملة وصندوق الرسائل القصيرة للجهات الفاعلة في مجال التهديد التي ترعاها الدولة برسم الرسوم البيانية الاجتماعية للسكان المصابين بسرعة. يتيح جمع البيانات الشامل هذا تحديد الأهداف عالية القيمة (HVTs) - مثل الأفراد العسكريين أو المسؤولين الحكوميين أو مقاولي الدفاع - للاستغلال الثانوي. علاوة على ذلك، فإن اعتراض اتصالات الرسائل القصيرة في الوقت الفعلي يسمح للخصوم بتجاوز 2FA على شبكات البنية التحتية الحيوية أو شن حرب نفسية عالية الاستهداف (على سبيل المثال، إرسال رسائل SMS محبطة أو خادعة أثناء انقطاع البنية التحتية).
4. تآكل سلامة الاستجابة للطوارئ:
من خلال الاستيلاء الناجح على العلامة التجارية ووظائف تطبيق مهم لإنقاذ الحياة، تنفذ هذه الحملة شكلاً مدمرًا من حرب المعلومات. إذا علم السكان المدنيون أن تطبيقات الإنذار في حالات الطوارئ يتم تصنيفها بشكل كبير، فسوف تنهار ثقة الجمهور في قنوات البث الحكومية الرسمية. قد يتردد المواطنون في تثبيت تحديثات شرعية لقيادة الجبهة الداخلية أو البدء في تجاهل صفارات الإنذار الأصلية، مما يزيد بشكل مباشر من خطر وقوع إصابات في صفوف المدنيين خلال الغارات الجوية المستمرة.
لاحتواء التهديد الذي يشكله com.red.alertx حملة برامج التجسس ومنع المزيد من تسريب البيانات، يجب على المنظمات والأفراد المتضررين تنفيذ العلاج التكتيكي الفوري والدفاعات الاستراتيجية طويلة المدى.
نظرًا لإمكانيات جمع البيانات الشاملة للبرامج الضارة، فإن الاعتماد فقط على إلغاء تثبيت التطبيق القياسي غير كافٍ.
يجب على مسؤولي الشبكة حظر جميع محاولات الاتصال بالبنية التحتية لممثل التهديد على الفور.
لمنع العدوى المستقبلية الناجمة عن الهندسة الاجتماعية في زمن الحرب والطعوم المضللة: